Introduction
In the rapidly changing realm of cybersecurity, proof of concept (PoC) exploits have become essential tools for identifying and addressing system vulnerabilities. These non-destructive demonstrations not only reveal weaknesses but also act as a crucial alert for organizations, prompting them to take immediate action against potential threats.
However, the swift spread of PoC information raises concerns about the risk of exploitation by malicious actors. Thus, organizations face the challenge of balancing their ethical responsibilities with the pressing need for security.
How can they effectively leverage the power of PoC exploits while ensuring they do not inadvertently create a roadmap for cybercriminals?
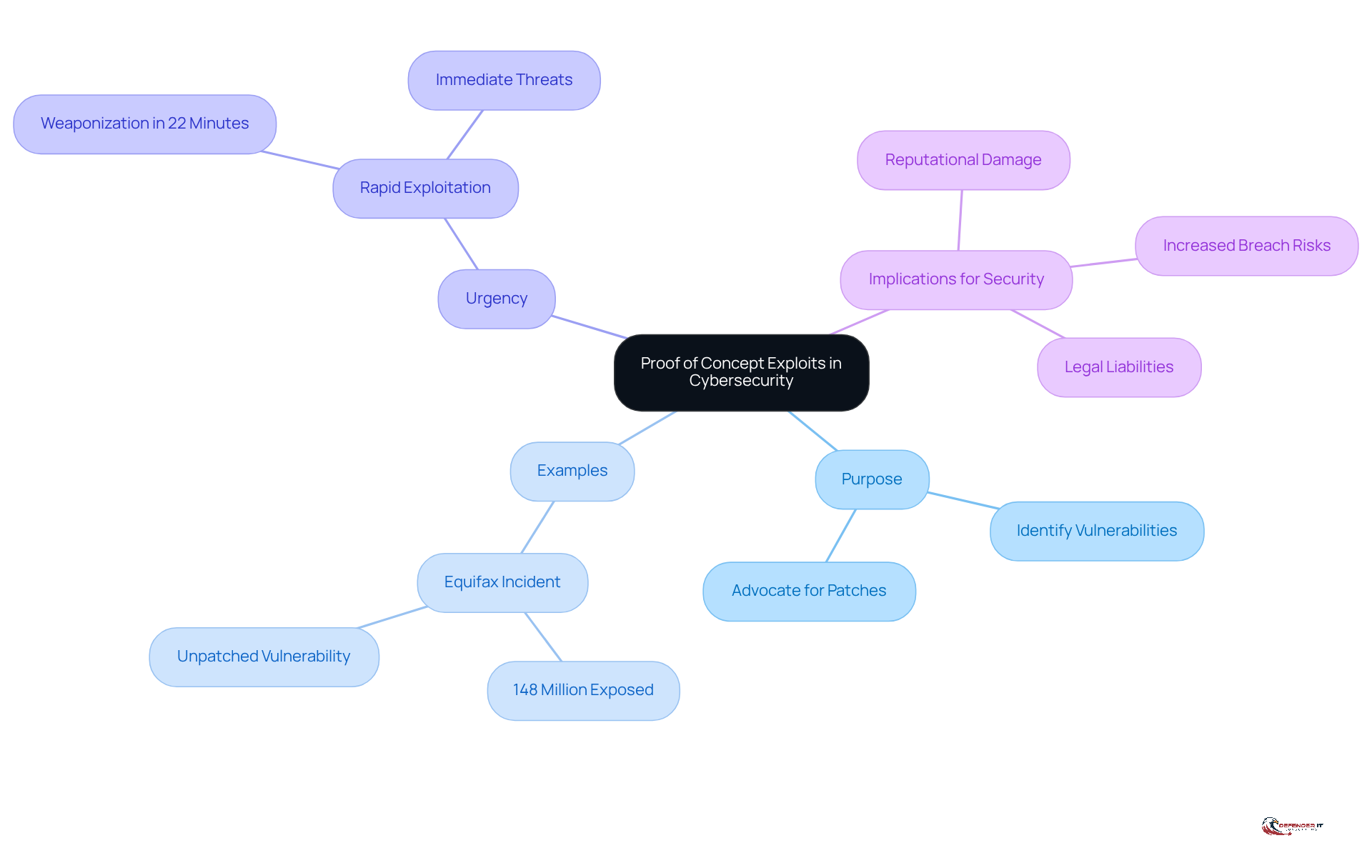
Define Proof of Concept Exploits in Cybersecurity
A proof of concept (PoC) demonstration serves as a vital illustration that confirms the existence of a weakness within a system or application. Unlike conventional attacks that may inflict damage, attacks using a proof of concept exploit are designed to be non-destructive, effectively showcasing how a vulnerability can be exploited. These tools are essential for security professionals, enabling them to identify weaknesses in systems and advocate for necessary patches or improvements. For example, a PoC might consist of a straightforward script that illustrates how an attacker could gain unauthorized access to sensitive data, prompting organizations to implement corrective measures.
The importance of proof of concept exploit attacks in managing vulnerabilities cannot be overstated, especially in 2026, as organizations face increasing pressure to promptly address known issues. High-profile breaches, such as the Equifax incident, which exposed the personal information of 148 million Americans due to an unaddressed vulnerability, underscore the risks associated with delayed responses to PoC disclosures. Moreover, the rapid dissemination of PoC information among cybercriminals can lead to misuse within minutes of publication, with hackers capable of weaponizing a proof of concept exploit in as little as 22 minutes. This urgency necessitates swift action from cybersecurity teams.
Incorporating PoC attacks into risk management strategies not only aids in identifying and addressing vulnerabilities but also fosters a proactive security posture. As experts note, “One of the biggest challenges for companies is the gap between when a proof-of-concept demonstration is published and when a fix is available to address the flaw.” While PoC disclosures aim to accelerate patch development, they also act as a proof of concept exploit for cybercriminals, offering a blueprint for executing attacks if vulnerabilities remain unaddressed. Therefore, understanding and leveraging PoC vulnerabilities is crucial for organizations striving to bolster their cybersecurity resilience.
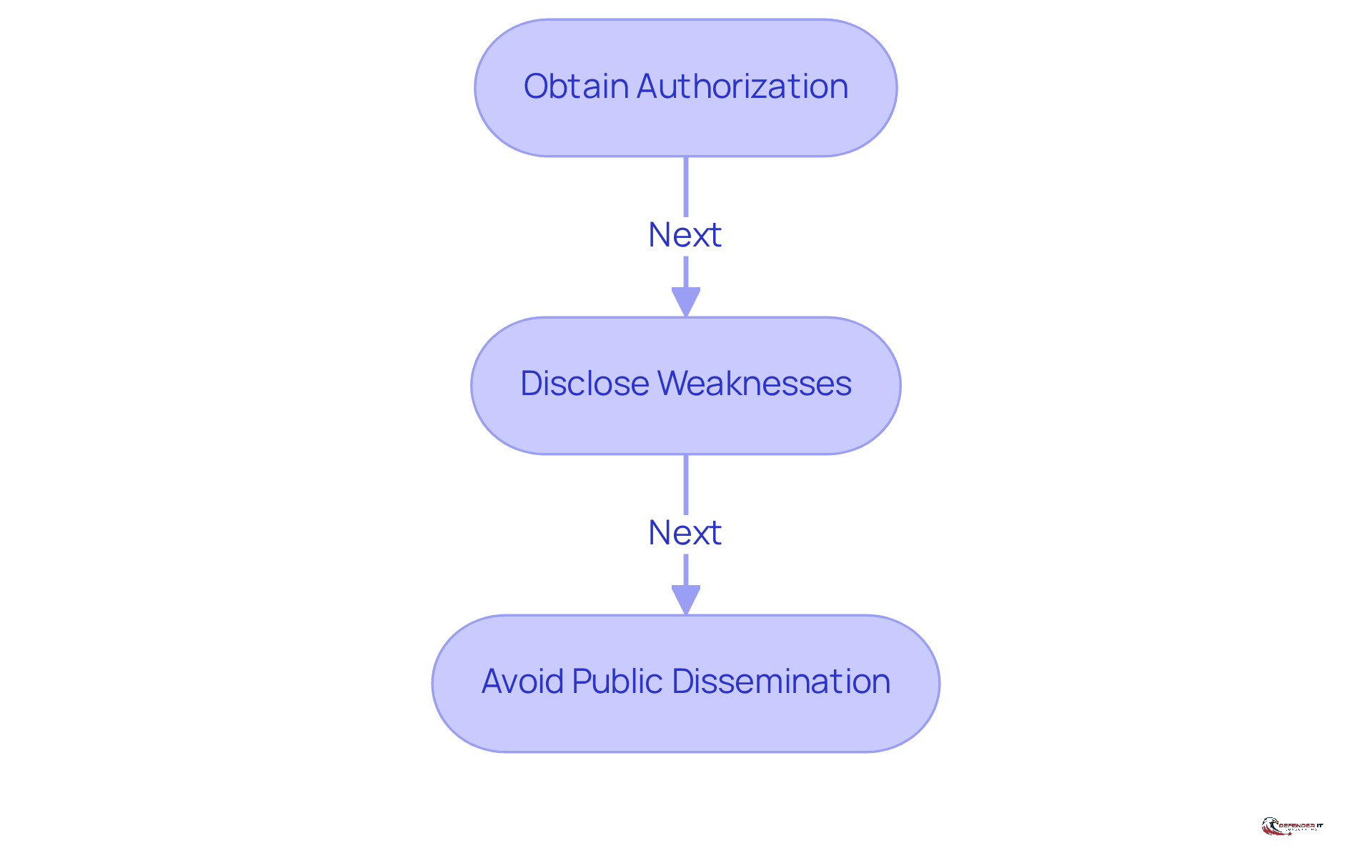
Understand Ethical Responsibilities in Using PoC Exploits
Ethical considerations are crucial when conducting proof of concept demonstrations in cybersecurity. Experts in the field must navigate the fine line between exposing vulnerabilities and preventing their misuse. This requires:
- Obtaining explicit authorization before testing systems
- Responsibly disclosing weaknesses to affected parties
- Avoiding the public dissemination of proof of concept exploit that could be misused by malicious actors
For instance, the responsible disclosure model advocates for researchers to inform vendors of vulnerabilities prior to public announcements. This approach allows sufficient time for the development of necessary patches, thereby enhancing overall security. Adhering to ethical guidelines not only protects organizations but also upholds the integrity of the cybersecurity profession.
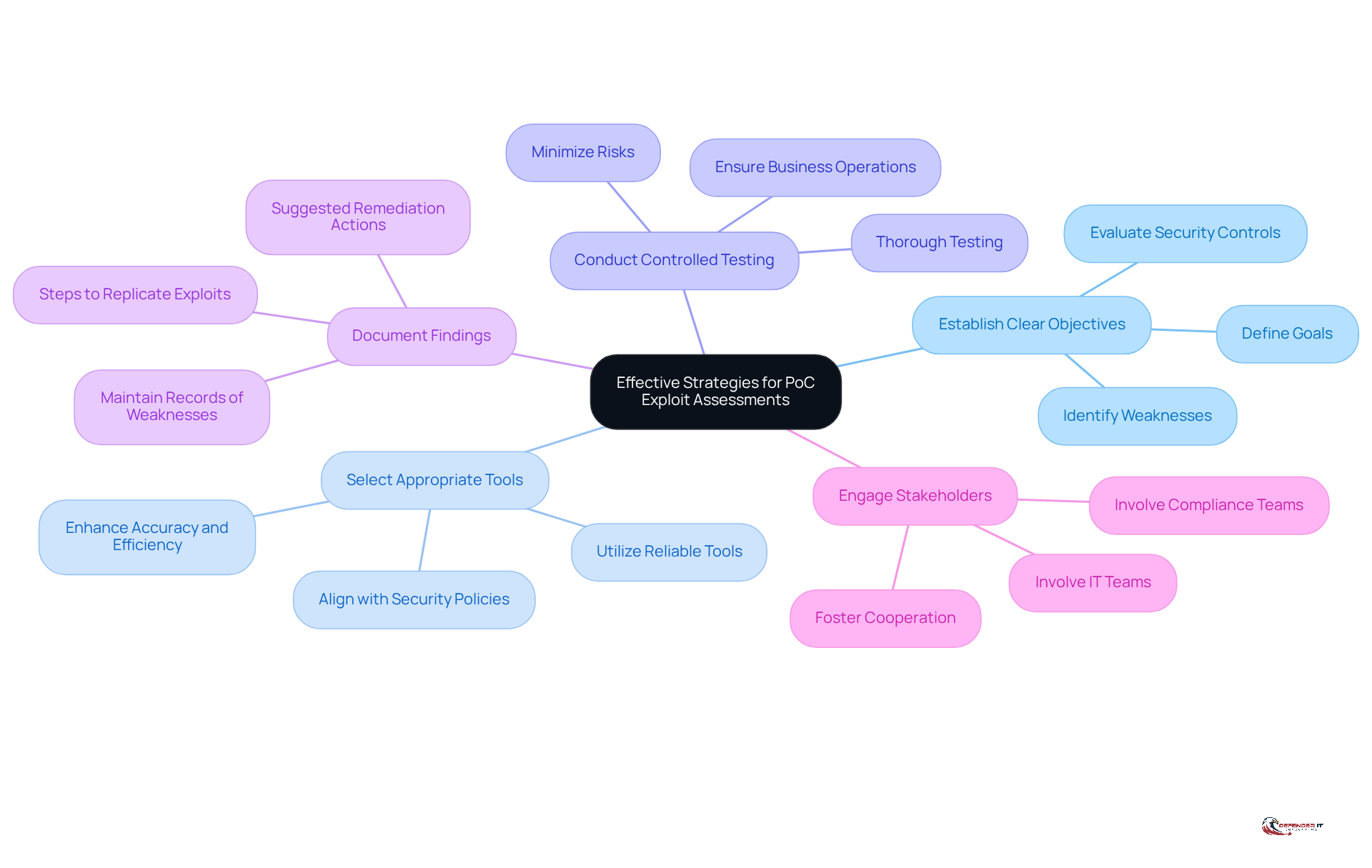
Implement Effective Strategies for PoC Exploit Assessments
To enhance risk management processes, organizations must adopt a structured approach to assessments of proof of concept exploit. This involves several key strategies:
- Establish Clear Objectives: Organizations should define the goals of the assessment, such as identifying specific weaknesses or evaluating the effectiveness of security controls. This clarity allows for focused efforts on critical areas that require attention.
- Select Appropriate Tools: It is essential to utilize reliable tools and frameworks that facilitate the development and execution of proof of concept exploit attacks, ensuring alignment with the organization’s security policies. The right tools can significantly enhance the accuracy and efficiency of assessments.
- Conduct Controlled Testing: Assessments should be performed in a controlled environment to minimize risks, ensuring that testing does not disrupt business operations. Controlled environments enable thorough testing without jeopardizing system integrity.
- Document Findings: Organizations must maintain thorough records of weaknesses discovered through proof of concept exploit, including steps to replicate the proof of concept exploit and suggested remediation actions. Comprehensive documentation is vital for tracking progress and ensuring accountability.
- Engage Stakeholders: Involving relevant stakeholders, including IT and compliance teams, is crucial to ensure that findings are addressed promptly and effectively. Cooperation among departments fosters a cohesive strategy for risk management.
By implementing these strategies, entities can significantly improve their risk management processes and strengthen their overall security posture. The dynamic nature of cyber threats necessitates that organizations remain vigilant and proactive in their security evaluations. Notably, nearly 100 new Proof of Concepts and weaknesses have emerged in the early weeks of 2026, with a total of 678 weaknesses monitored. This highlights the urgency for effective exploit evaluations. Furthermore, with 42 weaknesses [rated as critical under the CVSS v3.1 scoring system](https://thehackernews.com/search/label/PoC Exploit), the importance of these strategies cannot be overstated. As noted by Cyble Vulnerability Intelligence researchers, ‘the year may be a little more than a week old, but threat actors have already gathered nearly 100 Proof of Concepts and newly exploited flaws,’ underscoring the critical need for organizations to adopt robust assessment strategies.
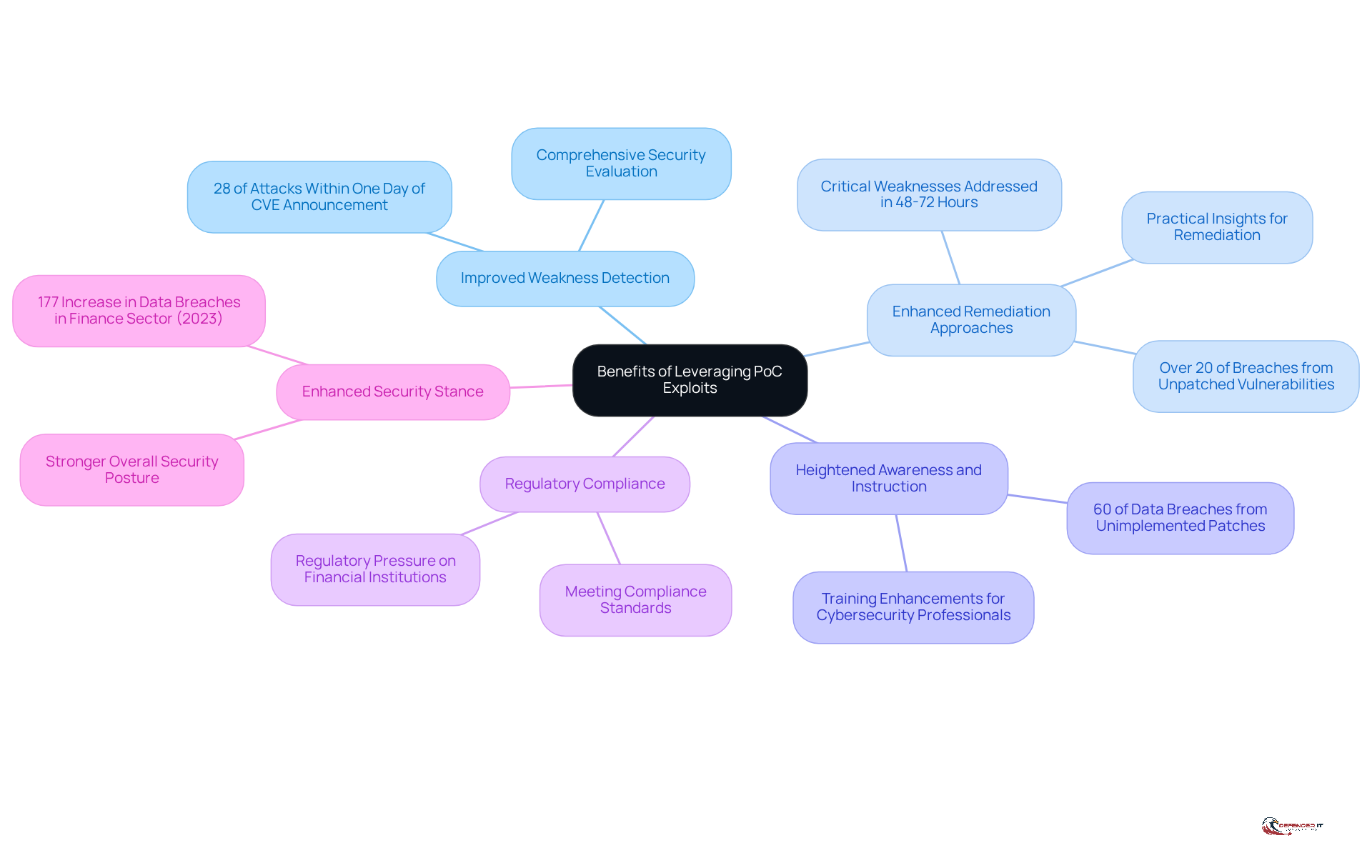
Highlight Benefits of Leveraging PoC Exploits
Leveraging proof of concept (PoC) advantages provides several key benefits for organizations:
- Improved Weakness Detection: PoC methods assist security teams in identifying vulnerabilities that may not be apparent through traditional assessment techniques. This enables a more comprehensive security evaluation. In 2025, approximately 28% of attacks were recorded within one day of a CVE announcement, underscoring the urgency of rapid threat identification and management.
- Enhanced Remediation Approaches: By demonstrating how vulnerabilities can be exploited using a proof of concept exploit, PoC presentations offer practical insights that inform remediation efforts, ensuring that security updates are effective. Organizations that can address critical weaknesses within 48 to 72 hours can prevent most mass exploitation, as these vulnerabilities account for over 20% of breaches.
- Heightened Awareness and Instruction: Utilizing PoC vulnerabilities in training sessions can enhance the skills of cybersecurity professionals, fostering a culture of proactive security awareness within the organization. This is particularly important, given that 60% of data breaches result from the failure to implement known patches, highlighting the necessity for ongoing education.
- Regulatory Compliance: In heavily regulated industries, demonstrating the application of PoC methods can help organizations meet compliance standards by showcasing their commitment to identifying and addressing vulnerabilities. Regulatory pressure is mounting for financial institutions to demonstrate effective vulnerability management, making PoC demonstrations a valuable asset.
- Enhanced Security Stance: Ultimately, the proactive use of PoC vulnerabilities contributes to a stronger overall security posture, mitigating the risk of successful cyber attacks and protecting sensitive data. With the finance sector experiencing a 177% increase in data breaches in 2023, the significance of a robust security strategy cannot be overstated. By recognizing these benefits, organizations can better understand the role of proof of concept exploit in their cybersecurity strategies.
Conclusion
Embracing proof of concept (PoC) exploits is essential for organizations seeking to enhance their cybersecurity defenses. These demonstrations not only reveal vulnerabilities but also act as a catalyst for timely interventions, fostering a more secure digital environment. By understanding and leveraging PoC strategies, organizations can better prepare themselves against the ever-evolving landscape of cyber threats.
The significance of PoC exploits lies in their ability to:
- Identify weaknesses
- Uphold the ethical responsibilities of cybersecurity professionals
- Implement effective assessment strategies
Organizations must act swiftly upon discovering vulnerabilities, as cybercriminals can exploit these weaknesses within minutes. Moreover, the advantages of utilizing PoC methods extend beyond immediate remediation; they also contribute to heightened security awareness and compliance with regulatory standards.
Given the increasing sophistication of cyber threats, adopting proof of concept exploit strategies is not merely advantageous but necessary. Organizations are urged to:
- Implement structured assessment approaches
- Engage stakeholders
- Prioritize ethical considerations
By doing so, they can fortify their security posture and significantly mitigate the risk of data breaches, ultimately safeguarding sensitive information and maintaining trust in their systems.
Frequently Asked Questions
What is a proof of concept (PoC) exploit in cybersecurity?
A proof of concept (PoC) exploit is a demonstration that confirms the existence of a weakness within a system or application. It is designed to be non-destructive, showcasing how a vulnerability can be exploited without causing damage.
How do PoC exploits help security professionals?
PoC exploits are essential tools for security professionals as they help identify weaknesses in systems, prompting necessary patches or improvements to enhance security.
Can you provide an example of a PoC exploit?
An example of a PoC exploit could be a simple script that demonstrates how an attacker could gain unauthorized access to sensitive data, encouraging organizations to implement corrective measures.
Why are PoC exploits particularly important in 2026?
In 2026, the importance of PoC exploits is underscored by the increasing pressure on organizations to address known vulnerabilities promptly, especially after high-profile breaches like the Equifax incident, which exposed personal information due to unaddressed weaknesses.
How quickly can cybercriminals misuse PoC information?
Cybercriminals can weaponize a proof of concept exploit within minutes of its publication, with the capability to do so in as little as 22 minutes.
What role do PoC attacks play in risk management strategies?
Incorporating PoC attacks into risk management strategies helps identify and address vulnerabilities, fostering a proactive security posture within organizations.
What is one of the major challenges associated with PoC disclosures?
One of the biggest challenges is the gap between when a PoC demonstration is published and when a fix is available to address the identified flaw, which can lead to potential exploitation by cybercriminals.
Why is it crucial for organizations to understand PoC vulnerabilities?
Understanding and leveraging PoC vulnerabilities is crucial for organizations striving to enhance their cybersecurity resilience and protect against potential attacks.
List of Sources
- Define Proof of Concept Exploits in Cybersecurity
- BlueHammer: Inside the Windows Zero-Day (https://cyderes.com/howler-cell/windows-zero-day-bluehammer)
- How Hackers Use Proof of Concept Exploits | Blade Technologies (https://bladetechinc.com/news/how-hackers-use-proof-of-concept-exploits)
- Vulnerabilities Statistics 2025: Record CVE Surge (https://deepstrike.io/blog/vulnerability-statistics-2025)
- BlueHammer: Windows zero-day exploit leaked – Help Net Security (https://helpnetsecurity.com/2026/04/08/bluehammer-windows-zero-day-exploit-leaked)
- The Price of Transparency: PoCs, Disclosure and Unsecured Hardware (https://radware.com/blog/threat-intelligence/the-price-of-transparency)
- Understand Ethical Responsibilities in Using PoC Exploits
- How Hackers Use Proof of Concept Exploits | Blade Technologies (https://bladetechinc.com/news/how-hackers-use-proof-of-concept-exploits)
- Coordinated Vulnerability Disclosure Program | CISA (https://cisa.gov/resources-tools/programs/coordinated-vulnerability-disclosure-program)
- Exploits in cybersecurity: Types, examples, and prevention (https://vectra.ai/topics/exploit)
- Responsible vulnerability disclosure in 2025: Why the debate still matters (https://scworld.com/perspective/responsible-vulnerability-disclosure-in-2025-why-the-debate-still-matters)
- What is Responsible Disclosure? | Bugcrowd (https://bugcrowd.com/resources/guide/what-is-responsible-disclosure)
- Implement Effective Strategies for PoC Exploit Assessments
- 678 Vulnerabilities Tracked As Critical CVEs And PoCs Rise (https://cyble.com/blog/678-vulnerabilities-reported-by-cyble)
- Attackers exploit BeyondTrust CVE-2026-1731 within hours of PoC release (https://securityaffairs.com/187962/uncategorized/attackers-exploit-beyondtrust-cve-2026-1731-within-hours-of-poc-release.html)
- PoC Exploit — Latest News, Reports & Analysis | The Hacker News (https://thehackernews.com/search/label/PoC Exploit)
- BeyondTrust Vulnerability Targeted by Hackers Within 24 Hours of PoC Release (https://securityweek.com/beyondtrust-vulnerability-targeted-by-hackers-within-24-hours-of-poc-release)
- PoC Exploit Released for WSUS Vulnerability | Cyber Security News ® posted on the topic | LinkedIn (https://linkedin.com/posts/cybersecurity-news_cybersecuritynews-activity-7385947930568015873-O3xk)
- Highlight Benefits of Leveraging PoC Exploits
- Top Cybersecurity Vulnerability Statistics (https://zerothreat.ai/blog/cybersecurity-vulnerability-statistics)
- Vulnerabilities Statistics 2025: Record CVE Surge (https://deepstrike.io/blog/vulnerability-statistics-2025)
- 9 Quotes that Capture the State of Offensive Security (https://netspi.com/blog/executive-blog/security-industry-trends/quotes-on-the-state-of-offensive-security)
- PoC exploit released for Fortinet 0-Day vulnerability | Cyber Security News ® posted on the topic | LinkedIn (https://linkedin.com/posts/cybersecurity-news_cybersecuritynews-vulnerability-activity-7337689912902594561–QP7)