Introduction
In today’s digital landscape, where cyber threats are pervasive and can disrupt operations in an instant, crafting a robust security incident response plan is not just a luxury; it is a necessity. This article outlines a structured approach to developing a NIST-compliant response plan, guiding organizations through the essential phases of:
- Preparation
- Detection
- Containment
- Recovery
The challenge, however, lies in ensuring that incident response strategies are not only effective but also adaptable to the ever-evolving threat landscape.
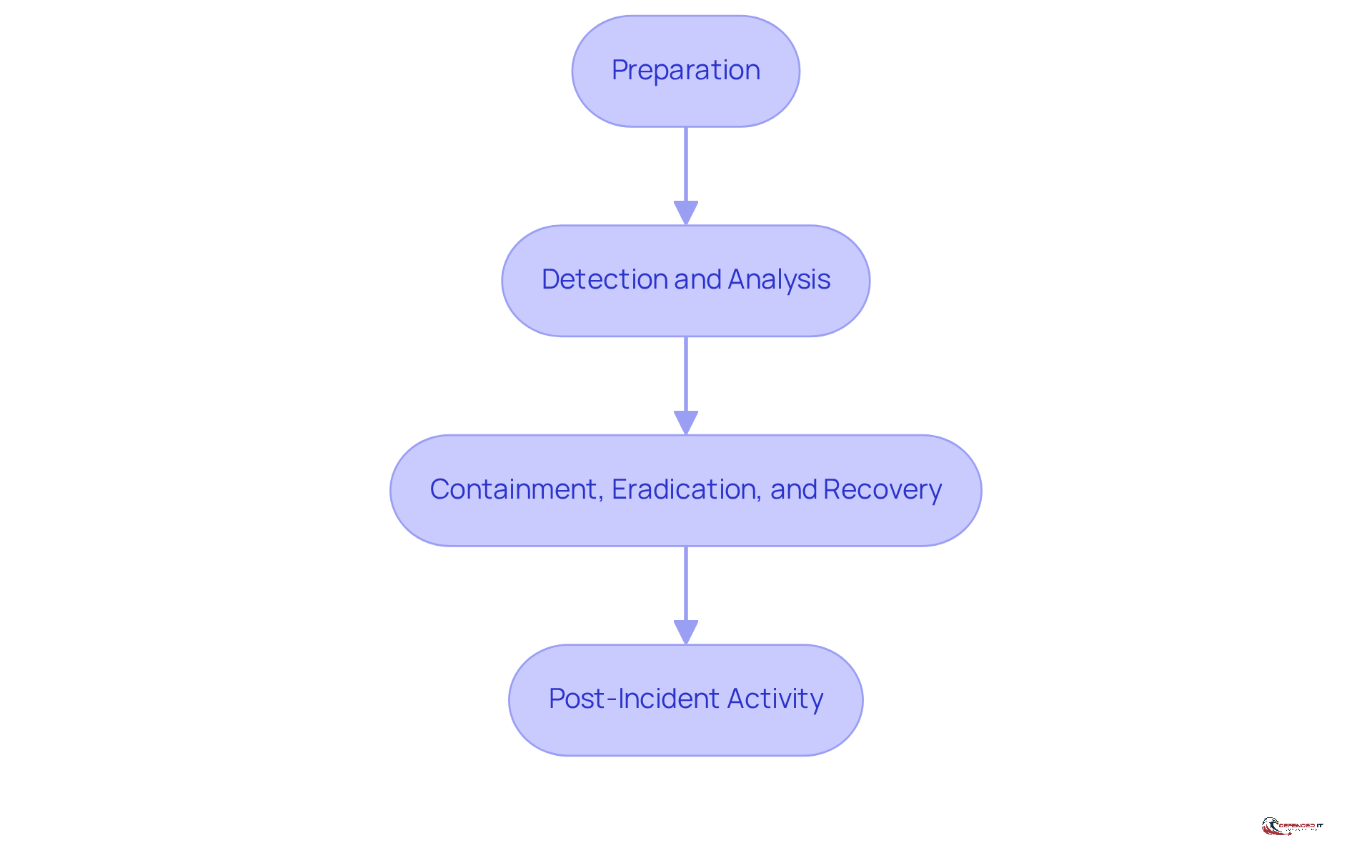
Understand the NIST Incident Response Framework
The NIST Incident Response Framework, as detailed in the guidelines, comprises four essential phases: Preparation, Detection and Analysis, Containment, Eradication, and Recovery, and Post-Incident Review. Understanding these phases is vital for crafting an effective incident response plan. Each phase has a distinct purpose:
- Preparation: This involves forming and training a response team, developing policies, and ensuring that necessary tools are readily available.
- Detection and Analysis: This phase focuses on identifying potential incidents through vigilant monitoring and thorough examination of security events.
- Containment, Eradication, and Recovery: Here, actions are taken to mitigate the impact of an incident, eliminate threats, and restore systems to their normal operational state.
- Post-Incident Review: This final phase entails analyzing the incident to extract insights and improve future responses.
Familiarizing yourself with the framework provides a structured approach to effectively managing security incidents.
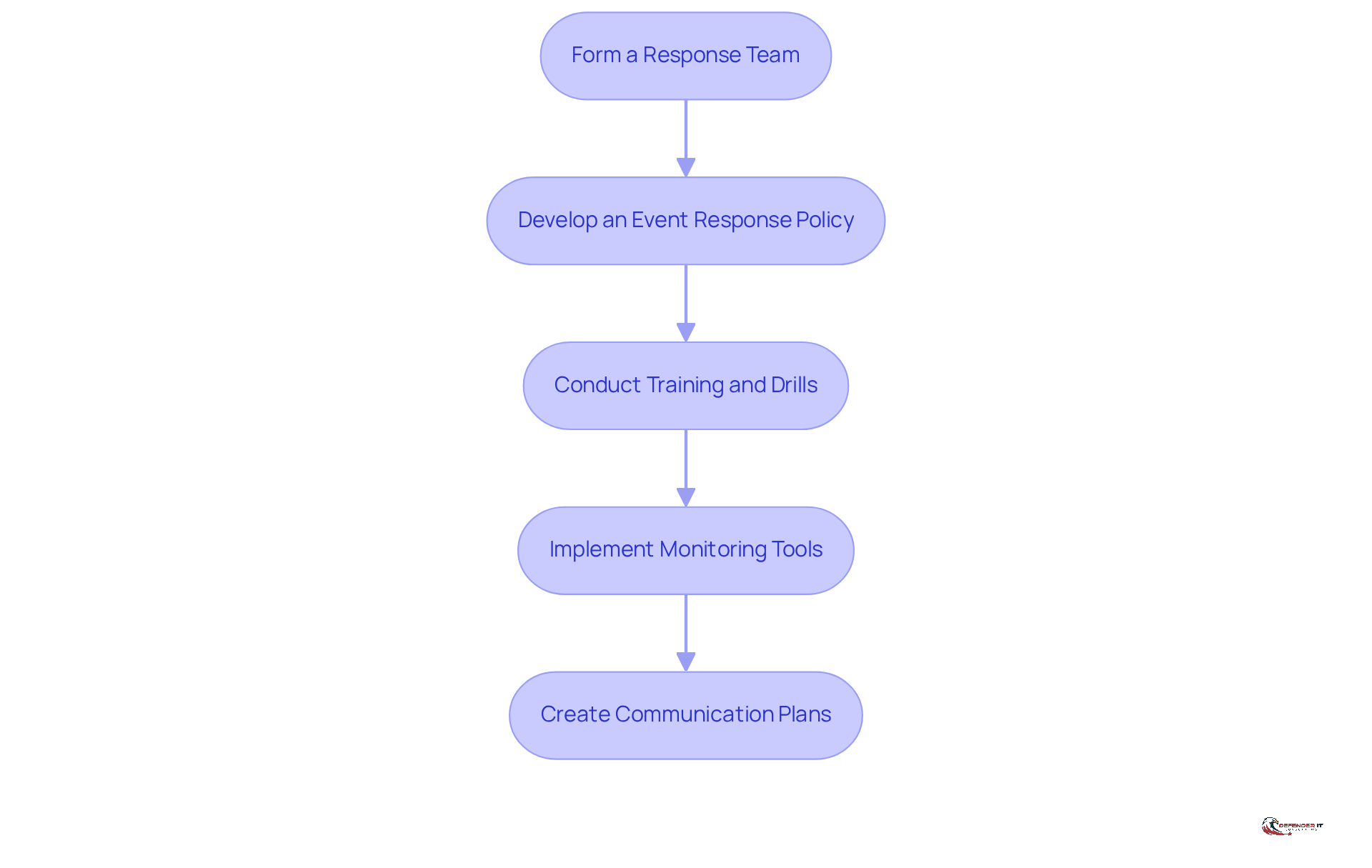
Prepare Your Organization for Incident Response
To effectively prepare your organization for incident response, consider the following essential steps:
- Form a team: Appoint a dedicated group responsible for managing incidents. Clearly define roles and responsibilities to ensure efficient coordination during a crisis. As noted, “Without predefined responsibilities, even a minor security event can spiral into a major crisis due to miscommunication or duplicated efforts.” Organizations with a clear structure can restore operations swiftly, minimizing disruption.
- Develop an incident response plan: Create a formal policy that outlines procedures for identifying, reporting, and addressing incidents. This policy should be regularly reviewed and updated to reflect evolving threats and organizational changes. Notably, 45% of organizations currently possess a formal plan, and 88% of those with plans also have cyber insurance, underscoring the necessity of having a strategy in cybersecurity.
- Conduct training: Regularly educate your team on emergency procedures and conduct drills to ensure preparedness. Ongoing training is crucial, as entities that engage in regular simulations can significantly enhance their response time. For instance, a mid-sized financial firm improved its reaction time by 40% after implementing monthly drills.
- Implement monitoring: Utilize security information and event management (SIEM) tools to monitor systems for suspicious activity. Efficient oversight is vital, as 65% of organizations neither record events nor maintain logs for more than 30 days, which hinders effective event detection and management. Keeping an up-to-date system inventory is essential for event detection and response.
- Create communication strategies: Develop internal and external communication strategies to ensure timely information sharing during an incident. Delays in communication can lead to reputational damage and regulatory penalties, making predefined communication channels essential.
By taking these preparatory measures, your organization will be better equipped to manage incidents promptly and efficiently, ultimately enhancing your overall security posture.
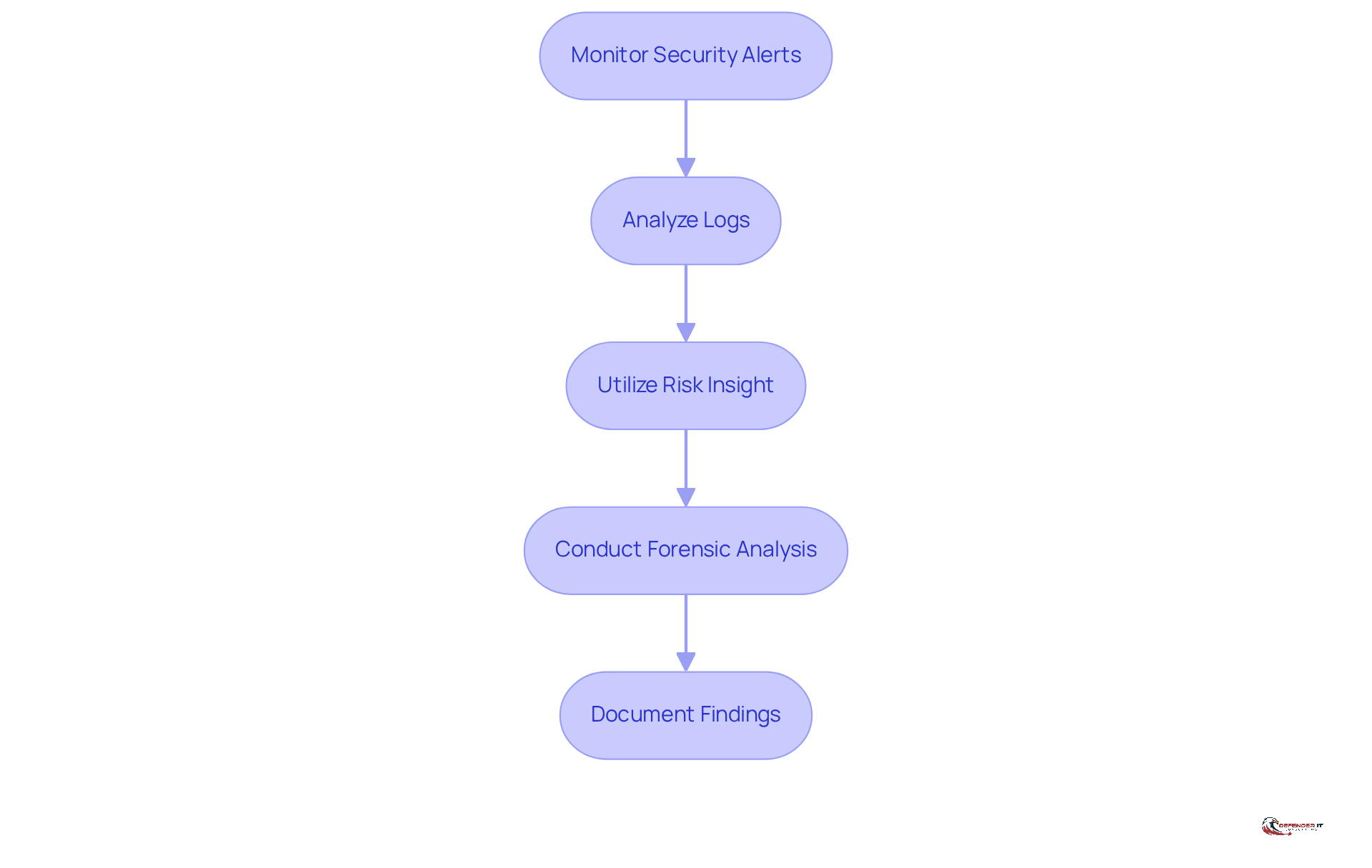
Detect and Analyze Security Incidents
To effectively detect and analyze security incidents, organizations should implement the following steps:
- Monitor Alerts: Regularly review alerts generated by security tools to identify potential incidents. Given that 61% of entities report delays in danger detection,
- Analyze Logs: Examine system and application logs for unusual activity that may indicate a security breach. Efficient log analysis can uncover trends that assist in recognizing dangers early.
- Utilize Risk Insight: Leverage risk intelligence to stay informed about emerging threats relevant to your organization. In 2026, the significance of risk intelligence is underscored by the fact that 91% of organizations with over 100,000 employees have adjusted their strategies due to changing risks. As noted by industry experts, this information is crucial.
- Conduct Investigation: If an incident is suspected, perform a thorough investigation to understand the nature and scope of the event. This step is vital for determining the impact and preventing future occurrences.
- Document Findings: Maintain comprehensive records of all findings during the detection and analysis phase to guide future actions and enhancements. Documentation plays a key role in refining response strategies and enhancing overall effectiveness.
By applying these detection and analysis strategies in accordance with the NIST framework, entities can significantly improve their capacity to recognize and react to security incidents swiftly, ultimately decreasing the average dwell time for threats, which currently stands at 24 days. Furthermore, it is critical to recognize that, on average, it takes 212 days to identify a breach, emphasizing the urgency of these strategies.
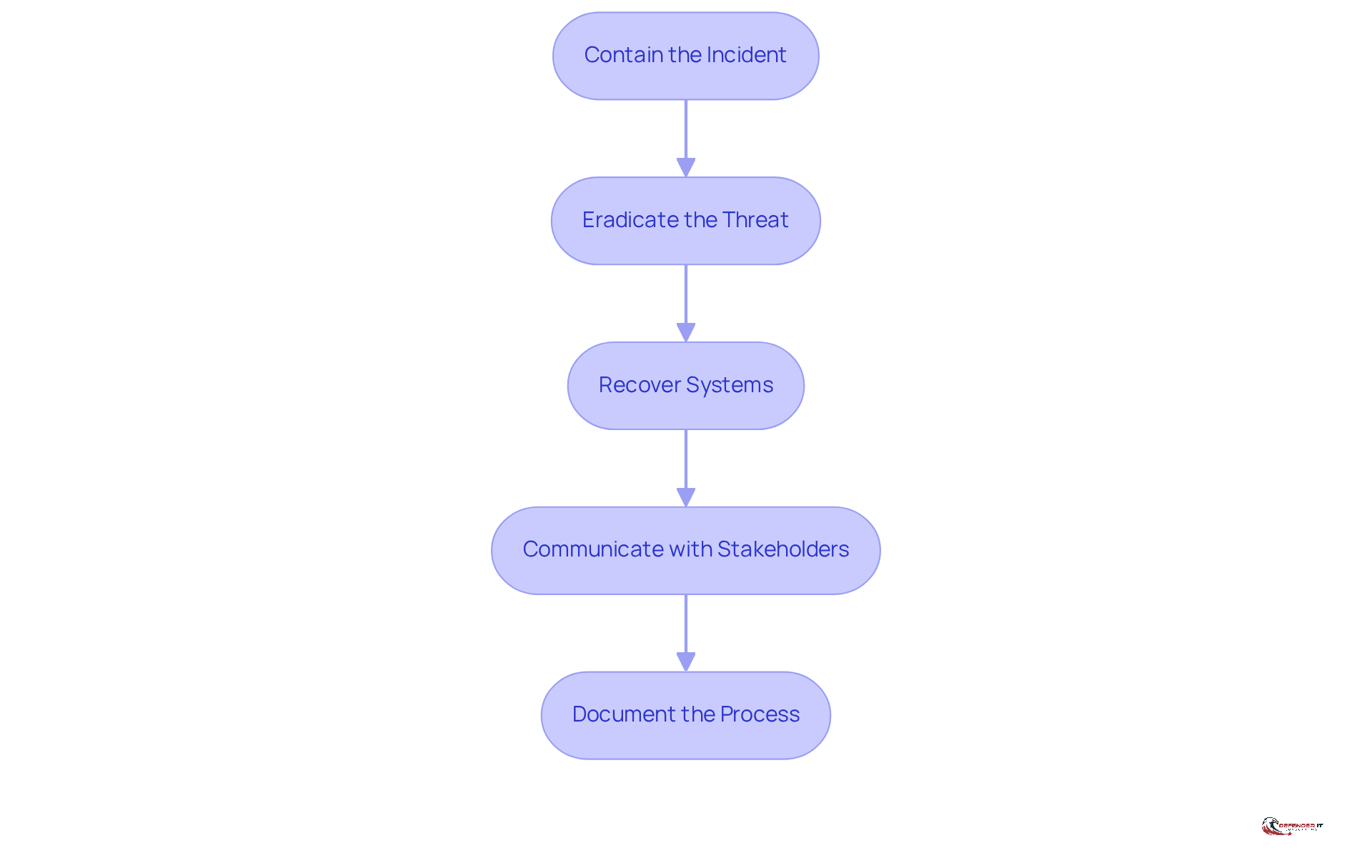
Contain, Eradicate, and Recover from Incidents
To effectively manage incidents, organizations should follow these essential steps:
- Contain the Incident: Implement immediate measures to limit the spread of the incident, such as isolating affected systems. This initial response is crucial to prevent further damage and loss.
- Eradicate the Threat: Thoroughly remove malicious software or unauthorized access points from your systems. This step is essential to ensure that the danger is completely eliminated, preventing recurrence. Regular audits of access rights and enforcing the principle of least privilege can significantly reduce insider threats.
- Recover Systems: Restore systems from clean backups, ensuring that all vulnerabilities are patched before bringing systems back online. Statistics indicate that organizations utilizing best practices can achieve a recovery success rate exceeding 90%, significantly reducing downtime and operational impact. According to the University of Maryland, 90% of all breaches result from human error, underscoring the importance of training.
- Communicate with Stakeholders: Maintain transparent communication with relevant stakeholders regarding the status of the situation and recovery efforts. Effective communication fosters trust and ensures that all parties are informed of the situation and any necessary actions.
- Document the Process: Record all actions taken during containment and recovery for future reference and improvement. Documentation not only assists in compliance but also enhances the entity’s capacity to learn from events and improve their strategies for addressing them. Organizations that frequently conduct tabletop drills to simulate crisis management report a 30% improvement in their ability to handle actual emergencies efficiently.
By adhering to these steps, organizations can effectively manage incidents, minimizing their impact on operations and enhancing overall resilience against future threats.
Conduct Post-Incident Review and Improvement
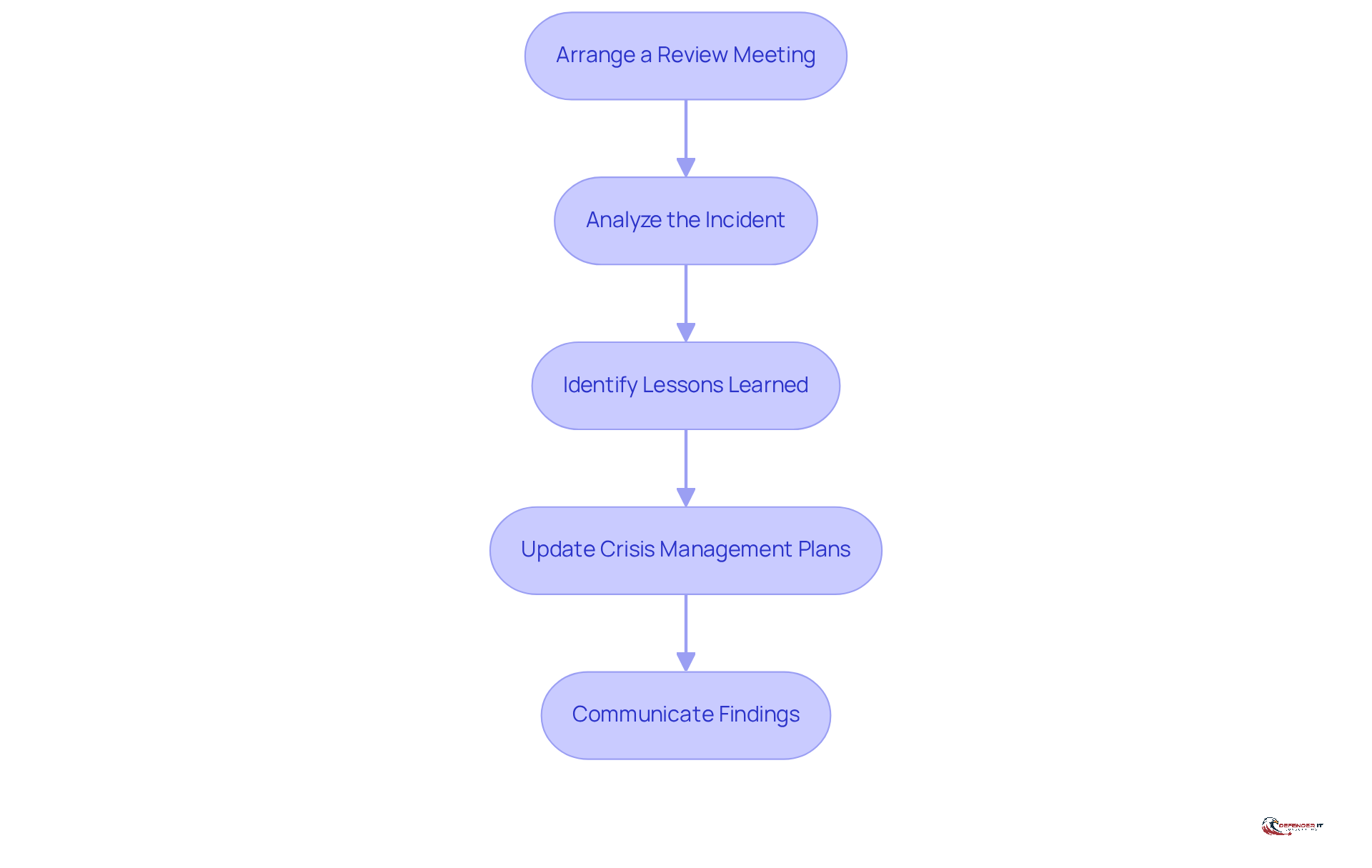
To effectively conduct a review and drive improvement, follow these essential steps:
- Arrange a Review Meeting: Gather the team along with essential stakeholders to discuss the occurrence in detail. Ideally, this meeting should take place within seven days of the event’s conclusion.
- Analyze the Incident: Examine the timeline of events, actions taken, and outcomes to pinpoint what was effective and what fell short. Research indicates that the typical duration to identify a breach is 197 days, underscoring the importance of prompt action.
- Identify Insights: Document essential insights and areas for improvement to enhance future event management efforts. Notably, studies show that 45% of companies revise their strategies after such evaluations, highlighting the significance of this action. For instance, a case study on organizations that engage in structured reviews reveals they can identify previously invisible risks, allowing them to close gaps in their security posture.
- Update Policies: Revise your policies and procedures based on the findings from the review to ensure they reflect the current landscape. Significantly, only 45% of organizations currently possess a response plan, indicating a considerable deficiency in readiness.
- Communicate Findings: Share the findings throughout the organization to cultivate a culture of awareness and vigilance. As Colin Low, an Independent Board Director, states, “If risk isn’t on the board calendar, it won’t get the attention it deserves.”
Conducting comprehensive reviews not only enhances response capabilities but also prepares organizations for future challenges. By fostering a proactive approach, entities can significantly mitigate the impact of future incidents.
Conclusion
Creating a robust NIST Security Incident Response Plan is essential for organizations aiming to effectively manage cybersecurity threats. By understanding the structured phases of the NIST Incident Response Framework – Preparation, Detection and Analysis, Containment, Eradication, Recovery, and Post-Incident Activity – organizations can proactively address potential incidents and minimize their impact.
Key steps include:
- Forming a dedicated response team
- Developing comprehensive policies
- Conducting regular training and drills
- Implementing monitoring tools
- Establishing clear communication channels
Thorough detection and analysis techniques, such as log examination and risk intelligence, significantly enhance an organization’s ability to identify and respond to security incidents swiftly. The processes of containment, eradication, and recovery are equally critical, ensuring that threats are neutralized and systems are restored efficiently. Conducting thorough post-incident reviews fosters a culture of continuous improvement, allowing organizations to learn from experiences and refine their strategies.
Ultimately, investing in a well-structured NIST Security Incident Response Plan not only fortifies an organization’s cybersecurity posture but also prepares it to navigate future challenges with confidence. Proactive measures and ongoing evaluations are crucial in creating a resilient defense against the evolving landscape of cyber threats. Organizations are encouraged to prioritize these practices to safeguard their assets and maintain trust in an increasingly digital world.
Frequently Asked Questions
What is the NIST Incident Response Framework?
The NIST Incident Response Framework, detailed in NIST SP 800-61, consists of four essential phases: Preparation, Detection and Analysis, Containment, Eradication, and Recovery, and Post-Incident Activity. Each phase serves a distinct purpose in managing cybersecurity incidents effectively.
What are the phases of the NIST Incident Response Framework?
The phases are:
- Preparation: Forming and training a response team, developing policies, and ensuring necessary tools are available.
- Detection and Analysis: Identifying potential incidents through monitoring and examination of security events.
- Containment, Eradication, and Recovery: Mitigating the impact of an incident, eliminating threats, and restoring systems.
- Post-Incident Activity: Analyzing the incident to gain insights and improve future responses.
How can an organization prepare for incident response?
Organizations can prepare by:
- Forming a dedicated response team with clearly defined roles.
- Developing a formal event response policy that outlines incident procedures.
- Conducting regular training and drills to enhance preparedness.
- Implementing monitoring tools like SIEM for suspicious activity oversight.
- Creating communication plans for timely information sharing during incidents.
Why is it important to have a response team in place?
A response team is crucial as it ensures efficient coordination during a crisis. Clearly defined roles prevent miscommunication and duplicated efforts, allowing for swift restoration of operations and minimizing disruption.
What should be included in an event response policy?
An event response policy should outline procedures for identifying, reporting, and addressing incidents. It should be regularly reviewed and updated to reflect evolving threats and changes within the organization.
How does training and conducting drills impact incident response?
Regular training and drills significantly enhance a team’s preparedness and response time. For example, a mid-sized financial firm improved its reaction time by 40% after implementing monthly drills.
What role do monitoring tools play in incident response?
Monitoring tools, such as security information and event management (SIEM) systems, are essential for detecting suspicious activity. They enable organizations to maintain oversight and respond effectively to incidents.
Why is communication important during an incident?
Effective communication is vital to ensure timely information sharing, which can prevent reputational damage and regulatory penalties. Predefined communication channels help manage information flow during an incident.
List of Sources
- Understand the NIST Incident Response Framework
- diligent.com (https://diligent.com/resources/blog/top-20-quotes-cyber-risk-virtual-summit)
- deliberatedirections.com (https://deliberatedirections.com/cybersecurity-quotes)
- Cybersecurity Quotes That Define the Future of Digital Protection (https://medium.com/@cyberpromagazine/cybersecurity-quotes-that-define-the-future-of-digital-protection-64897c07bfc6)
- Understanding the NIST Incident Response Guide (Updated for 2025) (https://drata.com/blog/nist-incident-response-guide)
- NIST Cybersecurity Framework Case Study: Learn 5 Best Practices (https://blog.charlesit.com/nist-cybersecurity-framework-case-study-learn-5-best-practices)
- Prepare Your Organization for Incident Response
- frsecure.com (https://frsecure.com/blog/incident-response-statistics-how-do-you-compare)
- Top 10 Incident Management Best Practices For IT Teams 2026 (https://cyble.com/knowledge-hub/top-10-incident-management-best-practices)
- cisa.gov (https://cisa.gov/news-events/news/cisa-urges-critical-infrastructure-organizations-take-action-against-insider-threats)
- 12 Incident Management Statistics to Keep in Mind For 2025 (https://blog.invgate.com/incident-management-statistics)
- Detect and Analyze Security Incidents
- 4 Data Security Incidents to Know About (February 2026) (https://securitymagazine.com/articles/102149-4-data-security-incidents-to-know-about-february-2026)
- 5 cybersecurity trends to watch in 2026 (https://cybersecuritydive.com/news/5-cybersecurity-trends-2026/810354)
- SOC Efficiency Stats: How Fast Do Teams Detect & Respond? (https://patentpc.com/blog/soc-efficiency-stats-how-fast-do-teams-detect-respond)
- Cyber threats to watch in 2026 – and other cybersecurity news (https://weforum.org/stories/2026/02/2026-cyberthreats-to-watch-and-other-cybersecurity-news)
- Cyber Security Best Practices for 2026 (https://sentinelone.com/cybersecurity-101/cybersecurity/cyber-security-best-practices)
- Contain, Eradicate, and Recover from Incidents
- surtech.co.za (https://surtech.co.za/20-expert-quotes-on-cyber-risk-and-security)
- 4 Data Security Incidents to Know About (February 2026) (https://securitymagazine.com/articles/102149-4-data-security-incidents-to-know-about-february-2026)
- Cyber threats to watch in 2026 – and other cybersecurity news (https://weforum.org/stories/2026/02/2026-cyberthreats-to-watch-and-other-cybersecurity-news)
- sentinelone.com (https://sentinelone.com/cybersecurity-101/cybersecurity/cyber-security-statistics)
- secureframe.com (https://secureframe.com/blog/data-breach-statistics)
- Conduct Post-Incident Review and Improvement
- frsecure.com (https://frsecure.com/blog/incident-response-statistics-how-do-you-compare)
- surtech.co.za (https://surtech.co.za/20-expert-quotes-on-cyber-risk-and-security)
- Post-incident review: Boost Your Cybersecurity Resilience (https://cdg.io/blog/post-incident-review)
- diligent.com (https://diligent.com/resources/blog/top-20-quotes-cyber-risk-virtual-summit)