Introduction
In today’s landscape, selecting the appropriate cybersecurity advisory services is essential, given the increasing sophistication and prevalence of digital threats. Organizations can achieve not only improved security measures but also customized solutions that cater to their specific operational requirements. Yet, with numerous options at their disposal, how can organizations identify which providers will genuinely strengthen their defenses and offer continuous support? This article explores best practices for choosing cybersecurity consulting services, providing insights that assist organizations in navigating this intricate environment and effectively protecting their digital assets.
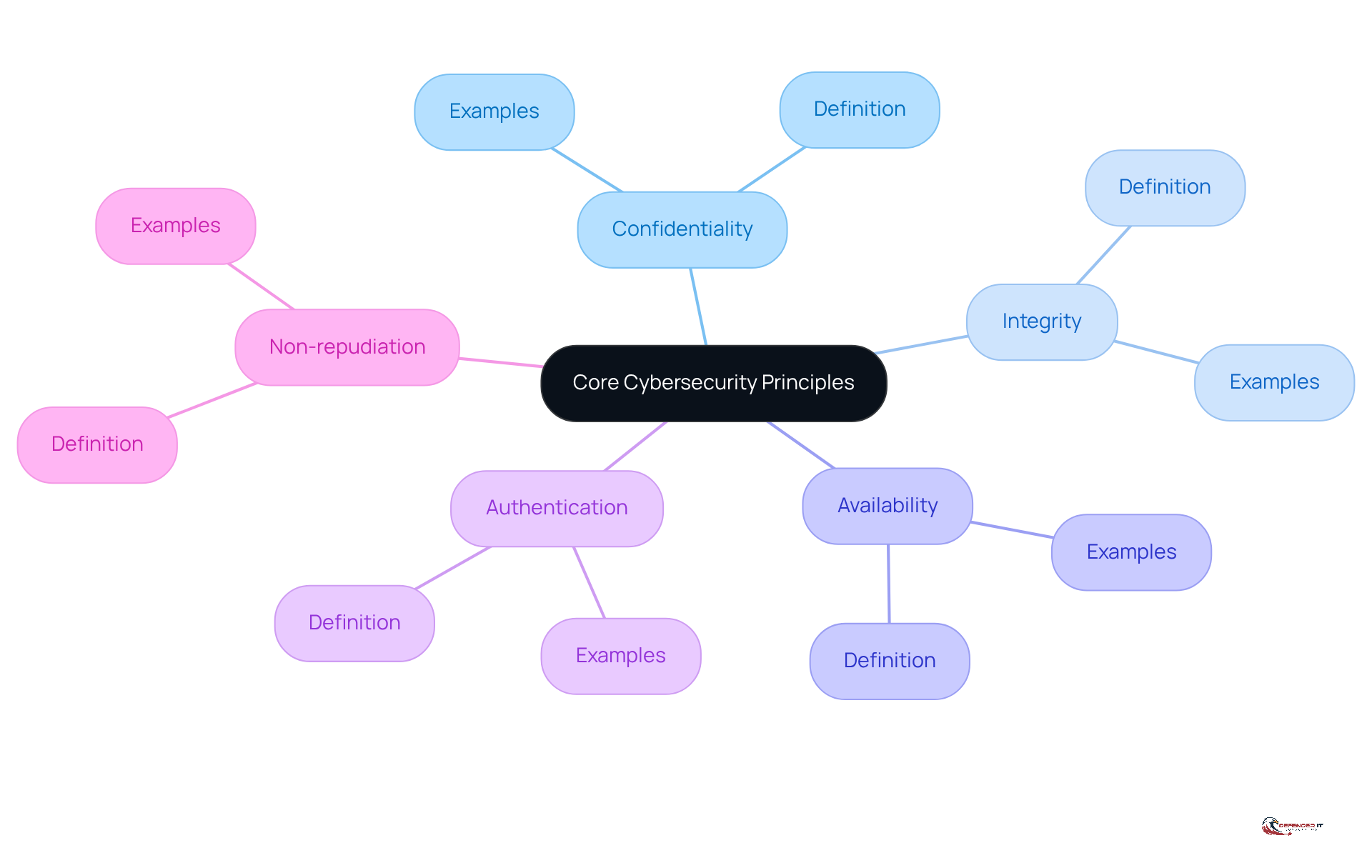
Understand Core Cybersecurity Principles
To effectively select , entities must first grasp the . These concepts include:
- Confidentiality: This principle ensures that is accessible only to those authorized to have access.
- Integrity: It involves , thereby preventing unauthorized modifications.
- Availability: This ensures that information and resources are accessible to authorized users when needed.
- Authentication: This process verifies the identity of users and systems to prevent unauthorized access.
- Non-repudiation: This principle ensures that actions or transactions can be verified and attributed to the correct parties.
By understanding these principles, entities can better assess the efficacy of potential consulting options and ensure alignment with their security goals.
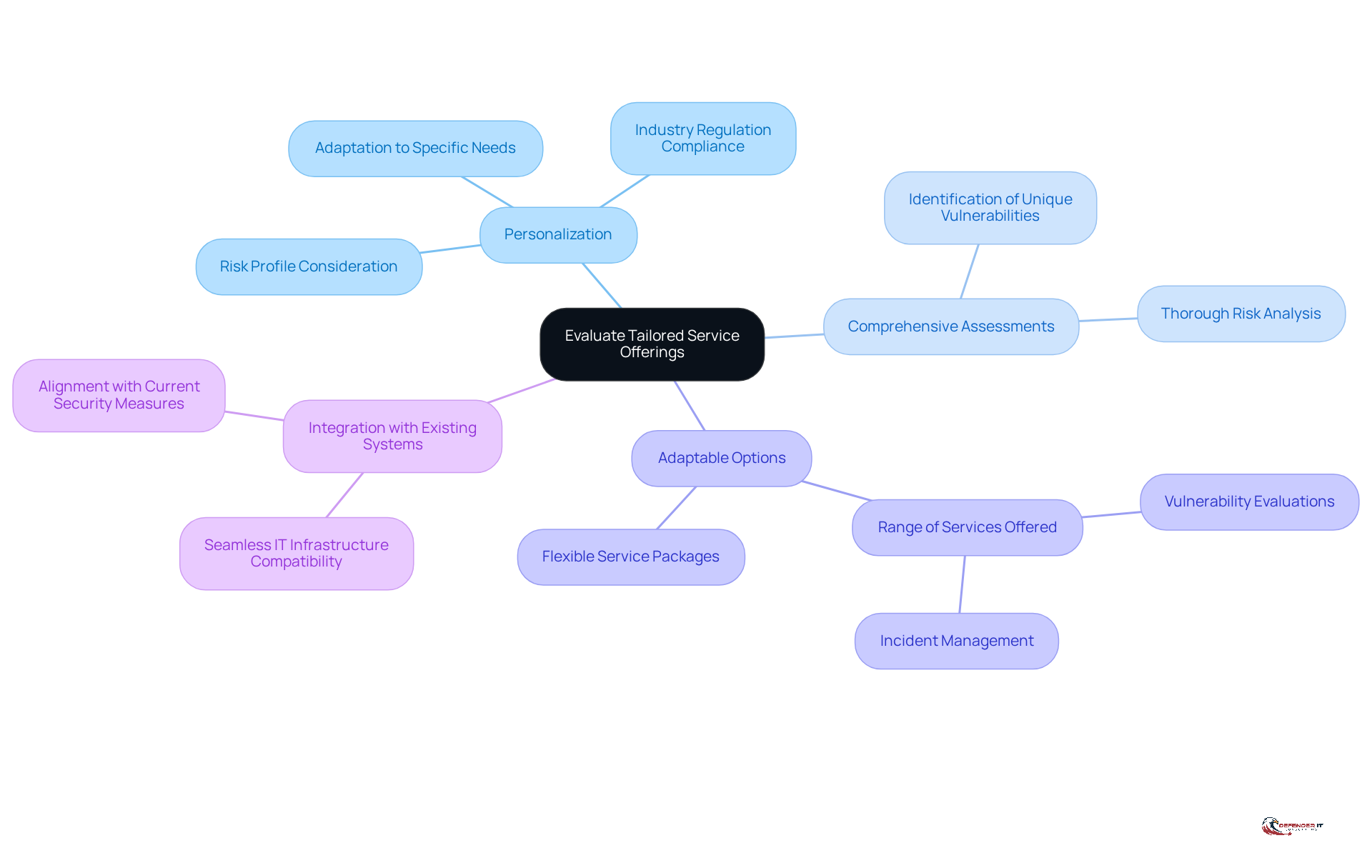
Evaluate Tailored Service Offerings
When selecting , it is crucial to evaluate the available. Focus on the following key aspects:
- Personalization: Look for options that adapt to your organization’s , industry regulations, and risk profile.
- Comprehensive Assessments: Ensure that the provider performs to identify vulnerabilities unique to your organization.
- Adaptable Options: Choose providers that offer a range of services, from to , facilitating a .
- : The consulting solution should seamlessly integrate with your current IT infrastructure and security measures.
By prioritizing , organizations can ensure they receive the most relevant and effective protection solutions.
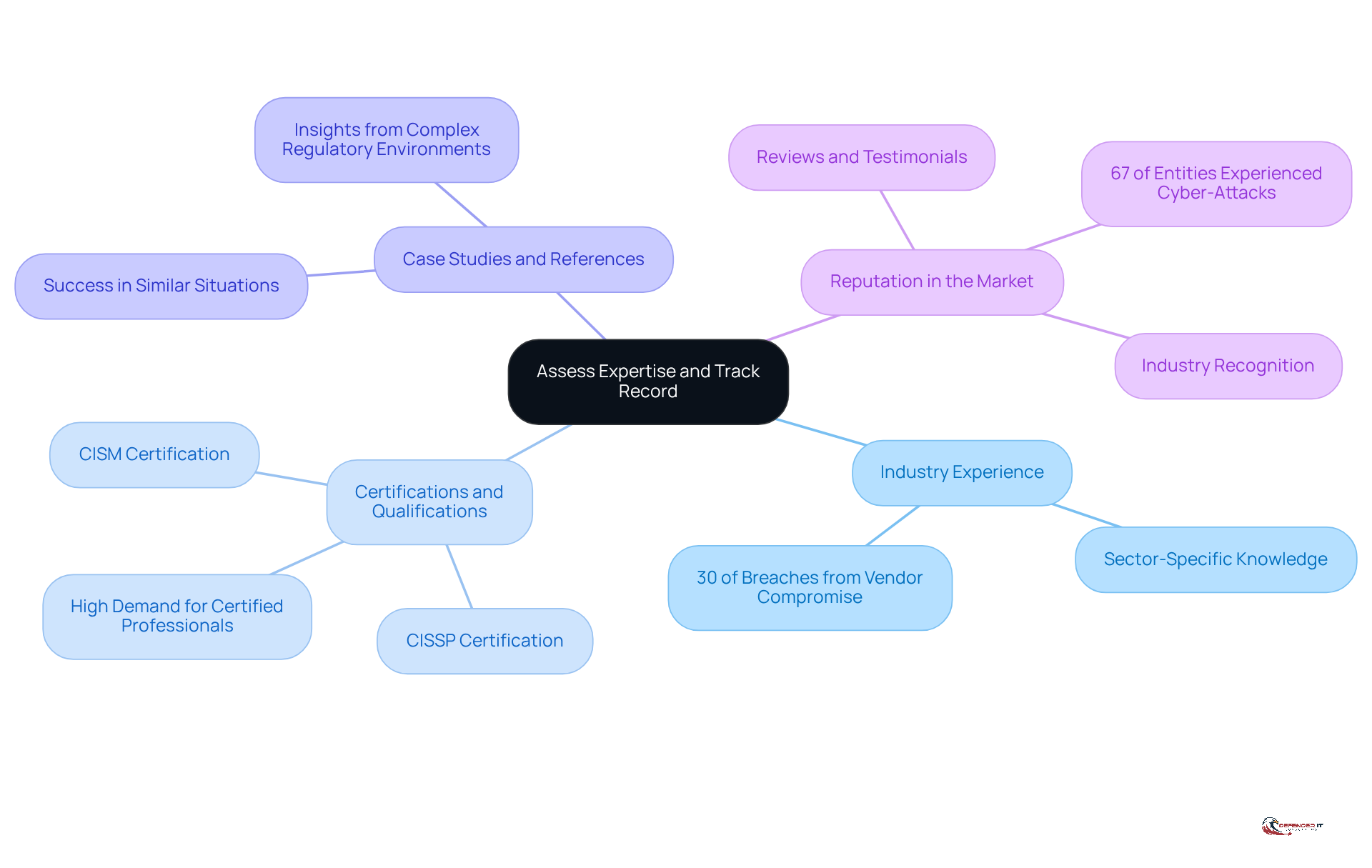
Assess Expertise and Track Record
To ensure the effectiveness of , organizations must conduct a thorough assessment of potential providers’ knowledge and history. The following key considerations are essential:
- Industry Experience: It is vital to seek providers with a strong background in your specific sector. Their familiarity with relevant regulations and threats is crucial, particularly given that nearly , underscoring the importance of (IBM X-Force).
- Certifications and Qualifications: Verify that the advisory team holds , such as CISSP or CISM, which validate their expertise. The demand for certified professionals remains high, making these qualifications essential for the effective management of security in digital environments.
- Case Studies and References: Request from previous clients to evaluate the provider’s success in similar situations. Organizations that have successfully navigated complex regulatory environments often share insights that can inform your decision-making process.
- Reputation in the Market: Investigate the provider’s . A can indicate reliability and effectiveness, especially as (IBM X-Force).
By thoroughly evaluating the skills and histories of potential providers, organizations can select consulting options that are well-equipped to , ultimately safeguarding their operations and reputation in an increasingly digital landscape.
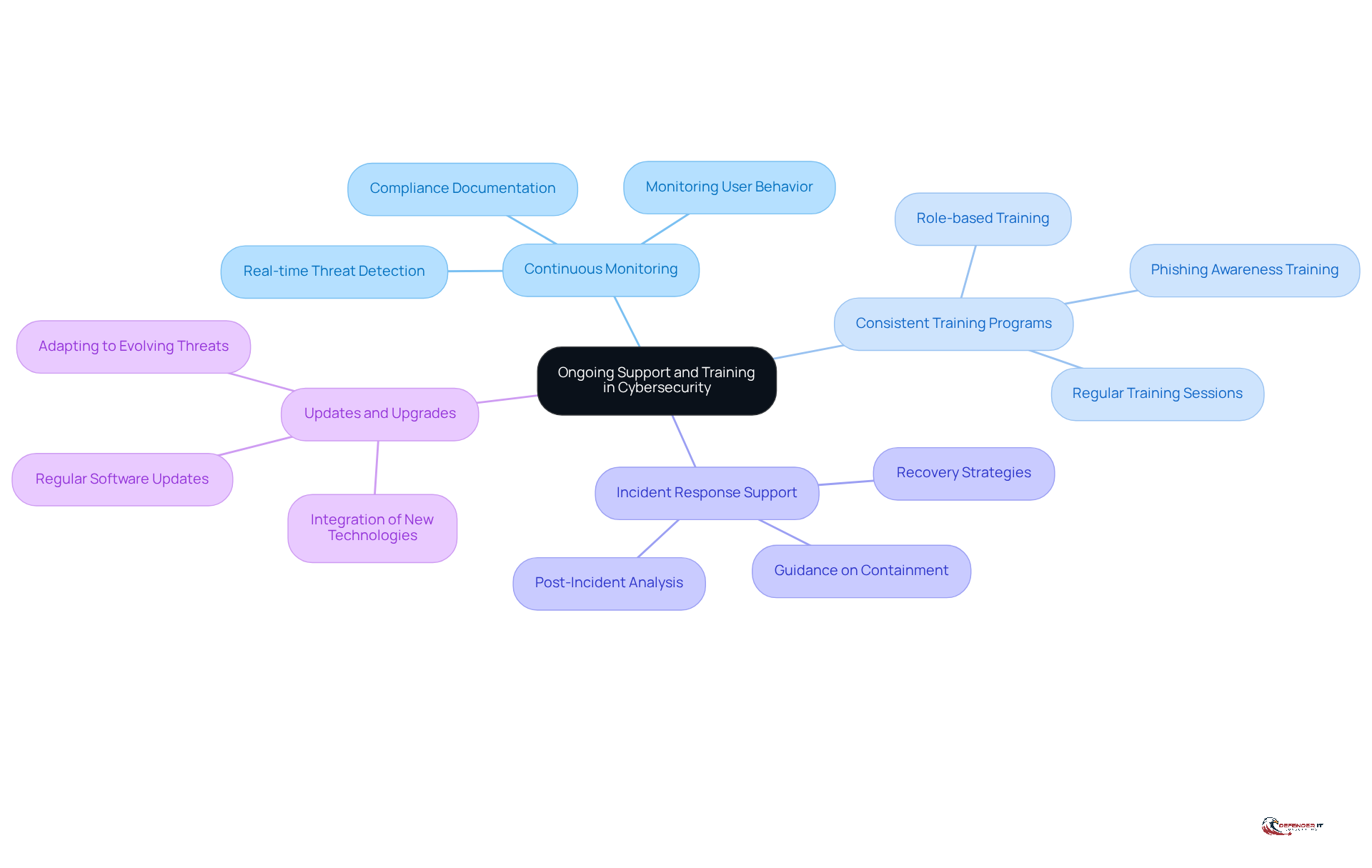
Prioritize Ongoing Support and Training
Selecting a provider of necessitates a thorough assessment of their commitment to continuous support and training. Prioritizing these elements can significantly enhance an organization’s resilience against . Consider the following key aspects:
- : It is essential that the provider offers ongoing monitoring options to detect and respond to threats in real-time.
- : Look for support options that provide regular training sessions for your staff, ensuring they remain informed about the latest threats and best practices.
- : Verify that the provider offers assistance during incidents, including guidance on .
- : Confirm that the advisory service is committed to in accordance with evolving threats.
By emphasizing , organizations can ensure their keep their cybersecurity measures effective over time.
Conclusion
Choosing the right cybersecurity advisory services is crucial for any organization that seeks to protect its digital assets. Organizations can make informed decisions that align with their security needs by understanding core cybersecurity principles, evaluating tailored service offerings, assessing the expertise of potential providers, and prioritizing ongoing support and training.
Understanding fundamental cybersecurity concepts such as confidentiality, integrity, and availability is essential. Additionally, evaluating customized services tailored to an organization’s specific requirements is vital for addressing unique vulnerabilities. A provider’s track record and industry experience further support the selection process, ensuring that the chosen consultant can effectively enhance the organization’s security posture.
The importance of ongoing support and training cannot be overstated. As cyber threats continue to evolve, organizations must remain vigilant and adaptable. By prioritizing these elements in their cybersecurity strategy, businesses can foster resilience and maintain robust defenses against emerging threats. Taking proactive steps today will not only protect valuable assets but also cultivate a culture of cybersecurity awareness that strengthens the organization for the future.
Frequently Asked Questions
What are the core principles of cybersecurity?
The core principles of cybersecurity include confidentiality, integrity, availability, authentication, and non-repudiation.
What does confidentiality mean in cybersecurity?
Confidentiality ensures that sensitive information is accessible only to those who are authorized to access it.
How is integrity defined in the context of cybersecurity?
Integrity involves maintaining the accuracy and completeness of data, which prevents unauthorized modifications.
What is meant by availability in cybersecurity?
Availability ensures that information and resources are accessible to authorized users whenever they need them.
What is the purpose of authentication in cybersecurity?
Authentication verifies the identity of users and systems to prevent unauthorized access.
What does non-repudiation refer to in cybersecurity?
Non-repudiation ensures that actions or transactions can be verified and attributed to the correct parties, preventing denial of involvement.
Why is understanding these principles important for selecting security consulting options?
Understanding these principles helps entities assess the efficacy of potential consulting options and ensures alignment with their security goals.
List of Sources
- Understand Core Cybersecurity Principles
- What is the CIA Triad? Definition, Importance, & Examples – SecurityScorecard (https://securityscorecard.com/blog/what-is-the-cia-triad)
- Top Cybersecurity Statistics: Facts, Stats and Breaches for 2025 (https://fortinet.com/resources/cyberglossary/cybersecurity-statistics)
- 205 Cybersecurity Stats and Facts for 2026 (https://vikingcloud.com/blog/cybersecurity-statistics)
- Evaluate Tailored Service Offerings
- Tuscaloosa News: Local News, Politics & Sports in Tuscaloosa, AL (https://tuscaloosanews.com/press-release/story/33922/digital-uppercut-strengthens-business-defense-with-advanced-cybersecurity-services-amid-rising-digital-threats)
- The top 20 expert quotes from the Cyber Risk Virtual Summit (https://diligent.com/resources/blog/top-20-quotes-cyber-risk-virtual-summit)
- Must-Know Small Business Cybersecurity Statistics for 2025 – BD Emerson (https://bdemerson.com/article/small-business-cybersecurity-statistics)
- 205 Cybersecurity Stats and Facts for 2026 (https://vikingcloud.com/blog/cybersecurity-statistics)
- 2024 Cybersecurity Statistics: The Ultimate List Of Stats, Data & Trends | PurpleSec (https://purplesec.us/resources/cybersecurity-statistics)
- Assess Expertise and Track Record
- Cybersecurity Trends 2026 | IBM (https://ibm.com/think/insights/more-2026-cyberthreat-trends)
- Global Cybersecurity Outlook 2026 (https://weforum.org/publications/global-cybersecurity-outlook-2026/in-full/3-the-trends-reshaping-cybersecurity)
- The Top 20 Expert Quotes On Cyber Risk and Security (https://surtech.co.za/20-expert-quotes-on-cyber-risk-and-security)
- Cybersecurity Awareness Month Quotes and Commentary from Industry Experts in 2025 (https://solutionsreview.com/cybersecurity-awareness-month-quotes-and-commentary-from-industry-experts-in-2025)
- Prioritize Ongoing Support and Training
- Constant Vigilance: The Importance of Continuous Cybersecurity Monitoring (https://csiweb.com/what-to-know/content-hub/blog/continuous-cybersecurity-monitoring)
- Why Continuous Monitoring Is Crucial for Modern Cybersecurity | TPx (https://tpx.com/blog/why-continuous-monitoring-is-crucial-for-modern-cybersecurity)
- ISACA Now Blog 2024 The Never ending Quest Why Continuous Monitoring is Crucial for Cybersecurity (https://isaca.org/resources/news-and-trends/isaca-now-blog/2024/the-never-ending-quest-why-continuous-monitoring-is-crucial-for-cybersecurity)
- [Updated 2026] Security Awareness Training Statistics – Keepnet (https://keepnetlabs.com/blog/security-awareness-training-statistics)
- Security Priorities 2026: Organizations Shift Toward Resilience and Identity as Cyber Risk Accelerates, Says Info-Tech Research Group (https://prnewswire.com/news-releases/security-priorities-2026-organizations-shift-toward-resilience-and-identity-as-cyber-risk-accelerates-says-info-tech-research-group-302668326.html)