Introduction
Organizations face increasing challenges in managing cybersecurity risks associated with third-party vendors, which can jeopardize their data security and compliance efforts. As businesses increasingly rely on third-party relationships, understanding the nuances of these interactions becomes paramount for maintaining data security and regulatory compliance. Yet, many organizations find it challenging to pinpoint and address the various risks that come with third-party relationships.
Failure to address these risks can result in significant data breaches and regulatory penalties. Navigating these complexities is essential not only for safeguarding operations but also for maintaining trust in partnerships that drive business success.
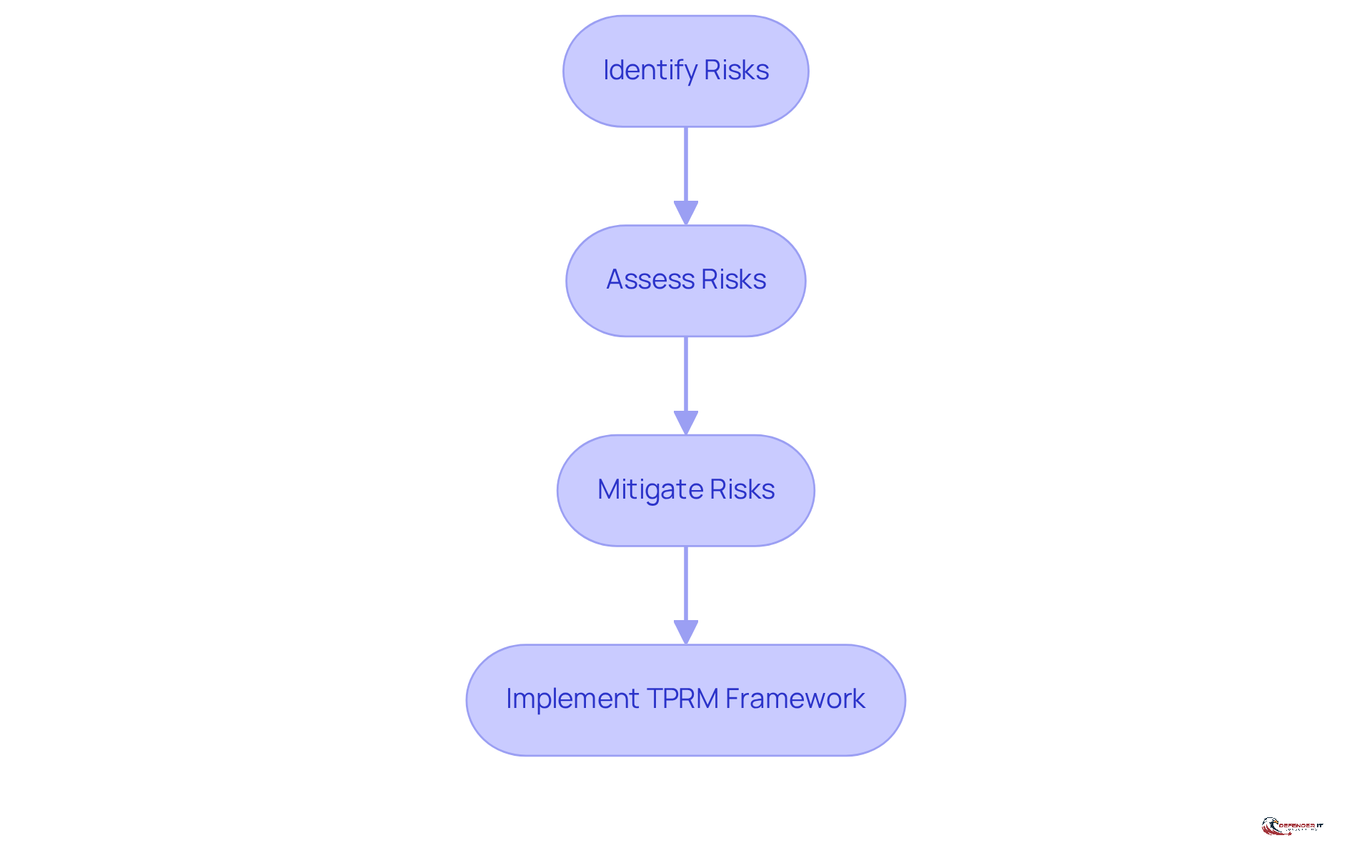
Define Third-Party Risk Management (TPRM)
Cybersecurity third party risk management is essential for protecting organizations from vulnerabilities posed by external vendors and service providers. The systematic process of identifying, assessing, and mitigating risks that arise from interactions with external entities is known as cybersecurity third party risk management (TPRM). This means evaluating how third-party relationships might affect a company’s operations, data security, and adherence to regulations as part of cybersecurity third party risk management.
Cybersecurity third party risk management is crucial for firms that depend on third parties for vital services, as it helps ensure that these external entities do not create vulnerabilities that could lead to data breaches, operational disruptions, or reputational harm. Failure to implement an effective cybersecurity third party risk management strategy can result in data breaches and operational failures. By creating a strong cybersecurity third party risk management framework, organizations can proactively manage threats and maintain a secure operational environment. Organizations risk significant operational and reputational damage without a robust cybersecurity third party risk management framework.
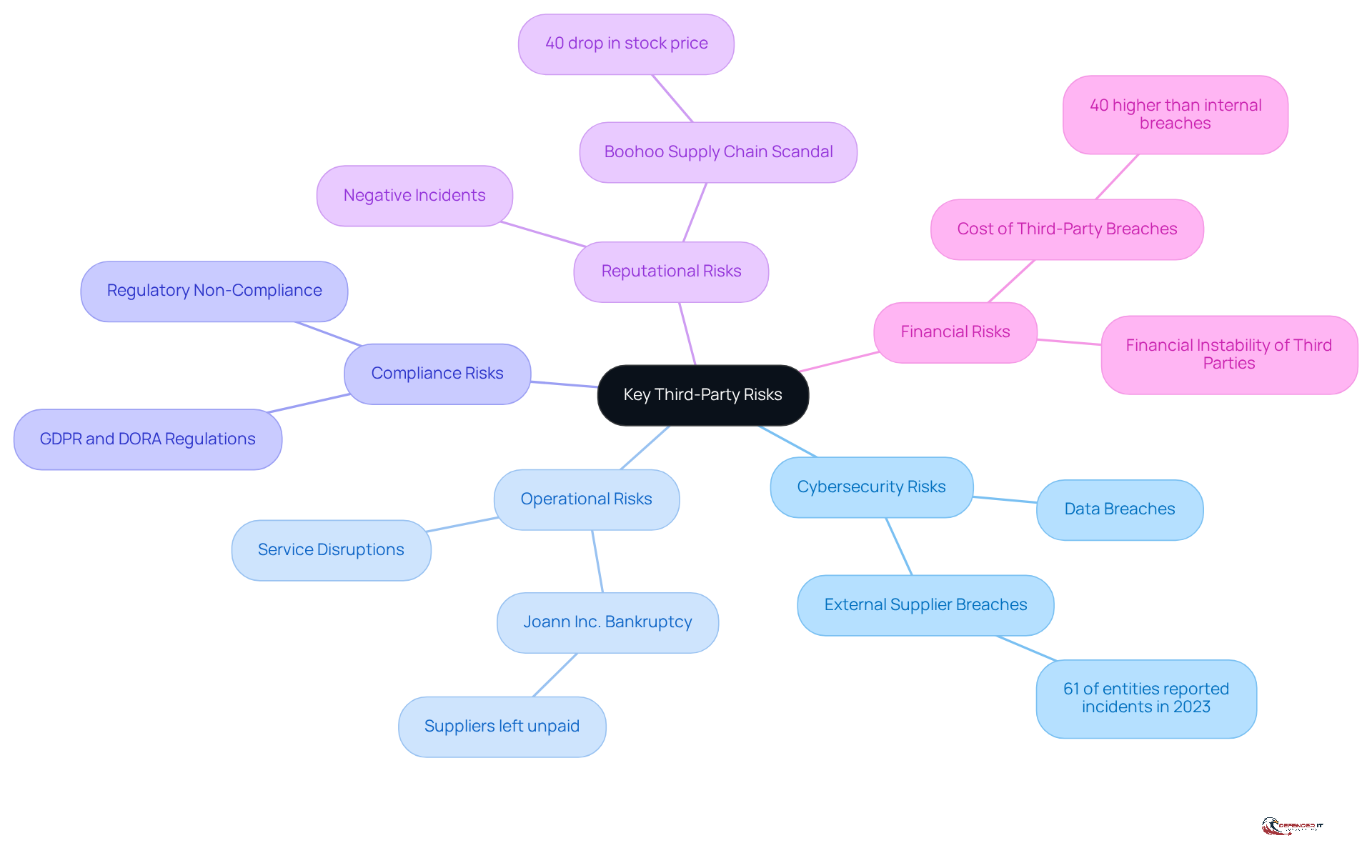
Identify Key Third-Party Risks
Despite the increasing reliance on third-party relationships, many organizations remain unaware of the significant risks they pose regarding cybersecurity third party risk management. Organizations must identify several key risks associated with third-party relationships, including:
- Cybersecurity Risks: These involve potential data breaches or cyberattacks that could exploit vulnerabilities in external systems. In 2023, 61% of entities reported incidents related to external supplier breaches, emphasizing the urgency of addressing these vulnerabilities.
- Operational Risks: Disruptions in service delivery caused by external failures can significantly affect a company’s operations. For instance, the bankruptcy of Joann Inc. in early 2024 left suppliers unpaid, causing widespread supply chain disruptions. Notably, only 39% of enterprises assess their cybersecurity third party risk management as highly effective, highlighting the importance of overseeing supplier financial stability.
- Compliance Risks: Third parties may not follow regulatory requirements, exposing the entity to legal penalties. With global regulations such as GDPR and DORA implementing stricter controls, ensuring adherence across all suppliers is crucial.
- Reputational Risks: Negative incidents involving third parties can damage an organization’s reputation and customer trust. The Boohoo supply chain scandal in 2020 serves as a stark reminder of how supplier mismanagement can lead to public outrage and financial losses.
- Financial Risks: Financial instability of a third party can lead to service disruptions or increased costs. The average cost of a third-party cyber breach is typically 40% higher than an internal breach, underscoring the financial implications of inadequate vendor oversight.
Conducting thorough evaluations of these challenges allows organizations to develop targeted strategies for cybersecurity third party risk management that mitigate risks and enhance their security posture. Without a proactive approach to these risks, organizations may find themselves facing severe operational and reputational consequences.
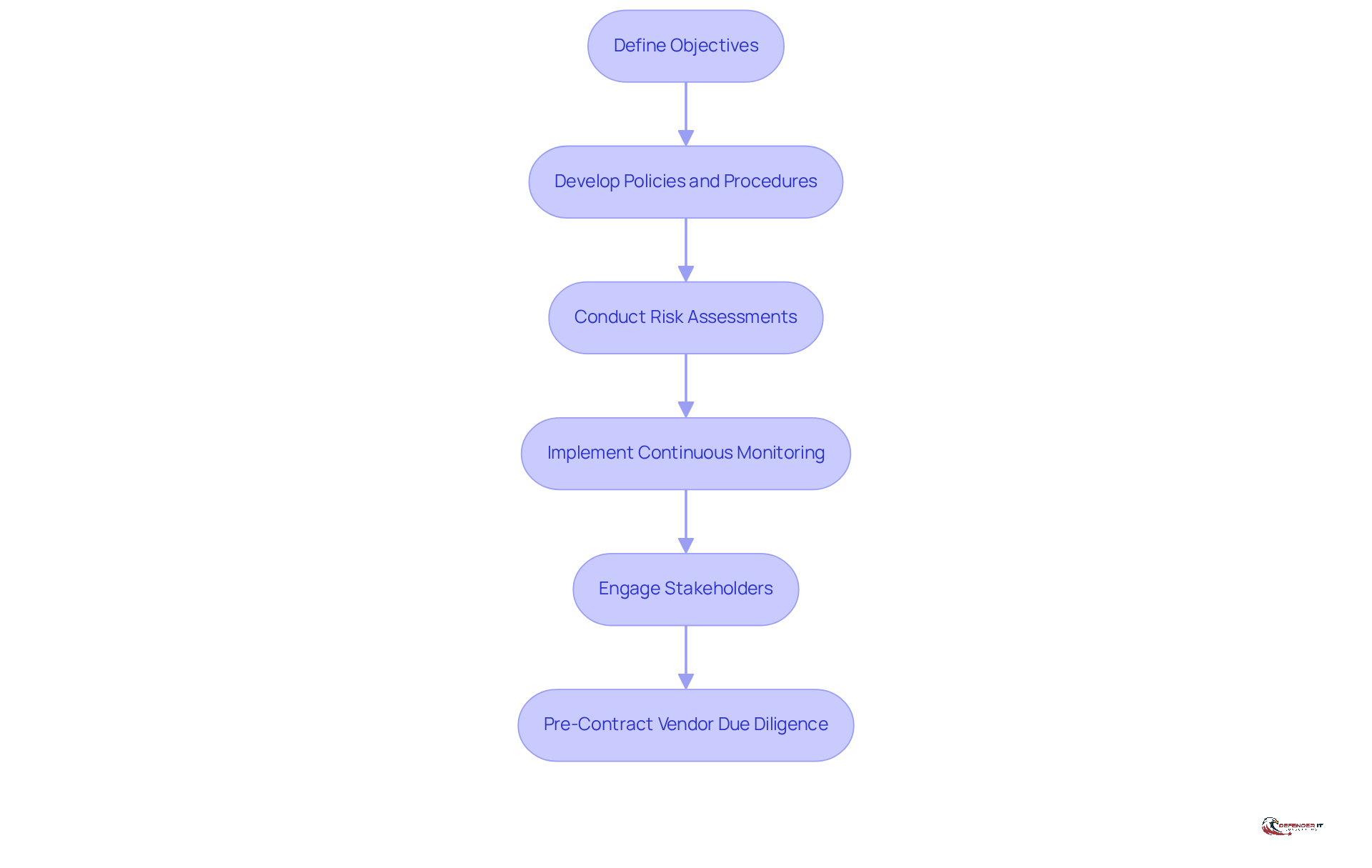
Establish a Structured TPRM Program
Organizations often struggle to keep pace with the evolving landscape of cybersecurity third party risk management, leading to significant vulnerabilities. To establish a structured Third-Party Risk Management (TPRM) program, organizations should adhere to the following best practices:
- Define Objectives: Clearly outline the goals of the TPRM program, including specific risk tolerance levels and compliance requirements. This foundational step ensures that all subsequent actions align with the organization’s strategic vision.
- Develop Policies and Procedures: Create comprehensive policies governing external engagements. These should encompass thorough evaluation protocols and oversight procedures that reflect the complexity of contemporary supplier relationships, especially considering the changing regulatory environments.
- Conduct Risk Assessments: Regularly evaluate the risks associated with each third-party provider. Using structured questionnaires and audits helps organizations gain valuable insights into how secure their suppliers really are, assisting in spotting weaknesses before they result in incidents. Significantly, 98% of entities have connections with external parties that have been compromised, and 77% of breaches in the last three years started with a supplier or third party, highlighting the necessity of comprehensive evaluations.
- Implement Continuous Monitoring: Establish mechanisms for ongoing monitoring. This includes assessing third-party performance and risk exposure regularly. Continuous monitoring tools are essential for timely identification of emerging threats, as nearly 33% of procurement managers reported an increase in cyberattacks on their supply chains in 2025, and 30% of breaches involved a third party in 2025. This proactive approach enables companies to respond swiftly to any deterioration in vendor security ratings.
- Engage Stakeholders: Involve key stakeholders across the organization to ensure alignment and support for the TPRM program. Working together makes management efforts more efficient, as successful TPRM programs necessitate cross-functional consensus on processes and goals. Furthermore, a collective operational perspective among continuity, security, procurement, and operations teams is essential for external resilience.
- Pre-Contract Vendor Due Diligence: Conduct thorough due diligence before engaging with vendors to ensure they meet security and compliance standards. This step is essential in reducing threats linked to external partnerships.
Failure to adopt a structured approach to cybersecurity third party risk management can expose organizations to heightened security threats and compliance risks. Without a robust cybersecurity third party risk management framework, organizations face risks to both their cybersecurity posture and operational integrity in an increasingly interconnected world.
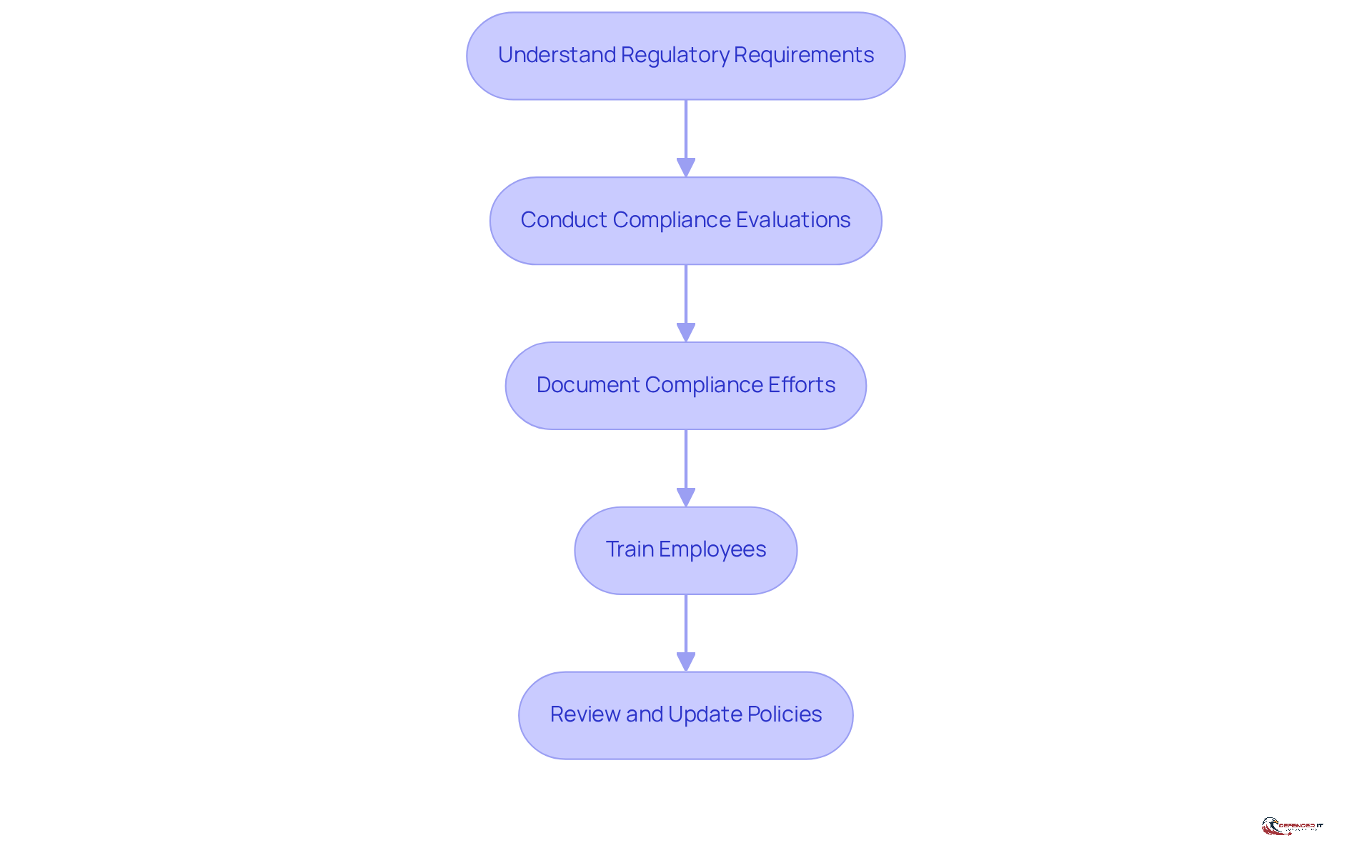
Integrate Compliance into TPRM Strategies
Integrating compliance into cybersecurity third party risk management is not only a regulatory necessity but also a strategic imperative for organizations aiming to safeguard their operations. This integration involves several key actions:
- Understand Regulatory Requirements: Familiarize yourself with relevant regulations that influence external relationships, such as GDPR, HIPAA, or PCI DSS.
- Conduct Compliance Evaluations: It is essential to regularly assess third-party suppliers for adherence to applicable regulations and industry standards.
- Document Compliance Efforts: Maintain comprehensive records of compliance evaluations, vendor contracts, and mitigation strategies to demonstrate due diligence.
- Train Employees: Provide training for employees involved in TPRM to ensure they understand compliance obligations and best practices.
- Review and Update Policies: Regularly review and update TPRM policies to reflect changes in regulations and compliance requirements.
This integration not only mitigates risks but also enhances overall operational efficiency. Ultimately, a proactive approach to cybersecurity third party risk management can be the difference between operational success and costly setbacks.
Highlight Benefits of Effective TPRM Practices
Organizations that neglect cybersecurity third party risk management expose themselves to significant vulnerabilities that can jeopardize their operations and reputation. Implementing effective TPRM practices offers several significant benefits:
- Decreased Threat Exposure: By recognizing and addressing external threats, organizations can lessen their susceptibility to cyberattacks and operational interruptions.
- Enhanced Compliance: A structured TPRM program ensures adherence to regulatory requirements, reducing the likelihood of legal penalties.
- Enhanced Vendor Relationships: Proactive threat management fosters trust and collaboration with vendors, leading to stronger partnerships.
- Enhanced Operational Resilience: Organizations can better endure disruptions by having a clear understanding of their external dependencies and challenges.
- Strengthened Reputation: A commitment to managing third-party challenges enhances a company’s reputation, demonstrating a dedication to security and compliance.
Ultimately, the decision to invest in cybersecurity third party risk management is not merely a matter of compliance; it is a strategic imperative that can safeguard an organization’s future.
Conclusion
Effective cybersecurity third-party risk management (TPRM) is essential for organizations aiming to mitigate vulnerabilities from external vendors and service providers. By systematically identifying, assessing, and mitigating risks associated with third-party relationships, companies can safeguard their operations. This approach not only enhances data security but also ensures regulatory compliance.
Implementing a robust TPRM framework helps prevent data breaches and operational disruptions while fortifying an organization’s reputation in an interconnected digital landscape. The article outlines essential practices for establishing a structured TPRM program, including:
- Defining objectives
- Developing comprehensive policies
- Conducting regular risk assessments
- Integrating compliance into TPRM strategies
Key risks identified include:
- Cybersecurity risks
- Operational risks
- Compliance risks
- Reputational risks
- Financial risks
Each of these requires targeted strategies to mitigate their potential impact. By engaging stakeholders and maintaining continuous monitoring, organizations can enhance their resilience against external threats and foster stronger relationships with their vendors.
Investing in effective third-party risk management is more than just a compliance necessity; it’s a strategic move that can greatly impact an organization’s success. By prioritizing TPRM, organizations can turn potential threats into opportunities for long-term stability and growth. Embracing these best practices leads to a more secure and resilient operational environment, ensuring that organizations are well-equipped to navigate the complexities of third-party relationships.
Frequently Asked Questions
What is Third-Party Risk Management (TPRM)?
Third-Party Risk Management (TPRM) is a systematic process aimed at identifying, assessing, and mitigating risks that arise from interactions with external vendors and service providers. It evaluates how these third-party relationships can affect a company’s operations, data security, and compliance with regulations.
Why is TPRM important for organizations?
TPRM is crucial for organizations that rely on third parties for essential services, as it helps prevent vulnerabilities that could lead to data breaches, operational disruptions, or reputational harm. Without an effective TPRM strategy, organizations risk significant operational and reputational damage.
What are the key risks associated with third-party relationships?
The key risks include:
- Cybersecurity Risks: Potential data breaches or cyberattacks exploiting vulnerabilities in external systems.
- Operational Risks: Service delivery disruptions caused by external failures.
- Compliance Risks: Non-adherence to regulatory requirements by third parties, leading to legal penalties.
- Reputational Risks: Negative incidents involving third parties that can harm an organization’s reputation.
- Financial Risks: Financial instability of a third party leading to service disruptions or increased costs.
What statistics highlight the urgency of addressing third-party cybersecurity risks?
In 2023, 61% of entities reported incidents related to external supplier breaches, emphasizing the need for organizations to address vulnerabilities associated with third-party relationships.
How can organizations mitigate the risks posed by third parties?
Organizations can mitigate risks by conducting thorough evaluations of third-party relationships, developing targeted strategies for TPRM, and ensuring oversight of supplier financial stability, compliance with regulations, and cybersecurity measures.
What are the consequences of not implementing a robust TPRM framework?
Without a robust TPRM framework, organizations may face severe operational disruptions, data breaches, legal penalties, and significant reputational damage.
List of Sources
- Define Third-Party Risk Management (TPRM)
- Why Is Third-Party Risk Management Important in 2026? (https://apexanalytix.com/resources/blog/why-is-third-party-risk-management-important)
- Why Third-Party Risk Is Reshaping Cybersecurity In 2026 (https://cyble.com/knowledge-hub/third-party-risk-is-reshaping-cybersecurity)
- 10 Critical Third-Party Risk Management Challenges in 2026 and How to Mitigate Them (https://processunity.com/resources/blogs/10-critical-third-party-risk-management-challenges-and-how-to-mitigate-them)
- Why Third-Party Risk Is the Biggest Gap in Your Clients’ Security Posture (https://thehackernews.com/2026/04/why-third-party-risk-is-biggest-gap-in.html)
- Why is Third-Party Risk Management Important in 2026? | UpGuard (https://upguard.com/blog/third-party-risk-management-important)
- Identify Key Third-Party Risks
- 8 critical vendor risks to monitor in 2026 – Copla (https://copla.com/blog/third-party-risk-management/8-critical-vendor-risk-types-to-monitor-examples-and-management-strategies)
- 10 Critical Third-Party Risk Management Challenges in 2026 and How to Mitigate Them (https://processunity.com/resources/blogs/10-critical-third-party-risk-management-challenges-and-how-to-mitigate-them)
- 100+ Essential Third-Party Risk Statistics and Trends [2026 Update] (https://secureframe.com/blog/third-party-risk-statistics)
- Why Third-Party Risk Is Reshaping Cybersecurity In 2026 (https://cyble.com/knowledge-hub/third-party-risk-is-reshaping-cybersecurity)
- April 2026 Vendor Management News (https://ncontracts.com/nsight-blog/april-2026-vendor-management-news)
- Establish a Structured TPRM Program
- Creating a Successful Third Party Risk Management Program (https://bitsight.com/learn/tprm/creating-a-successful-third-party-risk-management-program)
- Evolving From Third-Party Risk Management To Third-Party Resilience (https://forbes.com/councils/forbestechcouncil/2026/03/31/evolving-from-third-party-risk-management-to-third-party-resilience)
- Third-Party Risk Management Statistics | 360factors (https://360factors.com/blog/third-party-risk-management-statistics)
- 10 Critical Third-Party Risk Management Challenges in 2026 and How to Mitigate Them (https://processunity.com/resources/blogs/10-critical-third-party-risk-management-challenges-and-how-to-mitigate-them)
- 100+ Essential Third-Party Risk Statistics and Trends [2026 Update] (https://secureframe.com/blog/third-party-risk-statistics)
- Integrate Compliance into TPRM Strategies
- Third-Party Risk Management Statistics Every MSP Should Know in 2026 – Cynomi (https://cynomi.com/blog/third-party-risk-management-statistics-every-msp-should-know-in-2026)
- Why Is Third-Party Risk Management Important in 2026? (https://apexanalytix.com/resources/blog/why-is-third-party-risk-management-important)
- Third-Party Vendor Risk Management: Best Practices for 2026 – Centraleyes (https://centraleyes.com/third-party-vendor-risk-management-best-practices-for-2026)
- Third-Party Risk Management Statistics | 360factors (https://360factors.com/blog/third-party-risk-management-statistics)
- April 2026 Vendor Management News (https://ncontracts.com/nsight-blog/april-2026-vendor-management-news)
- Highlight Benefits of Effective TPRM Practices
- Why is Third-Party Risk Management Important in 2026? | UpGuard (https://upguard.com/blog/third-party-risk-management-important)
- Why Third-Party Risk Is the Biggest Gap in Your Clients’ Security Posture (https://thehackernews.com/2026/04/why-third-party-risk-is-biggest-gap-in.html)
- Industry News 2026 Enhancing Third Party Risk Management Moving from Questionnaire Fatigue to Contextual Assurance (https://isaca.org/resources/news-and-trends/industry-news/2026/enhancing-third-party-risk-management-moving-from-questionnaire-fatigue-to-contextual-assurance)
- The Future of TPRM: 5 Innovations Redefining TPRM in 2026 (https://processunity.com/resources/blogs/the-future-of-tprm-5-innovations-redefining-tprm-in-2026)
- Best Third-Party Risk Management Software Platforms in 2026 (https://riskonnect.com/best-third-party-risk-management-software-platforms-in-2026)