Introduction
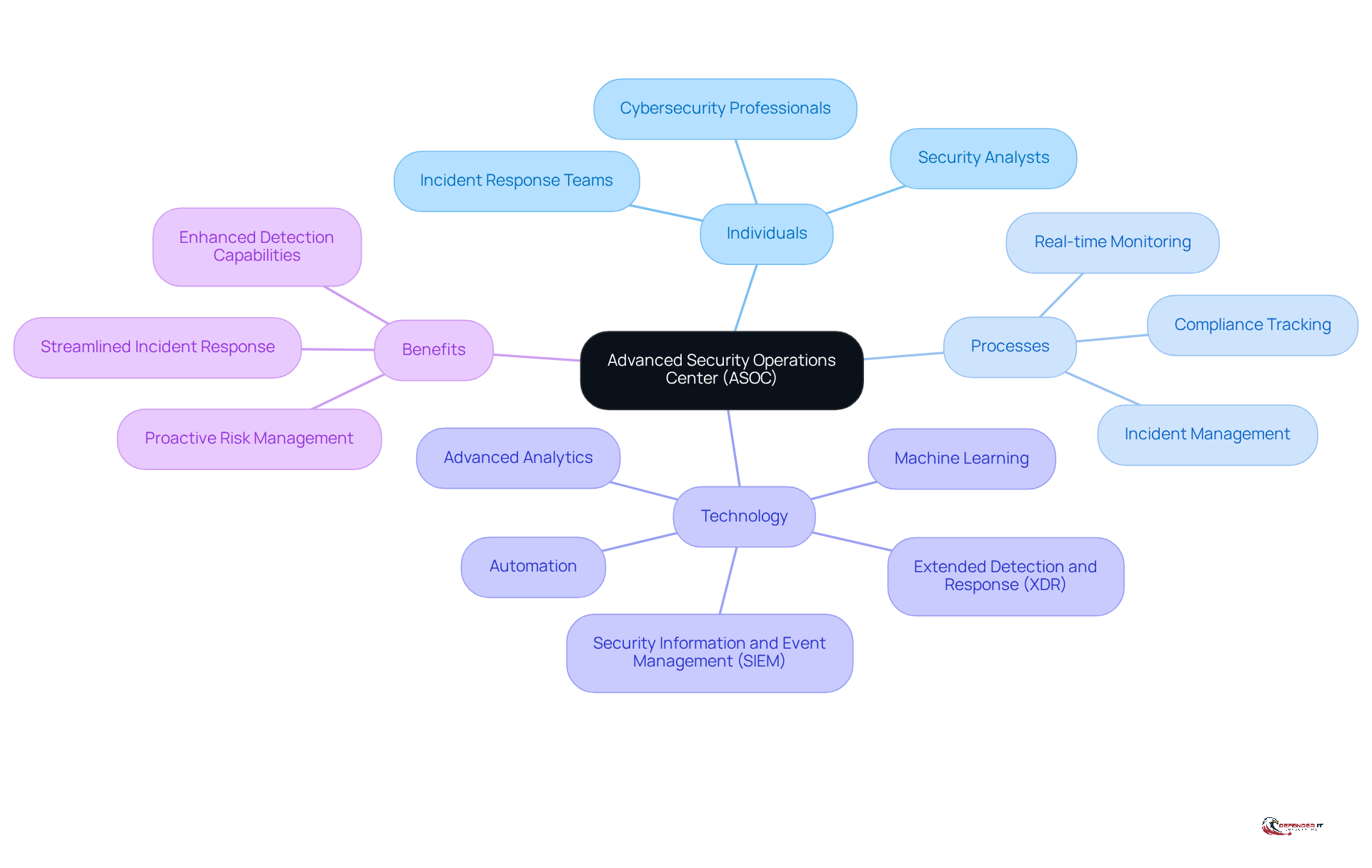
An advanced security operations center (ASOC) signifies a pivotal shift in organizational approaches to cybersecurity, transcending mere technological upgrades. By integrating cutting-edge analytics, machine learning, and automation, ASOCs empower teams to not only respond to threats but also to anticipate them, thereby significantly enhancing overall security.
However, the implementation of these sophisticated systems is not without challenges. Organizations often grapple with issues related to cost, compliance, and the necessity for robust incident response protocols. To optimize an ASOC and ensure it effectively safeguards against the evolving landscape of cyber threats, it is essential to adopt best practices that address these challenges head-on.
Define the Advanced Security Operations Center (ASOC)
An serves as a centralized unit that integrates individuals, processes, and technology to monitor, detect, and respond to in real-time. Unlike conventional security operations centers, advanced security operations centers leverage , machine learning, and automation to and streamline . This proactive approach enables organizations not only to react to events but also to anticipate potential risks, thereby strengthening their .
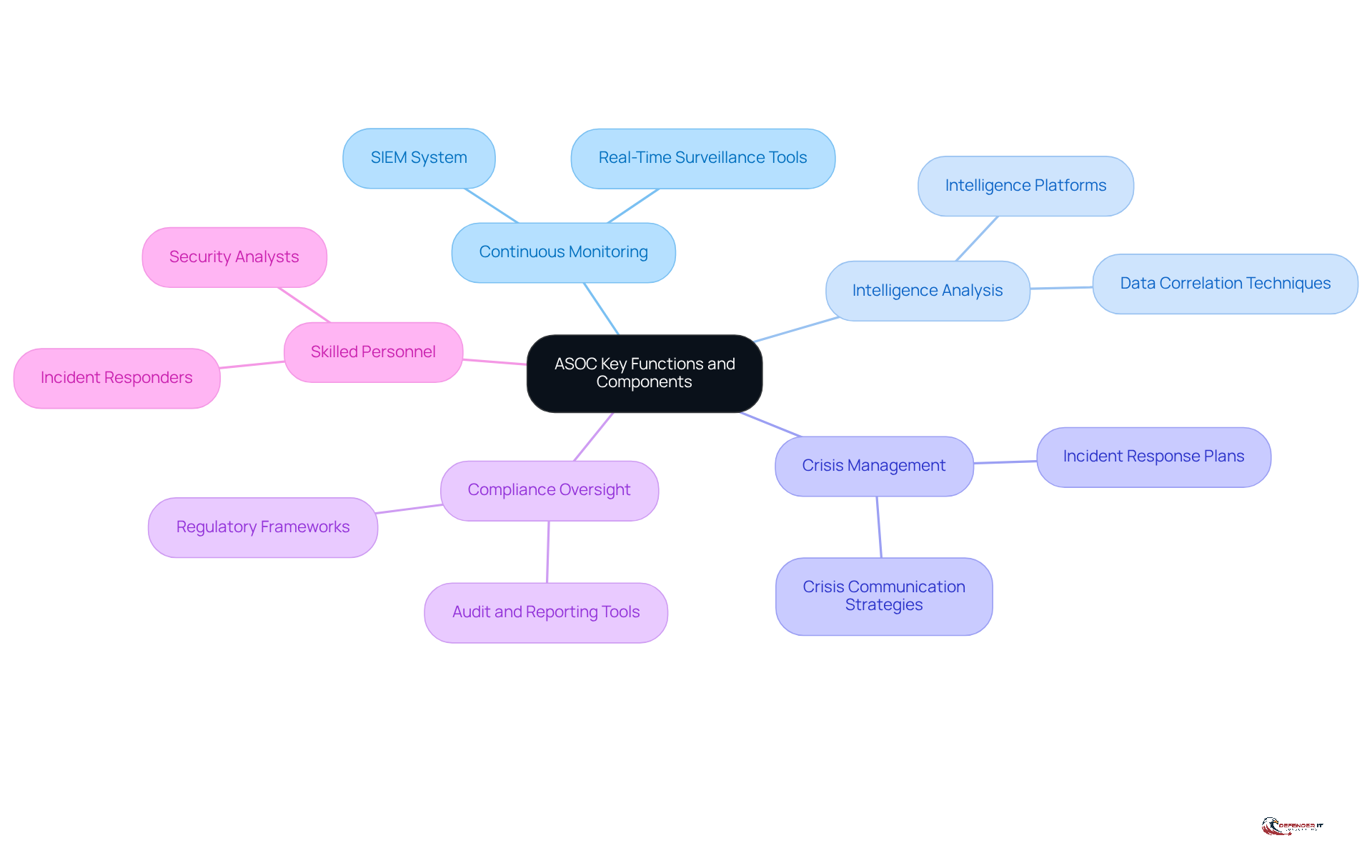
Identify Key Functions and Components of an ASOC
Key functions of an ASOC encompass , intelligence analysis, crisis management, and . Central to these functions are elements such as a , intelligence platforms, management tools, and skilled personnel, including security analysts and responders. By integrating these components, an ASOC can effectively manage , significantly reduce response times, and enhance overall visibility of threats.
For instance, organizations that have adopted report an 81% improvement in detection capabilities, with 84% of these entities experiencing a notable reduction in breaches. A well-implemented SIEM system correlates data from various sources, facilitating the swift identification of anomalies that may signal a security breach. Additionally, platforms like CognitiveSOC™ have proven capable of reducing by 40-60%, while efficiently managing Tier-2 and Tier-3 investigations without overwhelming analysts.
The is projected to grow from USD 12.06 billion in 2026 to USD 20.78 billion by 2031, underscoring its increasing significance within the industry. However, organizations encounter challenges, particularly concerning the primary cost issues for SIEM purchasers, which relate to licensing and log-retention requirements that can substantially affect budgets.
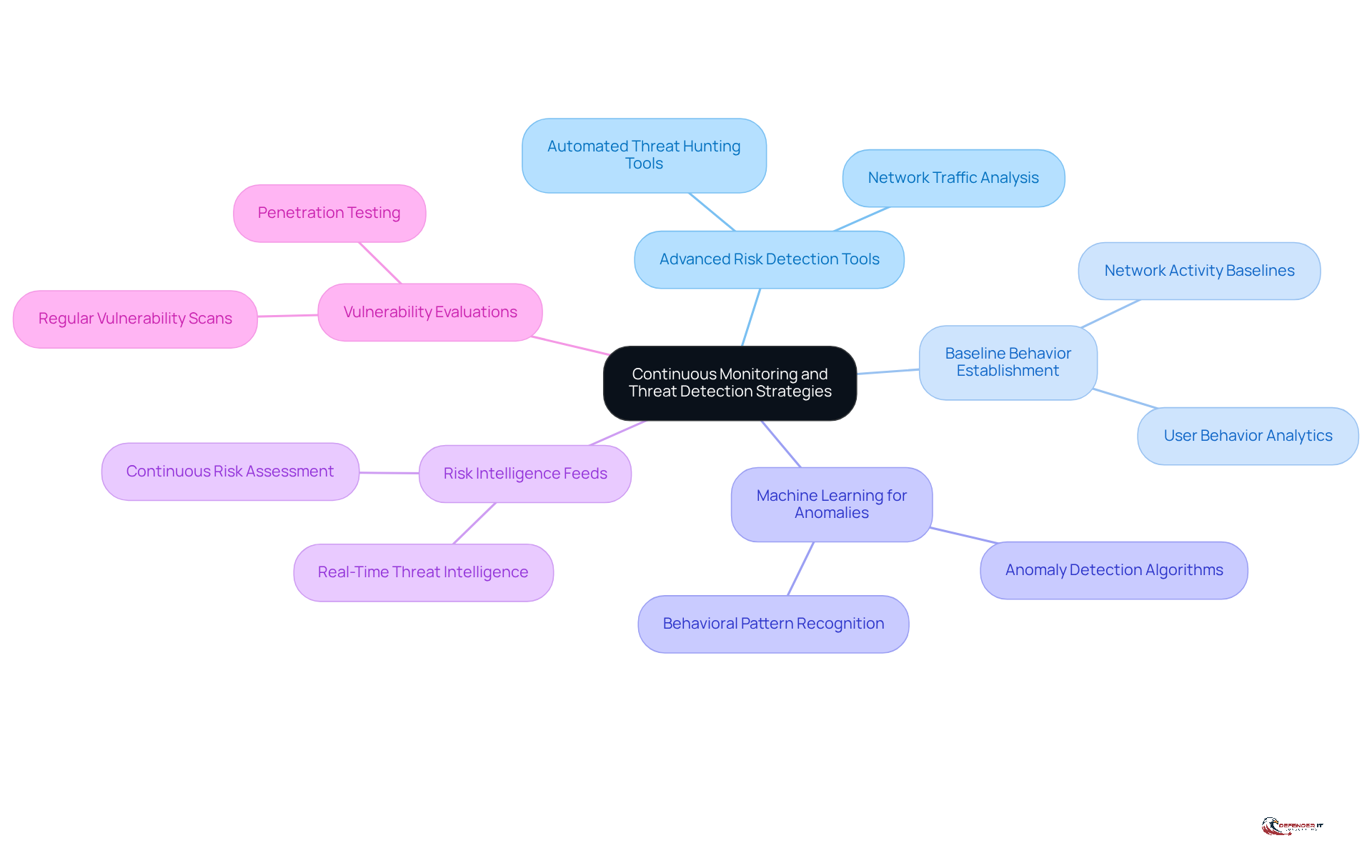
Implement Continuous Monitoring and Threat Detection Strategies
To ensure effective ongoing oversight and risk detection, companies must adopt a multi-layered strategy. This approach includes:
- Deploying
- Establishing
- Utilizing
- Consistently refreshing
- Conducting
These are crucial components of this strategy.
For instance, organizations can implement that continuously analyze network traffic and user behavior. These tools are designed to before they escalate into significant incidents. By integrating these methods, companies can enhance their and .
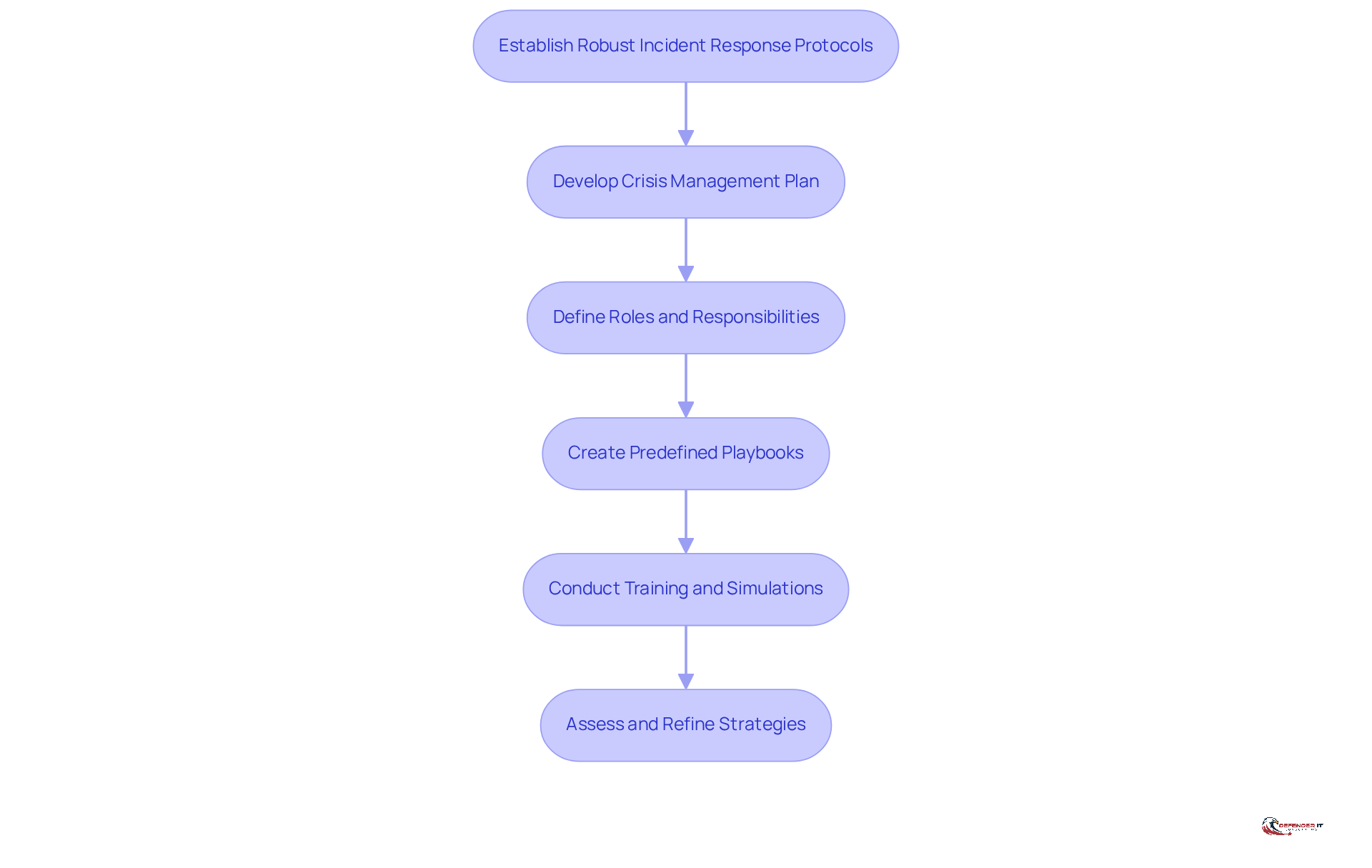
Establish Robust Incident Response Protocols
To establish robust , organizations must develop a comprehensive that clearly delineates roles, responsibilities, and procedures for various situations. This plan should include , such as and , detailing the necessary steps for containment, eradication, and recovery. Consistent training and simulations are essential to ensure that all team members are proficient in their roles during an event. For instance, a financial organization may conduct tabletop drills to rigorously assess their crisis management plan against potential cyber threats, enabling them to identify weaknesses and refine their management strategies.
According to the 2025 Verizon Data Breach Investigations Report, only 55% of companies have a fully documented crisis management plan, underscoring the critical need for organizations to prioritize this aspect of . As Dragos Roșioru, MXDR Team Lead at Heimdal®, states, “A well-crafted response strategy goes beyond mere preparedness.” It equips your team with the to respond swiftly and confidently in high-pressure situations. Such , particularly as the frequency and sophistication of cyberattacks continue to escalate, necessitating during incidents to ensure effective coordination.
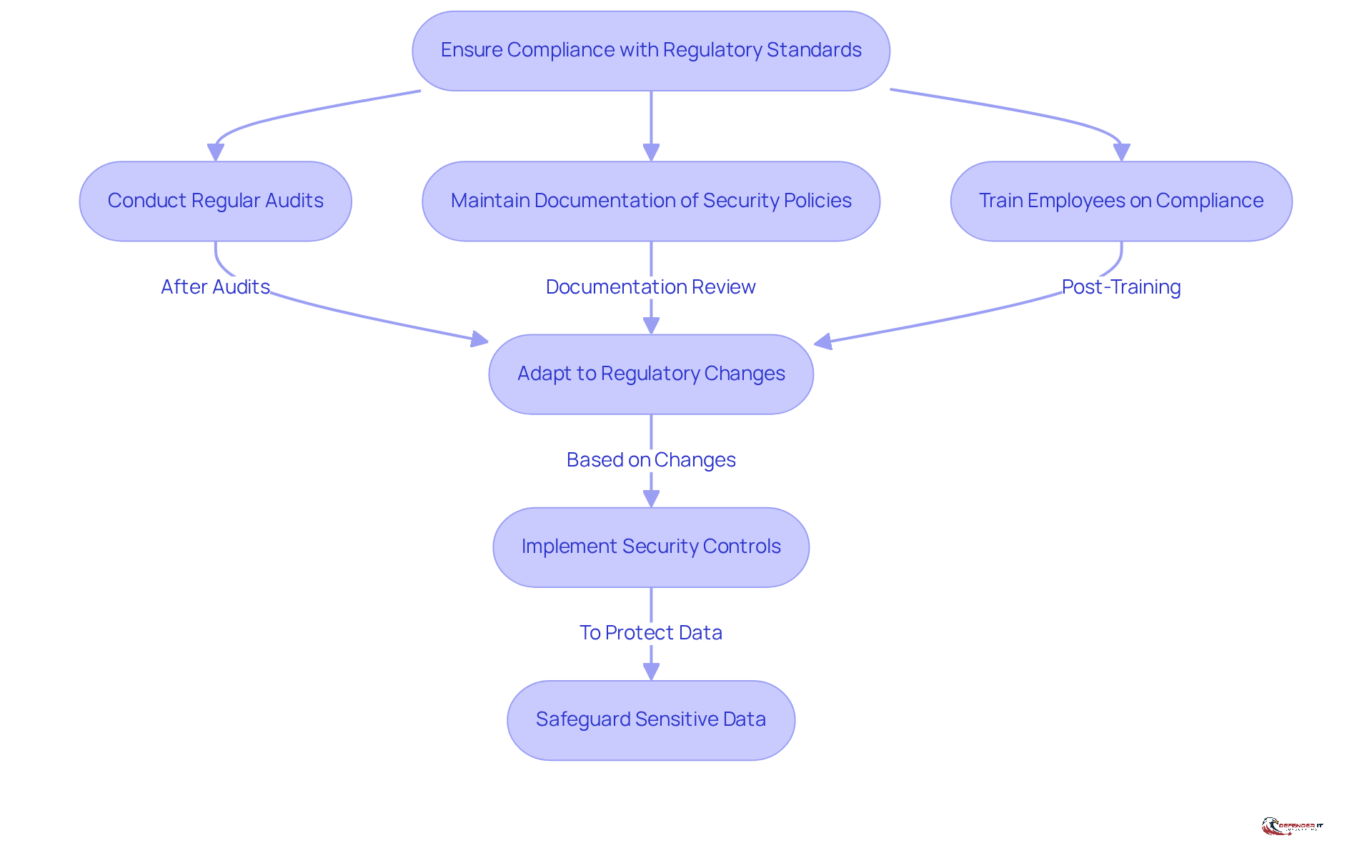
Ensure Compliance with Regulatory Standards and Best Practices
Organizations must prioritize , including GDPR, HIPAA, and , by implementing security controls that fulfill these requirements. This involves:
- Maintaining comprehensive documentation of
- Ensuring that all employees receive
Furthermore, organizations should remain vigilant about changes in regulations and adapt their practices accordingly. For example, a healthcare provider may need to enforce and to adhere to , thereby and mitigating the risk of potential fines.
Conclusion
Establishing an Advanced Security Operations Center (ASOC) is essential for organizations looking to strengthen their cybersecurity posture. By integrating advanced analytics, machine learning, and automation, ASOCs facilitate real-time monitoring and proactive risk management. This enables organizations not only to respond to incidents but also to effectively anticipate potential threats.
Key practices for optimizing an ASOC have been explored throughout this article. These practices include:
- Defining core functions and components such as continuous monitoring
- Threat detection strategies
- Robust incident response protocols
Additionally, the importance of compliance with regulatory standards has been emphasized, underscoring the necessity for organizations to remain vigilant and adapt to evolving regulations.
Ultimately, implementing these best practices is crucial for any organization aiming to fortify its cybersecurity defenses. By prioritizing continuous monitoring, investing in advanced detection tools, and developing comprehensive incident response plans, businesses can confidently navigate the complex landscape of cybersecurity threats. The proactive measures outlined not only safeguard operations but also ensure that organizations remain resilient in the face of an ever-evolving threat landscape.
Frequently Asked Questions
What is an Advanced Security Operations Center (ASOC)?
An ASOC is a centralized unit that integrates individuals, processes, and technology to monitor, detect, and respond to cybersecurity risks in real-time, using advanced analytics, machine learning, and automation.
How does an ASOC differ from a conventional security operations center?
Unlike conventional centers, an ASOC employs advanced technologies to enhance detection capabilities and streamline incident management, allowing organizations to not only react to events but also anticipate potential risks.
What are the key functions of an ASOC?
Key functions include continuous monitoring, intelligence analysis, crisis management, and compliance oversight.
What components are essential for an effective ASOC?
Essential components include a Security Information and Event Management (SIEM) system, intelligence platforms, management tools, and skilled personnel such as security analysts and responders.
How does a SIEM system improve security incident management?
A well-implemented SIEM system correlates data from various sources, facilitating the swift identification of anomalies that may indicate a security breach, thus improving detection capabilities.
What improvements have organizations reported after adopting advanced SIEM solutions?
Organizations report an 81% improvement in detection capabilities and 84% have experienced a notable reduction in breaches.
What is the projected growth of the SIEM market?
The SIEM market is projected to grow from USD 12.06 billion in 2026 to USD 20.78 billion by 2031.
What challenges do organizations face regarding SIEM systems?
Organizations encounter primary cost issues related to licensing and log-retention requirements, which can significantly impact budgets.