Introduction
As cyber threats evolve, organizations face increasing pressure to safeguard their data, making network vulnerability assessments more critical than ever. These assessments serve as a proactive measure to identify and mitigate weaknesses within an organization’s infrastructure, protecting valuable data against emerging cyber threats. Yet, many professionals find it challenging to navigate the complexities of network vulnerability assessments, prompting the question: how can one master this essential skill? This guide outlines the essential steps, tools, and strategies necessary for excelling in network vulnerability assessments, enabling organizations to strengthen their defenses and ensure compliance in a dynamic environment.
Understand Network Vulnerability Assessments
A vulnerability assessment (NVA) serves as a critical safeguard against potential cyber threats, identifying weaknesses before they can be exploited. This systematic process identifies, evaluates, and prioritizes vulnerabilities within a system, ensuring organizations can protect their digital assets and comply with industry regulations.
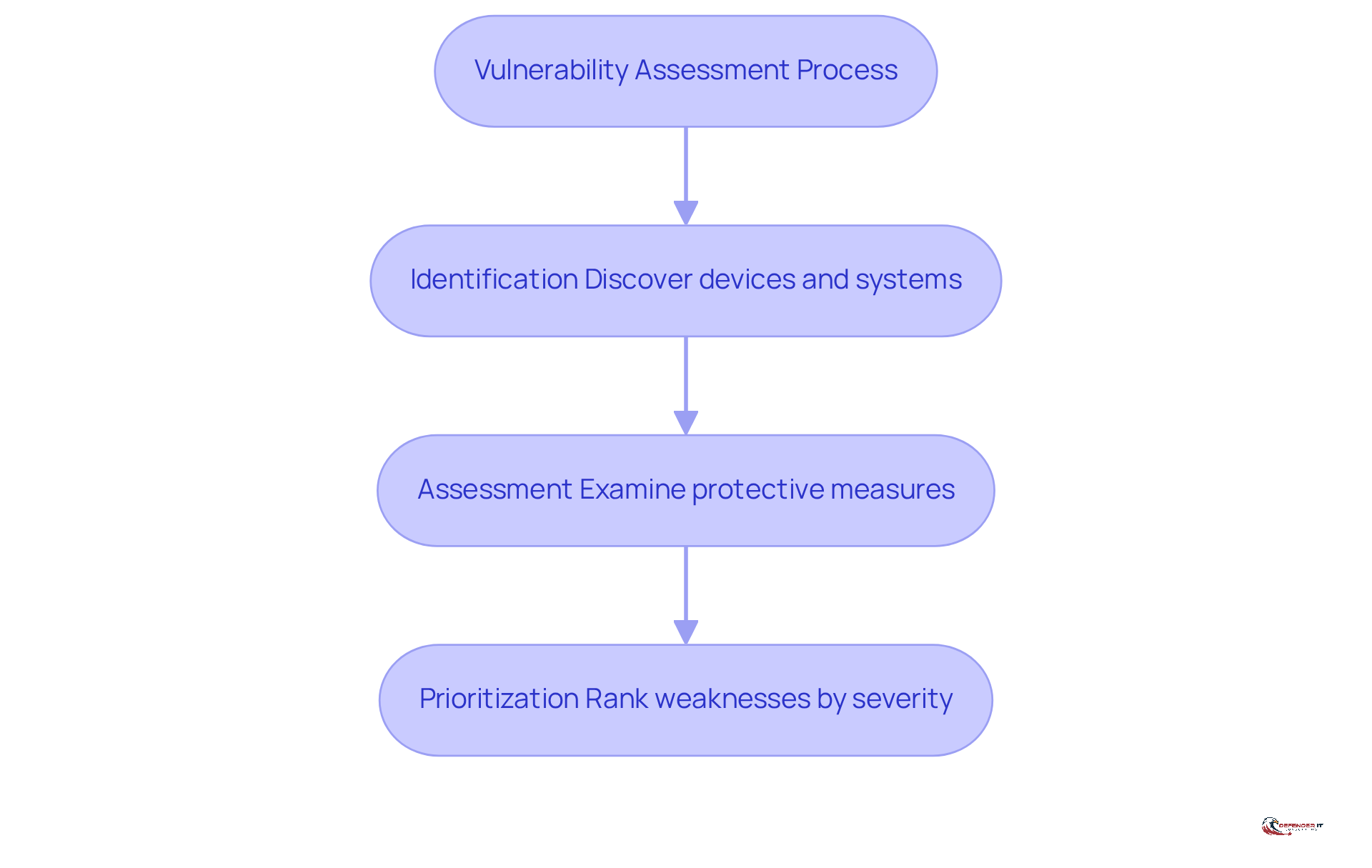
Key Components of a [[[[[Network Vulnerability Assessment](https://defenderit.consulting/master-pen-test-tools-best-practices-for-security-leaders/)](https://defenderit.consulting/master-pen-test-tools-best-practices-for-security-leaders/)](https://defenderit.consulting/master-pen-test-tools-best-practices-for-security-leaders/)](https://defenderit.consulting/master-pen-test-tools-best-practices-for-security-leaders/)](https://defenderit.consulting/master-pen-test-tools-best-practices-for-security-leaders/)
- Identification: Discovering all devices and systems within the network.
- Assessment: Examining the protective stance of these devices to detect possible weaknesses.
- Prioritization: Ranking weaknesses based on their severity and potential impact on the organization.
Importance of Network Vulnerability Assessments
- Proactive Defense: According to Interpol, addressing recognized weaknesses is crucial, as sixty percent of security breaches stem from uncorrected vulnerabilities. By identifying vulnerabilities before they can be exploited, organizations can implement necessary security measures.
- Regulatory Compliance: Industries such as finance and healthcare often mandate regular risk assessments to stay compliant with legal and regulatory standards. This is vital for maintaining operational integrity and avoiding penalties.
- Risk Management: Recognizing weaknesses assists organizations in managing risks efficiently, greatly decreasing the chances of data breaches and related financial losses. In 2025, organizations faced a staggering 48,185 published Common Vulnerabilities and Exposures (CVEs), underscoring the need for continuous vigilance in 2026 as cyber threats evolve.
- Successful Examples: Organizations that have implemented comprehensive NVAs have reported strengthened defenses and improved compliance with industry regulations. For instance, a healthcare organization that performed regular evaluations was able to decrease its mean time to recovery (MTTR) from 44 days to 30 days, showcasing the effectiveness of proactive risk management in enhancing compliance and security stance.
As cyber threats continue to evolve, neglecting vulnerability assessments could expose organizations to unprecedented risks and liabilities.
Conduct a Step-by-Step Network Vulnerability Assessment
To ensure robust cybersecurity, organizations must systematically engage a network vulnerability assessment professional to conduct assessments.
-
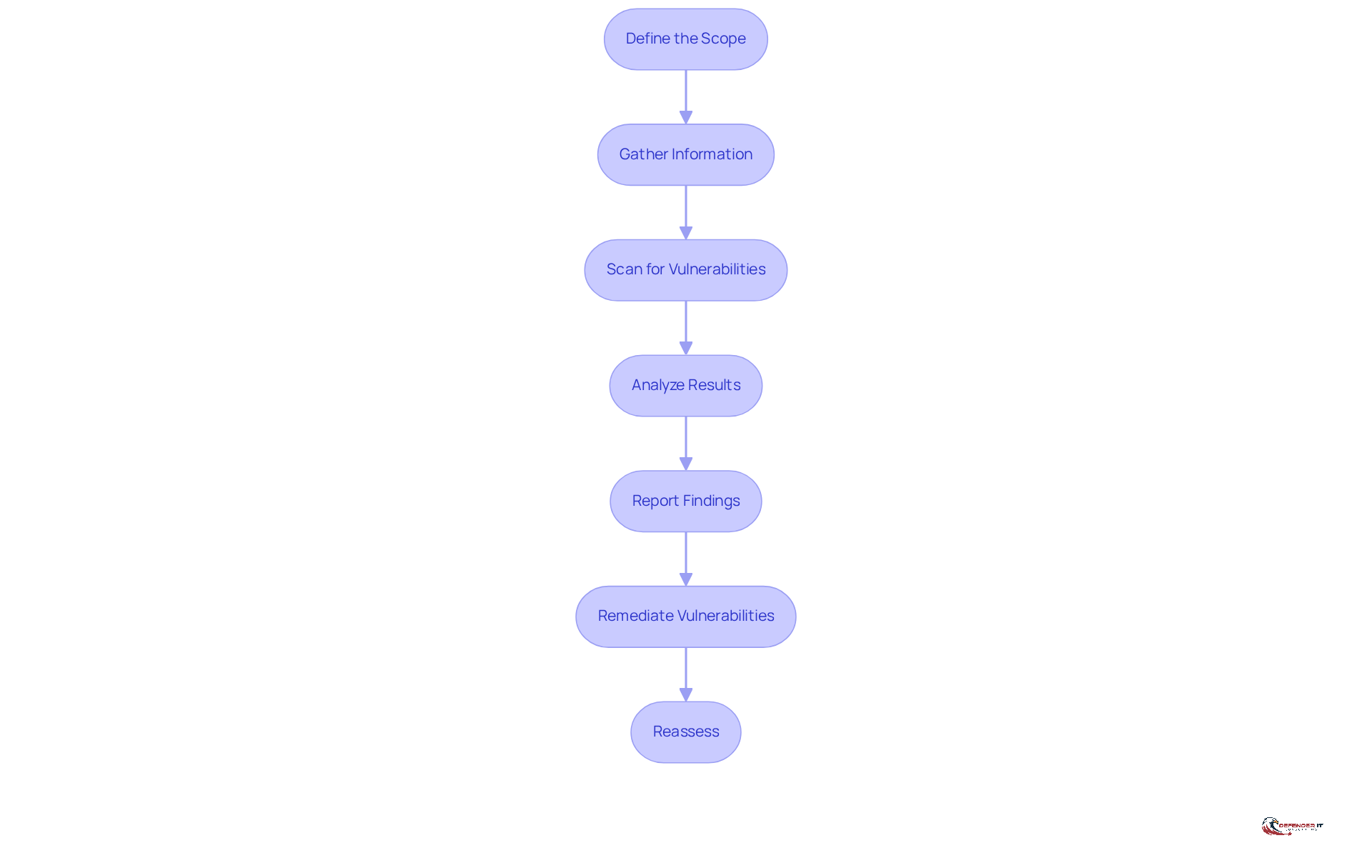
Define the Scope
- Clearly identify which segments of the network will be assessed, focusing on critical assets and sensitive data that require protection.
-
Gather Information
- Collect comprehensive data regarding the network architecture, including IP addresses, operating systems, and applications in use, to understand the environment better.
-
Scan for Vulnerabilities
- Employ automated tools such as Nessus or OpenVAS to perform scans for known vulnerabilities. Significantly, Intruder’s tool scans for over 140,000 recognized flaws, rendering it a strong choice for detecting weaknesses effectively throughout the network.
-
Analyze Results
- Carefully review the scan results to pinpoint vulnerabilities. Categorize these findings based on their severity and potential impact on the organization. The prevalence of attacks highlights the urgent need for consistent vulnerability assessments conducted by a network vulnerability assessment professional, as scanning for and exploiting weaknesses accounted for 26% of attacks in 2022.
-
Report Findings
- Develop a detailed report that outlines the identified vulnerabilities, assesses their potential impact, and provides actionable remediation recommendations.
-
Remediate Vulnerabilities
- Collaborate with IT teams to address the identified vulnerabilities through necessary patches, configuration changes, or other security measures to enhance network security. Risk management must be viewed as a continuous process, essential for maintaining robust cybersecurity.
-
Reassess
- Conduct a follow-up assessment post-remediation to verify that vulnerabilities have been effectively resolved, ensuring ongoing protection against cyber threats. The duration for security scans can range from a few minutes to several hours, depending on the infrastructure being examined.
Routine security evaluations are critical for maintaining a strong cybersecurity posture, enabling organizations to adapt to evolving threats and comply with regulatory standards. Without regular evaluations, organizations risk falling prey to evolving cyber threats that could compromise their integrity and data security.
Utilize Essential Tools and Resources for Assessments
To effectively assess network vulnerabilities, organizations should consider hiring a network vulnerability assessment professional to navigate a landscape of complex tools and varying user experiences.
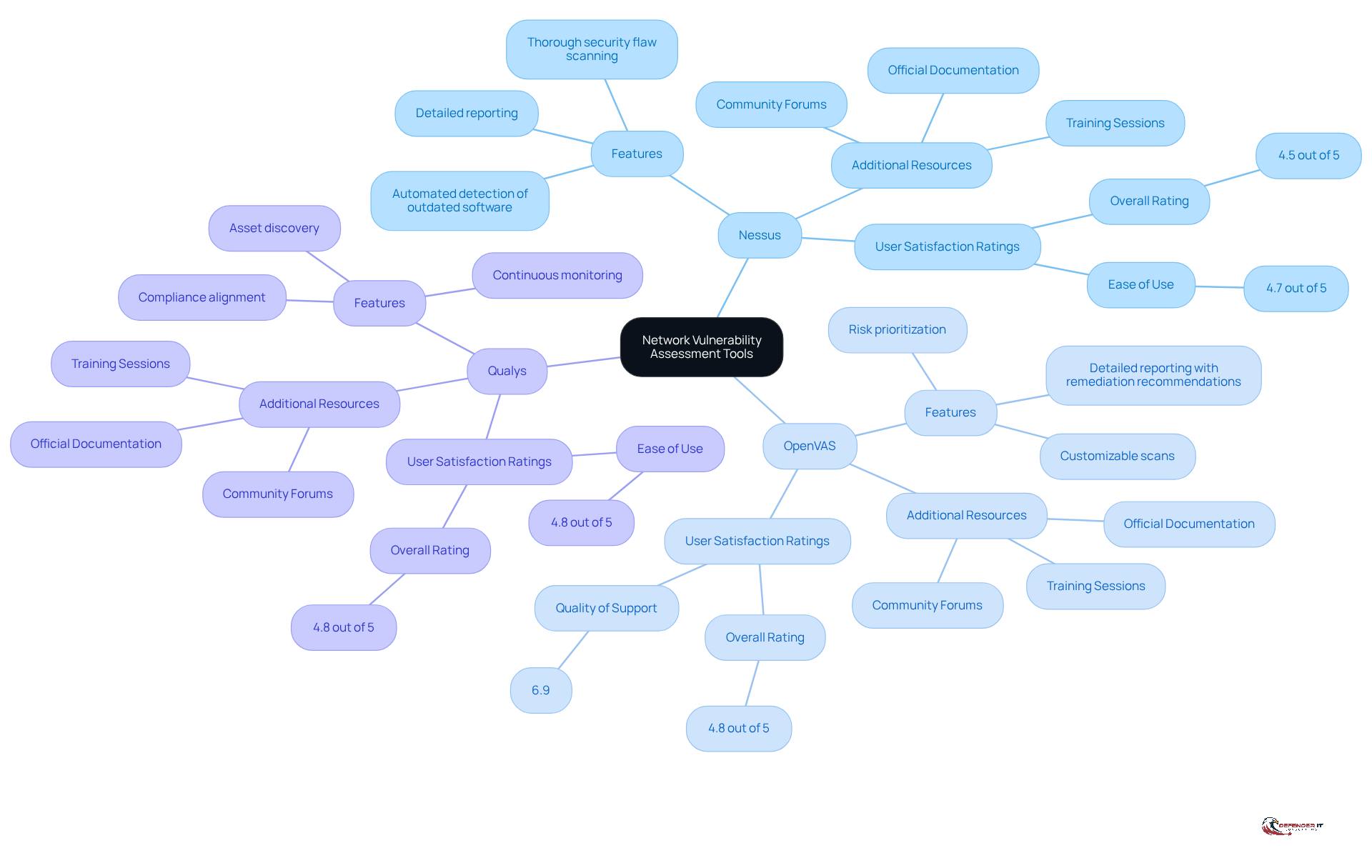
Vulnerability Scanning Tools
- Nessus: A widely used tool recognized for its thorough security flaw scanning capabilities. It automates the detection of outdated software, misconfigurations, and compliance issues, generating detailed reports that assist teams in prioritizing remediation efforts based on severity. Yet, many users find that it comes with a steep learning curve and some performance hiccups.
- OpenVAS: An open-source tool that excels in customizable scans, allowing users to prioritize risks based on severity levels, which enhances its effectiveness in vulnerability assessments. While it offers a free version, new users may find its interface challenging, requiring workarounds for larger scans.
- Qualys: A cloud-based platform that excels in continuous monitoring and risk management. It integrates asset discovery and compliance alignment, making it suitable for organizations in regulated environments. Qualys is acknowledged for its comprehensive security flaw database, although users have reported difficulties with its user interface and customer support response times.
User Satisfaction Ratings
- Nessus: Rated 4.5 out of 5 for ease of use, with users appreciating its comprehensive reporting features.
- OpenVAS: Holds an overall rating of 4.8 out of 5, with a focus on its customizable scanning capabilities, though it has a quality of support rating of 6.9.
- Qualys: Achieves a rating of 4.8 out of 5, recognized for its robust cloud security capabilities but noted for its complex user interface.
Additional Resources
- Documentation: Refer to the official documentation of each tool for best practices and usage guidelines.
- Training: Consider training sessions or certifications to enhance your understanding of these tools.
- Community Forums: Connect with cybersecurity groups for advice and shared experiences concerning security evaluations.
Understanding these tools’ strengths and weaknesses is crucial for optimizing your network vulnerability assessment professional strategy.
Overcome Challenges in Network Vulnerability Assessments
Organizations face significant challenges when evaluating system weaknesses, which can jeopardize their cybersecurity posture. Here are common obstacles and strategies to overcome them:
-
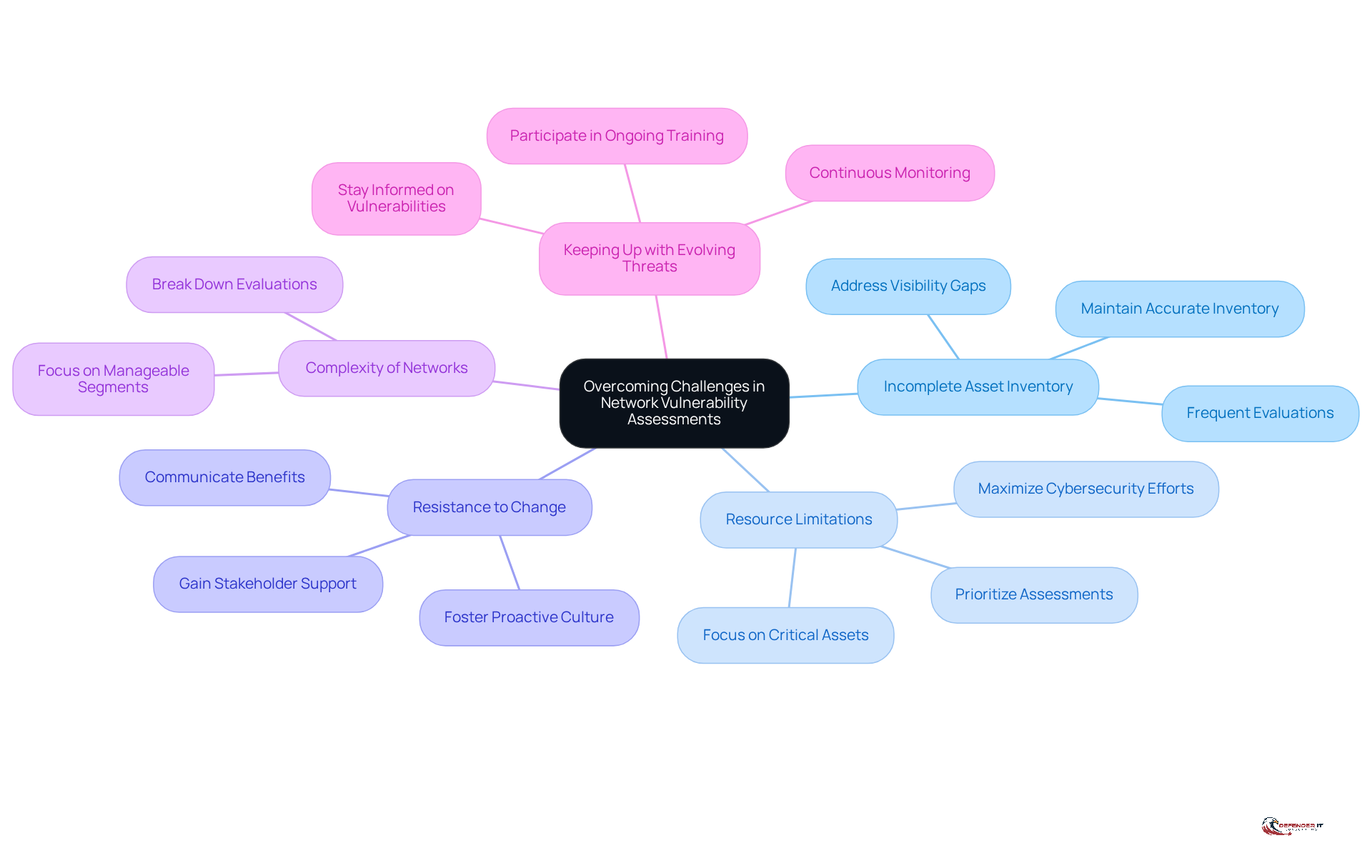
Challenge 1: Incomplete Asset Inventory
- Solution: Maintaining an accurate and up-to-date inventory of all network devices and systems is crucial. Frequent evaluations and modifications ensure that the inventory reflects the current state of the system, which is essential for identifying vulnerabilities. A study found that 71% of security teams reported visibility gaps in their systems, underscoring the need for thorough asset inventories. Organizations that have successfully implemented these inventories report significantly improved visibility into their networks, reducing blind spots that attackers can exploit.
-
Challenge 2: Resource Limitations
- Solution: To address resource constraints, prioritize assessments based on risk and potential impact. Focus on critical assets first, ensuring that limited resources are allocated where they can mitigate the most significant risks. This strategic approach allows organizations to maximize their cybersecurity efforts, especially in environments where resources are stretched thin.
-
Challenge 3: Resistance to Change
- Solution: Gaining stakeholder support is vital for successful vulnerability assessments. It’s important to show stakeholders why these evaluations matter, focusing on benefits like enhanced security and compliance. Engaging stakeholders through clear communication can help overcome resistance and foster a culture of proactive cybersecurity.
-
Challenge 4: Complexity of Networks
- Solution: The complexity of modern networks can be daunting. To simplify the evaluation process, break it down into manageable segments. Focus on one area of the network at a time, which can help streamline the assessment and make it more effective.
-
Challenge 5: Keeping Up with Evolving Threats
- Solution: Staying informed about the latest vulnerabilities and threats is essential for effective cybersecurity. The evolving nature of ransomware attacks, as highlighted by recent incidents like the DaVita ransomware attack that exposed 2.7 million patient records, emphasizes the need for continuous monitoring. Subscribe to reputable cybersecurity news sources and participate in ongoing training to keep skills current. Organizations that actively monitor emerging threats are better positioned to adapt their defenses and respond to incidents swiftly.
Ultimately, addressing these challenges is not just about compliance; it is about safeguarding the organization against evolving threats that could have devastating consequences.
Conclusion
To effectively safeguard against cyber threats, professionals must master network vulnerability assessments. By systematically identifying, evaluating, and prioritizing vulnerabilities, organizations can proactively defend their digital assets and ensure compliance with industry regulations. This approach not only mitigates risks but also enhances the overall cybersecurity posture of organizations, ensuring they are better prepared for future challenges.
The article highlights key components of a network vulnerability assessment, including:
- Identification
- Assessment
- Prioritization of vulnerabilities
It emphasizes the importance of:
- Proactive defense
- Regulatory compliance
- Effective risk management
Successful examples illustrate how regular assessments can lead to improved security and operational efficiency, showcasing the tangible benefits of a robust vulnerability assessment strategy.
In today’s fast-changing cyber landscape, it’s crucial for organizations to prioritize vulnerability assessments to stay ahead of potential threats. By adopting best practices, utilizing essential tools, and addressing common challenges, professionals can significantly enhance their organization’s security framework. Embracing a culture of continuous assessment and improvement is not merely a compliance requirement; it is a vital step in safeguarding sensitive data and maintaining trust in an increasingly digital world.
Frequently Asked Questions
What is a Network Vulnerability Assessment (NVA)?
A Network Vulnerability Assessment (NVA) is a systematic process that identifies, evaluates, and prioritizes vulnerabilities within a system, helping organizations safeguard against potential cyber threats and comply with industry regulations.
What are the key components of a Network Vulnerability Assessment?
The key components include: – Identification: Discovering all devices and systems within the network. – Assessment: Examining the protective stance of these devices to detect possible weaknesses. – Prioritization: Ranking weaknesses based on their severity and potential impact on the organization.
Why are Network Vulnerability Assessments important?
They are important for several reasons: – Proactive Defense: They help address recognized weaknesses, as many security breaches occur from uncorrected vulnerabilities. – Regulatory Compliance: Regular assessments are often mandated in industries like finance and healthcare to maintain compliance with legal standards. – Risk Management: They assist organizations in managing risks efficiently, reducing the chances of data breaches and financial losses.
What statistics highlight the need for continuous vulnerability assessments?
In 2025, organizations faced 48,185 published Common Vulnerabilities and Exposures (CVEs), indicating a growing need for vigilance as cyber threats evolve.
Can you provide an example of a successful Network Vulnerability Assessment?
Yes, a healthcare organization that conducted regular vulnerability evaluations was able to decrease its mean time to recovery (MTTR) from 44 days to 30 days, demonstrating the effectiveness of proactive risk management in enhancing compliance and security.
What risks do organizations face if they neglect vulnerability assessments?
Neglecting vulnerability assessments can expose organizations to unprecedented risks and liabilities, making them vulnerable to cyber threats and potential data breaches.
List of Sources
- Understand Network Vulnerability Assessments
- Cyberattacks target US infrastructure, and other cybersecurity news (https://weforum.org/stories/2026/04/cyberattacks-target-us-infrastructure-cybersecurity-news)
- 35 Cyber Security Vulnerability Statistics, Facts In 2026 (https://getastra.com/blog/security-audit/cyber-security-vulnerability-statistics)
- Ultimate Guide to Vulnerability Assessment: What, Why & How (2026 Edition) (https://acronis.com/en/blog/posts/ultimate-guide-to-vulnerability-assessment-2026)
- Vulnerability Statistics Report (https://edgescan.com/stats-report)
- Network Security Vulnerability Assessment Guide for 2026 (https://ibntech.com/blog/network-security-vulnerability-assessment)
- Conduct a Step-by-Step Network Vulnerability Assessment
- Network Security Vulnerability Assessment Guide for 2026 (https://ibntech.com/blog/network-security-vulnerability-assessment)
- How To Perform A Vulnerability Assessment: Step-by-Step (https://intruder.io/blog/how-to-perform-a-vulnerability-assessment-step-by-step)
- Vulnerability Assessment Methodology: A Step-by-Step Guide 2026 (https://qualysec.com/vulnerability-assessment-methodology)
- Compare 2026 Network Vulnerability Assessment Tools for CISOs – Cygnostic (https://cygnostic.io/compare-2026-network-vulnerability-assessment-tools-for-cisos)
- How to Do a Network Vulnerability Assessment (Step by Step Guide) – Netsurit US (https://netsurit.com/en-us/network-vulnerability-assessment)
- Utilize Essential Tools and Resources for Assessments
- Best Vulnerability Scanning Tools: Top 5 in 2026 (https://ninjaone.com/blog/vulnerability-scanning-tools)
- Best Vulnerability Scanning Tool for 2026- Top 10 List (https://securityboulevard.com/2025/12/best-vulnerability-scanning-tool-for-2026-top-10-list)
- 9 Vulnerability Management Tools in 2026 | SentinelOne (https://sentinelone.com/cybersecurity-101/cybersecurity/8-vulnerability-management-tools)
- 10 Best Vulnerability Scanning Tools in 2026 Ranked (https://invicti.com/blog/web-security/10-best-vulnerability-scanning-tools)
- Must-Have Cybersecurity Tools for 2026 (https://uscsinstitute.org/cybersecurity-insights/blog/must-have-cybersecurity-tools-for-2026)
- Overcome Challenges in Network Vulnerability Assessments
- Top Cybersecurity Challenges to Watch for in 2026 | SWK Technologies (https://swktech.com/top-cybersecurity-challenges-to-watch-for-in-2026)
- 2026 Cyber Risk Management Strategies To Adopt Now (https://forbes.com/councils/forbestechcouncil/2026/03/02/2026-cyber-risk-management-strategies-to-adopt-now)
- 5 Key Enterprise Network Security Challenges Firms Must Address In 2026 | BlackFog (https://blackfog.com/5-key-enterprise-network-security-challenges-2026)
- Navigating the Cyber Threat Landscape: 2026 Outlook and Emerging Risks (https://panorays.com/blog/cyber-threat-landscape-2026-emerging-risks)