Introduction
In today’s digital landscape, understanding the complexities of cybersecurity is paramount. Organizations face an increasingly intricate threat environment, making it essential to implement robust protective measures. A System Security Plan (SSP) is a critical framework designed to safeguard sensitive information. It outlines the necessary compliance strategies and protective measures to effectively mitigate risks.
Yet, many organizations still struggle with defining what constitutes an effective SSP and its vital role in ensuring both compliance and security. This article explores the essential components of a System Security Plan, highlighting its significance in the current digital environment. Additionally, it outlines actionable steps organizations can take to bolster their cybersecurity posture.
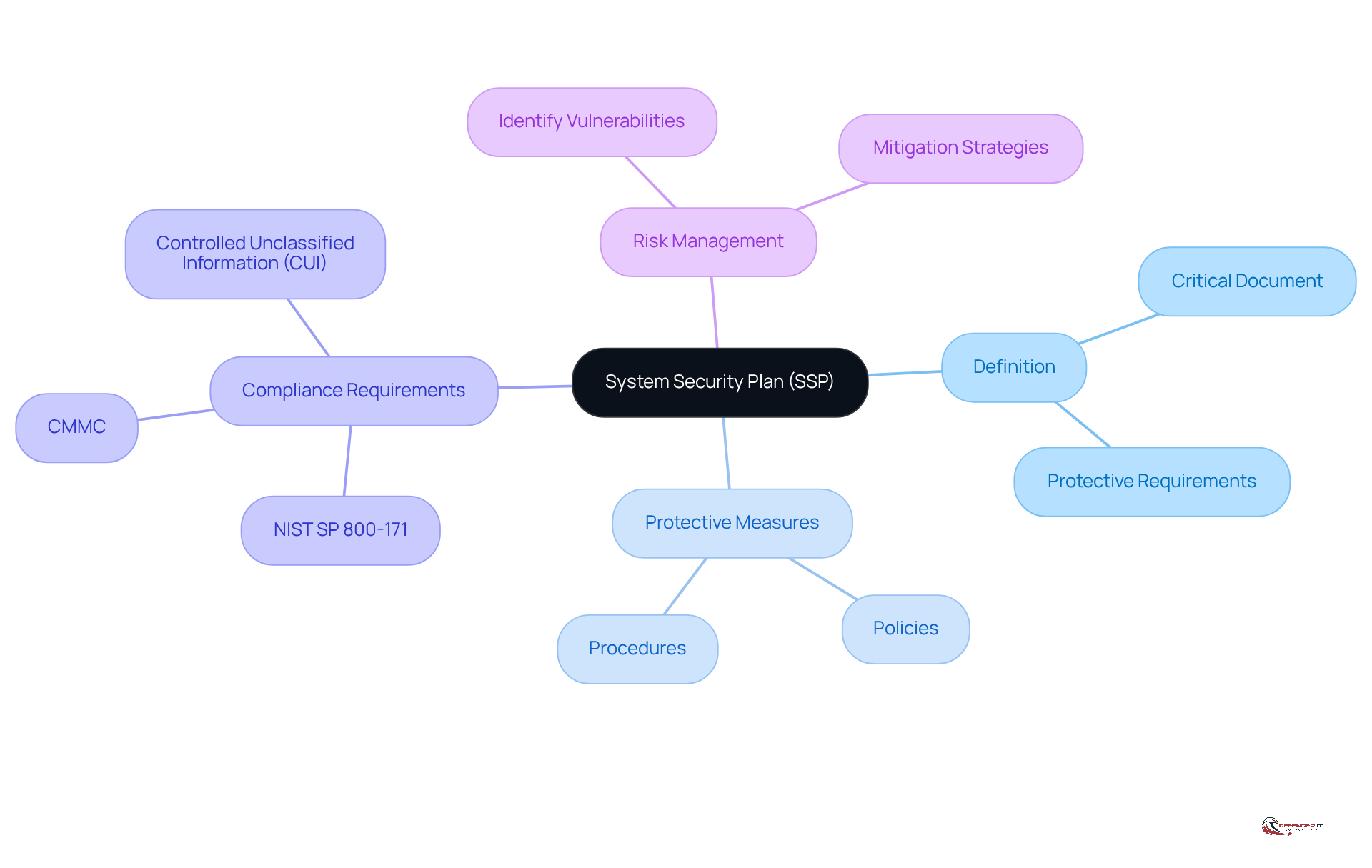
Define System Security Plan (SSP)
What is a system security plan? It is a critical document that outlines how an organization meets the protective requirements for its information systems. This comprehensive blueprint details the protective measures, policies, and procedures implemented to safeguard sensitive data. Understanding what is a system security plan is essential for compliance with various regulatory frameworks, including NIST SP 800-171 and CMMC, and is often a requirement for entities managing Controlled Unclassified Information (CUI). By documenting the protective measures in place, the SSP enables organizations to identify vulnerabilities and develop effective risk management and mitigation strategies.
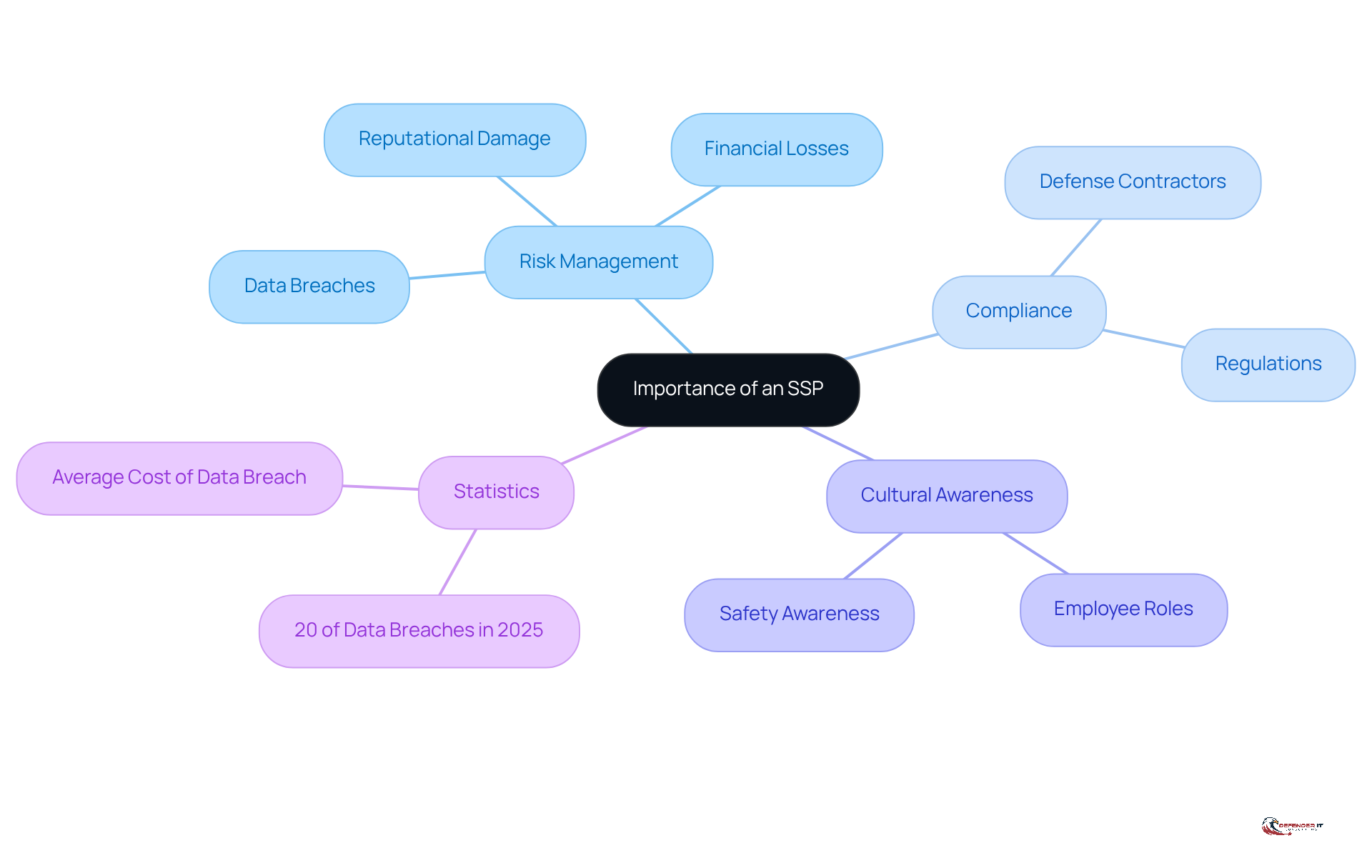
Contextualize the Importance of an SSP
In the current landscape of sophisticated cyber threats, understanding what is a system security plan is of utmost importance. Organizations face significant risks, including data breaches, financial losses, and reputational damage. An SSP, or what is a system security plan, not only aids in meeting compliance requirements but also serves as a proactive strategy to bolster an entity’s defense posture.
For instance, defense contractors must adhere to stringent regulations, leading to the question of what is a system security plan as a critical component of their cybersecurity framework. Moreover, an effective SSP cultivates a culture of safety awareness within the organization, ensuring that all employees understand their roles in safeguarding sensitive information.
This proactive approach is essential, particularly as projections indicate that 20% of data breaches in 2025 will involve the exploitation of vulnerabilities. This statistic underscores the necessity for comprehensive security measures. By implementing robust SSPs, organizations can significantly enhance their resilience against evolving cyber threats and promote a more security-conscious environment.
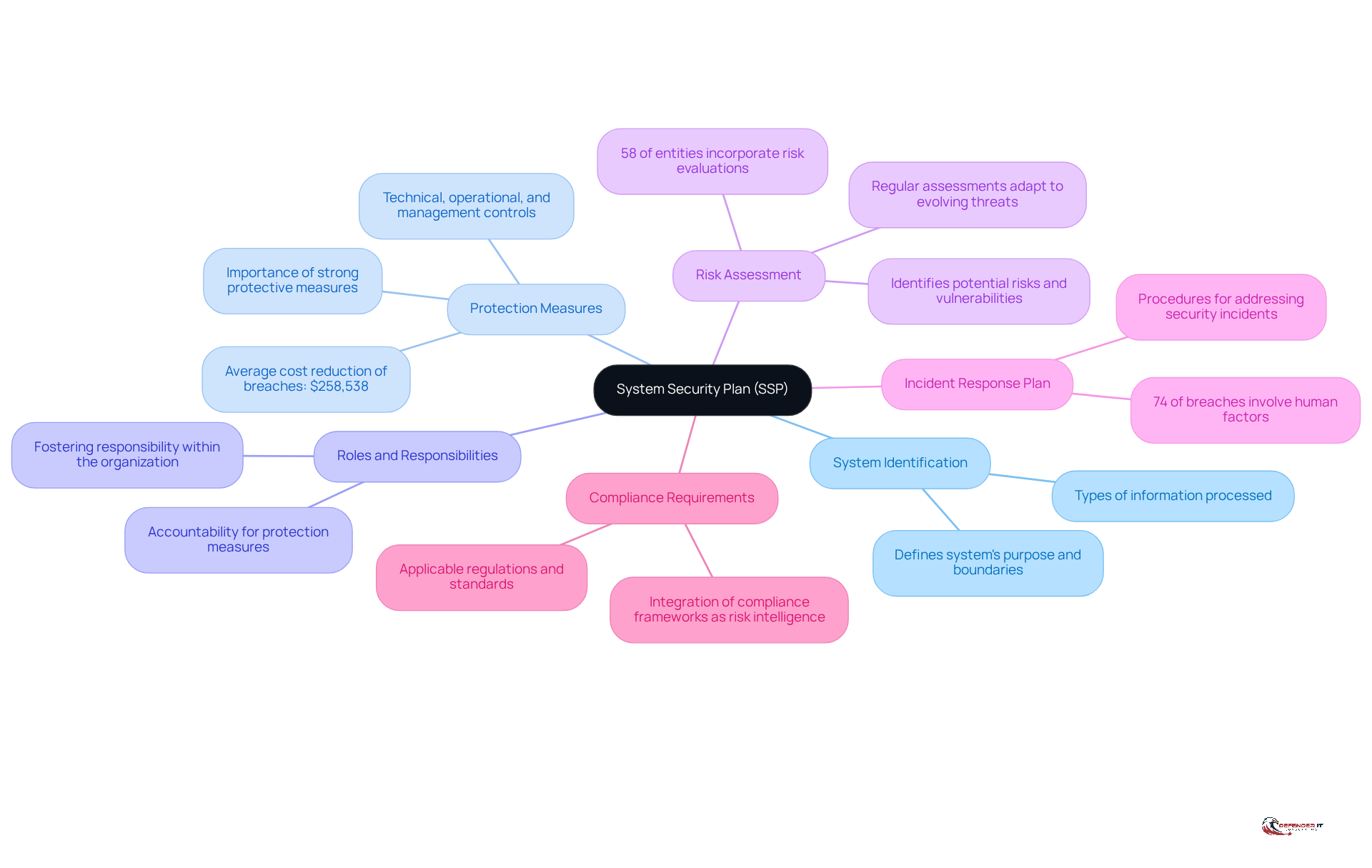
Identify Key Components of an SSP
Understanding what is a system security plan is essential for organizations seeking to protect their digital assets. The key components of an effective SSP include:
- System Identification: This section defines the system’s purpose, boundaries, and the types of information it processes, ensuring that all stakeholders understand the system’s scope.
- Protection Measures: It outlines the specific protective actions implemented to safeguard the system, encompassing technical, operational, and management controls. Organizations that implement extensive protective measures report a significant decrease in data breach expenses, averaging $258,538 due to insights from AI and machine learning. Cybersecurity specialists emphasize that “implementing strong protective measures is crucial for reducing financial losses linked to breaches.”
- Roles and Responsibilities: This details who is accountable for executing and upholding the protection measures, fostering a sense of responsibility within the organization.
- Risk Assessment: A critical element, this identifies potential risks and vulnerabilities associated with the system and outlines strategies for mitigation. Notably, 58% of entities incorporate risk evaluations in their SSPs, which raises the question of what is a system security plan and its role in indicating a proactive approach to cybersecurity. Industry reports highlight that “regular risk assessments are vital for adapting to evolving threats.”
- Incident Response Plan: This outlines procedures for addressing security incidents, ensuring that the organization can effectively manage and recover from breaches. Given that 74% of data breaches involve human factors, having a robust incident response plan is essential.
- Compliance Requirements: This lists applicable regulations and standards that the organization must adhere to, such as NIST or ISO standards. As compliance becomes increasingly complex, businesses are recognizing the importance of integrating compliance frameworks as real-time risk intelligence sources. The trend towards continuous compliance practices is becoming more prevalent, underscoring the need for businesses to stay ahead of regulatory demands.
By incorporating these elements, organizations can enhance their cybersecurity posture and ensure they are well-prepared to face evolving threats.
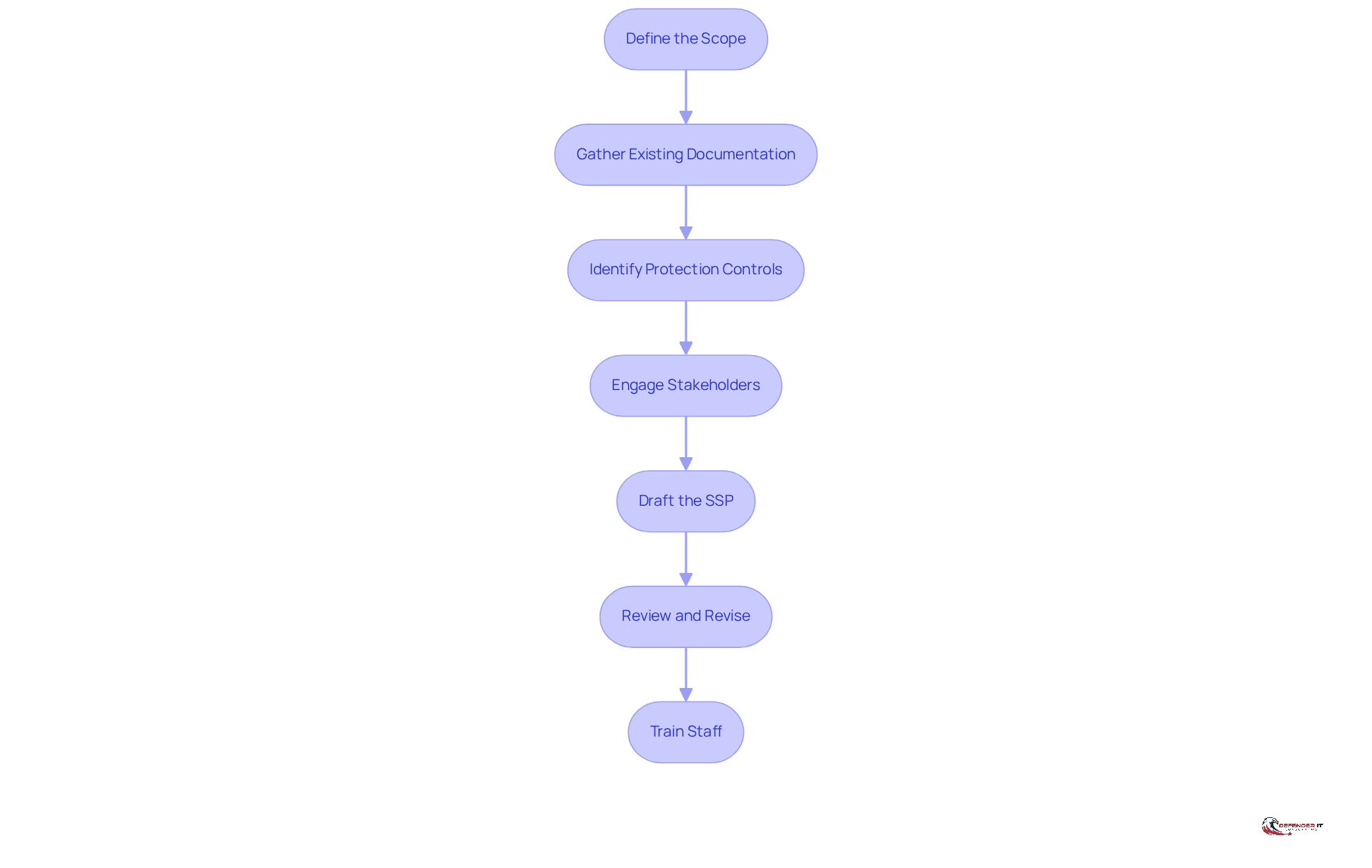
Outline Steps to Create an Effective SSP
Creating an effective System Security Plan (SSP) involves several critical steps:
- Define the Scope: Clearly determine which systems and data will be included in the SSP.
- Gather Existing Documentation: Collect relevant policies, procedures, and previous assessments to inform the SSP.
- Identify Protection Controls: Evaluate current protective measures and recognize any gaps that need to be addressed.
- Engage Stakeholders: Involve key personnel from IT, compliance, and management to ensure comprehensive coverage of protection needs.
- Draft the SSP: Compile the information into a structured document, ensuring clarity and completeness.
- Review and Revise: Conduct regular reviews of the SSP to ensure it remains up-to-date with evolving threats and compliance requirements.
- Train Staff: Provide training to employees on the SSP and their roles in maintaining security, fostering a culture of security awareness.
Conclusion
A System Security Plan (SSP) is essential for organizations aiming to protect their information systems and sensitive data. By detailing the protective measures, policies, and procedures in place, the SSP not only ensures compliance with regulatory standards but also enables organizations to identify vulnerabilities and implement effective risk management strategies.
Key components of an SSP encompass:
- System identification
- Protective measures
- Roles and responsibilities
- Risk assessments
- Incident response plans
- Compliance requirements
Each element is crucial in enhancing an organization’s cybersecurity posture, fostering a culture of awareness, and preparing for evolving threats. The proactive establishment of an SSP can significantly mitigate risks associated with data breaches and financial losses.
The significance of developing and maintaining an effective System Security Plan cannot be overstated. As cyber threats grow increasingly sophisticated, organizations must prioritize the creation of robust SSPs that comply with regulations and safeguard their digital assets. By embracing the steps outlined in this article, organizations can strengthen their defenses and cultivate an environment where security is a shared responsibility. Taking action now will lead to a more secure future for organizations and their stakeholders.
Frequently Asked Questions
What is a System Security Plan (SSP)?
A System Security Plan (SSP) is a critical document that outlines how an organization meets the protective requirements for its information systems. It details the protective measures, policies, and procedures implemented to safeguard sensitive data.
Why is a System Security Plan important?
An SSP is essential for compliance with various regulatory frameworks, such as NIST SP 800-171 and CMMC. It is often required for entities managing Controlled Unclassified Information (CUI) and helps organizations identify vulnerabilities and develop effective risk management and mitigation strategies.
What does an SSP document include?
An SSP includes a comprehensive blueprint of the protective measures in place, as well as the policies and procedures that an organization implements to protect sensitive information.
How does an SSP help with risk management?
By documenting the protective measures, an SSP enables organizations to identify vulnerabilities, allowing them to develop effective risk management and mitigation strategies.