Introduction
Application security penetration testing is a crucial strategy for organizations seeking to protect their digital assets from rising cyber threats. By proactively identifying vulnerabilities, businesses can prevent costly data breaches and improve compliance with industry regulations. As the landscape of cyber risks continues to evolve, organizations must ensure their testing methods remain effective and relevant. This article outlines four best practices that can help organizations refine their penetration testing approaches, ultimately strengthening their security posture in an increasingly complex environment.
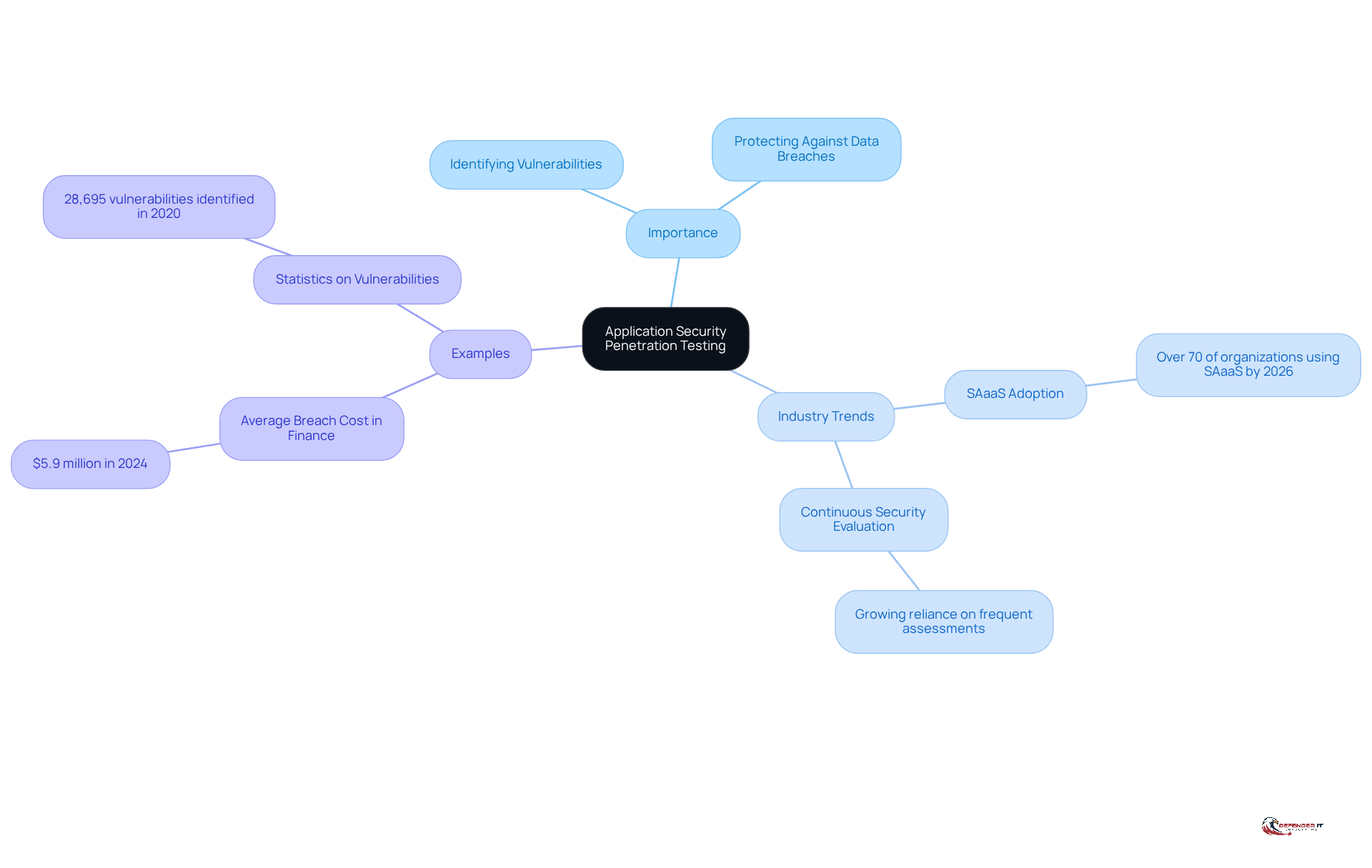
Understand the Importance of Application Security Penetration Testing
Application security penetration testing is essential for identifying vulnerabilities within applications before they can be exploited by malicious actors. This proactive approach is particularly crucial for organizations in regulated industries, such as finance and healthcare, where can lead to significant financial losses and reputational damage. For example, financial organizations that regularly conduct security assessments have successfully pinpointed weaknesses in their online banking applications, enabling them to address these vulnerabilities before cybercriminals can exploit them. According to IBM, the financial industry faced an average breach cost of approximately $5.9 million in 2024, underscoring the necessity of robust protective measures.
Current trends indicate a growing reliance on security assessments as companies strive to enhance their security posture. By 2026, the adoption of continuous security evaluation models is expected to rise, with over 70% of organizations utilizing Security Assessment as a Service (SAaaS). This transition facilitates more frequent assessments, allowing organizations to stay ahead of evolving threats. Furthermore, vulnerability assessments not only aid in identifying weaknesses but also ensure compliance with industry benchmarks and regulations, thereby fulfilling critical protection requirements. As Nivedita James Palatty notes, “this article has gathered essential evaluation statistics that demonstrate the significance of application security penetration testing, and how companies are increasingly utilizing its services to enhance their protection efforts.” As the landscape of cyber threats continues to evolve, the importance of application protection evaluation cannot be overstated.
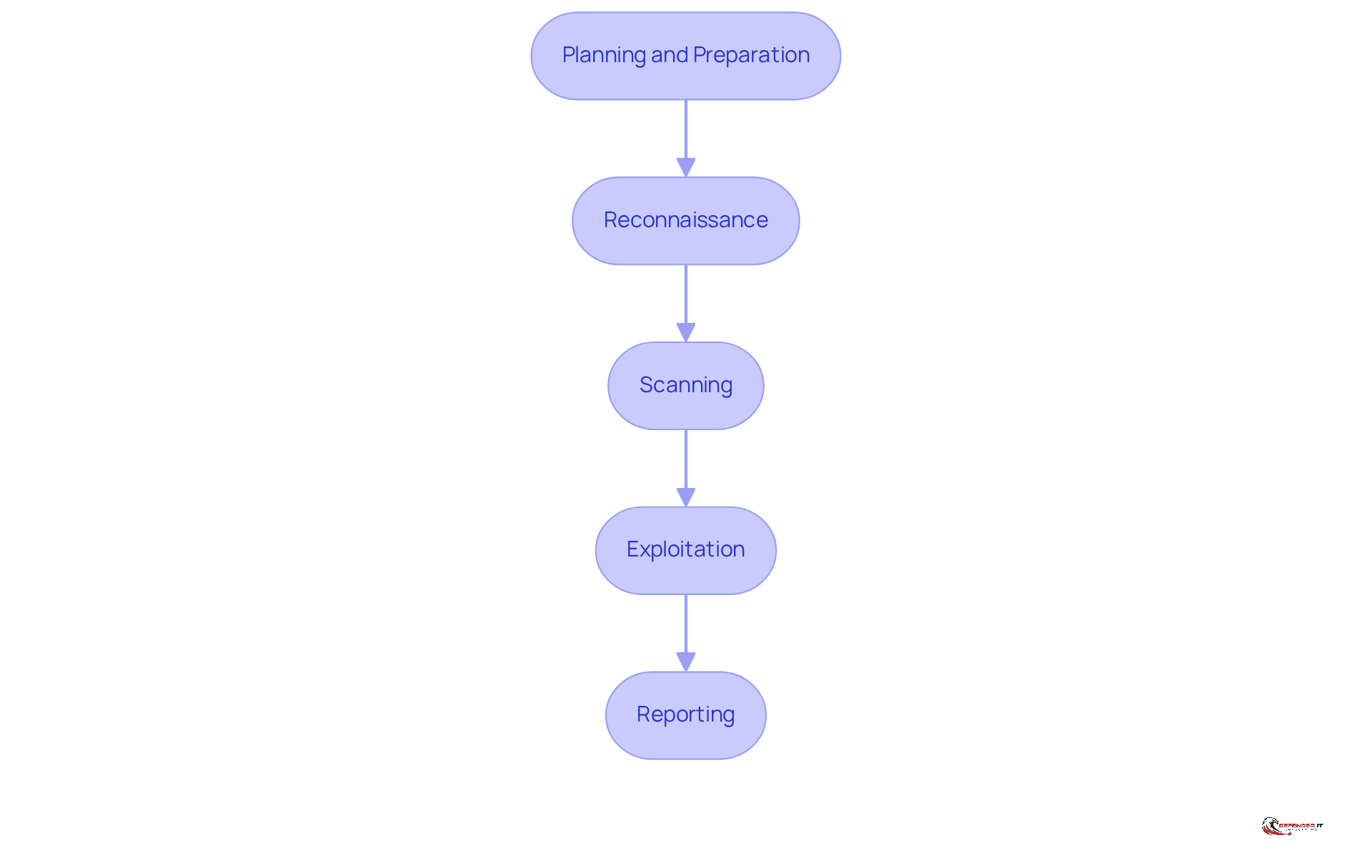
Follow a Structured Approach: Stages of Penetration Testing
A systematic method for security assessment encompasses several essential phases:
- Planning and Preparation: This initial phase involves defining the scope, objectives, and rules of engagement for the test.
- Reconnaissance: In this stage, information about the target application is gathered to identify potential attack vectors.
- Scanning: Automated tools are employed to within the application.
- Exploitation: Here, attempts are made to exploit identified vulnerabilities to assess their impact.
- Reporting: This final phase documents findings, including discovered vulnerabilities, exploitation attempts, and recommendations for remediation.
By adhering to this organized approach, organizations can ensure a [comprehensive evaluation of their application security penetration testing](https://thehackernews.com/expert-insights/2026/01/the-2026-state-of-pentesting-how-modern.html), leading to more effective remediation strategies.
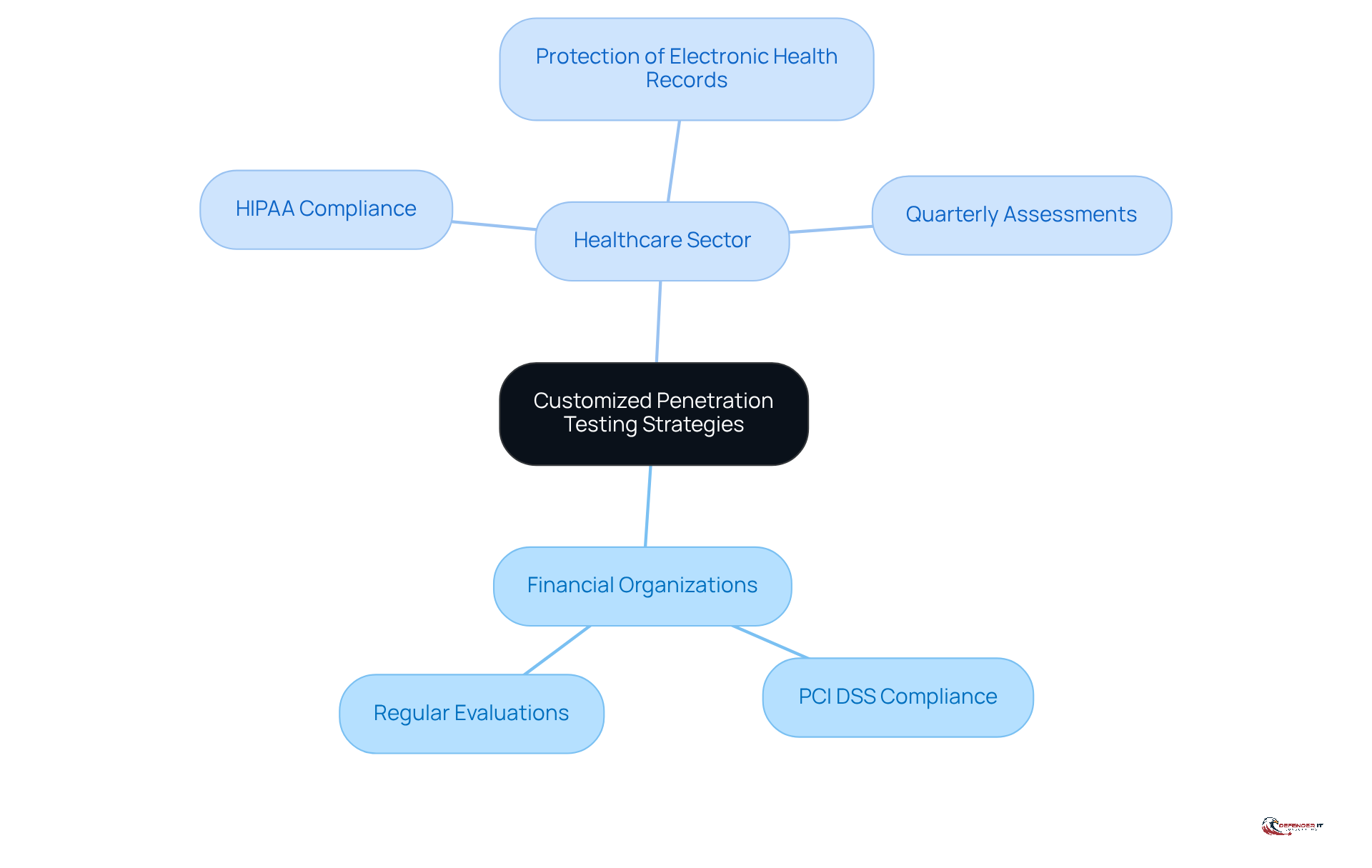
Customize Penetration Testing Strategies for Your Industry
Different sectors face unique protection needs and threat environments that necessitate tailored testing approaches. For instance, financial organizations must adhere to regulations such as PCI DSS, which mandates regular evaluations to protect sensitive payment information. In the healthcare sector, where patient information is particularly vulnerable, testing must prioritize the safeguarding of electronic health records and ensure compliance with HIPAA regulations. The updates to HIPAA in 2026 require designated protection officers and formalized risk management procedures, highlighting the need for stricter access controls and enhanced encryption. Consequently, it is essential for healthcare institutions to conduct quarterly assessments that simulate real-world attacks, allowing them to efficiently identify vulnerabilities, as healthcare providers must perform these evaluations to bolster their protective measures.
By [customizing application security penetration testing strategies](https://defenderit.consulting/4-best-practices-for-cloud-networking-security-in-manufacturing/) to address these specific requirements, organizations can more effectively identify and mitigate risks that are particularly relevant to their operations. This approach not only strengthens their overall security posture but also ensures , ultimately safeguarding their reputation and operational integrity. Regular risk assessments and continuous training for IT teams are vital components of this strategy, as ongoing training fosters awareness among staff and patients regarding privacy risks, thereby promoting a culture of compliance and preparedness against evolving cyber threats.
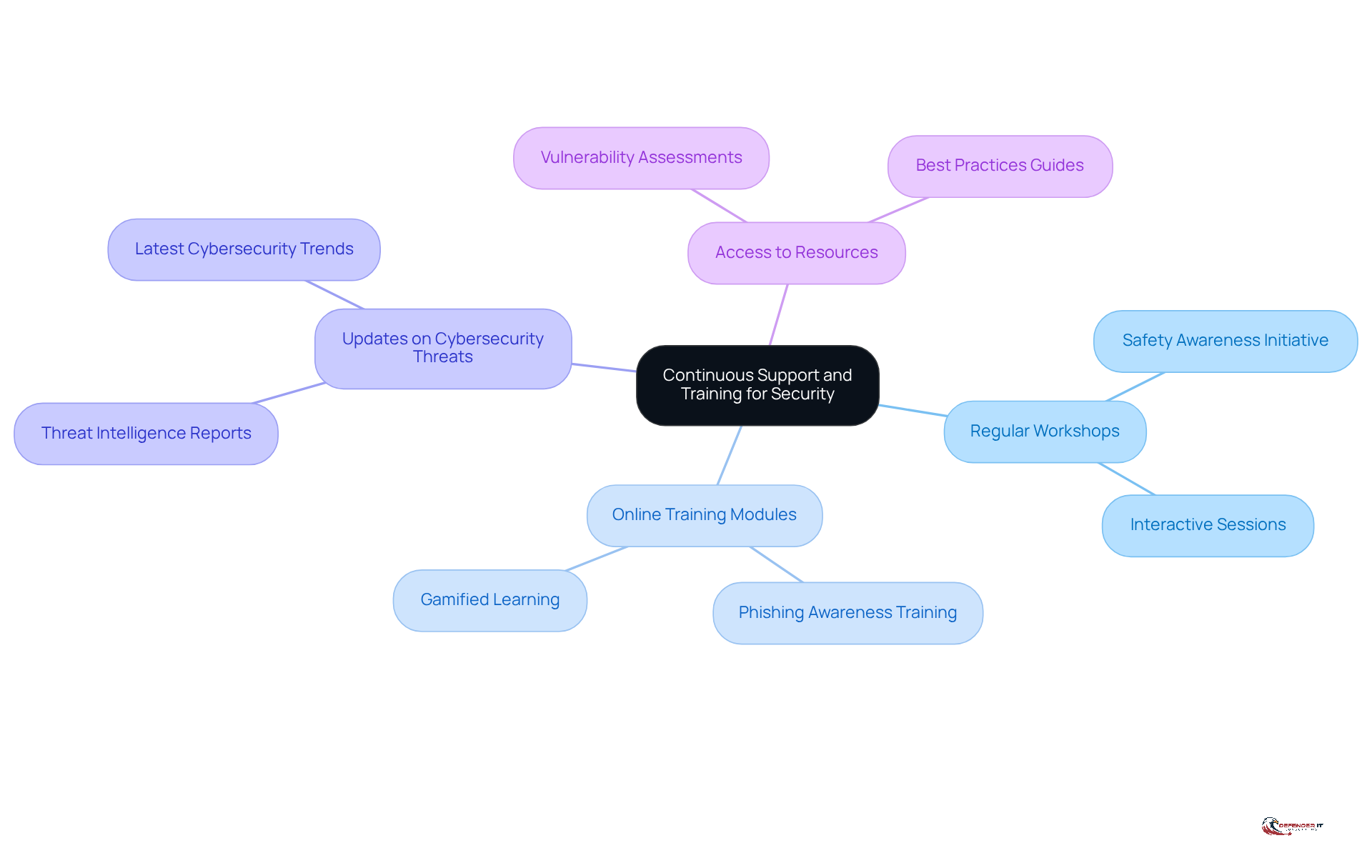
Implement Continuous Support and Training for Lasting Security
To maintain a strong protective posture, companies must prioritize for their personnel. This commitment includes:
- Regular workshops
- Online training modules
- Updates on the latest cybersecurity threats and best practices
For instance, organizations can implement a safety awareness initiative designed to equip staff with the skills to recognize phishing attempts and other social engineering tactics.
Furthermore, providing access to resources such as threat intelligence reports enables teams to stay informed about the ever-evolving threat landscape. By cultivating a culture of security awareness and ensuring continuous training, organizations can significantly mitigate their risk of becoming victims of cyber attacks.
Conclusion
Application security penetration testing is a crucial defense against cyber threats, allowing organizations to identify and address vulnerabilities before they can be exploited. This proactive approach is particularly essential in sectors where data breaches can lead to significant financial and reputational damage. As cyber threats continue to evolve, the necessity for rigorous and structured penetration testing practices becomes increasingly clear.
The article underscores the importance of a systematic approach to penetration testing, which includes phases such as:
- Planning
- Reconnaissance
- Exploitation
- Reporting
By tailoring penetration testing strategies to the specific needs of various sectors, organizations can effectively manage their unique risk profiles and comply with regulatory requirements. Additionally, the focus on continuous training and support highlights the importance of cultivating a culture of security awareness among personnel, which is vital for maintaining a strong defense against potential cyber attacks.
Ultimately, investing in application security penetration testing and ongoing education transcends mere compliance; it is a strategic necessity that protects an organization’s integrity and reputation. By adopting these best practices, companies can strengthen their security posture, adapt to emerging threats, and safeguard sensitive data, thereby ensuring resilience in an increasingly complex digital landscape.
Frequently Asked Questions
What is application security penetration testing?
Application security penetration testing is a proactive approach used to identify vulnerabilities within applications before they can be exploited by malicious actors.
Why is application security penetration testing important for organizations?
It is crucial for organizations, especially in regulated industries like finance and healthcare, as data breaches can lead to significant financial losses and reputational damage.
Can you provide an example of how penetration testing helps organizations?
Financial organizations that regularly conduct security assessments have successfully identified weaknesses in their online banking applications, allowing them to address these vulnerabilities before cybercriminals can exploit them.
What are the financial implications of data breaches in the financial industry?
According to IBM, the financial industry faced an average breach cost of approximately $5.9 million in 2024, highlighting the necessity of robust protective measures.
What trends are emerging in the field of application security testing?
There is a growing reliance on security assessments, with a projected rise in the adoption of continuous security evaluation models. By 2026, over 70% of organizations are expected to utilize Security Assessment as a Service (SAaaS).
How do vulnerability assessments contribute to compliance?
Vulnerability assessments help identify weaknesses and ensure compliance with industry benchmarks and regulations, fulfilling critical protection requirements.
What is the significance of application security penetration testing according to experts?
Experts like Nivedita James Palatty emphasize the importance of application security penetration testing and how companies are increasingly utilizing its services to enhance their protection efforts against evolving cyber threats.