Introduction
In an era where cyber threats are increasingly prevalent, understanding the dark web is essential for security leaders. Dark web monitoring not only reveals compromised data but also enables organizations to prevent potential breaches before they escalate. As cybercrime continues to evolve, a critical question emerges: how can companies effectively leverage dark web monitoring to protect their assets and uphold a strong security posture? By examining best practices and key use cases, we can uncover vital insights that may reshape an organization’s approach to cybersecurity.
Understand Dark Web Monitoring and Its Importance
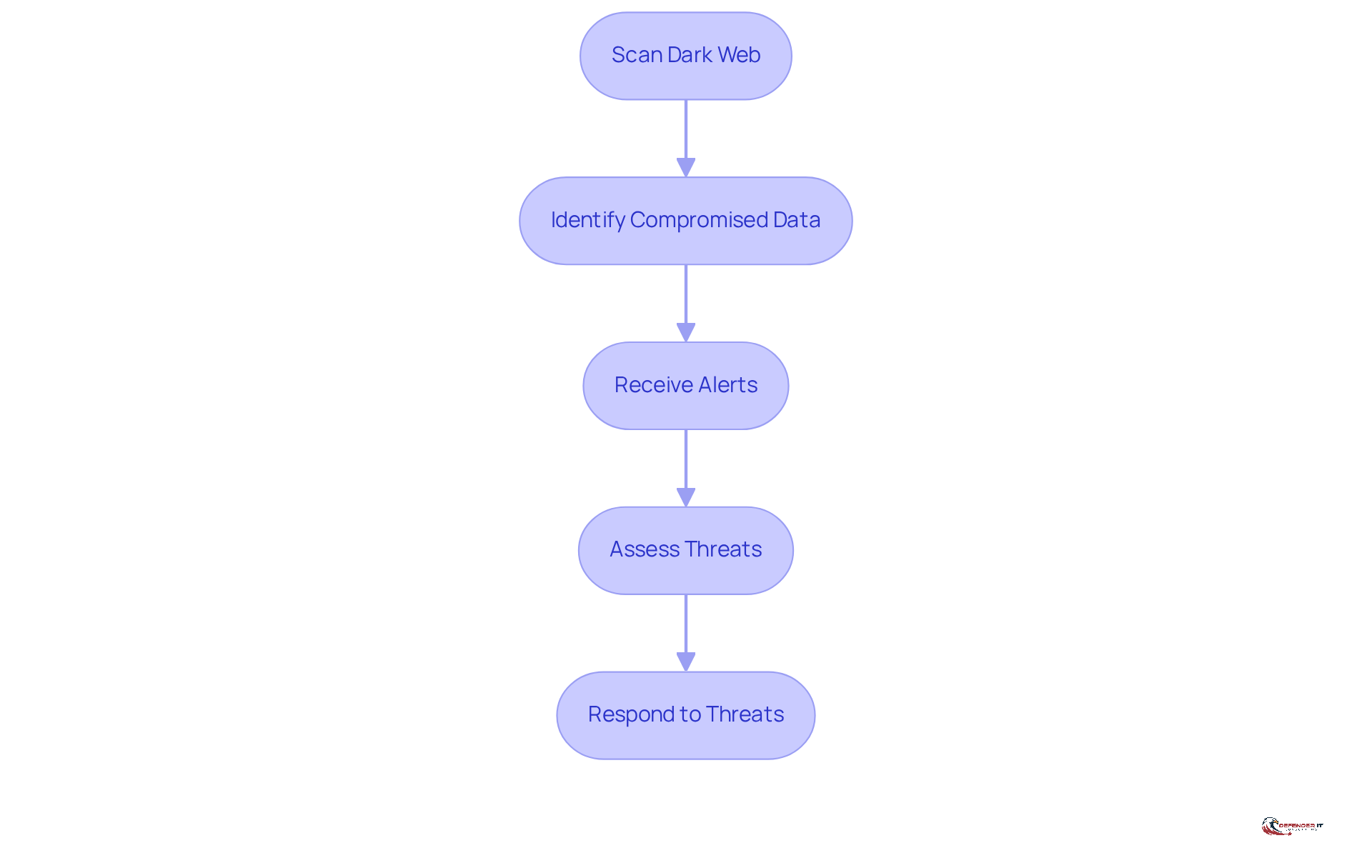
The critical process of dark web monitoring involves scanning the concealed areas of the internet where cybercriminals operate. This practice aims to identify compromised data, such as stolen credentials or sensitive information. Companies can detect potential threats before they escalate into significant breaches by proactively engaging in dark web monitoring.
Understanding the landscape of the hidden web enables security leaders to against cyber threats. The importance of this surveillance lies in its ability to provide early alerts regarding data breaches. Such timely notifications allow organizations to act swiftly, thereby mitigating risks effectively.
For instance, a company that utilizes dark web monitoring can quickly respond to the discovery of its employees’ credentials being sold. This proactive approach helps prevent unauthorized access to its systems, safeguarding sensitive information and maintaining organizational integrity.
Explore Key Use Cases for Dark Web Monitoring
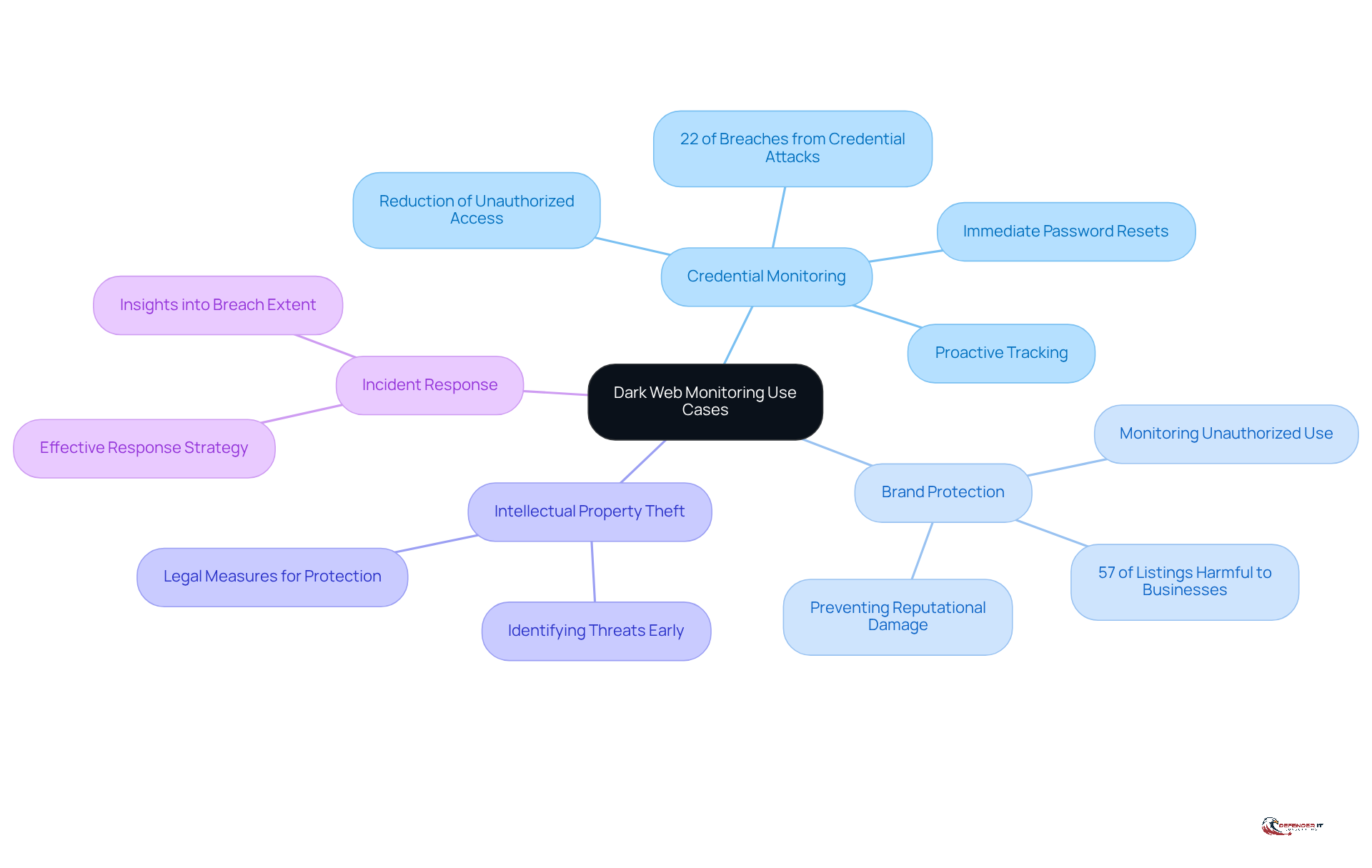
Dark web monitoring serves several critical use cases that enhance organizational security:
- Credential Monitoring: Organizations can actively track whether their employees’ login credentials are being sold or shared on the dark web. This proactive approach allows for immediate password resets and the implementation of enhanced security measures, significantly reducing the risk of unauthorized access. In 2025, credential-based attacks accounted for 22% of all breaches, underscoring the necessity of vigilant credential monitoring. Credential breaches enable wide lateral movement and ransomware with minimal technical exploits, highlighting the urgent need for organizations to monitor their credentials closely.
- Brand Protection: Companies can monitor for unauthorized use of their brand names or trademarks on hidden web platforms. This vigilance helps prevent reputational damage and fraud, ensuring that their remains intact in an increasingly digital marketplace. With 57% of listings on the dark web capable of harming businesses, dark web monitoring and proactive brand oversight are essential.
- Intellectual Property Theft: Dark web monitoring can identify discussions or sales of proprietary information or trade secrets on illicit forums. By identifying these threats early, entities can take legal measures to safeguard their intellectual property and preserve their competitive advantage.
- Incident Response: In the event of a data breach, hidden web surveillance offers valuable insights into the extent of the breach and the specific data compromised. This information is vital for creating an effective response strategy, enabling entities to reduce damage and recuperate more efficiently.
These use cases demonstrate the proactive aspect of underground web surveillance, emphasizing its crucial role in a comprehensive cybersecurity strategy. By leveraging these insights, companies can better safeguard their assets and respond to emerging threats.
Implement Best Practices for Effective Dark Web Monitoring
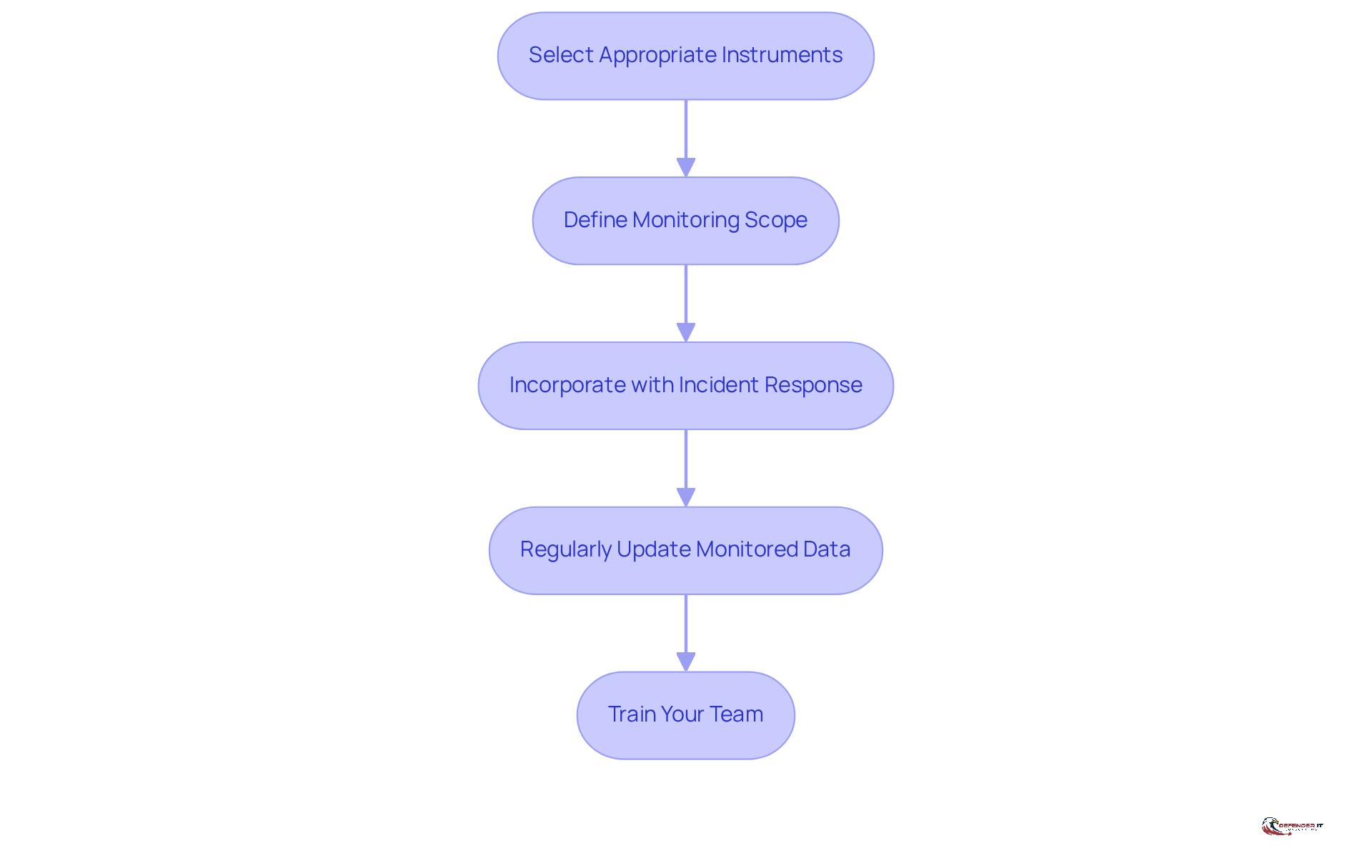
To implement effective dark web monitoring, organizations should prioritize the following best practices:
- Select the Appropriate Instruments: Invest in comprehensive deep web surveillance tools that provide real-time notifications and cover a wide range of deep web sources.
- Define Monitoring Scope: Clearly outline the specific data to be monitored, such as employee credentials, customer information, or proprietary data.
- Incorporate with Incident Response: Ensure that your underground web surveillance efforts are integrated with your incident response strategy, facilitating prompt action when threats are detected.
- Regularly Update Monitored Data: Continuously refresh the information being monitored to reflect any changes in your organization’s data landscape.
- Train Your Team: Provide training for your security team on how to interpret and respond effectively.
By adhering to these best practices, organizations can improve their dark web monitoring efforts and better protect themselves from cyber threats.
Maintain Vigilance and Adapt Strategies for Continuous Improvement
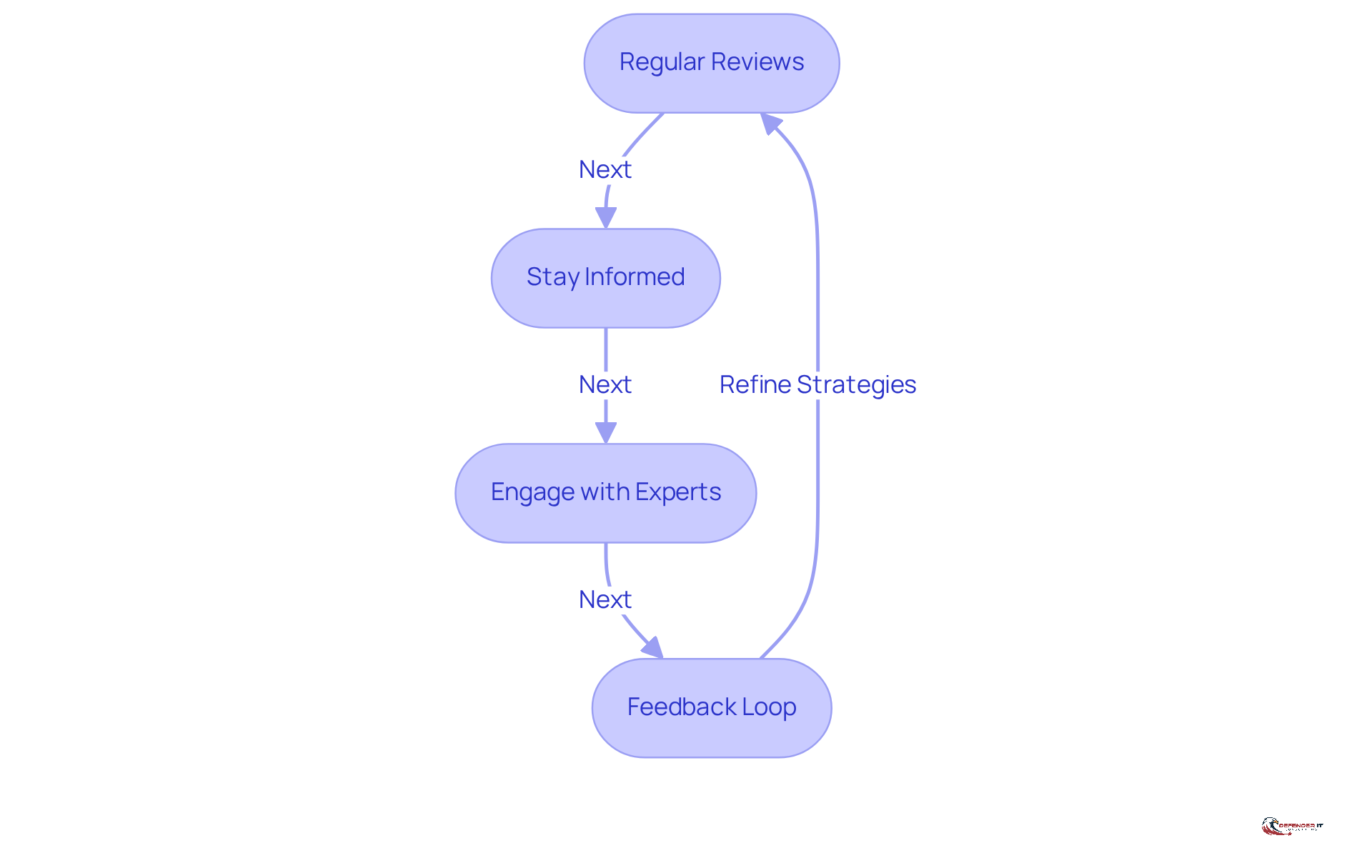
To ensure the efficiency of , organizations must remain vigilant and adapt their strategies over time. This can be achieved through several key practices:
- Regular Reviews: Conduct periodic assessments of your deep web monitoring program to evaluate its effectiveness and implement necessary adjustments. This proactive approach helps identify gaps and enhances overall security posture. For instance, with ransomware attacks surging by 55.5% in 2023, regular reviews are crucial to staying ahead of evolving threats.
- Stay Informed: Keep abreast of the latest trends and threats in the dark web landscape. Cybercriminals continuously advance their strategies, making it essential for companies to understand [emerging threats](https://zerofox.com/blog/2026-cyber-threat-predictions), such as AI-driven phishing and advanced impersonation attempts. According to ZeroFox Intelligence, the integration of AI in cyber attacks has rendered them more convincing and harder to detect.
- Engage with Experts: Collaborate with cybersecurity experts and threat intelligence providers to gain insights into emerging threats and best practices. Leveraging expert knowledge can significantly enhance your organization’s ability to anticipate and respond to potential risks. For instance, entities that subscribe to services like ZeroFox Intelligence can access real-time indicators and context for improved decision-making.
- Feedback Loop: Establish a feedback loop where lessons learned from incidents are utilized to refine monitoring strategies and improve response protocols. This iterative process fosters a culture of continuous improvement, allowing organizations to adapt swiftly to the dynamic threat landscape. As emphasized in case studies on AI-driven attacks, entities that learn from past incidents can better prepare for future threats.
By fostering a culture of continuous improvement, organizations can enhance their resilience against cyber threats and ensure the effectiveness of their [dark web monitoring efforts](https://pandasecurity.com/en/mediacenter/dark-web-statistics).
Conclusion
Proactive dark web monitoring is crucial for organizations aiming to protect sensitive information and uphold their cybersecurity posture. By consistently scanning the hidden corners of the internet, security leaders can identify compromised data and address threats before they escalate into significant breaches. This vigilance safeguards employee credentials and preserves brand integrity and intellectual property, making it an essential element of any comprehensive cybersecurity strategy.
The article outlines key use cases for dark web monitoring, including:
- Credential monitoring
- Brand protection
- Intellectual property theft prevention
- Incident response
Each area emphasizes the necessity of a proactive approach in confronting cyber threats. By implementing best practices – such as selecting suitable tools, defining monitoring scopes, and integrating monitoring efforts with incident response strategies – organizations can significantly bolster their defenses against emerging threats.
Ultimately, maintaining vigilance and adapting strategies for continuous improvement in dark web monitoring is vital for organizations to stay ahead of cybercriminals. Regular reviews, staying informed about the latest trends, and engaging with cybersecurity experts are essential steps in fostering a culture of resilience. By prioritizing dark web monitoring, organizations not only protect their assets but also position themselves as leaders in the fight against cyber threats, ensuring a safer digital landscape for all.
Frequently Asked Questions
What is dark web monitoring?
Dark web monitoring is the process of scanning hidden areas of the internet where cybercriminals operate to identify compromised data, such as stolen credentials or sensitive information.
Why is dark web monitoring important for companies?
Dark web monitoring is important because it allows companies to detect potential threats before they escalate into significant breaches, providing early alerts regarding data breaches and enabling swift action to mitigate risks.
How does dark web monitoring help organizations respond to threats?
By utilizing dark web monitoring, organizations can quickly respond to the discovery of their employees’ credentials being sold, which helps prevent unauthorized access to their systems and safeguards sensitive information.
What are the benefits of engaging in dark web monitoring?
The benefits include early detection of compromised data, the ability to act quickly to mitigate risks, and enhanced organizational integrity by safeguarding sensitive information from cyber threats.