Introduction
A robust assessment of cloud infrastructure security posture is essential for organizations aiming to protect their digital assets in an increasingly dangerous cyber landscape. With a significant 83% of businesses reporting at least one cloud security breach in recent months, the need for effective risk management strategies has never been more urgent. This article outlines a structured, four-step approach to conducting these assessments, providing organizations with the knowledge necessary to identify vulnerabilities and strengthen their defenses. Given the evolving threats and complex compliance requirements, how can companies ensure they are not only prepared but also resilient against future attacks?
Understand Cloud Infrastructure Security Posture Assessment
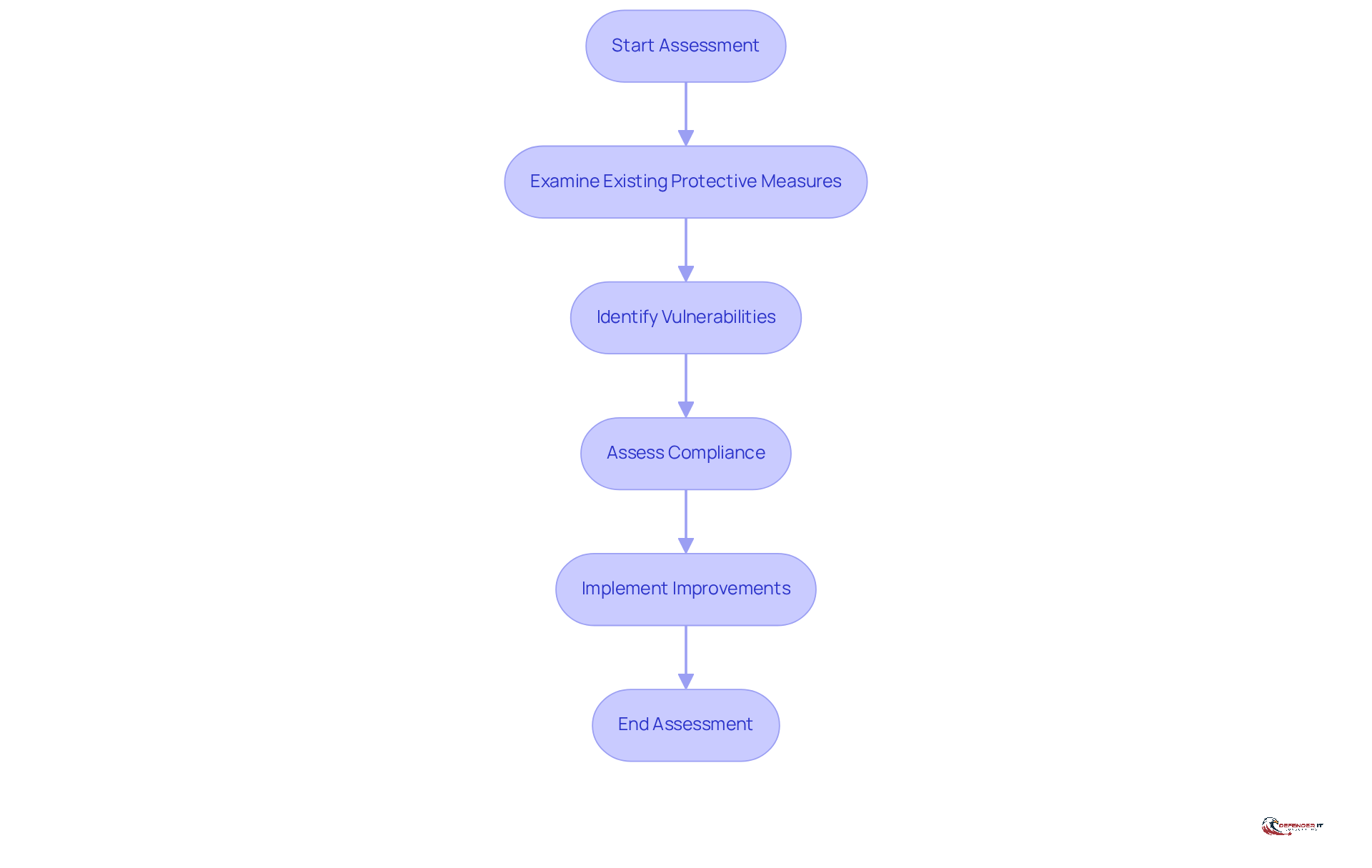
A [cloud infrastructure security posture assessment](https://defenderit.consulting) serves as a critical evaluation of a company’s protective measures, essential for navigating the complexities of today’s cybersecurity landscape. This process involves a thorough examination of existing protective measures, identification of vulnerabilities, and assessment of compliance with relevant regulations. As of 2026, the significance of these evaluations has escalated, with 83% of organizations experiencing at least one breach in the past 18 months. This statistic underscores the urgent need for improved security practices.
Conducting a cloud infrastructure security posture assessment allows businesses to gain a comprehensive understanding of their current security stance, identify critical gaps, and implement necessary improvements. This proactive strategy not only mitigates risks associated with cyber threats but also safeguards sensitive data and ensures compliance with industry standards. For example, organizations that have integrated security tools report substantial enhancements in their ability to detect misconfigurations and validate security controls in real-time, thereby strengthening their overall security posture. These tools are vital in addressing the fact that over 70% of breaches in networks stem from compromised identities, highlighting the necessity for robust identity management.
Moreover, as the threat landscape evolves, the importance of these evaluations cannot be overstated. With human errors accounting for 88% of all security incidents, companies must prioritize the improvement of their cloud protection strategies. The growing trend of adopting centralized platforms to address operational confusion and vulnerabilities further emphasizes the need for comprehensive security assessments. By integrating cloud infrastructure security posture assessment into their protective strategies, organizations can enhance their readiness for emerging threats and maintain a robust defense framework.
Identify Key Areas for Evaluation
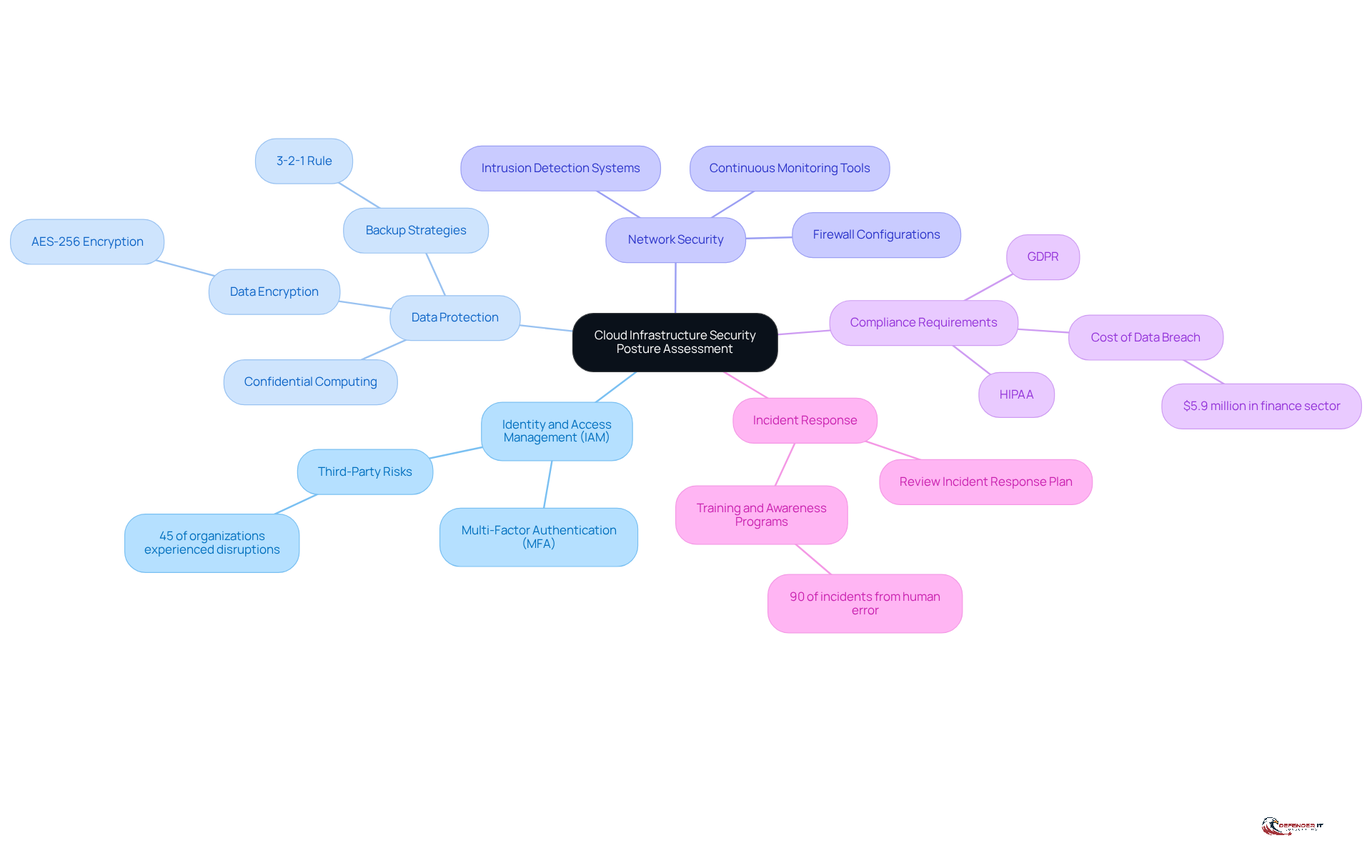
When conducting a security assessment, organizations should focus on several key areas:
- User Identity Management: It is essential to evaluate how user identities are managed and to ensure that access controls are appropriately enforced. Implementing strong authentication measures can significantly reduce the risk of account hijacking, thereby enhancing overall security. Additionally, organizations should assess third-party risks, as 45% of entities have experienced business interruptions related to third parties in the past two years.
- Data Encryption: Organizations must assess the measures in place for data encryption, both at rest and in transit, to safeguard sensitive information. Encryption protocols are crucial for protecting data in online environments. Chris Shyrock emphasizes that effective backup strategies often adhere to the 3-2-1 rule, which involves maintaining multiple copies of data across different storage systems. Furthermore, adopting confidential computing technologies can secure data during processing.
- Network Security: A thorough review of firewall configurations, intrusion detection systems, and network segmentation is necessary to protect against unauthorized access. Continuous monitoring tools play a vital role in detecting suspicious activity and ensuring that potential vulnerabilities are addressed promptly.
- Regulatory Compliance: Identifying relevant regulations, such as GDPR, is critical to ensuring that the cloud infrastructure meets these standards. The average cost of a data breach in the finance sector is $5.9 million, underscoring the financial implications of inadequate data protection measures. Implementing compliance-as-code can streamline the integration of regulatory controls into infrastructure definitions, thereby enhancing audit readiness.
- Incident Response: It is important to review the incident response plan to ensure it is robust and capable of effectively addressing potential breaches. Well-developed incident response programs enable organizations to detect, investigate, and respond swiftly to breaches, minimizing potential damage. Incorporating training and awareness programs is crucial, as 90% of all cyber incidents result from human error or behavior.
By concentrating on these aspects, organizations can perform a cloud infrastructure security posture assessment to gain a comprehensive understanding of their security posture and identify critical weaknesses, ultimately enhancing their resilience against emerging cyber threats.
Conduct the Assessment: Step-by-Step Process
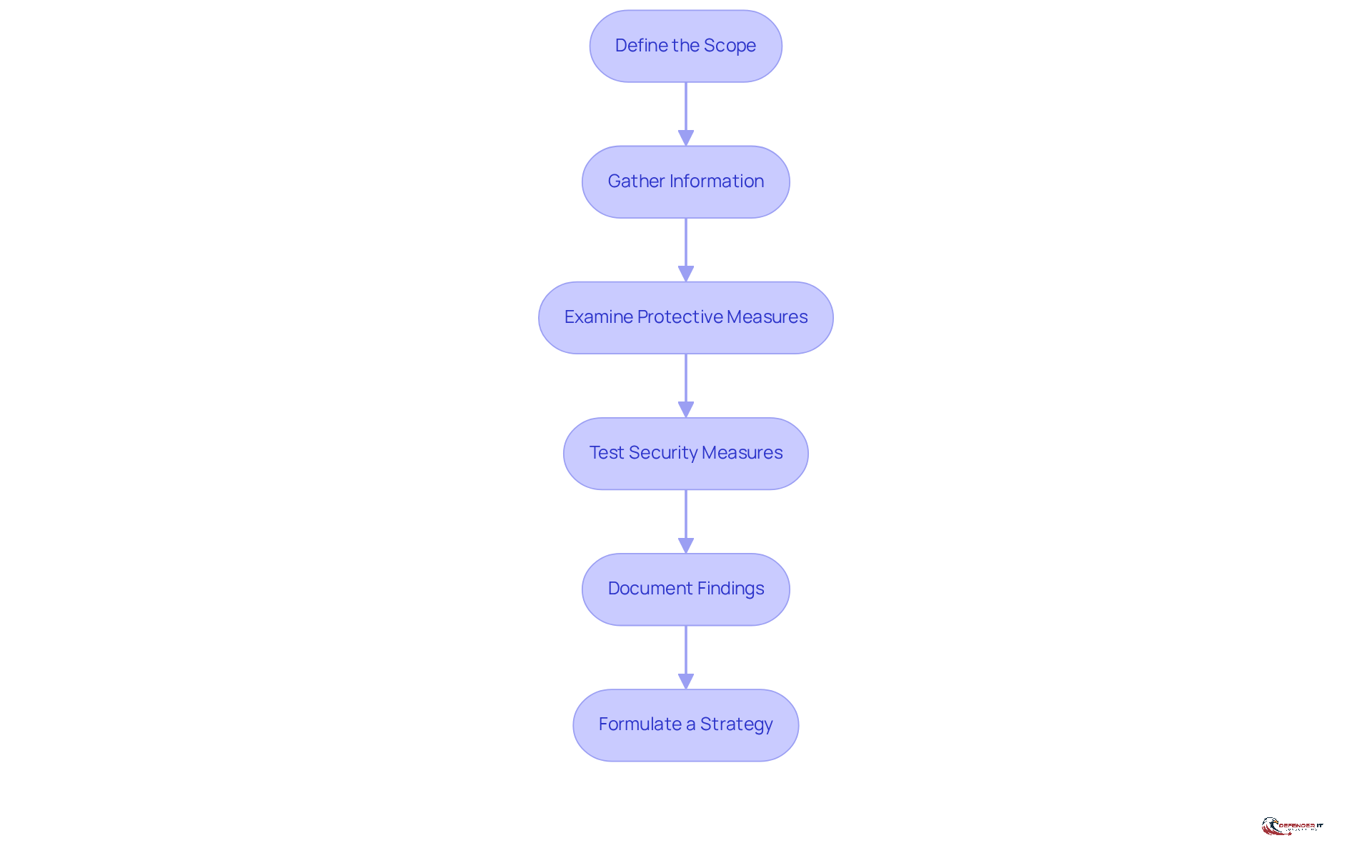
To conduct a security assessment effectively, follow these structured steps:
- Define the Scope: Clearly outline the specific cloud services and components included in the assessment. This focused approach ensures that resources are allocated efficiently and that all critical areas are covered.
- Gather Data: Collect comprehensive data on existing protective measures, configurations, and compliance documentation. This process may involve interviews with key stakeholders and a thorough review of system logs to understand the current safety landscape.
- Examine Protective Measures: Assess the effectiveness of current measures against established industry standards and best practices. Identify any gaps or weaknesses that could expose the organization to risks, as 83% of organizations cite security as their top concern. Regular audits help maintain adherence to both internal and external regulations, enabling timely adjustments to practices.
- Perform Testing: Conduct simulations to simulate potential attacks. This proactive method aids in recognizing exploitable weaknesses, with regular evaluations enhancing security capabilities. The typical expense of a breach in a hybrid cloud setting was $3.61 million, highlighting the monetary motivation for comprehensive evaluations.
- Create Report: Compile a detailed report of the evaluation results, highlighting identified vulnerabilities, compliance gaps, and actionable recommendations for improvement. Proper documentation is crucial for follow-up improvements and compliance maintenance.
- Formulate a Strategy: Utilizing the findings, develop a prioritized strategy to tackle identified problems and improve the overall safety posture. This plan should include remediation steps, timelines, and responsible parties to ensure accountability.
By following these steps, entities can conduct a comprehensive and efficient cloud infrastructure security posture assessment, ultimately lowering the risk of breaches and improving their resilience against evolving cyber threats.
Utilize Tools and Resources for Effective Assessment
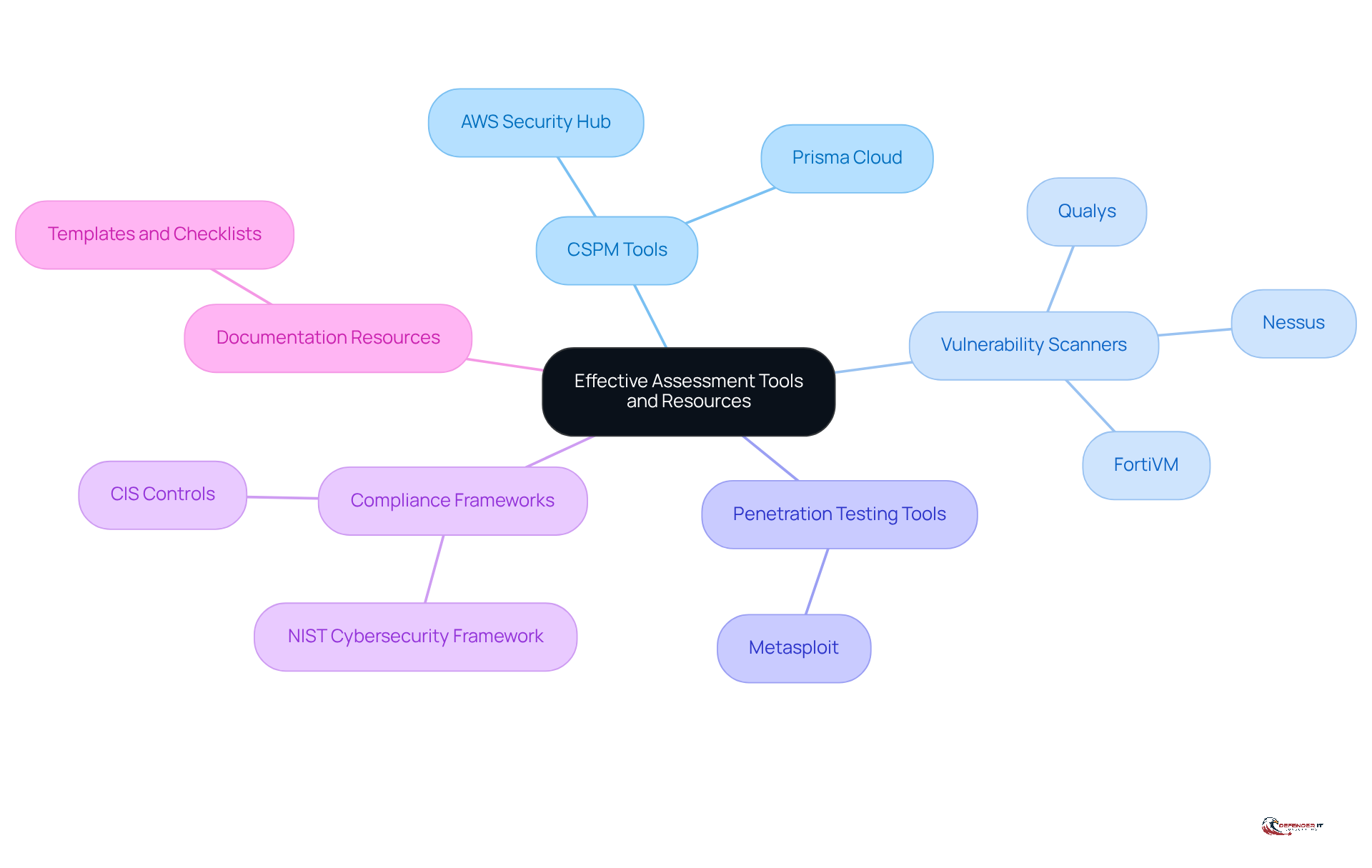
To enhance your security posture, consider utilizing the following tools and resources:
- Security solutions: Solutions such as AWS Security Hub and Prisma Cloud automate the evaluation process by continuously monitoring configurations and compliance. This ensures that protection standards are consistently met. Given that 88% of entities are anticipated to function in cloud environments, the use of CSPM tools is crucial for maintaining robust security across diverse environments.
- Vulnerability detection tools: Tools like Nessus and Qualys are essential for detecting weaknesses within your online infrastructure. These scanners provide an integrated view of vulnerabilities and their risk severity levels, enabling organizations to prioritize remediation effectively. Notably, approximately 45% of all data breaches occur in cloud environments, underscoring the importance of proactive security measures.
- Penetration testing tools: Tools such as Metasploit allow you to simulate attacks, assessing the effectiveness of your protective measures and identifying potential vulnerabilities before they can be exploited. With threat simulation, proactive defense is vital for staying ahead of threats.
- Evaluation frameworks: Established frameworks like the CIS Controls or NIST Cybersecurity Framework can guide your evaluation, ensuring thorough coverage of best practices and alignment with regulatory requirements.
- Standardization resources: Standardizing your evaluation process with templates and checklists from trusted cybersecurity entities can streamline the review and enhance consistency in reporting. The fact that 80% of entities encountered a cloud breach in the past year emphasizes the persistent vulnerabilities that necessitate comprehensive documentation and evaluation processes.
By combining these tools and resources, organizations can conduct a more thorough and efficient cloud infrastructure security posture assessment, ultimately resulting in a stronger security posture. Continuous monitoring and automated assessments are essential in this evolving landscape.
Conclusion
Conducting a thorough cloud infrastructure security posture assessment is essential for organizations seeking to protect their digital assets in an increasingly complex cybersecurity landscape. This assessment not only identifies vulnerabilities but also enhances compliance and strengthens overall security measures against potential breaches. By prioritizing these evaluations, businesses can proactively manage risks and ensure they are prepared to address emerging cyber threats.
Key areas of focus during the assessment include:
- Identity and access management
- Data protection
- Network security
- Compliance requirements
- Incident response strategies
Each of these components plays a crucial role in forming a comprehensive security posture capable of withstanding the challenges posed by evolving threats. Furthermore, leveraging advanced tools and resources such as Cloud Security Posture Management (CSPM) and vulnerability scanners can significantly streamline the evaluation process, ensuring that organizations maintain robust defenses.
Ultimately, the importance of a cloud infrastructure security posture assessment cannot be overstated. As cyber threats continue to escalate, organizations must commit to regular evaluations and enhancements of their security strategies. By doing so, they not only protect sensitive data but also cultivate a culture of security awareness that can mitigate the impact of human error, a leading cause of breaches. Taking action now to implement these assessments will pave the way for a more secure future in the cloud.
Frequently Asked Questions
What is a cloud infrastructure security posture assessment?
A cloud infrastructure security posture assessment is a critical evaluation of a company’s protective measures, aimed at examining existing security practices, identifying vulnerabilities, and assessing compliance with relevant regulations.
Why has the significance of these assessments increased as of 2026?
The significance has increased due to the alarming statistic that 83% of organizations experienced at least one cloud protection breach in the past 18 months, highlighting the urgent need for proactive risk management.
What are the benefits of conducting a cloud infrastructure security posture assessment?
Conducting this assessment helps businesses understand their current security stance, identify critical gaps, implement necessary improvements, mitigate cyber threats, safeguard sensitive data, and ensure compliance with regulatory requirements.
How do automated security validation tools contribute to security posture?
Organizations using automated security validation tools report significant improvements in detecting misconfigurations and validating security controls in real-time, which strengthens their overall security posture.
What percentage of breaches in networks are attributed to compromised identities?
Over 70% of breaches in networks stem from compromised identities, emphasizing the need for robust identity and access management practices.
What role do human errors play in data breaches?
Human errors account for 88% of all data breaches, indicating the importance of continuous assessment and enhancement of cloud protection strategies.
How can organizations enhance their readiness for emerging threats?
By integrating cloud infrastructure security posture assessments into their protective strategies, organizations can improve their defense framework and better prepare for evolving threats.
What trend is emerging in addressing operational confusion and vulnerabilities in cloud security?
There is a growing trend of adopting centralized platforms to manage operational confusion and vulnerabilities, further underscoring the need for comprehensive evaluations.
List of Sources
- Understand Cloud Infrastructure Security Posture Assessment
- The Future of Cloud Security: 7 Key Trends (https://cymulate.com/blog/cloud-security-trends)
- Cloud Security and Compliance Updates Expected in 2026 (https://databank.com/resources/blogs/cloud-security-and-compliance-updates-expected-in-2026)
- 50+ Cloud Security Statistics in 2026 (https://sentinelone.com/cybersecurity-101/cloud-security/cloud-security-statistics)
- What is Security Posture Assessment? A Complete Guide – Cynomi (https://cynomi.com/learn/security-posture-risk-assessment)
- 68 Cloud Security Statistics to Be Aware of in 2026 (https://getastra.com/blog/cloud/cloud-security-statistics)
- Identify Key Areas for Evaluation
- Data Protection Strategies for 2026 (https://hyperproof.io/resource/data-protection-strategies-for-2026)
- Key Cyber Security Statistics for 2026 (https://sentinelone.com/cybersecurity-101/cybersecurity/cyber-security-statistics)
- Data Protection Strategies for 2026 & Beyond: A Practical Roadmap (https://securityboulevard.com/2026/03/data-protection-strategies-for-2026-beyond-a-practical-roadmap)
- Cloud Security and Compliance Updates Expected in 2026 (https://databank.com/resources/blogs/cloud-security-and-compliance-updates-expected-in-2026)
- How Secure Is the Cloud in 2026? Risks, Security Controls, and Best Practices | Cybernews (https://cybernews.com/partner-content/how-secure-is-the-cloud-in-2026-risks-security-controls-and-best-practices)
- Conduct the Assessment: Step-by-Step Process
- 68 Cloud Security Statistics to Be Aware of in 2026 (https://getastra.com/blog/cloud/cloud-security-statistics)
- Cloud Security Assessment: 8-Step Process and Checklist (https://aquasec.com/cloud-native-academy/cspm/cloud-security-assessment)
- Top Cloud Security Statistics: What You Need to Know (https://zerothreat.ai/blog/cloud-security-statistics)
- 9 Quotes that Capture the State of Offensive Security (https://netspi.com/blog/executive-blog/security-industry-trends/quotes-on-the-state-of-offensive-security)
- Cloud Security Assessment Checklist for 2026 (https://sentinelone.com/cybersecurity-101/cloud-security/cloud-security-assessment-checklist)
- Utilize Tools and Resources for Effective Assessment
- 50+ Cloud Security Statistics in 2026 (https://sentinelone.com/cybersecurity-101/cloud-security/cloud-security-statistics)
- 9 Vulnerability Management Tools in 2026 | SentinelOne (https://sentinelone.com/cybersecurity-101/cybersecurity/8-vulnerability-management-tools)
- What is Security Posture Assessment? A Complete Guide – Cynomi (https://cynomi.com/learn/security-posture-risk-assessment)