Introduction
Manufacturing leaders face increasing pressure to comply with cybersecurity regulations amid a surge in cyber threats. Understanding the fundamental principles and regulations governing cybersecurity is essential for organizations aiming to protect sensitive data and ensure operational integrity. Given the complexities of regulations and the ongoing need for improvement, leaders must find effective ways to navigate compliance and cultivate a security-focused culture. Failure to implement robust compliance strategies can lead to significant data breaches and operational disruptions.
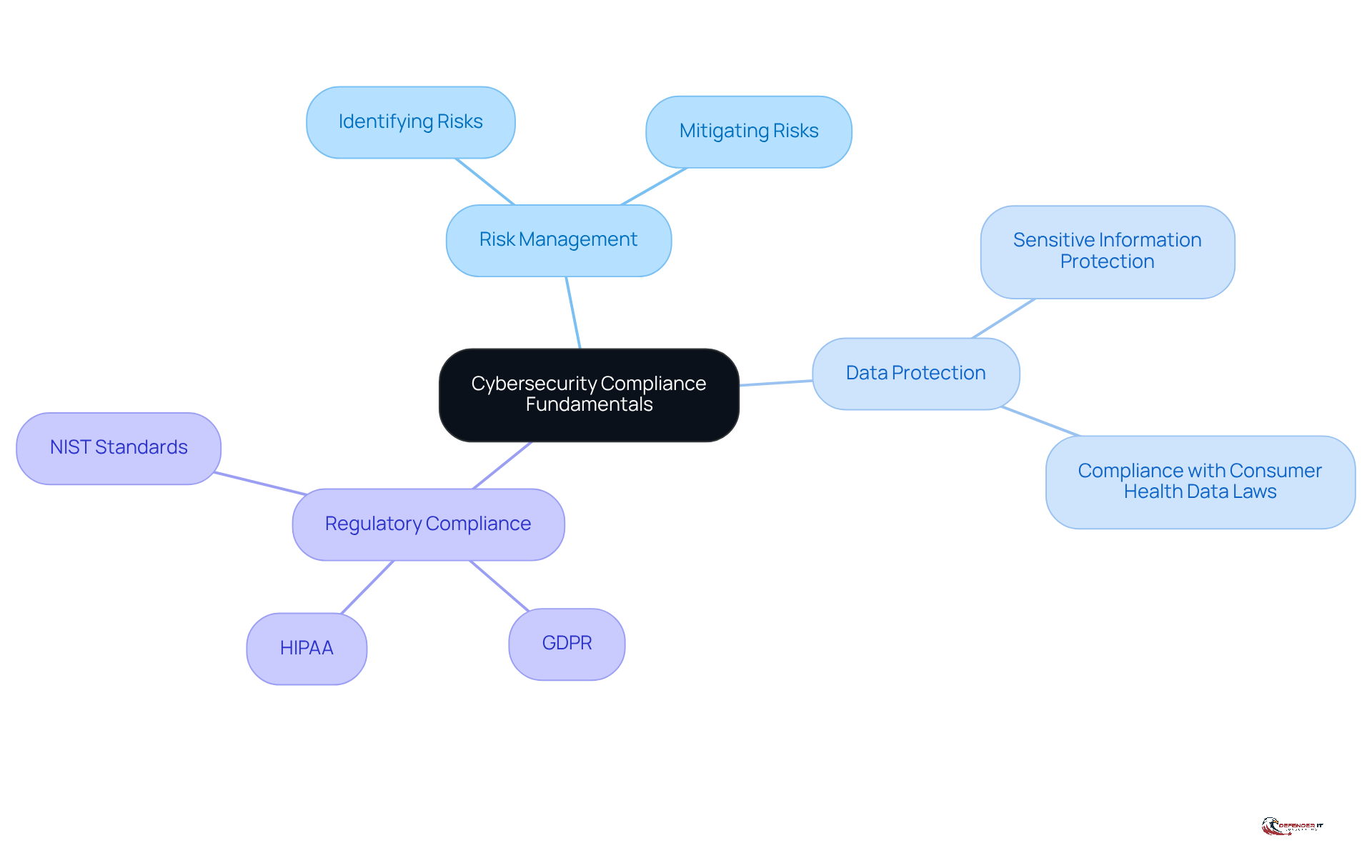
Understand Cybersecurity Compliance Fundamentals
Manufacturing leaders face an urgent need to understand the fundamental principles of cybersecurity regulations to protect their organizations effectively. Adhering to laws, regulations, and standards aimed at safeguarding sensitive data and ensuring the integrity of IT systems is what cybersecurity compliance involves. Key components include:
- Risk Management: This entails identifying and mitigating risks associated with cyber threats, which are increasingly sophisticated. The frequency of cyber attacks underscores the critical need for robust risk management strategies. Regulators expect businesses to demonstrate a proactive approach to managing cyber risk, highlighting the importance of cybersecurity compliance for organizations to stay ahead of potential threats.
- Data Protection: Implementing measures to protect sensitive information from unauthorized access is crucial. Organizations must evaluate their data practices to comply with new consumer health data laws, which require affirmative consent and data minimization. Significantly, just 34% of individuals had recorded all necessary actions to adhere to HIPAA regulations, emphasizing the importance of detailed documentation in regulatory efforts.
Compliance with industry-specific regulations such as GDPR, HIPAA, or NIST standards is vital for ensuring cybersecurity compliance. In 2026, the legal environment highlights resilience under pressure, making it essential for organizations to show proactive management of cyber threats. Furthermore, organizations that neglect proactive cyber threat management risk not only legal repercussions but also a decline in customer trust.
By grasping these basics, leaders can recognize the importance of cybersecurity compliance in safeguarding their organizations from cyber threats and potential legal consequences. Additionally, as cybersecurity evolves into a board-level issue, leaders must ensure that their regulatory strategies are embedded within overall business governance, emphasizing the significance of cybersecurity as a vital business risk. It’s essential that every employee is trained, as each person plays a role in maintaining compliance. Lastly, organizations must adjust to fragmented regulations and supply chain vulnerabilities to navigate the complex regulatory environment effectively.
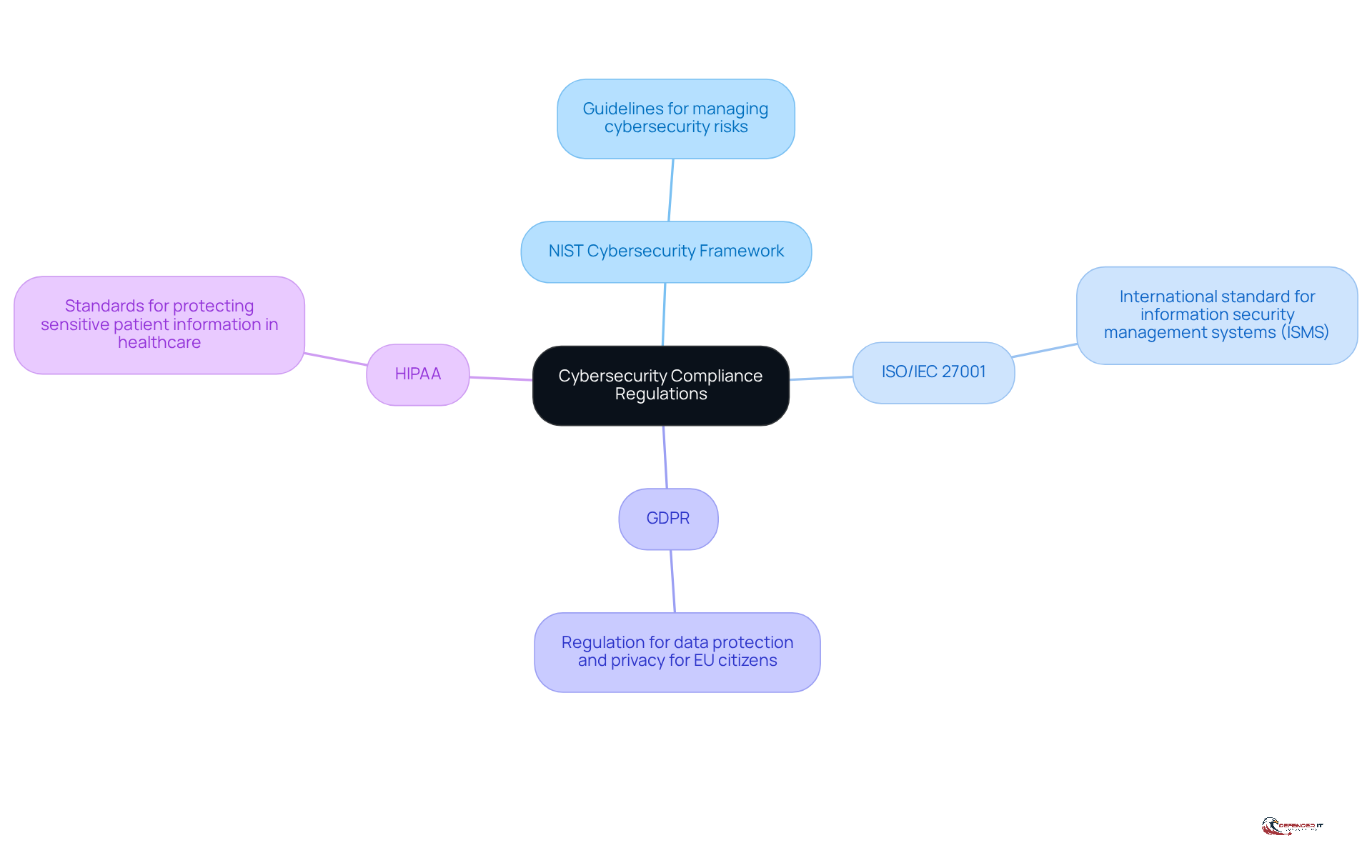
Identify Key Regulations and Frameworks
Navigating the complex landscape of cybersecurity compliance can be daunting for manufacturing leaders. To effectively manage this challenge, it is essential to familiarize themselves with key regulations and frameworks that govern compliance. Some of the most relevant include:
- NIST Cybersecurity Framework: A voluntary framework that provides guidelines for managing cybersecurity risks.
- ISO/IEC 27001: An international standard for information security management systems (ISMS).
- GDPR: A regulation that mandates strict data protection and privacy measures for organizations handling EU citizens’ data.
- HIPAA: Applicable to healthcare-related manufacturing, it sets standards for protecting sensitive patient information.
By understanding these regulations, leaders can enhance their security strategies and ensure cybersecurity compliance with legal standards, ultimately safeguarding organizational integrity.
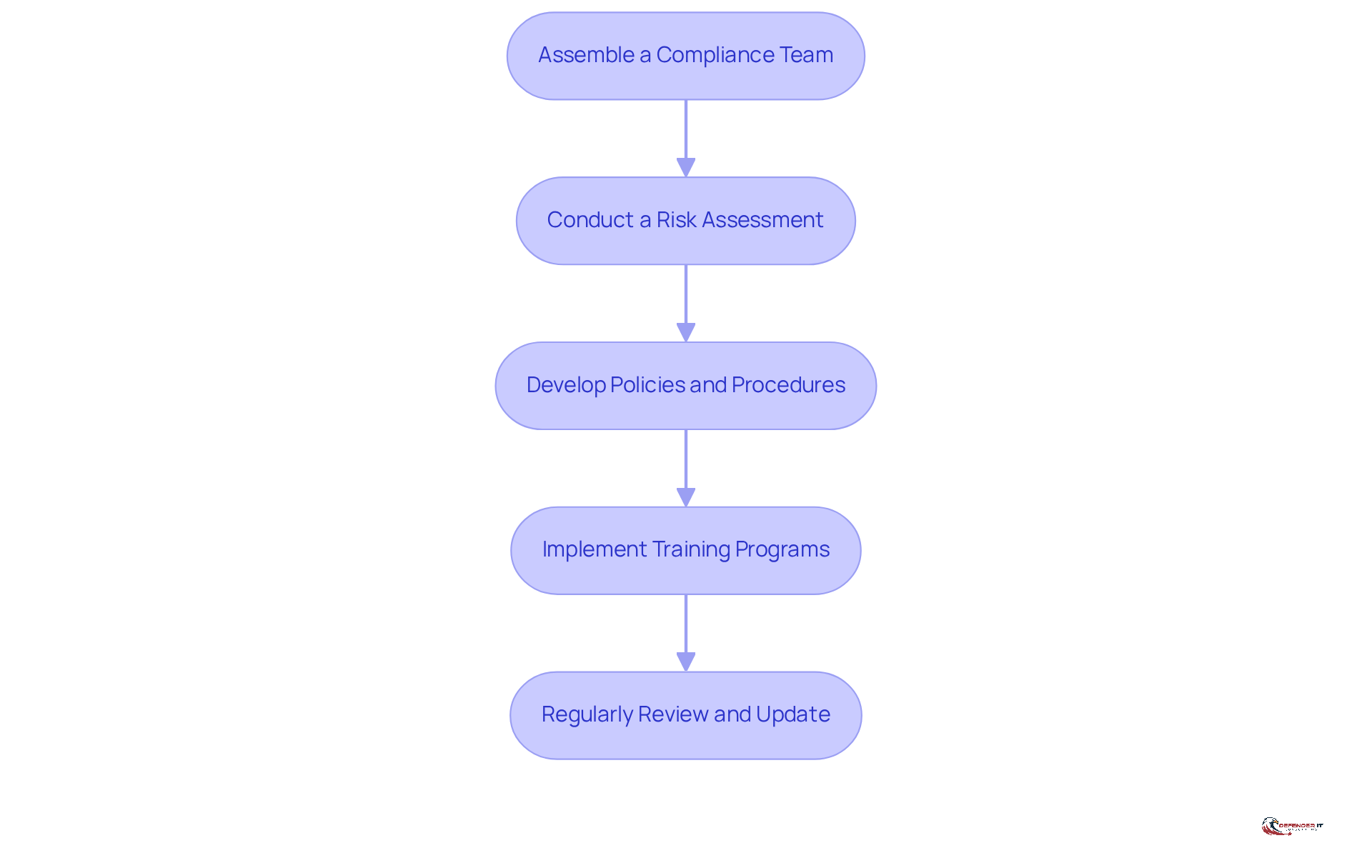
Establish a Cybersecurity Compliance Program
To effectively navigate the complexities of cybersecurity compliance, manufacturing leaders must take decisive action. Here are essential steps to establish an effective cybersecurity compliance program:
- Assemble a Compliance Team: Form a dedicated team responsible for overseeing compliance efforts, including representatives from IT, legal, and operations. This team is crucial for navigating the complexities of regulatory requirements and ensuring a unified approach to achieving cybersecurity compliance.
- Conduct a Risk Assessment: Identify vulnerabilities and assess the potential impact of cyber threats on operations. Many organizations struggle to gain a clear view of their cybersecurity risks, with 76% utilizing technology for evaluations (Lucia Giles, Sr. Content Marketing Manager, Vanta). This highlights the importance of utilizing advanced tools to enhance visibility into risks.
- Develop Policies and Procedures: Create clear policies that outline security protocols, data handling practices, and incident response plans. Effective policies are essential for ensuring cybersecurity compliance. They guide organizational behavior and establish accountability. As Lucia Giles observes, ‘85% of organizations state that regulatory requirements, particularly concerning cybersecurity compliance, have become more complex over the past three years, reflecting increasing regulatory burdens and heightened expectations from stakeholders.’
- Implement Training Programs: Educate employees on regulatory requirements and best practices to foster a culture of security awareness. Given that 82% of organizations use technology for regulatory training (Vanta), continuous education is essential for sustaining a knowledgeable workforce.
- Regularly Review and Update: Continuously monitor adherence efforts and update policies as regulations evolve or new threats emerge. Organizations that prioritize regular evaluations are better positioned to adapt to the changing security landscape. Tools such as CyberArrow can automate regulatory tasks, making this process more efficient.
Ultimately, a proactive approach to cybersecurity compliance not only mitigates risks but also positions organizations for long-term success in a dynamic regulatory environment.
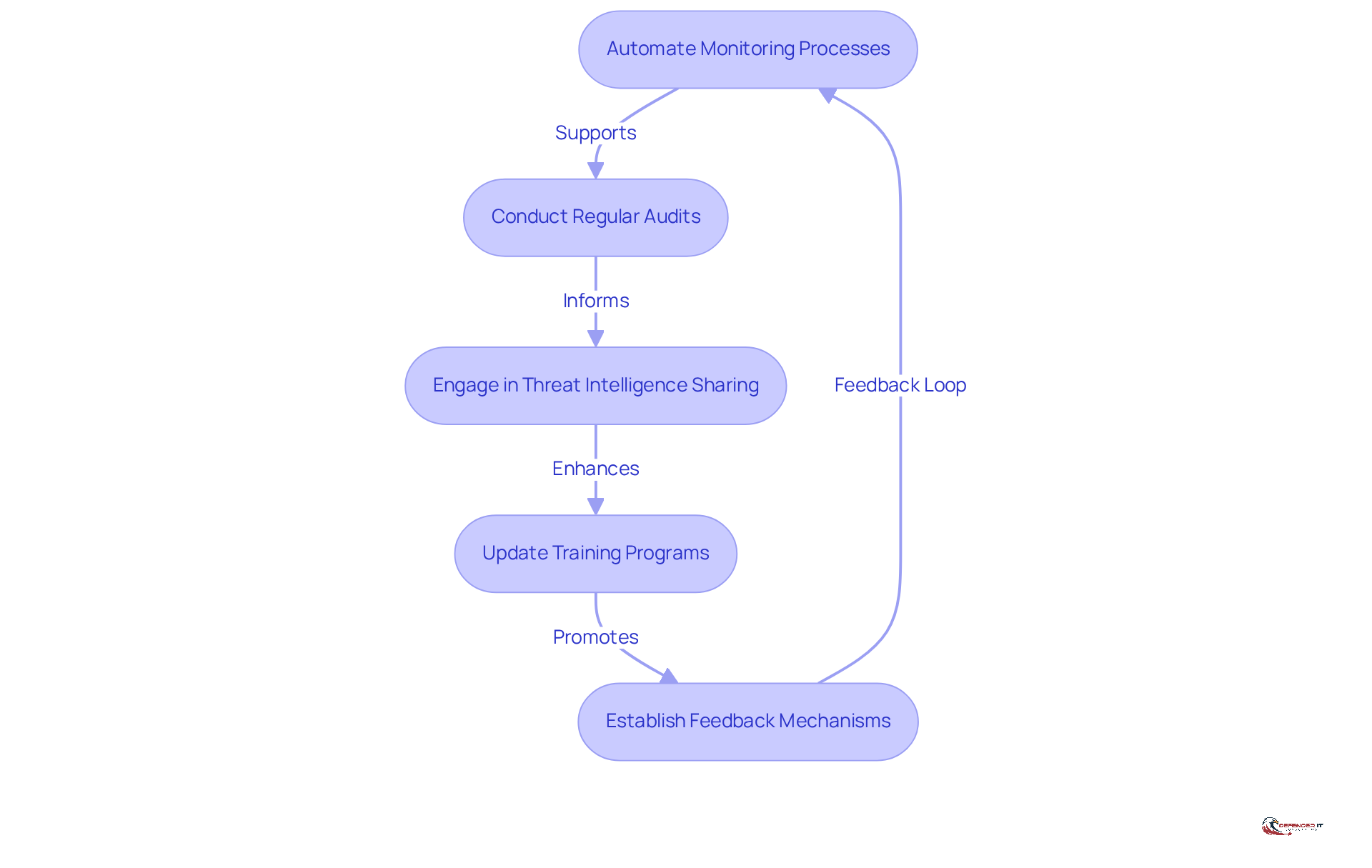
Implement Continuous Monitoring and Improvement Strategies
To navigate the complexities of cybersecurity, manufacturing leaders must adopt proactive compliance strategies that ensure ongoing security and resilience:
- Automate Monitoring Processes: Leverage automated monitoring tools that provide real-time insights into systems and networks, enabling the detection of anomalies and potential breaches. Organizations that implement efficient network security monitoring solutions experience a 30% reduction in successful cyberattacks, underscoring the effectiveness of these tools. Additionally, tools like Cloud Security Posture Management (CSPM) systems and Endpoint Detection and Response (EDR) solutions can enhance monitoring capabilities.
- Conduct Regular Audits: Schedule periodic audits to evaluate adherence to established policies and identify areas for improvement. Routine evaluations of security strategies should occur at least every three years to ensure cybersecurity compliance, mitigating the risk of falling behind in security measures. This aligns with the guideline that emphasizes the necessity of audit frequency in maintaining adherence.
- Engage in Threat Intelligence Sharing: Collaborate with industry peers to share insights on emerging threats and best practices for compliance. This proactive approach enhances security measures and ensures cybersecurity compliance by helping to tailor responses based on specific risks. For instance, the healthcare sector’s adoption of real-time monitoring illustrates the effectiveness of such collaboration in protecting sensitive data.
- Update Training Programs: Regularly refresh training materials to reflect new regulations and evolving cyber threats. To achieve effective cybersecurity, a comprehensive approach that includes training, aligned processes, and strategic prioritization from leadership is essential, ensuring that employees are equipped to recognize and respond to threats.
- Establish Feedback Mechanisms: Create channels for employees to report security concerns and propose enhancements to regulatory practices. This promotes a culture of security awareness and encourages proactive involvement in upholding regulations.
Ultimately, a proactive strategy for cybersecurity compliance not only safeguards against threats but also fosters a culture of security awareness that is essential in today’s digital landscape.
Conclusion
Manufacturing leaders face increasing pressure to navigate the complexities of cybersecurity compliance amid evolving threats. By prioritizing compliance with established regulations and frameworks, leaders can protect sensitive data and enhance their organization’s overall resilience in a complex regulatory environment. Cybersecurity compliance is a vital aspect of strategic governance that directly impacts customer trust and operational integrity.
The article outlines several key strategies for achieving effective cybersecurity compliance. It emphasizes the importance of:
- Risk management
- Data protection
- A thorough understanding of relevant regulations such as NIST, ISO, GDPR, and HIPAA
Establishing a dedicated compliance team, conducting regular risk assessments, and implementing comprehensive training programs are vital steps in creating a robust compliance framework. Furthermore, the necessity of continuous monitoring and regular audits cannot be overstated, as they ensure that organizations remain vigilant and responsive to emerging threats and regulatory changes.
In a landscape where cyber threats are increasingly sophisticated, manufacturing leaders must take proactive steps to foster a culture of cybersecurity awareness within their organizations. By embracing these best practices and committing to continuous improvement, leaders can achieve compliance and position their organizations for long-term success. By prioritizing cybersecurity compliance, manufacturing leaders can secure their organizations’ futures in an increasingly digital landscape.
Frequently Asked Questions
What is cybersecurity compliance?
Cybersecurity compliance involves adhering to laws, regulations, and standards designed to protect sensitive data and ensure the integrity of IT systems.
Why is risk management important in cybersecurity compliance?
Risk management is crucial as it involves identifying and mitigating risks associated with increasingly sophisticated cyber threats. Regulators expect businesses to proactively manage cyber risks to stay ahead of potential threats.
What measures should organizations take for data protection?
Organizations must implement measures to protect sensitive information from unauthorized access, evaluate their data practices, and comply with consumer health data laws that require affirmative consent and data minimization.
Which regulations are important for cybersecurity compliance?
Important regulations include industry-specific standards such as GDPR, HIPAA, and NIST, which are vital for ensuring cybersecurity compliance.
What are the risks of neglecting proactive cyber threat management?
Organizations that neglect proactive cyber threat management risk legal repercussions and a decline in customer trust.
How should cybersecurity compliance be integrated into business governance?
Cybersecurity compliance should be embedded within overall business governance, emphasizing its significance as a vital business risk.
Why is employee training essential for cybersecurity compliance?
Every employee plays a role in maintaining compliance, making training essential to ensure that all staff understand their responsibilities regarding cybersecurity.
How can organizations navigate fragmented regulations and supply chain vulnerabilities?
Organizations must adjust their strategies to effectively navigate the complex regulatory environment, addressing fragmented regulations and vulnerabilities within their supply chains.
List of Sources
- Understand Cybersecurity Compliance Fundamentals
- The future of cybersecurity compliance in 2026 | FDM Group (https://fdmgroup.com/news-insights/future-of-cybersecurity-compliance-2026)
- The Top 20 Expert Quotes On Cyber Risk and Security (https://surtech.co.za/20-expert-quotes-on-cyber-risk-and-security)
- How 2026 Will Reshape Data Privacy and Cybersecurity (https://founderslegal.com/how-2026-will-reshape-data-privacy-and-cybersecurity)
- 41 Cybersecurity Quotes to Protect Your Digital Life (https://acecloudhosting.com/blog/cybersecurity-quotes)
- Cyber security compliance statistics for 2026 | CyberArrow (https://cyberarrow.io/blog/cyber-security-compliance-statistics)
- Identify Key Regulations and Frameworks
- Compliance with Cybersecurity and Privacy Laws and Regulations (https://nist.gov/mep/cybersecurity-resources-manufacturers/compliance-cybersecurity-and-privacy-laws-and-regulations)
- Manufacturing Cybersecurity – Standards, Regulation and Compliance – Industrial Cyber (https://industrialcyber.co/expert/manufacturing-cybersecurity-standards-regulation-and-compliance)
- Establish a Cybersecurity Compliance Program
- Cyber security compliance statistics for 2026 | CyberArrow (https://cyberarrow.io/blog/cyber-security-compliance-statistics)
- New cyber strategy bets on coordination over regulation | Federal News Network (https://federalnewsnetwork.com/cybersecurity/2026/04/new-cyber-strategy-bets-on-coordination-over-regulation)
- Trump’s 2026 Cybersecurity Strategy: From Compliance to Consequence (https://aikido.dev/blog/trump-cybersecurity-strategy-2026)
- 110 security and compliance statistics for tech leaders to know in 2025 (https://vanta.com/resources/compliance-statistics)
- 130+ Compliance Statistics & Trends to Know for 2026 (https://secureframe.com/blog/compliance-statistics)
- Implement Continuous Monitoring and Improvement Strategies
- 8 Great Cyber Security Quotes From Influencers | Proofpoint US (https://proofpoint.com/us/blog/identity-threat-defense/8-great-cyber-security-quotes-influencers)
- TOP 25 COMPLIANCE QUOTES (of 106) | A-Z Quotes (https://azquotes.com/quotes/topics/compliance.html)
- Cybersecurity Continuous Monitoring: Finding the Right Support (https://resources.steelpatriotpartners.com/cybersecurity-continuous-monitoring-finding-the-right-support)
- Cybersecurity Awareness Month Quotes and Commentary from Industry Experts in 2025 (https://solutionsreview.com/cybersecurity-awareness-month-quotes-and-commentary-from-industry-experts-in-2025)