Introduction
Understanding Controlled Unclassified Information (CUI) is increasingly vital as organizations navigate the complexities of data protection and compliance. This guide explores the responsibilities associated with applying CUI markings in dissemination instructions, emphasizing the essential roles of:
- Information owners
- Designating officials
- Program managers
Given the rising compliance challenges and frequent marking errors, a critical question arises: who is ultimately responsible for ensuring that CUI is labeled correctly and consistently across all platforms?
Understand Controlled Unclassified Information (CUI)
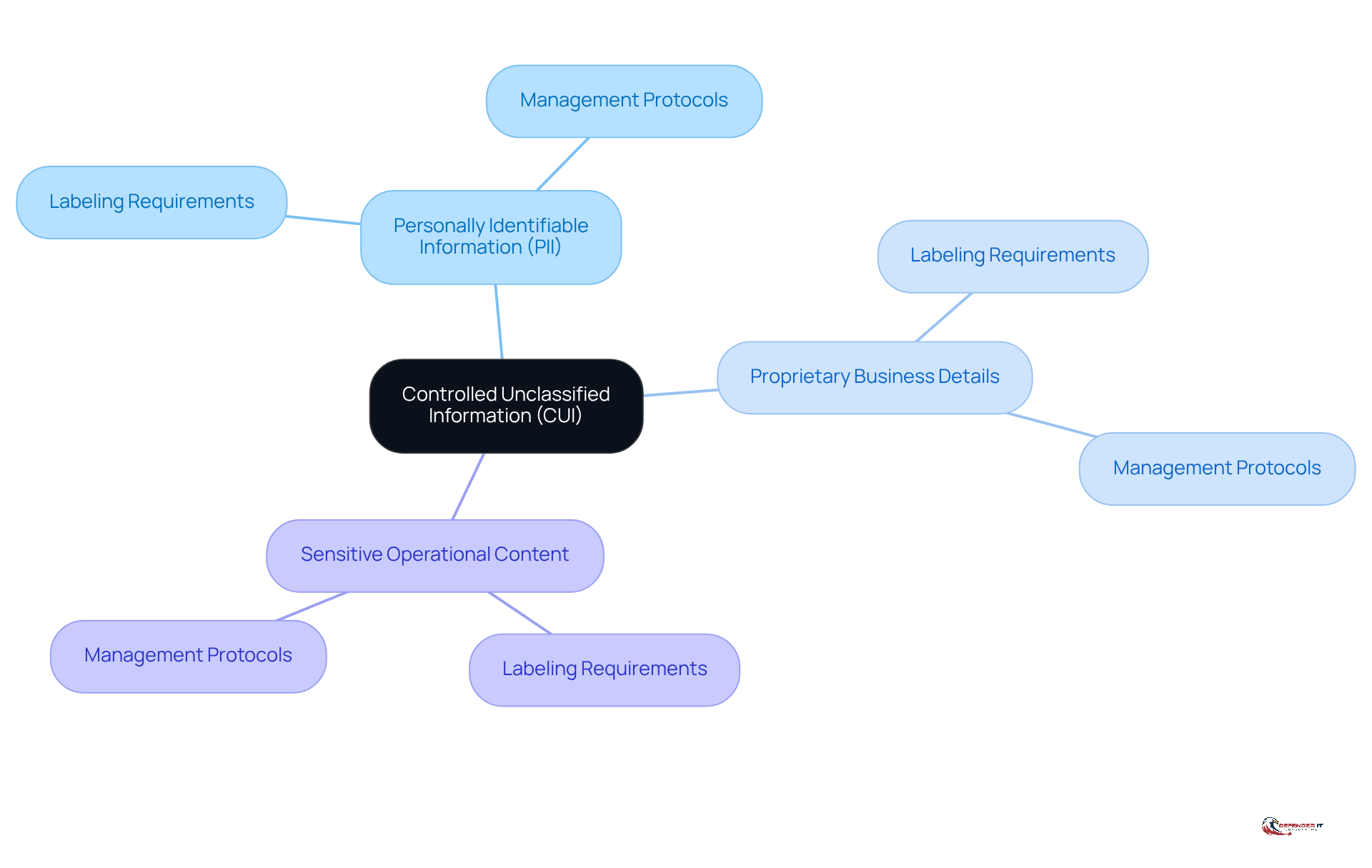
is defined as information that necessitates safeguarding or dissemination controls as mandated by law, regulation, or government-wide policy. Understanding CUI is crucial for organizations, particularly for entities that handle government contracts or sensitive information. CUI encompasses various data types, including:
- personally identifiable information (PII)
- proprietary business details
- sensitive operational content
Familiarizing oneself with the categories of CUI and the specific requirements for labeling and managing this data is the foundational step toward ensuring compliance and protecting sensitive information.
As of 2026, a significant percentage of organizations reported awareness of CUI requirements, with estimates suggesting that awareness levels have increased to approximately 70%. This growing recognition highlights the critical role of CUI within cybersecurity frameworks. Eric Trexler emphasizes, “Understanding CUI is not merely a regulatory obligation; it is a critical component of an organization’s overall security posture.”
Establishing a culture of data protection is essential. Organizations must ensure they are well-versed in CUI regulations and the specific protocols for marking and handling this information. Additionally, contractors are required to report any suspected or confirmed breaches within eight hours of discovery, a critical obligation that organizations must prioritize. This foundational knowledge not only aids in compliance but also fosters a proactive approach to data security.
Identify Responsible Parties for CUI Markings
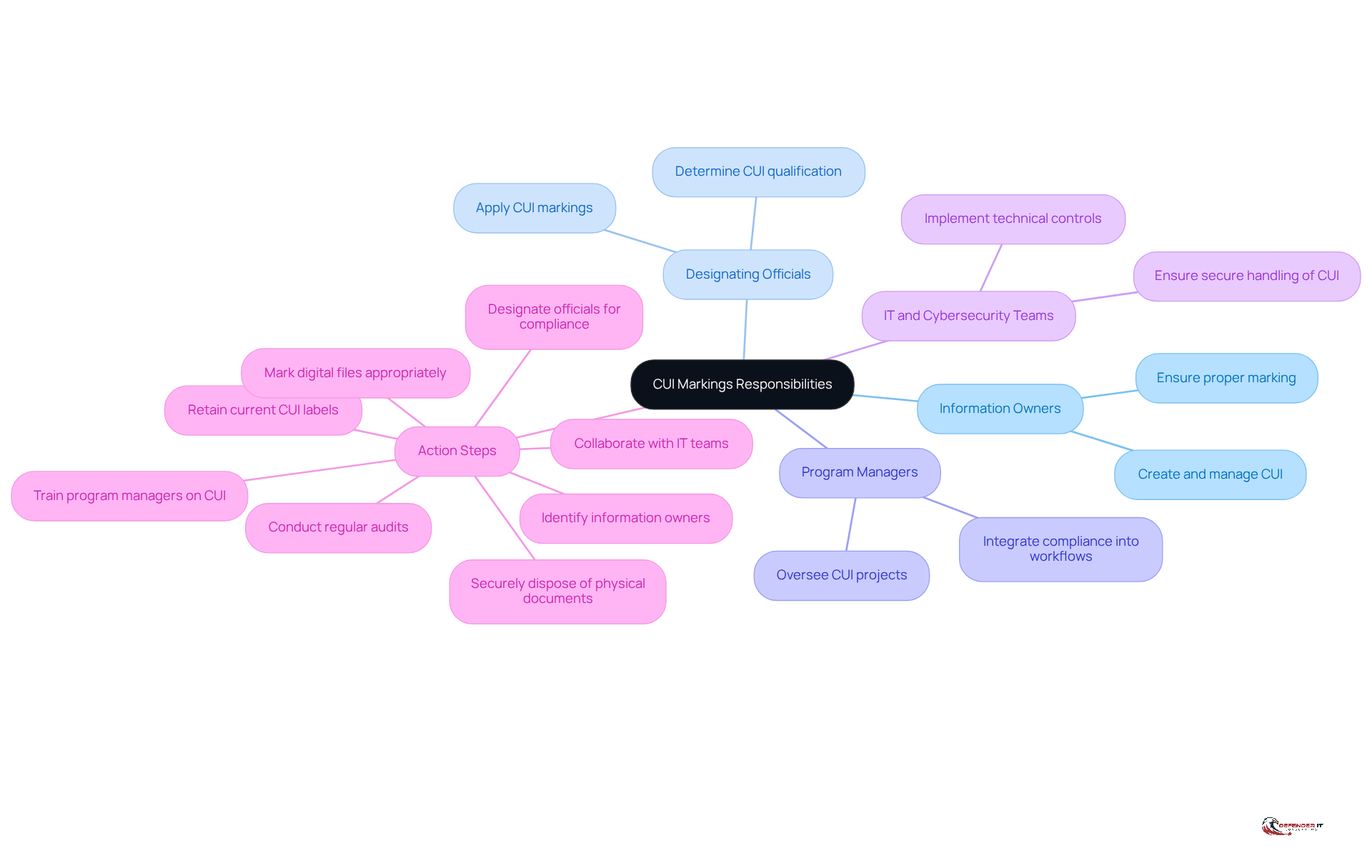
The responsibility for implementing labels lies with key stakeholders within an organization, including those who are responsible for CUI markings, each playing a vital role in ensuring compliance and security. The primary stakeholders include:
- CUI creators: These individuals create or manage CUI and are primarily responsible for ensuring that it is marked appropriately. Their understanding of the data’s sensitivity is crucial for its proper handling.
- CUI reviewers: Authorized personnel who are responsible for evaluating and determining what information qualifies as CUI. Their role is essential in maintaining adherence to federal guidelines and organizational policies.
- Project managers: They oversee projects involving CUI and ensure that all labeling requirements are met. Their leadership is critical in integrating CUI compliance into project workflows.
- IT security teams: These teams support the marking process by implementing technical controls and ensuring that CUI is handled securely. Their expertise is vital in protecting sensitive data from unauthorized access.
To effectively manage CUI compliance, organizations should take the following action steps:
- Identify the stakeholders within your organization to clarify labeling responsibilities.
- Designate officials responsible for making evaluation decisions and ensuring adherence to policies.
- Ensure that employees receive training on CUI requirements to facilitate proper handling and labeling.
- Collaborate with legal teams to establish robust protocols for labeling and securely managing CUI, thereby enhancing overall security.
- Conduct regular audits to identify gaps in adherence and continuously improve policies and procedures related to CUI.
- Retain current CUI labels and apply them to any derived documents to ensure compliance.
- Ensure physical documents containing CUI are disposed of securely and in accordance with handling regulations.
- Mark digital files containing CUI in headers, footers, and key locations to indicate their sensitive nature.
Apply CUI Markings in Dissemination Instructions
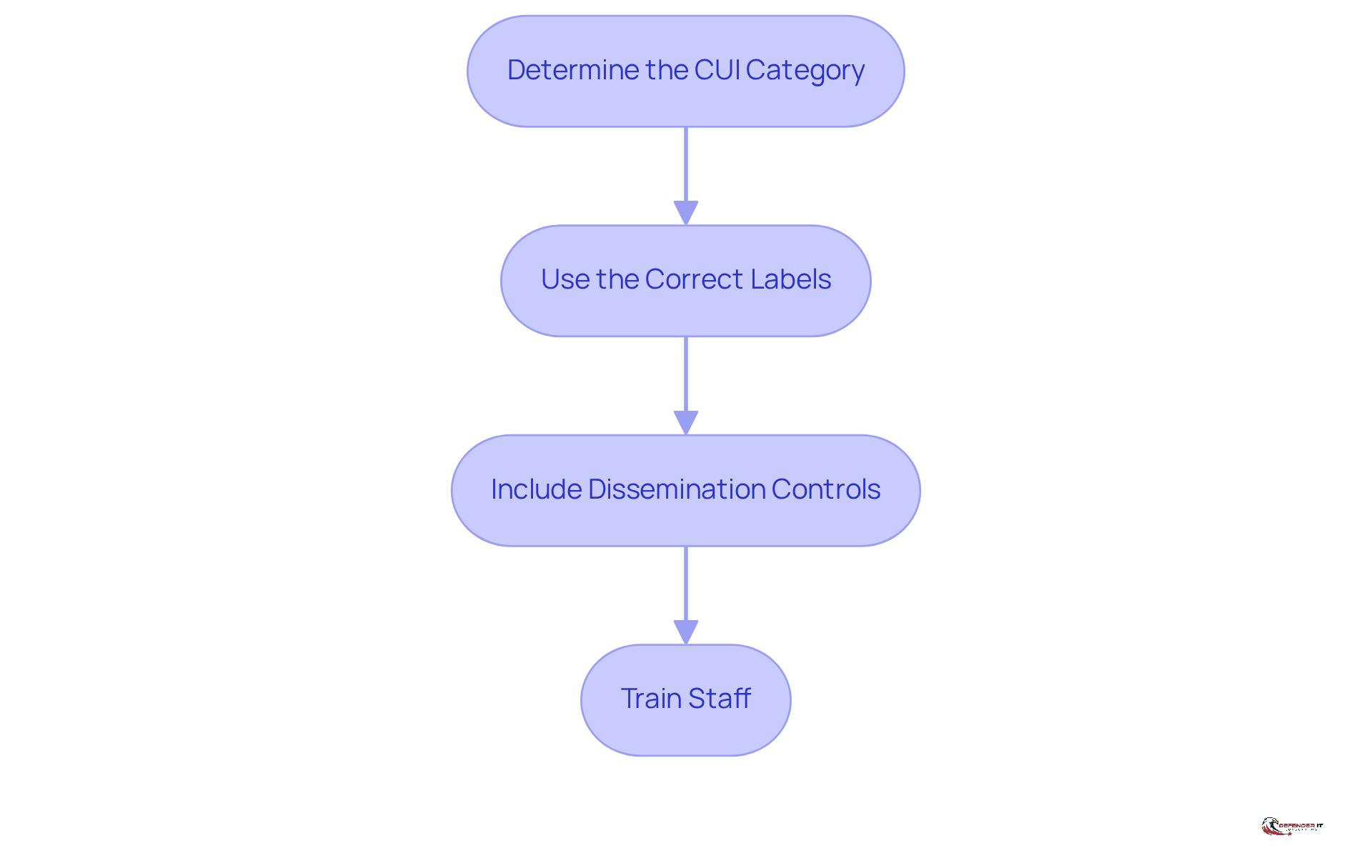
To apply CUI markings, follow these steps:
- Determine the CUI Category: Identify the specific category of information relevant to the content being disseminated. It is crucial for proper handling to understand the requirements in dissemination instructions regarding the CUI category.
- Use the Correct Labels: Apply labels according to the guidelines established by the CUI program. This includes placing the ‘CUI’ banner at both the top and bottom of documents and including a designation indicator on the first page. Proper labeling is essential; evaluations have shown that 9% of documents from 2023 and 11% from 2024 lacked the required CUI designation indicator block, raising the question of who is responsible for applying CUI markings.
- Include Limitations: Clearly specify any limitations on the distribution, such as ‘Limited Distribution’ or ‘For Official Use Only’. Organizations often restrict distribution to ‘Federal Employees and Contractors Only’ or ‘Federal Employees Only’, which raises questions about limitations in dissemination instructions and can hinder effective sharing. It is recommended to use ‘None’ or no limitation designation when appropriate.
- Train Staff: Ensure that all personnel involved in the dissemination receive comprehensive training on labeling requirements and the significance of adherence. Familiarity with the CUI registry and ongoing training can significantly enhance an organization’s ability to identify who is responsible for applying CUI markings to protect sensitive information.
Best Practices:
- Always verify that markings are visible and correctly applied before dissemination to prevent compliance issues.
- Utilize templates that include CUI symbols to streamline the process and reduce the risk of errors.
- Consistently assess and refresh training to represent current adherence levels and optimal methods for indicating CUI in documents.
Troubleshoot Common Issues with CUI Markings
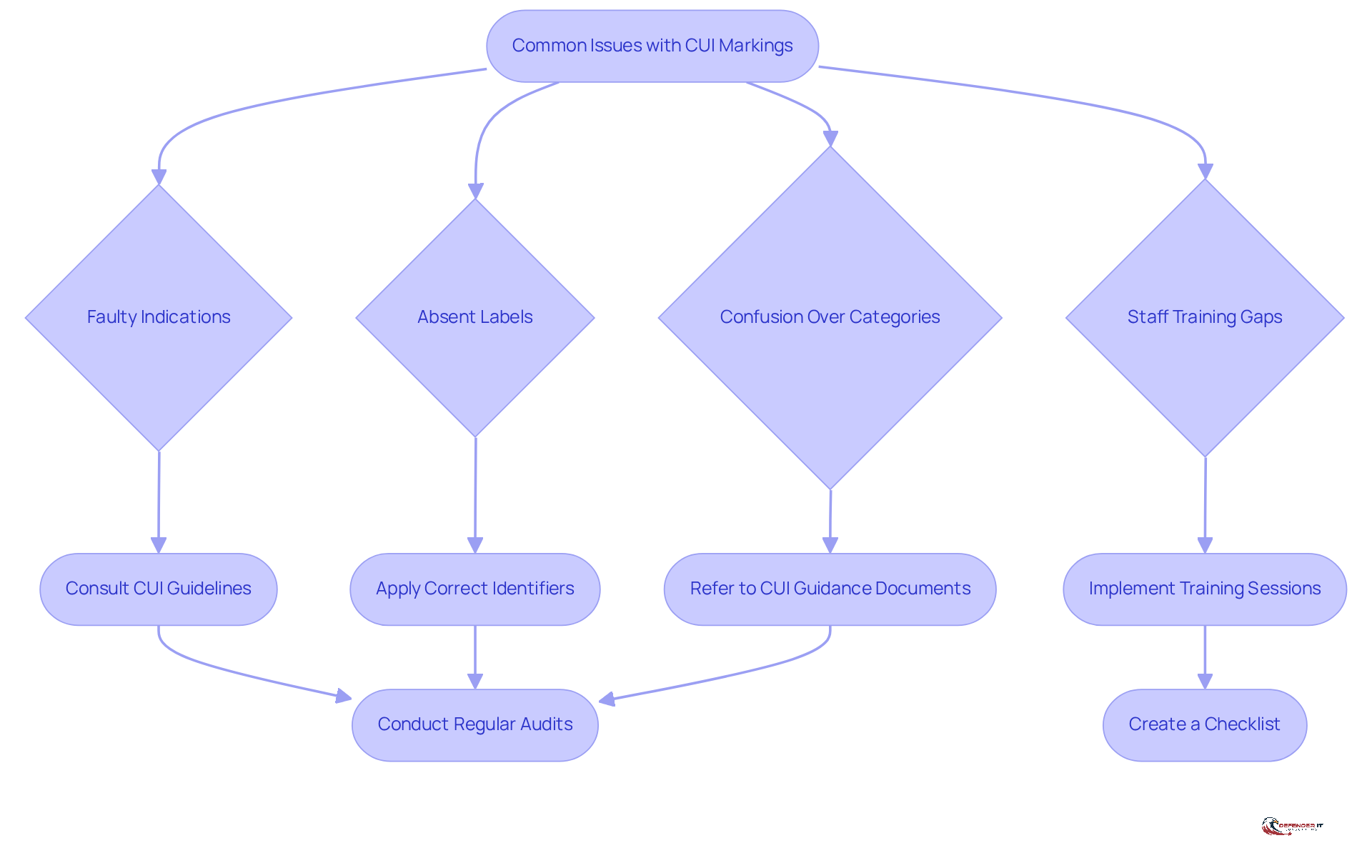
Common issues with Controlled Unclassified Information (CUI) labels can lead to confusion and significant risks. Recent assessments indicate that approximately 9% of documents examined lacked the necessary CUI designation indicator block. Furthermore, in 2024, 11% of 26,000 reviewed documents also failed to include this crucial identification. This highlights the prevalence of inaccurate or absent indicators. To address these challenges, consider the following troubleshooting tips:
- Faulty Indications: If indications are applied improperly, consult the guidelines to ensure adherence. Utilize the manual as a reference to confirm the appropriate categories and labels.
- Absent Labels: If CUI is found without the appropriate labels, promptly apply the correct identifiers and notify the information owner to ensure accountability and compliance.
- Confusion Over Categories: In instances of uncertainty regarding applicable categories, consult designated officials or refer to the classification guide to clarify the correct classification. This confusion often arises from misconceptions about who is responsible for applying markings in dissemination instructions and the CUI program.
- Lack of Training: If staff members lack familiarity with CUI requirements, implement regular training sessions to reinforce understanding and compliance. This proactive approach can significantly reduce errors in assessment.
Action Steps:
- Conduct regular audits of documents to identify and rectify issues, ensuring that all documents are properly classified.
- Create a checklist for staff to follow when labeling CUI to minimize errors and enhance consistency in application.
By addressing these common challenges, organizations can strengthen their compliance posture and mitigate the risk of mishandling sensitive data. It is also essential to recognize the importance of accuracy in dissemination instructions, which underscores the importance of accurately identifying the information that requires protection.
Conclusion
Understanding the responsibility for applying Controlled Unclassified Information (CUI) markings is crucial for organizations managing sensitive data. This responsibility is shared among key stakeholders, including:
- Information owners
- Designating officials
- Program managers
- IT teams
Each group plays a vital role in ensuring compliance and security. By clearly defining these roles and implementing robust protocols, organizations can effectively manage CUI and safeguard sensitive information.
The article underscores the significance of accurate CUI labeling, outlining the necessary steps for proper application and the potential challenges organizations may encounter. Essential insights include:
- The importance of training staff
- Conducting regular audits
- Adhering to established guidelines to address common issues such as missing or incorrect indicators
These measures not only enhance compliance but also cultivate a culture of data protection within the organization.
Ultimately, effective CUI management transcends mere regulatory compliance; it is a fundamental aspect of an organization’s security framework. By prioritizing clarity in responsibilities and following best practices, organizations can significantly mitigate the risk of mishandling sensitive information. Adopting these strategies empowers entities to protect their data and uphold trust in their operations.
Frequently Asked Questions
What is Controlled Unclassified Information (CUI)?
Controlled Unclassified Information (CUI) is defined as sensitive yet unclassified material that requires safeguarding or dissemination controls mandated by law, regulation, or government-wide policy.
Why is understanding CUI important?
Understanding CUI is crucial for compliance with federal regulations, especially for entities that handle government contracts or sensitive information. It helps organizations protect sensitive data and maintain a strong security posture.
What types of data are considered CUI?
CUI encompasses various data types, including personally identifiable information (PII), proprietary business details, and sensitive operational content.
What percentage of organizations are aware of CUI requirements as of 2026?
As of 2026, approximately 70% of organizations reported awareness of CUI requirements, indicating a growing recognition of its importance within cybersecurity frameworks.
What is the significance of establishing a culture of data protection regarding CUI?
Establishing a culture of data protection is essential for organizations to be well-versed in CUI categories and the specific protocols for marking and handling this information, which aids in compliance and proactive data safeguarding.
What are the reporting obligations for contractors regarding CUI incidents?
Contractors are required to report any suspected or confirmed CUI incidents within eight hours of discovery, which is a critical obligation that organizations must prioritize.
List of Sources
- Understand Controlled Unclassified Information (CUI)
- mxdusa.org (https://mxdusa.org/news/taking-the-mystery-out-of-controlled-unclassified-information-cui)
- hklaw.com (https://hklaw.com/en/insights/publications/2026/03/gsas-new-cui-security-requirements-what-government-contractors)
- DOD Is Finally Leaning Into CMMC 2.0 Requirements for CUI (https://fedtechmagazine.com/article/2026/03/dod-finally-leaning-cmmc-20-requirements-cui)
- Proposed Rule Would Impose Government-Wide Controlled Unclassified Information (CUI) Handling Requirements – ConsensusDocs (https://consensusdocs.org/news/proposed-rule-would-impose-government-wide-controlled-unclassified-information-cui-handling-requirements)
- New GSA Guidance on Protecting CUI in Contractor Systems, Plus a Look Ahead at Pending FAR Changes | JD Supra (https://jdsupra.com/legalnews/new-gsa-guidance-on-protecting-cui-in-2838068)
- Identify Responsible Parties for CUI Markings
- Who Can Decontrol Controlled Unclassified Information? Understanding the Authority Behind CUI – The Computer Company (https://computercompany.net/who-can-decontrol-controlled-unclassified-information-understanding-the-authority-behind-cui)
- Who is Responsible for Applying CUI Markings? | Workstreet (https://workstreet.com/blog/who-is-responsible-for-applying-cui-markings)
- Who Is Responsible For CUI (Controlled Unclassified Information)? (https://exostar.com/blog/cmmc-compliance/who-is-responsible-for-cui-controlled-unclassified-information)
- New GSA Guidance on Protecting CUI in Contractor Systems, Plus a Look Ahead at Pending FAR Changes (https://natlawreview.com/article/new-gsa-guidance-protecting-cui-contractor-systems-plus-look-ahead-pending-far)
- Apply CUI Markings in Dissemination Instructions
- Controlled Unclassified Information (CUI) Program Frequently Asked Questions (FAQs) | US EPA (https://epa.gov/cui/controlled-unclassified-information-cui-program-frequently-asked-questions-faqs)
- cozen.com (https://cozen.com/news-resources/publications/2025/far-proposed-controlled-unclassified-information-rule-a-path-toward-standardization)
- Management Advisory: DoD Policy and Training on Dissemination Controls for Controlled Uncl (https://dodig.mil/Reports/Audits-and-Evaluations/Article/4397146/management-advisory-dod-policy-and-training-on-dissemination-controls-for-contr)
- CUI 101: Controlled Unclassified Information markings refresher (https://dla.mil/About-DLA/News/News-Article-View/Article/4022931/cui-101-controlled-unclassified-information-markings-refresher)
- How to Mark Controlled Unclassified Information (CUI) (https://totem.tech/how-to-mark-controlled-unclassified-information-cui-2)
- Troubleshoot Common Issues with CUI Markings
- Dealing With Unmarked and Mismarked CUI (https://trustedsec.com/blog/dealing-with-unmarked-and-mismarked-cui)
- Is CUI Really Being Overmarked or Is There Just More CUI Than Everyone Expected? | Jacob Horne | 56 comments (https://bm.linkedin.com/posts/jacob-evan-horne_is-cui-really-being-overmarked-or-is-there-activity-7033796761231982592-WtbL)
- New GSA Guidance on Protecting CUI in Contractor Systems, Plus a Look Ahead at Pending FAR Changes (https://natlawreview.com/article/new-gsa-guidance-protecting-cui-contractor-systems-plus-look-ahead-pending-far)
- Management Advisory: DoD Policy and Training on Dissemination Controls for Controlled Uncl (https://dodig.mil/Reports/Audits-and-Evaluations/Article/4397146/management-advisory-dod-policy-and-training-on-dissemination-controls-for-contr)