Introduction
The digital landscape presents significant risks as cyber threats evolve and grow increasingly sophisticated. Organizations must prioritize network vulnerability assessments to identify and address potential weaknesses that could compromise their security. This guide outlines the essential steps for conducting effective assessments, emphasizing the tools and techniques that can strengthen defenses against complex attacks.
With so much at stake, businesses must ensure they are compliant with emerging regulations while proactively safeguarding their digital assets.
Define Network Vulnerability Assessment
A is a comprehensive procedure designed to discover, assess, and prioritize flaws within a network. This evaluation employs a combination of and to uncover potential vulnerabilities, including outdated software, misconfigured devices, and unpatched systems. Given that it takes over 20 minutes of manual effort to identify, prioritize, and address a single weakness, organizations must adopt a proactive strategy to effectively mitigate risks.
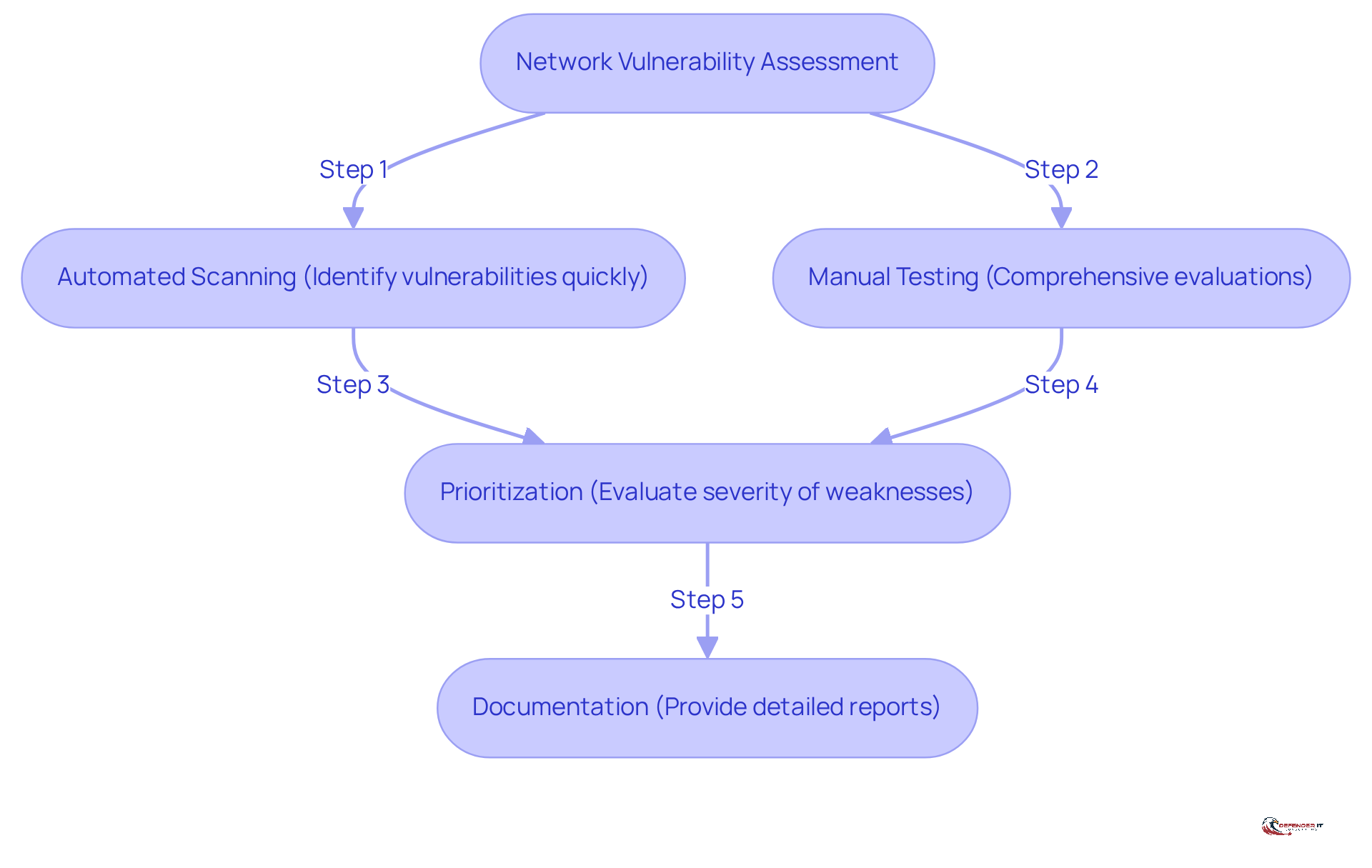
Key components of a include:
- Automated Scanning: Advanced tools are utilized to swiftly identify vulnerabilities across the network.
- : Comprehensive evaluations are performed to ensure that no weaknesses are overlooked, particularly in complex environments.
- Prioritization: The severity of identified weaknesses is evaluated to focus remediation efforts on the most critical issues.
- Documentation: A detailed report is provided, serving as evidence of , which is essential for .
In 2026, the significance of network weakness evaluations will be amplified by new global data privacy regulations, which will impose stricter penalties for non-compliance. Organizations that do not maintain adequate audit trails and oversight may face substantial . Real-world examples underscore this urgency; for instance, firms that conducted regular risk evaluations reported a , thereby enhancing their overall . A report indicates that 60% of small businesses fail within six months of a cyber attack, highlighting the critical need for such evaluations.
As evolve, particularly with the rise of AI-driven attacks, the importance of conducting thorough s cannot be overstated. These evaluations not only help organizations secure their digital assets but also ensure compliance with new regulations, ultimately protecting their reputation and operational integrity.
Outline the Steps for Conducting the Assessment
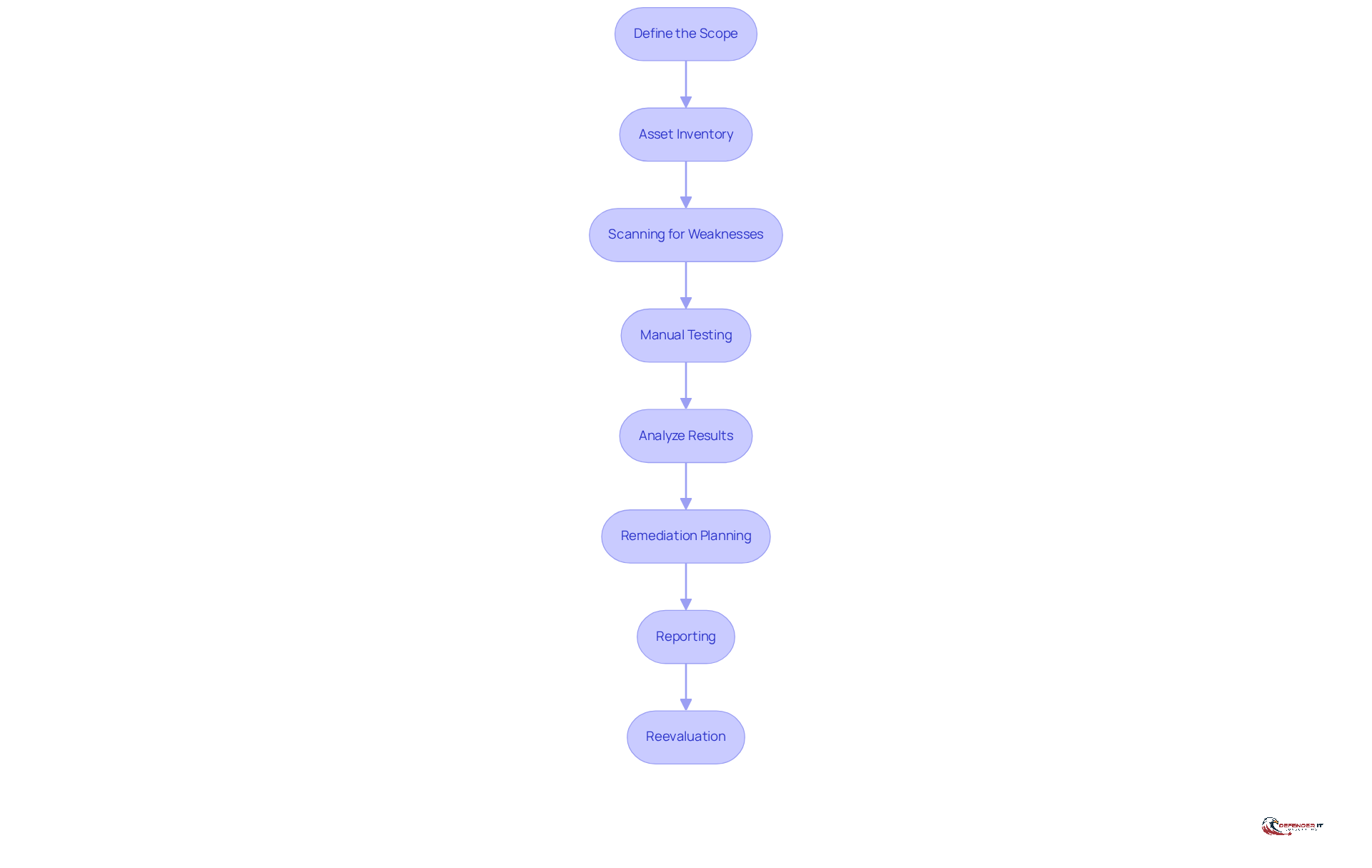
- Define the Scope: Clearly outline which systems, networks, and applications will be part of the evaluation. This focus ensures that critical assets are prioritized, as one in three breaches go undetected, underscoring the necessity for .
- Asset Inventory: Compile a within the defined scope, encompassing hardware, software, and network devices. This step is crucial for understanding the environment and .
- Scanning for Weaknesses: Utilize to conduct scans across the network for identified flaws. These tools effectively identify that could be exploited by attackers, particularly as 75 percent of phishing kits available for sale on the dark web reference AI, making it essential to stay ahead of evolving threats.
- Manual Testing: Enhance automated scans with manual testing to uncover weaknesses that automated tools might overlook, including complex business logic flaws that require human insight. As Cody Chamberlain emphasizes, focusing on the fundamentals is vital in .
- Analyze Results: Evaluate the findings from both automated and manual assessments, prioritizing weaknesses based on their risk levels and potential impact on the organization.
- Remediation Planning: Develop a , specifying timelines and assigning responsibilities for remediation efforts.
- Reporting: Create a , findings, and remediation strategies. This report serves as a crucial communication tool for stakeholders.
- Reevaluation: Establish a schedule for to ensure that new risks are detected and addressed promptly, maintaining a robust . Continuous vigilance is essential, as is a collective responsibility, not solely that of IT.
Identify Tools and Techniques for Effective Assessment
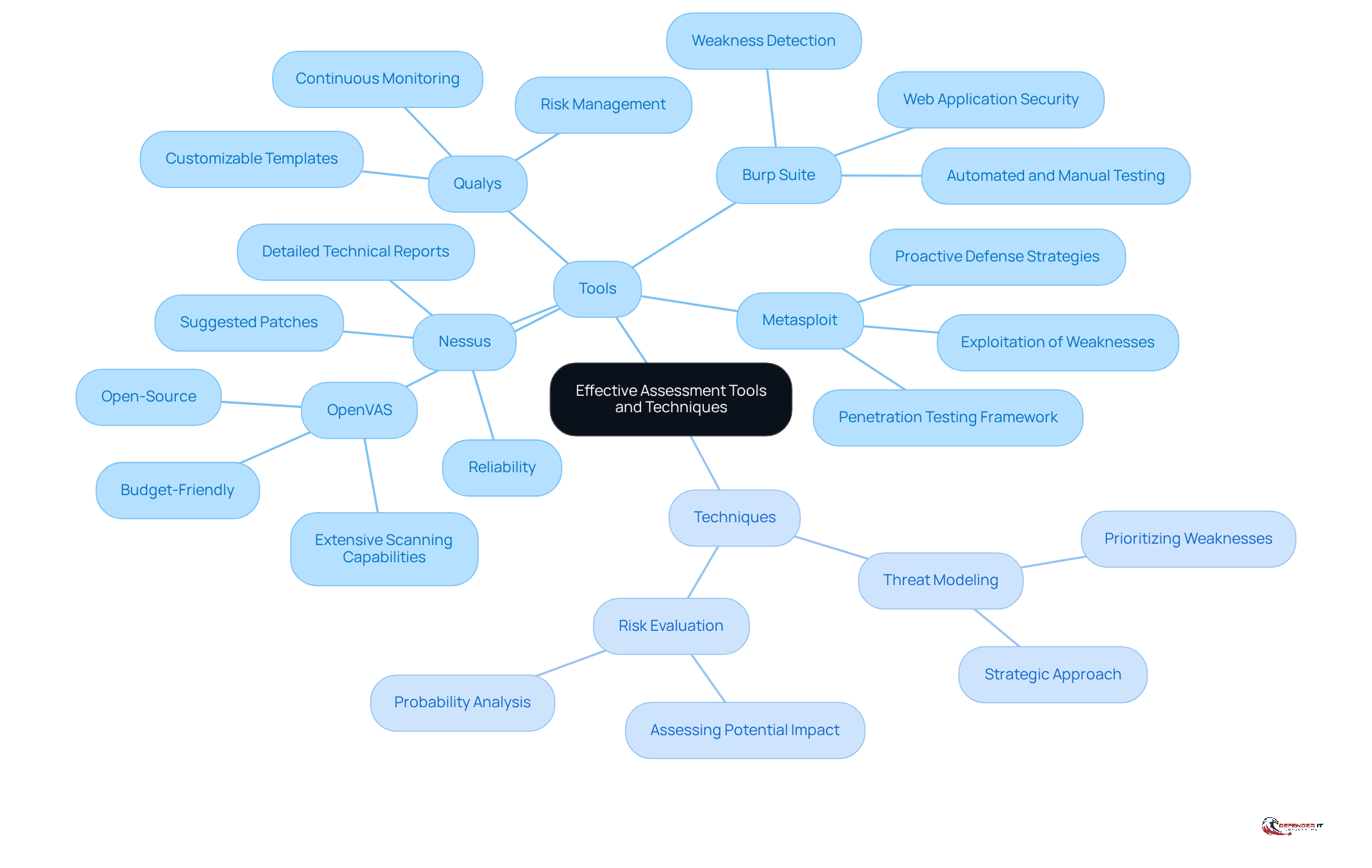
Utilizing reliable tools and techniques is essential to conduct an effective . The following tools are highly regarded in the industry:
- Nessus: Known for its reliability, Nessus identifies vulnerabilities across various platforms and generates detailed technical reports on these vulnerabilities, along with suggested patches. This makes it a trusted choice for organizations seeking to enhance their security posture.
- Qualys: This cloud-based solution excels in continuous monitoring and risk management, making it ideal for entities operating in dynamic environments. Its integration of discovery, assessment, and patch management ensures comprehensive coverage, while customizable templates for frameworks such as PCI or HIPAA enhance compliance auditing.
- OpenVAS: As an open-source security scanner, OpenVAS provides extensive scanning capabilities, making it suitable for organizations with budget constraints while still delivering robust results.
- Burp Suite: A powerful resource for web application security assessment, Burp Suite efficiently detects weaknesses within web applications through both automated and manual testing techniques.
- Metasploit: This allows security experts to exploit weaknesses, offering insights into the effectiveness of current security measures and supporting proactive defense strategies.
In addition to these tools, employing methods such as and risk evaluation can significantly enhance the efficiency of the process. These methods assist organizations in prioritizing weaknesses based on potential impact and probability, ensuring a more strategic approach to cybersecurity. Furthermore, generate various reports, including executive summaries on risk trends and compliance/regulatory documents, which are crucial for entities operating in regulated environments. Given that the , investing in effective is vital for safeguarding organizational assets.
Avoid Common Pitfalls in Network Vulnerability Assessments
To ensure a successful , organizations must avoid several common pitfalls that can compromise their :
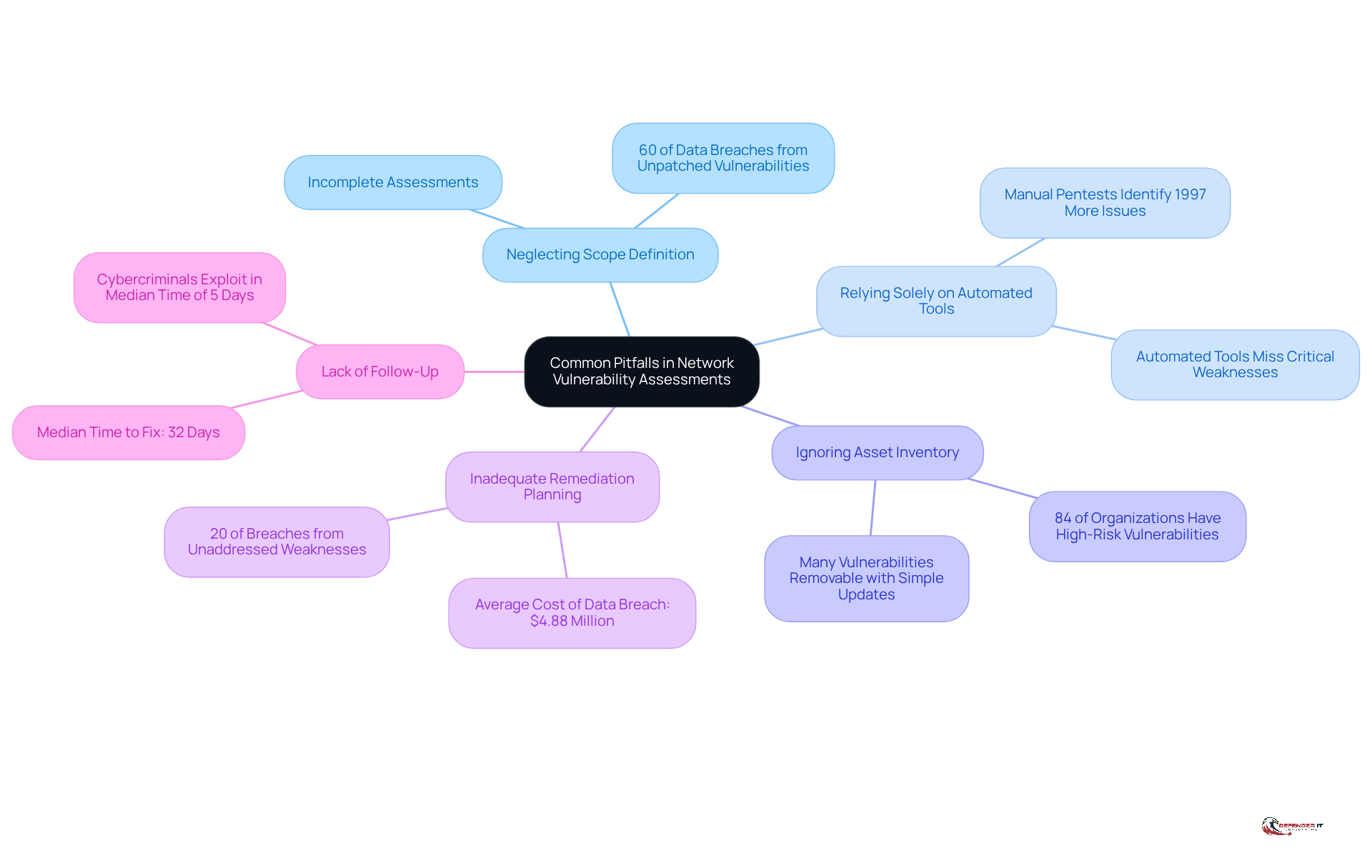
- Neglecting Scope Definition: A poorly defined scope can lead to incomplete assessments, resulting in critical vulnerabilities being overlooked. For instance, organizations that fail to include all relevant assets may expose themselves to significant risks, as 60% of are caused by the failure to apply available patches.
- Relying Solely on Automated Tools: While automated tools are essential for efficiency, they should not replace . Manual evaluations can reveal weaknesses that automated scans may overlook, as research demonstrates that manual pentests identified almost 1997% more distinct problems than automated scanners.
- Ignoring Asset Inventory: Maintaining an up-to-date inventory of assets is crucial. Without it, critical systems may be excluded from assessments, increasing the . In 2025, organizations reported that , many of which could be eliminated with a simple software update if recognized.
- Inadequate : Creating a clear strategy for tackling recognized weaknesses is essential. Organizations that neglect this step often leave issues unresolved, which can lead to increased risk exposure. , underscoring the financial implications of inadequate remediation. Furthermore, 20% of security breaches originated from an unaddressed weakness, highlighting the significance of prompt action.
- Lack of Follow-Up: Regular reassessments are essential to stay ahead of newly discovered threats. Cybercriminals took advantage of weaknesses at a median time of only five days, while companies required an average of 32 days to fix them. This gap emphasizes the need for and timely updates to security measures.
By recognizing these pitfalls and implementing proactive strategies, organizations can significantly enhance the effectiveness of their s to better protect their digital assets.
Conclusion
Conducting a network vulnerability assessment is essential for any organization that seeks to protect its digital assets and ensure regulatory compliance. By identifying and addressing vulnerabilities, businesses can significantly lower their exposure to cyber threats and improve their overall security posture. This proactive strategy not only safeguards sensitive data but also lessens the financial consequences associated with data breaches, which are anticipated to escalate in the coming years.
The article delineates critical steps for executing an effective assessment, including:
- Defining the scope
- Performing asset inventory
- Utilizing both automated and manual testing
- Formulating a comprehensive remediation plan
It underscores the necessity of avoiding common pitfalls, such as neglecting asset inventories or depending solely on automated tools. By grasping these key components and applying best practices, organizations can ensure they are well-prepared to tackle evolving cyber threats.
Ultimately, the importance of network vulnerability assessments cannot be overstated. As cyber threats grow increasingly sophisticated, businesses must prioritize regular evaluations to stay ahead of potential risks. Fostering a culture of continuous monitoring and proactive risk management is vital for protecting not only organizational assets but also for maintaining trust with customers and stakeholders. Implementing these measures today can significantly impact achieving long-term security and operational integrity.
Frequently Asked Questions
What is a network vulnerability assessment?
A network vulnerability assessment is a comprehensive procedure aimed at discovering, assessing, and prioritizing flaws within a network using automated scanning tools and manual testing.
What are the key components of a network vulnerability assessment?
The key components include automated scanning, manual testing, prioritization of identified weaknesses, and documentation of findings.
Why is manual testing important in a network vulnerability assessment?
Manual testing is important because it ensures that no weaknesses are overlooked, particularly in complex environments where automated tools may miss certain vulnerabilities.
How does prioritization work in a network vulnerability assessment?
Prioritization involves evaluating the severity of identified weaknesses to focus remediation efforts on the most critical issues first.
What role does documentation play in a network vulnerability assessment?
Documentation provides a detailed report that serves as evidence of proactive risk management, which is crucial for compliance audits.
Why will network vulnerability assessments become more significant by 2026?
By 2026, new global data privacy regulations will impose stricter penalties for non-compliance, making regular network vulnerability assessments essential for organizations to avoid financial repercussions.
What are the consequences of not conducting regular network vulnerability assessments?
Organizations that do not conduct regular assessments may face substantial financial penalties, and they are at a higher risk of cyber attacks, which can lead to significant operational disruptions.
How do network vulnerability assessments help organizations?
These assessments help organizations secure their digital assets, ensure compliance with regulations, and protect their reputation and operational integrity against evolving cyber threats.
What is the impact of cyber attacks on small businesses?
Reports indicate that 60% of small businesses fail within six months of a cyber attack, highlighting the critical need for regular network vulnerability assessments to mitigate risks.
List of Sources
- Define Network Vulnerability Assessment
- acronis.com (https://acronis.com/en/blog/posts/ultimate-guide-to-vulnerability-assessment-2026)
- Top Cyber Risks in 2026: How to Avoid Hidden Network Vulnerabilities (https://zeronetworks.com/blog/top-cyber-risks-in-2026-how-to-avoid-hidden-network-vulnerabilities)
- The Top 10 IT Security Risks of 2026 (https://splashtop.com/blog/top-it-security-risks-2026)
- Critical Security Findings Nearly Quadrupled Year-Over-Year, OX Security’s 2026 Application Security Benchmark Finds (https://prnewswire.com/news-releases/critical-security-findings-nearly-quadrupled-year-over-year-ox-securitys-2026-application-security-benchmark-finds-302715348.html)
- 35 Cyber Security Vulnerability Statistics, Facts In 2026 (https://getastra.com/blog/security-audit/cyber-security-vulnerability-statistics)
- Outline the Steps for Conducting the Assessment
- Solutions Review: Cybersecurity Awareness Month Quotes from Industry Experts in 2024 – Mark43 (https://mark43.com/press/solutions-review-cybersecurity-awareness-month-quotes-from-industry-experts-in-2024)
- Federal News Network’s Risk & Compliance Exchange 2026 | Federal News Network (https://federalnewsnetwork.com/cme-event/exchanges/federal-news-networks-risk-compliance-exchange-2026)
- Cybersecurity Quotes That Define the Future of Digital Protection (https://medium.com/@cyberpromagazine/cybersecurity-quotes-that-define-the-future-of-digital-protection-64897c07bfc6)
- 4 steps to conducting a proper vulnerability assessment (https://candid.org/blogs/4-steps-to-conducting-a-proper-vulnerability-assessment)
- 9 Quotes that Capture the State of Offensive Security (https://netspi.com/blog/executive-blog/security-industry-trends/quotes-on-the-state-of-offensive-security)
- Identify Tools and Techniques for Effective Assessment
- Top 15 Penetration Testing Tools In 2026 | CloudSEK (https://cloudsek.com/knowledge-base/top-penetration-testing-tools)
- 9 Vulnerability Management Tools in 2026 | SentinelOne (https://sentinelone.com/cybersecurity-101/cybersecurity/8-vulnerability-management-tools)
- Must-Have Cybersecurity Tools for 2026 (https://uscsinstitute.org/cybersecurity-insights/blog/must-have-cybersecurity-tools-for-2026)
- Avoid Common Pitfalls in Network Vulnerability Assessments
- acronis.com (https://acronis.com/en/blog/posts/ultimate-guide-to-vulnerability-assessment-2026)
- Top Cyber Risks in 2026: How to Avoid Hidden Network Vulnerabilities (https://zeronetworks.com/blog/top-cyber-risks-in-2026-how-to-avoid-hidden-network-vulnerabilities)
- 35 Cyber Security Vulnerability Statistics, Facts In 2026 (https://getastra.com/blog/security-audit/cyber-security-vulnerability-statistics)
- Top Cybersecurity Vulnerability Statistics (https://zerothreat.ai/blog/cybersecurity-vulnerability-statistics)
- Vulnerabilities Statistics 2025: Record CVE Surge (https://deepstrike.io/blog/vulnerability-statistics-2025)