Introduction
Mastering penetration testing is crucial for organizations seeking to strengthen their cybersecurity defenses. By simulating cyber attacks, penetration testing reveals vulnerabilities that malicious actors could exploit, offering organizations critical insights into their security posture. Given the rapid evolution of cyber threats, businesses must effectively navigate the five essential phases of penetration testing to achieve optimal security. This article outlines the necessary steps in this process, providing a roadmap for organizations to enhance their cybersecurity strategies and safeguard against emerging threats.
Understand Penetration Testing and Its Importance
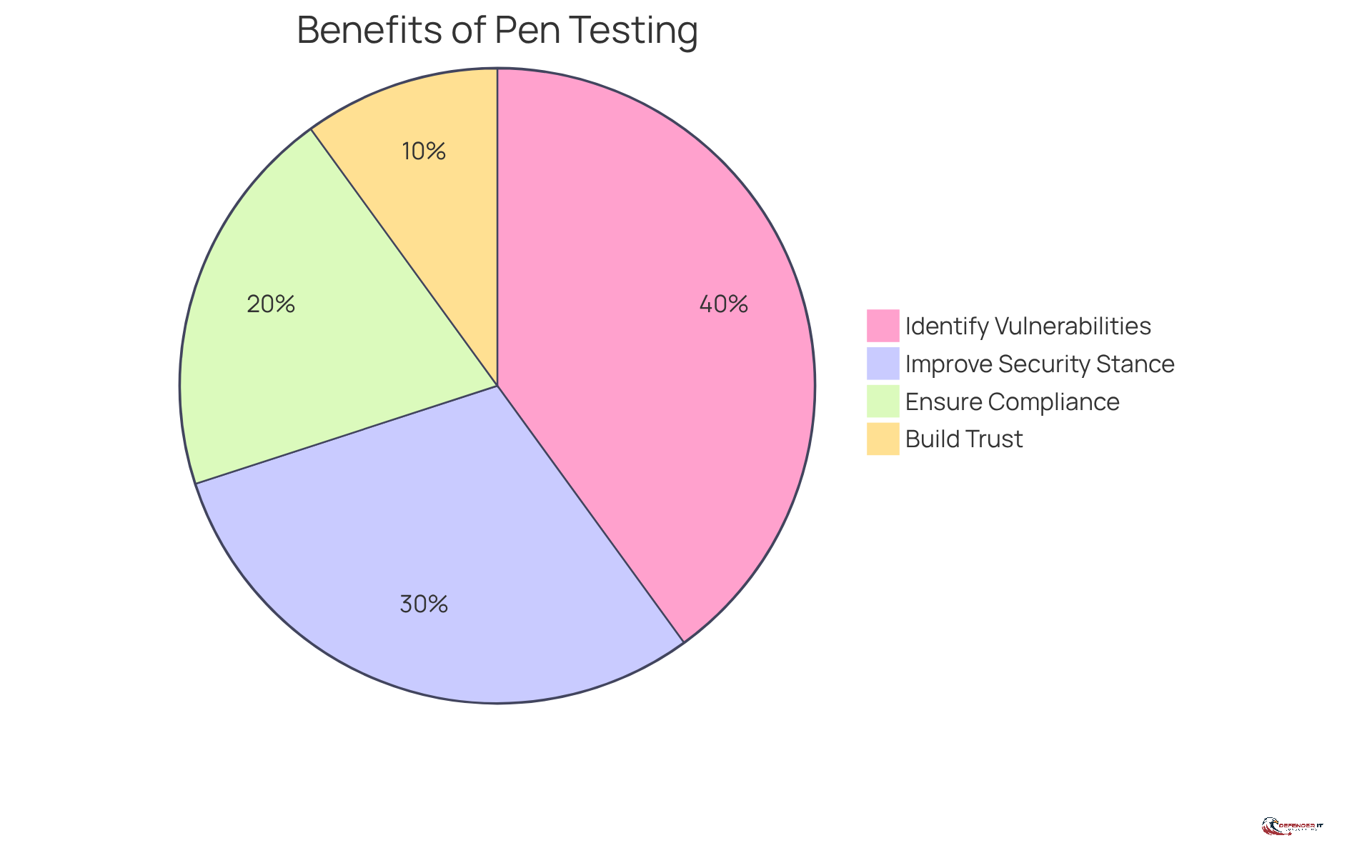
Penetration assessment, commonly known as ‘pen testing’, simulates cyber attacks on computer systems to identify exploitable vulnerabilities. This practice is crucial for a robust , enabling organizations to proactively discover weaknesses before malicious actors can exploit them. The significance of is highlighted by several key benefits:
- : Regular penetration tests uncover security gaps that could be targeted by attackers. In fact, 66% of firms reported that ethical hackers effectively detected over 65,000 flaws in 2021 alone, marking a 21% increase in legitimate issues compared to the previous year.
- : By addressing recognized weaknesses, organizations can bolster their defenses. A study revealed that businesses conducting red team exercises reduced breach costs by an average of $204,000, underscoring the financial impact of .
- : Many sectors, particularly those in regulated fields, are required to perform regular , including intrusion assessments, to meet compliance standards. Approximately 75% of organizations conduct penetration tests to support their vulnerability management programs, ensuring adherence to regulatory requirements.
- : Demonstrating a commitment to security through consistent evaluations can significantly enhance customer confidence and protect an organization’s reputation. As cyber threats continue to escalate, businesses that prioritize security are more likely to maintain customer trust.
Recent trends indicate a growing interest in , with the global market for these evaluations projected to increase from $1.6 billion in 2021 to $3.0 billion by 2026. This growth reflects a heightened awareness of among organizations, particularly in response to rising cyber threats. By acknowledging the importance of security assessments, organizations can effectively master its phases and ensure cybersecurity success.
Conduct Reconnaissance and Planning
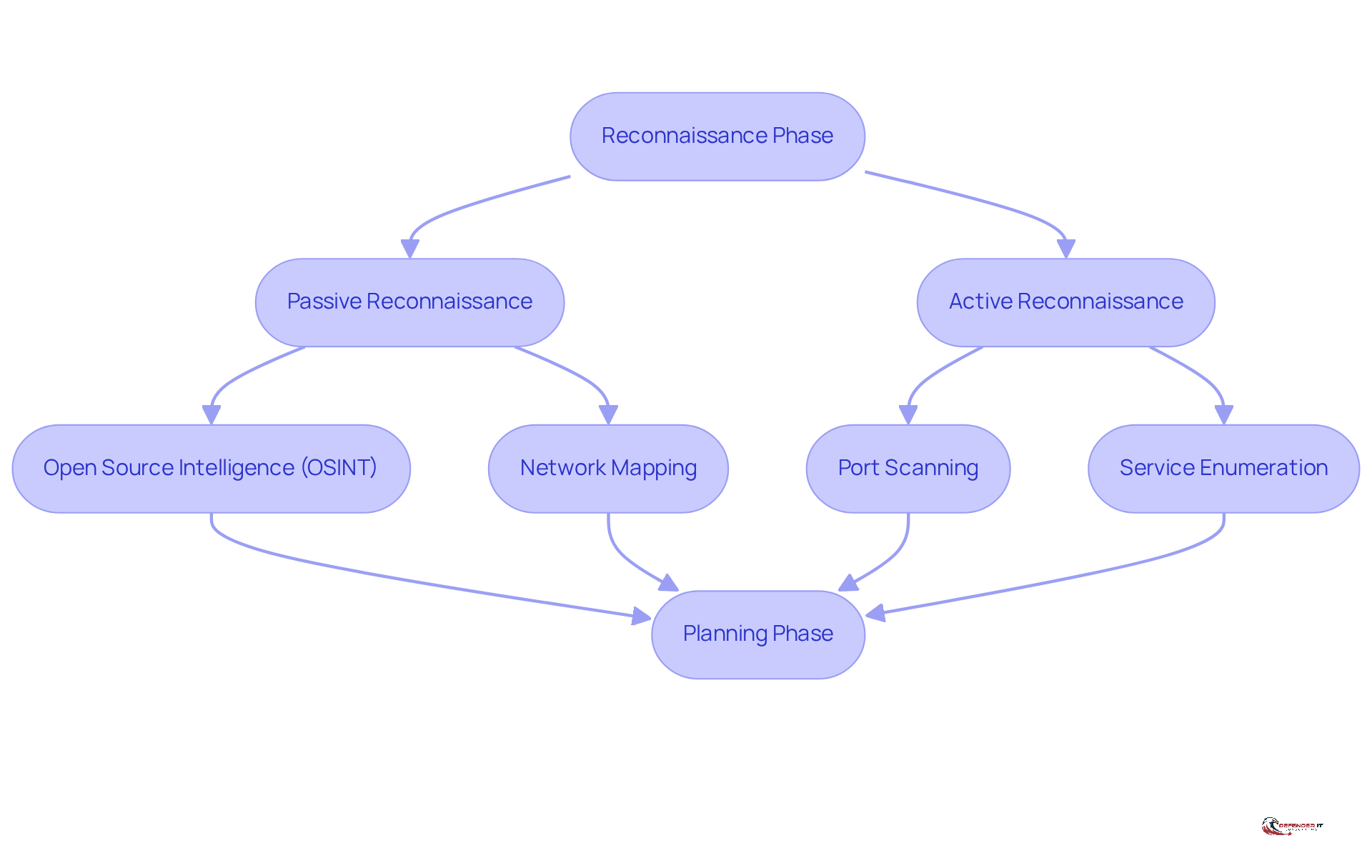
The reconnaissance phase serves as the foundational step in security testing, focusing on the about the target system. This phase is divided into two primary types: passive and active reconnaissance.
-
Passive Reconnaissance: This method entails collecting information without direct interaction with the target, thereby minimizing the risk of detection. Techniques include:
- : Utilizing publicly available resources such as social media, company websites, and domain registration details to gather insights about the target.
- Network Mapping: Employing tools like Nmap, which is utilized by 72% of penetration testers, to identify the network structure and potential entry points, facilitating a clearer understanding of the target’s environment.
-
Active Reconnaissance: Conversely, this approach involves direct interaction with the target to extract information. Techniques include:
- : Identifying open ports and the services running on the target system, which can expose potential vulnerabilities.
- : Determining the versions of services in operation to identify specific vulnerabilities that could be exploited.
Planning: Following the information-gathering process, it is essential to that outlines the scope of the . This plan should detail which systems will be tested, the methods to be employed, and the . A structured approach not only ensures that the testing is focused and efficient but also aligns with best practices in , thereby enhancing the overall effectiveness of the process. Cybersecurity professionals emphasize that for addressing operational scalability issues and ensuring that findings lead to actionable results.
Execute Scanning and Vulnerability Assessment
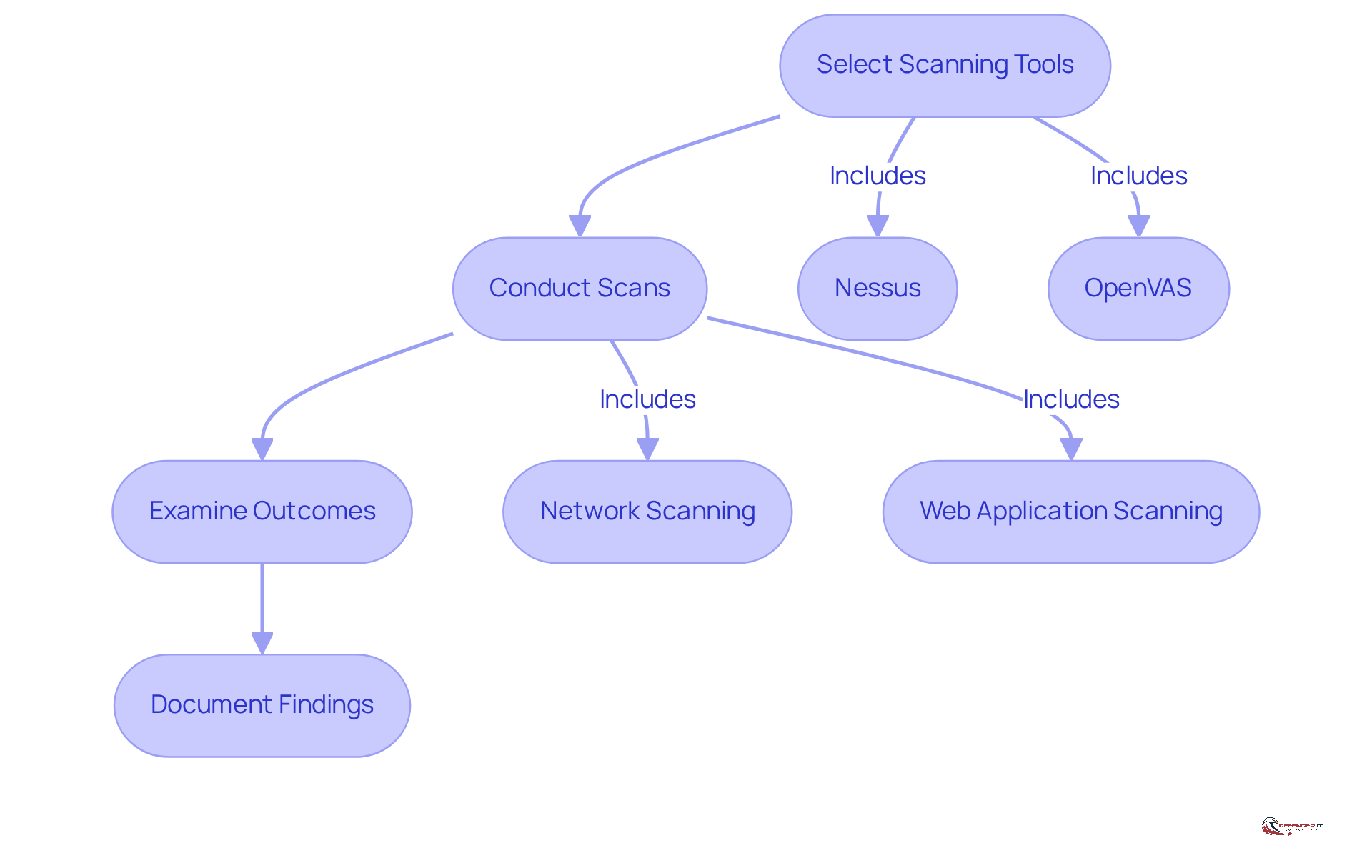
After the reconnaissance phase of , the next essential step is conducting scanning and threat assessment. This phase of penetration testing employs to uncover weaknesses within target systems. Here’s how to proceed effectively:
-
Select : Choose appropriate tools for scanning, such as:
- Nessus: A leading recognized for its ability to identify vulnerabilities across systems and applications.
- OpenVAS: An open-source solution providing extensive security flaw scanning capabilities.
-
Conduct Scans: Execute scans on the identified systems to reveal weaknesses. Focus on:
- Network Scanning: Identify live hosts, open ports, and the services operating on those ports.
- : Utilize tools like Burp Suite to in web applications, including SQL injection and cross-site scripting (XSS).
-
Examine Outcomes: After scanning, assess the results to identify crucial weaknesses. Prioritize these based on their severity and potential impact on the organization. Notably, 4.6% of weaknesses in web applications are categorized as critical, and 84% of businesses possess high-risk issues, half of which could be addressed with straightforward updates. This underscores the need for thorough analysis.
-
: Maintain comprehensive records of all identified weaknesses, detailing their descriptions, potential impacts, and recommended remediation steps. This documentation is essential for monitoring weaknesses and ensuring prompt resolution, as 60% of . Furthermore, 80% of organizations fail to tackle new issues within the first 1.5 years following the initial scan, emphasizing the necessity of effective . As stated by the National Vulnerability Database, ” before the corresponding CVEs are released,” reinforcing the necessity for proactive measures.
Perform Exploitation of Vulnerabilities
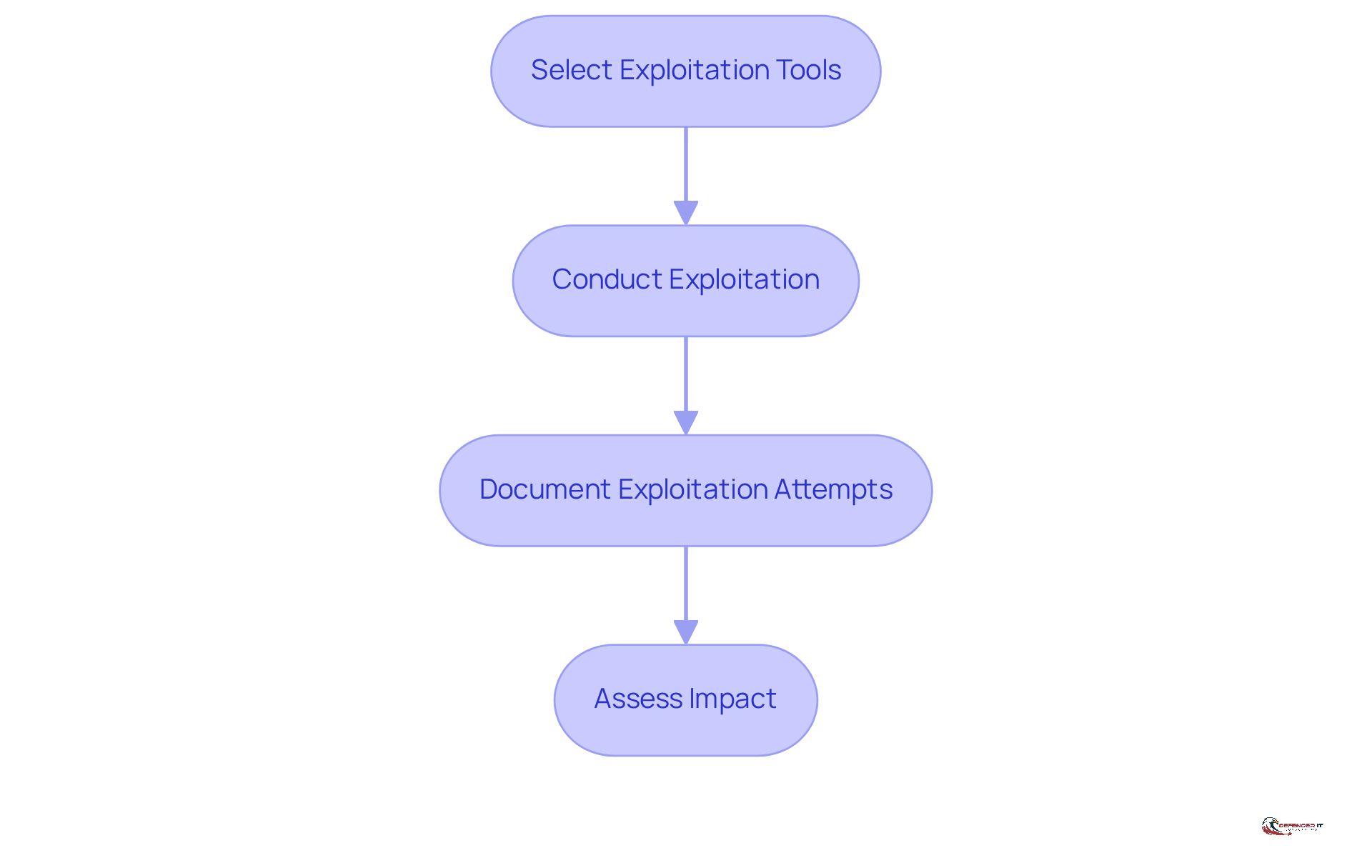
In the exploitation phase, organizations actively utilize identified weaknesses to . This phase of is critical for effectively understanding and mitigating risks. Here’s how to conduct this phase:
-
Select : Choose advanced tools such as:
- Metasploit Framework: A robust platform that enables penetration testers to exploit vulnerabilities and simulate real-world attack scenarios.
- Burp Suite: An essential tool for exploiting web application weaknesses, allowing thorough testing of security measures.
-
Conduct Exploitation: Execute exploitation attempts in a controlled environment, focusing on:
- : Leverage vulnerabilities to gain unauthorized access to systems or sensitive data, demonstrating potential risks. Notably, 84% of companies possess high-risk weaknesses on their perimeter devices and software, underscoring the urgency of addressing these issues during the phase of penetration testing.
- Privilege Escalation: After gaining access, attempt to elevate privileges to achieve higher-level access, illustrating the extent of the weaknesses.
-
: Meticulously record all exploitation attempts, noting both successful and unsuccessful efforts. This documentation is vital for the final report and informs remediation strategies, ensuring that all findings are actionable. It is significant to note that 73% of flaws are closed or remediated between the first and last scan conducted by entities, highlighting the importance of thorough documentation.
-
Assess Impact: Evaluate the potential consequences of the exploited weaknesses on the organization, including . Understanding these impacts is crucial in the phase of penetration testing for and enhancing overall . With 60% of data breaches attributed to the failure to apply available patches, the implications of exploited vulnerabilities are substantial.
By systematically addressing these steps, organizations can gain valuable insights into their security weaknesses and take informed actions to mitigate risks effectively.
Compile Reporting and Remediation Strategies
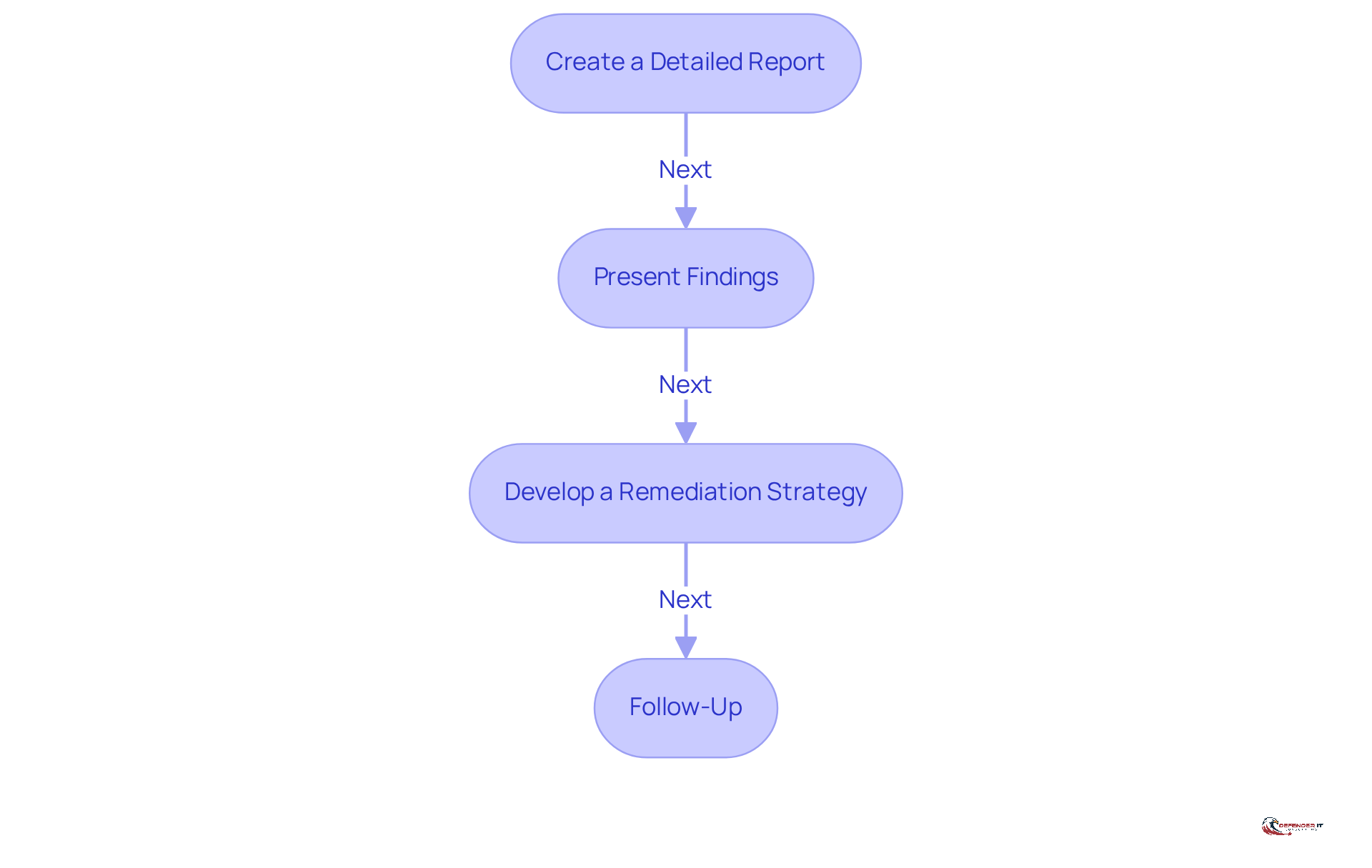
The critical phase of involves compiling a and developing effective . Here’s how to approach this phase:
-
Create a Detailed Report: The report should encompass the following elements:
- : This section provides a high-level overview of findings and recommendations tailored for decision-makers.
- Technical Details: Include comprehensive information regarding , exploitation attempts, and their potential impacts on the organization.
- : Offer , which may include patching, configuration changes, and policy updates.
-
Present Findings: It is essential to schedule a meeting with stakeholders to present the findings and discuss their implications for the entity’s .
-
: Collaborate with IT and security teams to formulate a remediation plan that prioritizes weaknesses based on their severity and potential impact. Ensure that the plan outlines timelines and assigns responsible parties for each action item.
-
Follow-Up: After remediation efforts, conduct follow-up assessments to verify that vulnerabilities have been effectively addressed and that the organization’s security posture has improved.
Conclusion
Mastering the five phases of penetration testing is crucial for organizations seeking to strengthen their cybersecurity posture. By systematically identifying and addressing vulnerabilities, businesses can proactively protect their systems from potential threats. This comprehensive approach not only mitigates risks but also fortifies the overall security framework, ensuring that organizations are well-equipped to confront evolving cyber challenges.
The article explored key aspects of penetration testing, emphasizing the importance of understanding the process, the necessity of thorough reconnaissance and planning, the execution of scanning and vulnerability assessments, the critical phase of exploitation, and the final steps of reporting and remediation. Each phase is integral to developing a robust security strategy, enabling organizations to identify weaknesses before they can be exploited by malicious actors.
Embracing these practices transcends technical necessity; it represents a strategic imperative in today’s digital landscape. Organizations are urged to prioritize penetration testing within their cybersecurity initiatives. By doing so, they not only comply with regulatory requirements but also cultivate customer trust and confidence. Investing in these assessments today will yield significant returns in safeguarding valuable assets and maintaining a resilient security posture against future threats.
Frequently Asked Questions
What is penetration testing?
Penetration testing, or ‘pen testing’, simulates cyber attacks on computer systems to identify exploitable vulnerabilities, playing a crucial role in a robust cybersecurity strategy.
Why is penetration testing important?
It helps organizations proactively discover weaknesses before they can be exploited by malicious actors, ensuring stronger security measures and compliance with regulations.
What are the key benefits of penetration testing?
Key benefits include identifying vulnerabilities, improving security stance, ensuring compliance with regulations, and building trust with customers.
How do penetration tests help identify vulnerabilities?
Regular penetration tests uncover security gaps; for instance, 66% of firms reported that ethical hackers detected over 65,000 flaws in 2021, marking a significant increase in identified issues.
How does penetration testing improve an organization’s security stance?
Addressing recognized weaknesses from penetration tests can bolster defenses, potentially reducing breach costs significantly; businesses conducting red team exercises saw an average reduction of $204,000 in breach costs.
What role does penetration testing play in compliance?
Many regulated sectors require regular security evaluations, including penetration tests, to meet compliance standards. Approximately 75% of organizations conduct these tests to support their vulnerability management programs.
How does penetration testing build trust with customers?
Demonstrating a commitment to security through consistent evaluations enhances customer confidence and protects an organization’s reputation, which is vital in an era of escalating cyber threats.
What is the projected growth of the penetration testing market?
The global market for security assessments is projected to grow from $1.6 billion in 2021 to $3.0 billion by 2026, reflecting increased awareness of cybersecurity needs.
What is the reconnaissance phase in penetration testing?
The reconnaissance phase involves gathering comprehensive information about the target system and is divided into passive and active reconnaissance.
What is passive reconnaissance?
Passive reconnaissance involves collecting information without direct interaction with the target, using techniques like Open Source Intelligence (OSINT) and network mapping.
What is active reconnaissance?
Active reconnaissance involves direct interaction with the target to extract information, utilizing techniques such as port scanning and service enumeration.
Why is planning important in penetration testing?
Developing a comprehensive plan after information gathering is essential to outline the scope of the assessment, ensuring focused and efficient testing that aligns with best practices in cybersecurity.