Introduction
Manufacturers are facing unprecedented cybersecurity challenges that threaten their operational integrity. Breaches can lead to devastating financial and reputational damage. As organizations grapple with stringent regulatory requirements, the proactive identification of threats becomes not just a necessity but a critical component of operational integrity.
We will discuss four best practices for effective threat hunting services that enhance security posture and ensure compliance in a complex threat landscape:
- Adopt a proactive approach to threat detection.
- Implement continuous monitoring and analysis.
- Foster collaboration between IT and security teams.
- Regularly update and test incident response plans.
Manufacturing firms must adopt proactive strategies to safeguard their assets against evolving cyber threats.
Understand the Importance of Threat Hunting in Regulated Industries
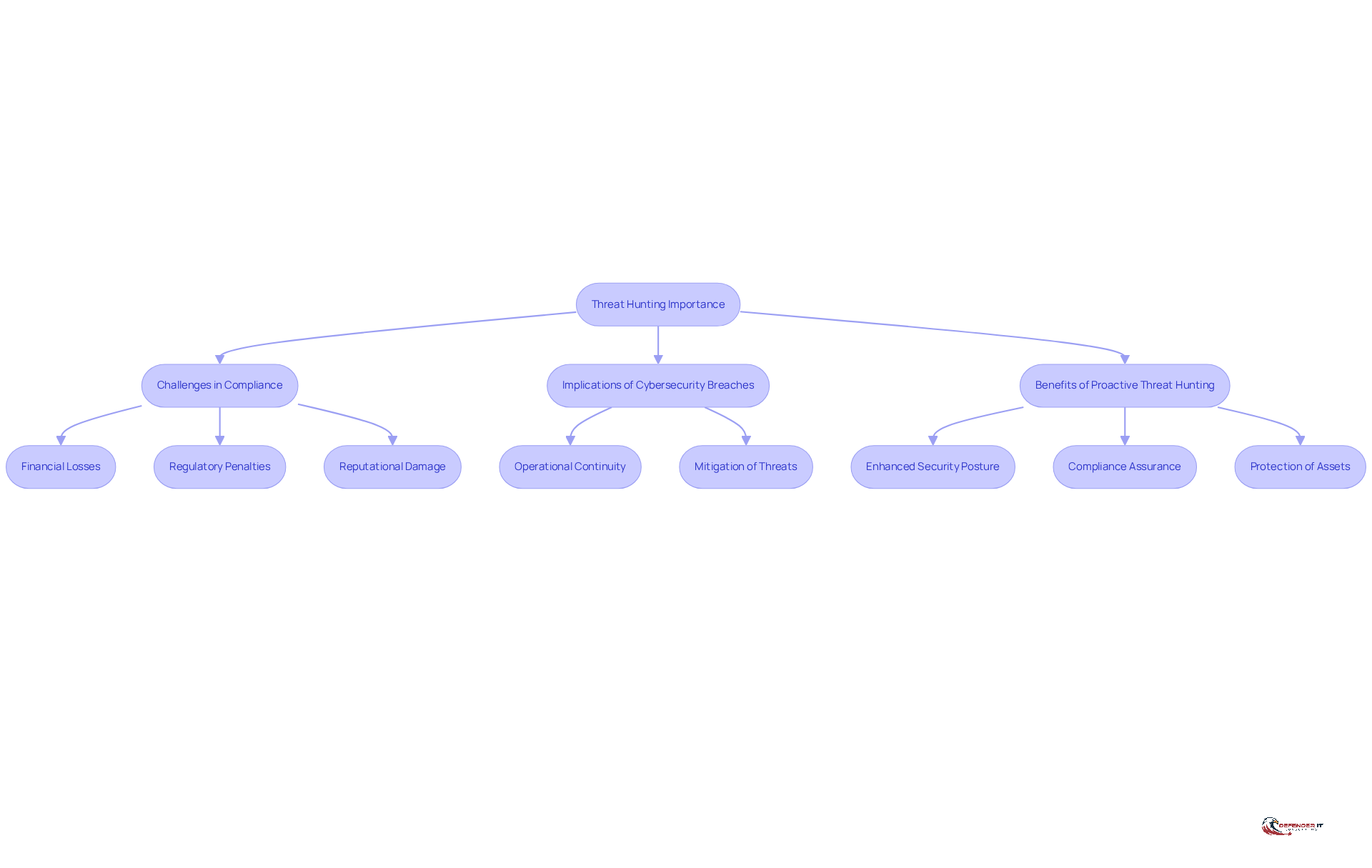
In the production sector, the implications of cybersecurity breaches can be devastating, making compliance with regulations imperative. Organizations face significant challenges in meeting stringent regulatory requirements for data protection. Proactively identifying risks is crucial in this environment, as it helps mitigate potential threats before they cause significant harm.
For instance, a production facility that suffers a cyber attack could face not only financial losses but also regulatory penalties and reputational damage. Neglecting these risks can result in substantial financial losses and harm to reputation.
Implementing an effective threat hunting service enables organizations to bolster their security posture, ensure compliance, and protect their essential assets from evolving cyber threats. This proactive approach is essential for maintaining operational continuity and safeguarding the integrity of manufacturing processes.
Adopt Effective Methodologies for Threat Hunting
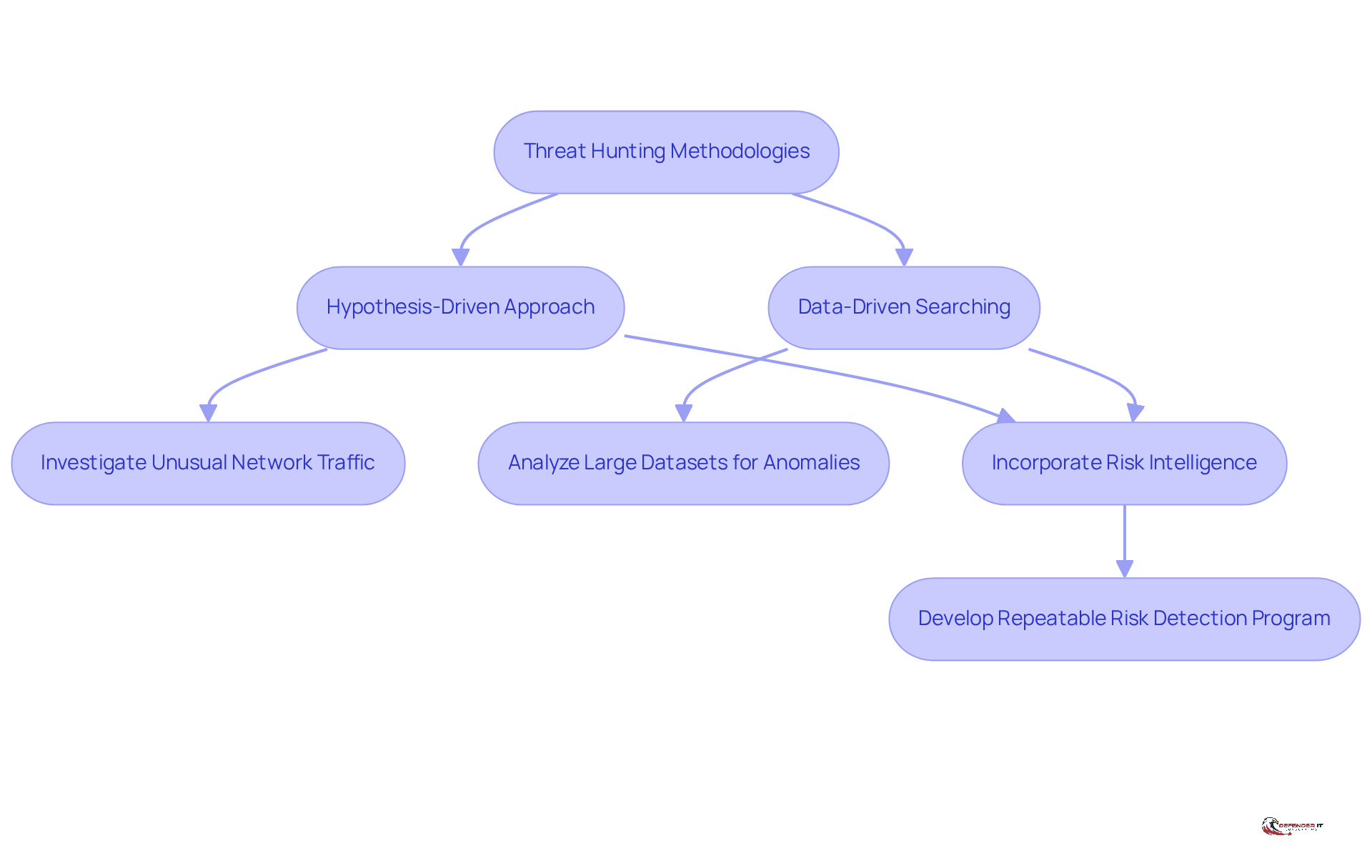
Organizations face challenges in effectively detecting risks due to the evolving nature of threats. A hypothesis-driven approach allows analysts to focus on specific indicators of compromise by formulating hypotheses based on recognized danger patterns. For example, a manufacturing firm might investigate unusual network traffic patterns as a potential sign of a breach. Conversely, data-driven searching involves analyzing large datasets to identify anomalies, which can reveal hidden risks. Incorporating risk intelligence into the search process significantly enhances the capacity to identify advanced dangers, as it offers context and insights into emerging attack vectors.
These structured approaches enable organizations to develop a repeatable and scalable risk detection program that adapts to the evolving threat landscape, thereby enhancing their overall security posture with a threat hunting service.
Invest in Continuous Training and Skill Development for Security Teams
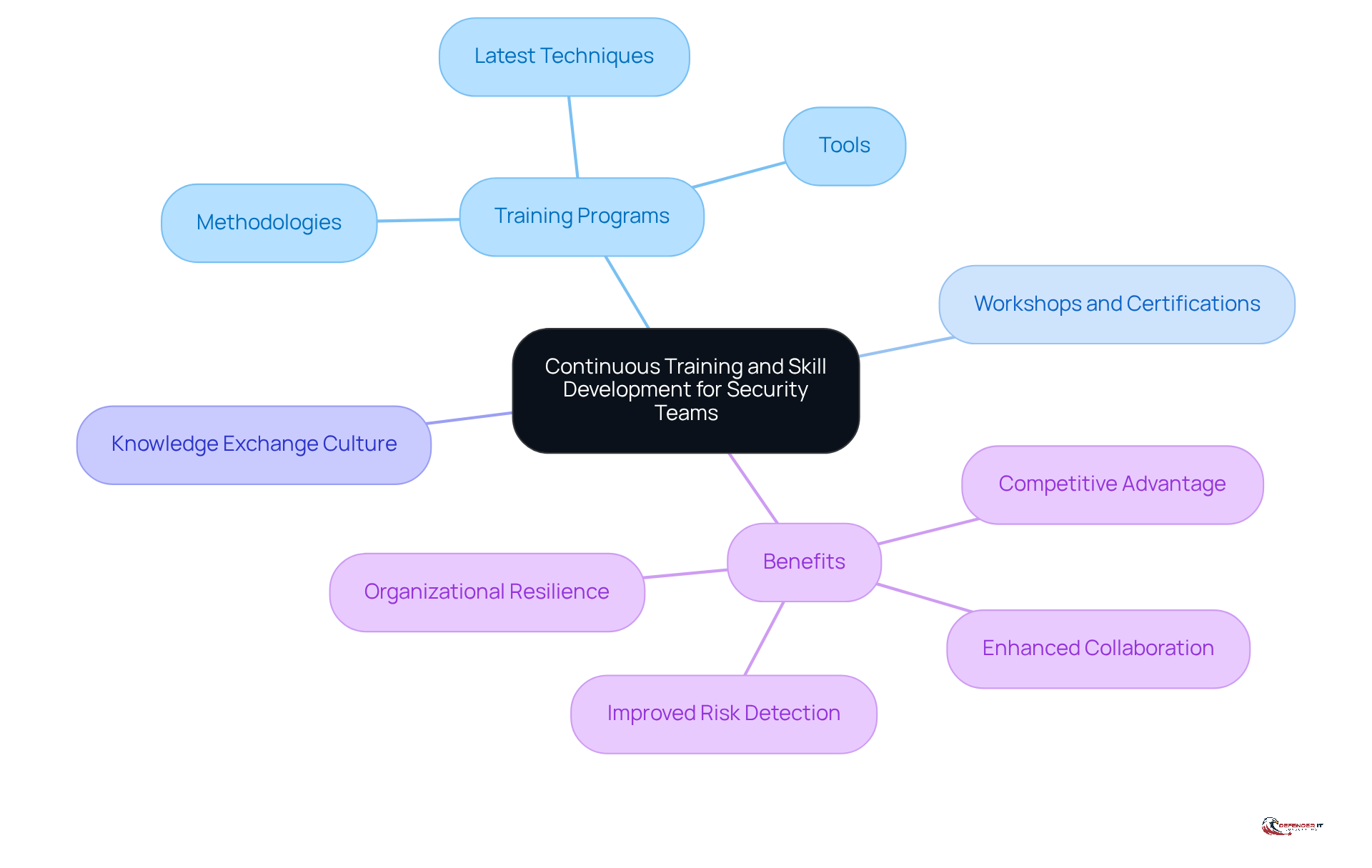
Without continuous training, cybersecurity teams may find themselves ill-equipped to identify emerging risks effectively. Organizations should implement regular training programs that cover the latest risk detection techniques, tools, and methodologies. For example, engaging in workshops or certifications centered on risk detection can greatly improve a team’s skills. Furthermore, cultivating a culture of knowledge exchange within the team can result in enhanced collaboration and innovation in detection strategies. This investment not only enhances risk detection but also positions the organization as a leader in cybersecurity within the manufacturing sector.
Leverage Advanced Technologies and Tools for Enhanced Threat Detection
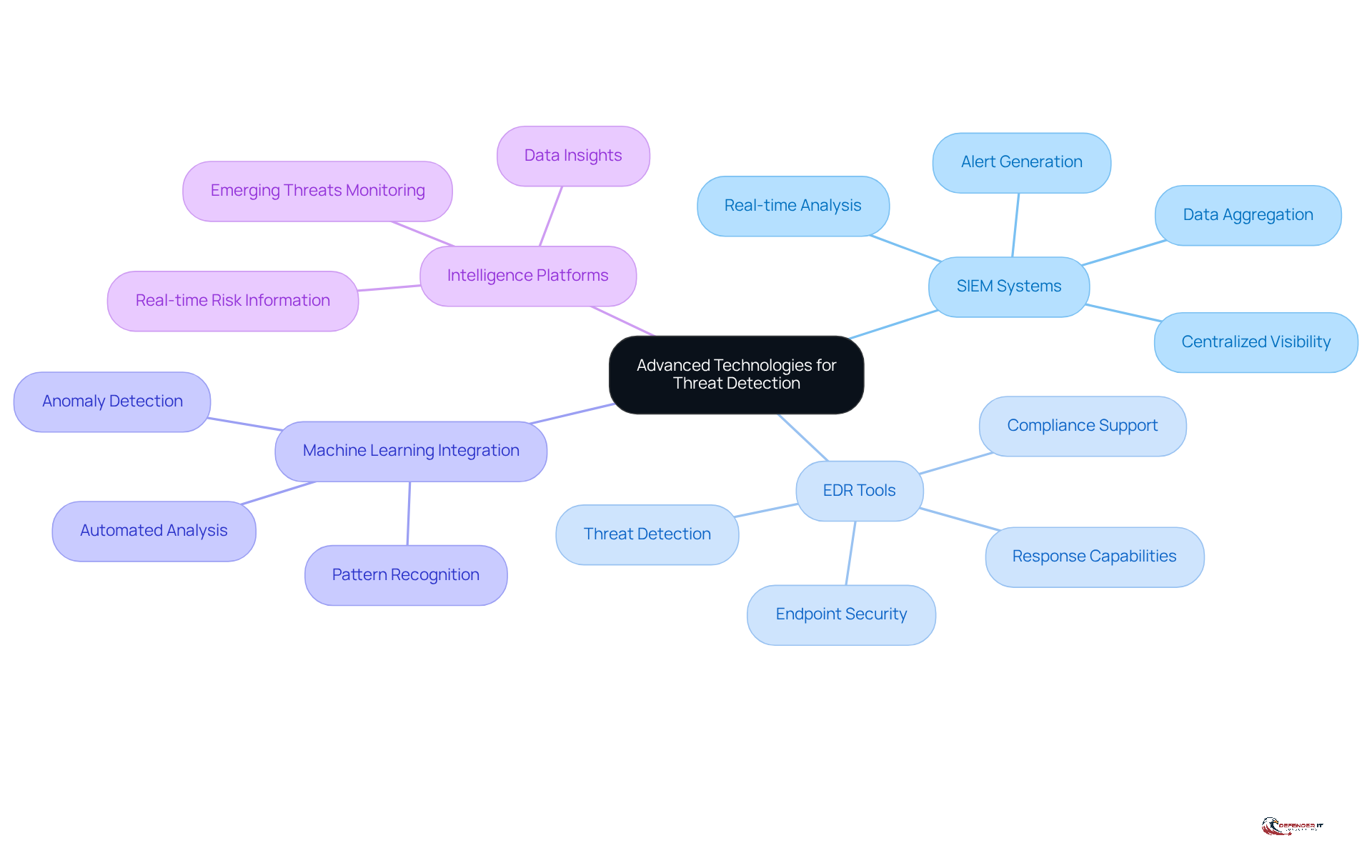
The integration of advanced technologies into risk management is essential for enhancing a company’s capability to detect and respond to cyber threats effectively. Security Information and Event Management (SIEM) systems and Endpoint Detection and Response (EDR) tools play pivotal roles in this effort. SIEM tools aggregate security information from various sources, providing centralized visibility and real-time analysis of network activities. This enables organizations to identify anomalies that may indicate a breach, such as unusual login patterns or unauthorized access attempts. The surge in DDoS attacks presents significant challenges for organizations striving to maintain robust cybersecurity measures.
EDR tools focus on securing endpoints, working directly with user systems to spot and respond to threats. They are designed for sophisticated danger detection and response, significantly lowering the risk of unauthorized access and cybercriminal activities. A notable case is the cyberattack on Jaguar Land Rover, which underscored the urgent need for improved cybersecurity measures in the automotive industry. The incident initiated discussions on enhancing business resilience through effective risk detection strategies.
Moreover, integrating machine learning algorithms can automate the analysis of vast data sets, identifying patterns that suggest potential cyber attacks. For instance, a manufacturing firm may examine production line data to identify anomalies suggestive of a cyber risk. Furthermore, intelligence platforms offer real-time information on emerging risks, enabling entities to stay ahead of possible attacks. Ultimately, the proactive adoption of these technologies can redefine an organization’s approach to cybersecurity, ensuring resilience against evolving threats.
Conclusion
In an era where cyber threats are becoming increasingly sophisticated, the manufacturing sector must prioritize effective threat hunting services to safeguard its operations. A proactive approach not only enhances compliance with stringent regulations but also protects vital assets and ensures operational continuity. Understanding the importance of threat hunting allows organizations to tackle risks before they turn into major breaches.
Key practices discussed include:
- Adopting hypothesis-driven and data-driven methodologies that adapt to the evolving threat environment
- Investing in continuous skill development for security teams
- Leveraging advanced technologies such as SIEM and EDR tools
Each of these elements plays a crucial role in establishing a robust threat detection framework, ensuring that organizations are well-equipped to identify and respond to potential risks effectively.
By prioritizing threat hunting, organizations not only safeguard their assets but also gain a competitive edge in the market. Committing to these best practices enables organizations to protect themselves from cyber threats while fostering a culture of security that enhances trust and reliability in their operations. By embracing these strategies, manufacturing firms can transform their approach to cybersecurity, ensuring resilience against evolving threats and fostering greater trust among stakeholders.
Frequently Asked Questions
Why is threat hunting important in regulated industries?
Threat hunting is crucial in regulated industries because cybersecurity breaches can have devastating implications, including financial losses, regulatory penalties, and reputational damage. Proactively identifying risks helps mitigate potential threats before they cause significant harm.
What challenges do organizations face regarding cybersecurity compliance?
Organizations face significant challenges in meeting stringent regulatory requirements for data protection, which are essential to avoid severe consequences from cyber attacks.
What are the potential consequences of neglecting cybersecurity risks in production facilities?
Neglecting cybersecurity risks can lead to substantial financial losses, regulatory penalties, and damage to an organization’s reputation.
How does implementing a threat hunting service benefit organizations?
Implementing an effective threat hunting service helps organizations enhance their security posture, ensure compliance with regulations, and protect essential assets from evolving cyber threats.
What is the significance of a proactive approach to threat hunting?
A proactive approach to threat hunting is essential for maintaining operational continuity and safeguarding the integrity of manufacturing processes against cyber threats.
List of Sources
- Understand the Importance of Threat Hunting in Regulated Industries
- Threat Landscape Grows Increasingly Dangerous for Manufacturers (https://darkreading.com/cyberattacks-data-breaches/threat-landscape-increasingly-dangerous-manufacturers)
- Cybersecurity Strategies and Best Practices for Manufacturing – Industrial Cyber (https://industrialcyber.co/expert/cybersecurity-strategies-and-best-practices-for-manufacturing)
- Top Cyberthreats in Manufacturing: Ransomware, Skills Gaps, and MDR (https://eset.com/us/business/resource-center/white-papers/top-cybersecurity-in-manufacturing?srsltid=AfmBOooEXimclQUNjjjCXYJODi0y4h4uow6DE2TLJmNvzNe1X3Z8KLJT)
- 7 Key Manufacturing Cybersecurity Trends for 2026 | Huntress (https://huntress.com/blog/manufacturing-cybersecurity-trends)
- 5 ways to protect manufacturing from cyberattacks (https://manufacturingdive.com/news/how-to-protect-your-manufacturing-company-from-cyberattacks/814285)
- Adopt Effective Methodologies for Threat Hunting
- Threat Hunting Methodologies: Techniques and Best Practices (https://sentinelone.com/blog/a-modern-approach-to-adaptive-threat-hunting-methodologies)
- Threat Hunting Methodology: 8 Techniques to Follow (https://bitsight.com/resources/threat-hunting-methodology-8-techniques-follow)
- From Hypothesis to Action: Proactive Threat Hunting with Elastic Security — Elastic Security Labs (https://elastic.co/security-labs/proactive-threat-hunting-with-elastic-security)
- Cybersecurity in Manufacturing: Threats, Trends, and Preparation (https://forescout.com/blog/cybersecurity-in-manufacturing-threats-trends-and-preparation)
- 2025 Threat Hunting Report | Latest Cybersecurity Trends & Insights | CrowdStrike (https://crowdstrike.com/en-us/resources/reports/threat-hunting-report)
- Invest in Continuous Training and Skill Development for Security Teams
- Building Cyber Resilience: How Continuous Training Fortifies Organizational Security | OffSec (https://offsec.com/blog/cyber-resilience-and-continuous-training)
- Why Cybersecurity Training is the Smartest Investment for Organization in 2026 (https://uscsinstitute.org/cybersecurity-insights/blog/why-cybersecurity-training-is-the-smartest-investment-for-organization-in-2026)
- Global cybersecurity training use by type 2024| Statista (https://statista.com/statistics/1376495/cybersecurity-training-use-employees-worldwide-by-type?srsltid=AfmBOoqxOyFT8ODU0zhFUz7Vm3nxKQ9Gi2JNEltcz9A8MG9H9gqGS1nZ)
- Why Continuous Learning is Key to Strengthening Cyber Teams – Circadence (https://circadence.com/blog/continuous-learning-key-strengthening-cyber-teams)
- Security Awareness Training Statistics 2025 [100+ Studies] | Brightside AI Blog (https://brside.com/blog/security-awareness-training-statistics-2025-100-studies)
- Leverage Advanced Technologies and Tools for Enhanced Threat Detection
- 2026 Will Be a Breakthrough Year for Cyberthreats: Four Predictions for Manufacturers (https://ien.com/redzone/blog/22958566/2026-will-be-a-breakthrough-year-for-cyberthreats-four-predictions-for-manufacturers)
- Cybersecurity 2026: AI, CISA, manufacturing sector all in the hot seat (https://cybersecuritydive.com/news/cyber-trends-outlook-2026/810708)
- Introducing the 2026 Cloudflare Threat Report (https://blog.cloudflare.com/2026-threat-report)
- EDR vs. SIEM | Huntress (https://huntress.com/edr-guide/edr-vs-siem)
- 7 Key Manufacturing Cybersecurity Trends for 2026 | Huntress (https://huntress.com/blog/manufacturing-cybersecurity-trends)