Introduction
The digital landscape presents significant challenges as cybercrime evolves rapidly, creating unprecedented risks for organizations globally. Security leaders are at the forefront of this struggle, required to grasp not only the historical context of cyber threats but also the intricate trends that define today’s cyber environment. As cybercriminals adopt advanced technologies and sophisticated tactics, leaders must find effective ways to protect their organizations from these ongoing attacks. This article examines the rise of cybercrime, detailing its evolution, current trends, and essential strategies that security leaders can employ to strengthen their defenses in a constantly shifting threat landscape.
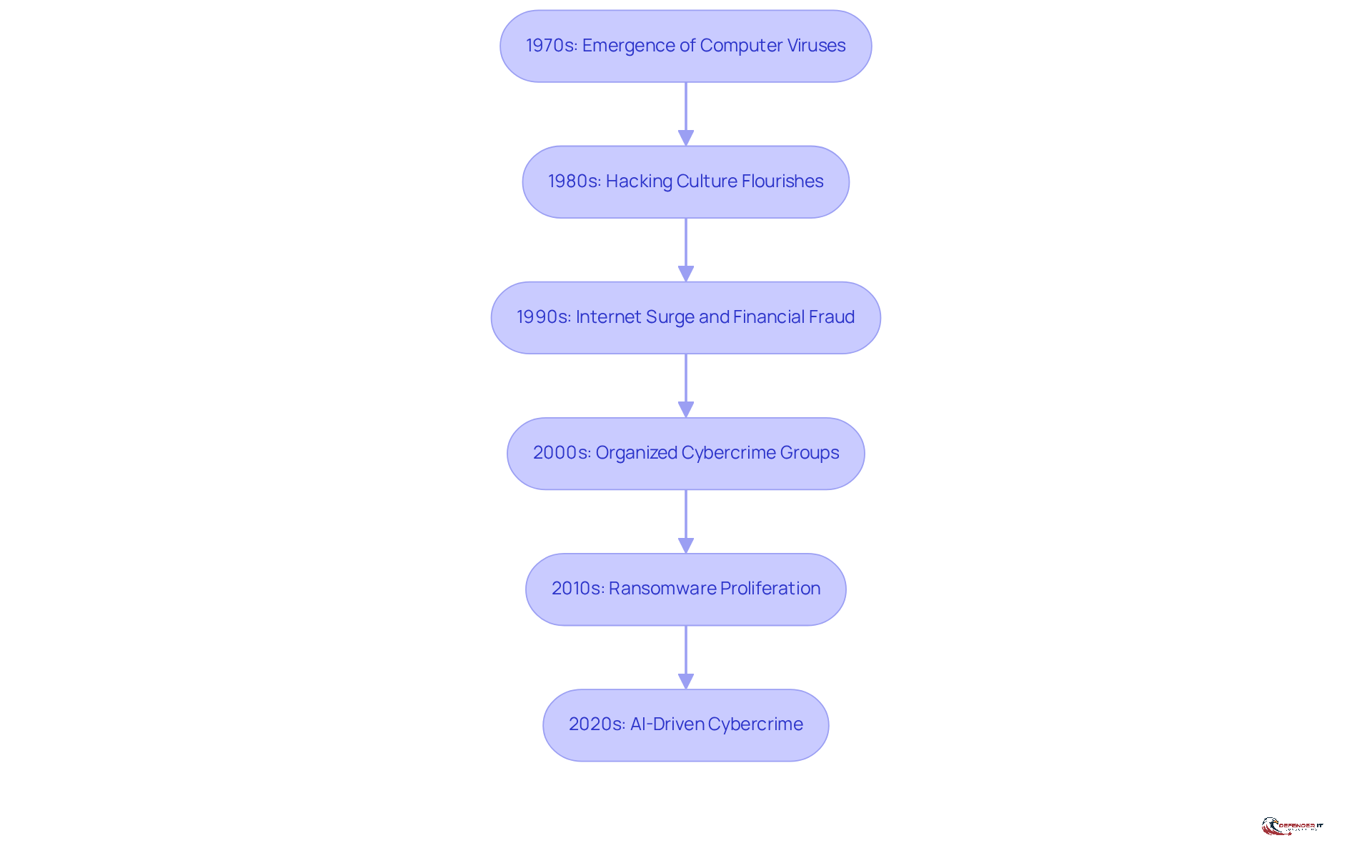
Explore the Evolution of Cybercrime: Historical Context and Key Milestones
Cybercrime has a rich history that dates back to the early days of computing, marked by several key milestones:
-
1970s: The emergence of computer viruses began with early examples like the Creeper virus, laying the groundwork for future threats.
-
1980s: The hacking culture flourished, highlighted by notorious figures such as Kevin Mitnick, who became emblematic of the era’s challenges.
-
1990s: The introduction of the internet catalyzed a surge in cybercrime, which marked the rise of cybercrime and led to the first major financial fraud cases, highlighting vulnerabilities in digital transactions. This period witnessed notable risks, including the Melissa Virus, which caused an estimated $80 million in damages.
-
2000s: The rise of cybercrime as organized groups took shape to execute large-scale attacks, marking a shift towards more sophisticated and coordinated efforts. The SolarWinds incident, impacting an estimated 18,000 networks, exemplified the growing complexity of cyber threats.
-
2010s: Ransomware and data violations proliferated, impacting millions and demonstrating the severe financial and reputational risks associated with cyber incidents. The average cost of a data breach rose to $4.45 million, underscoring the financial impact of these attacks.
-
2020s: The rise of cybercrime, driven by AI technologies, has transformed the landscape, as attackers enhance their tactics, making detection and prevention increasingly challenging. Ginni Rometty accurately stated, “Cybercrime is the sole largest danger to every company on the planet,” emphasizing the necessity for businesses to adapt.
Understanding these milestones is vital for security leaders, as it offers insight into the intricacies of today’s cyber challenges and highlights the need for adaptive strategies to protect against evolving risks.
Analyze Current Cybercrime Trends: Threats Facing Security Leaders Today
As of 2025, several key trends are shaping the cybercrime landscape:
-
Ransomware-as-a-Service (RaaS): Cybercriminals are increasingly offering ransomware tools for hire, facilitating sophisticated attacks by less skilled attackers. This model has contributed to the dramatic rise of cybercrime, particularly in ransomware incidents, with organizations experiencing an average increase in ransom payments to $1.5 million, reflecting the growing financial stakes involved.
-
AI-Driven Attacks: The use of artificial intelligence by cybercriminals to automate and enhance phishing and social engineering attacks has transformed the risk environment. In fact, 82.6% of phishing emails in 2025 contained AI-generated content, complicating traditional detection methods. Additionally, 80% of ransomware attacks utilized AI tools according to a 2025 MIT study, underscoring the significance of AI in relation to the rise of cybercrime.
-
Supply Chain Vulnerabilities: Attacks aimed at third-party vendors have become a common tactic for cybercriminals seeking entry into larger enterprises. Notable incidents have highlighted the necessity of protecting supply chains, as attackers exploit these weaknesses to access larger targets. Organizations must evaluate third-party vendor cybersecurity practices to mitigate vulnerabilities.
-
Phishing and Social Engineering: Phishing attacks continue to evolve, focusing on more personalized and targeted approaches. The sophistication of these attacks has increased, making it essential for entities to implement robust training and awareness programs to mitigate risks.
-
Data Breaches: The frequency and severity of data breaches are on the rise, resulting in significant financial and reputational consequences for businesses. In 2025, 75% of security leaders reported a significant increase in security incidents, underscoring the urgent need for enhanced cybersecurity measures in light of the rise of cybercrime.
Security leaders must remain knowledgeable about these trends to develop effective countermeasures and safeguard their organizations.
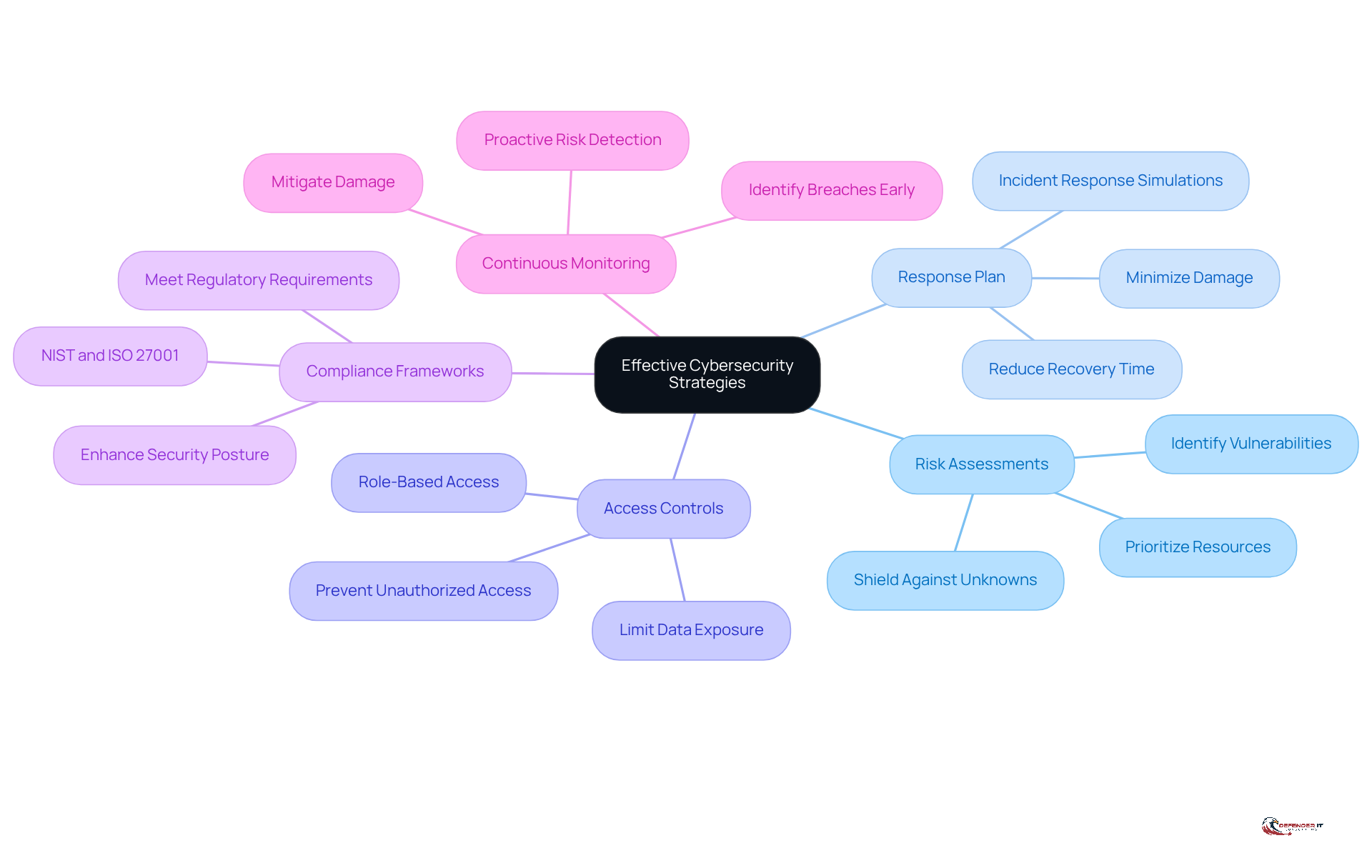
Implement Effective Cybersecurity Strategies: Risk Management and Compliance Solutions
To effectively combat cybercrime, security leaders should adopt several key strategies:
-
Conduct Regular Risk Assessments: Systematic evaluations of an organization’s security posture are essential. These assessments help identify weaknesses and gauge the potential impacts of various threats, enabling organizations to prioritize resources effectively. As Mekan Bairyev noted, “a cybersecurity risk assessment is your shield against the unknown.” Without regular evaluations, organizations remain vulnerable to data breaches, compliance violations, and significant financial losses.
-
Develop a Comprehensive Response Plan: A well-structured response strategy is crucial for minimizing damage during a cyber event. Organizations with established response plans have reported success in reducing the impact of incidents, highlighting the importance of preparedness. For example, companies that practiced incident response simulations experienced a 30% reduction in recovery time during actual incidents.
-
Implement Strong Access Controls: Limiting access to sensitive data based on user roles is vital for minimizing exposure. Organizations that enforce stringent access controls can significantly reduce the likelihood of unauthorized access and data incidents, which are increasingly common in today’s risk environment.
-
Adopt Compliance Frameworks: Utilizing established frameworks such as NIST or ISO 27001 can guide the development of robust security policies and procedures. Compliance not only aids in meeting regulatory requirements but also enhances overall security posture by ensuring adherence to best practices.
-
Engage in Continuous Monitoring: Regular observation of systems for unusual activity is essential for proactive risk detection. Organizations that implement continuous monitoring can identify potential breaches before they escalate, thereby mitigating the risk of substantial damage.
By incorporating these strategies, companies can significantly enhance their cybersecurity protections, reduce risk exposure, and foster a culture of security awareness that is crucial due to the rise of cybercrime in today’s evolving cyber threat landscape.
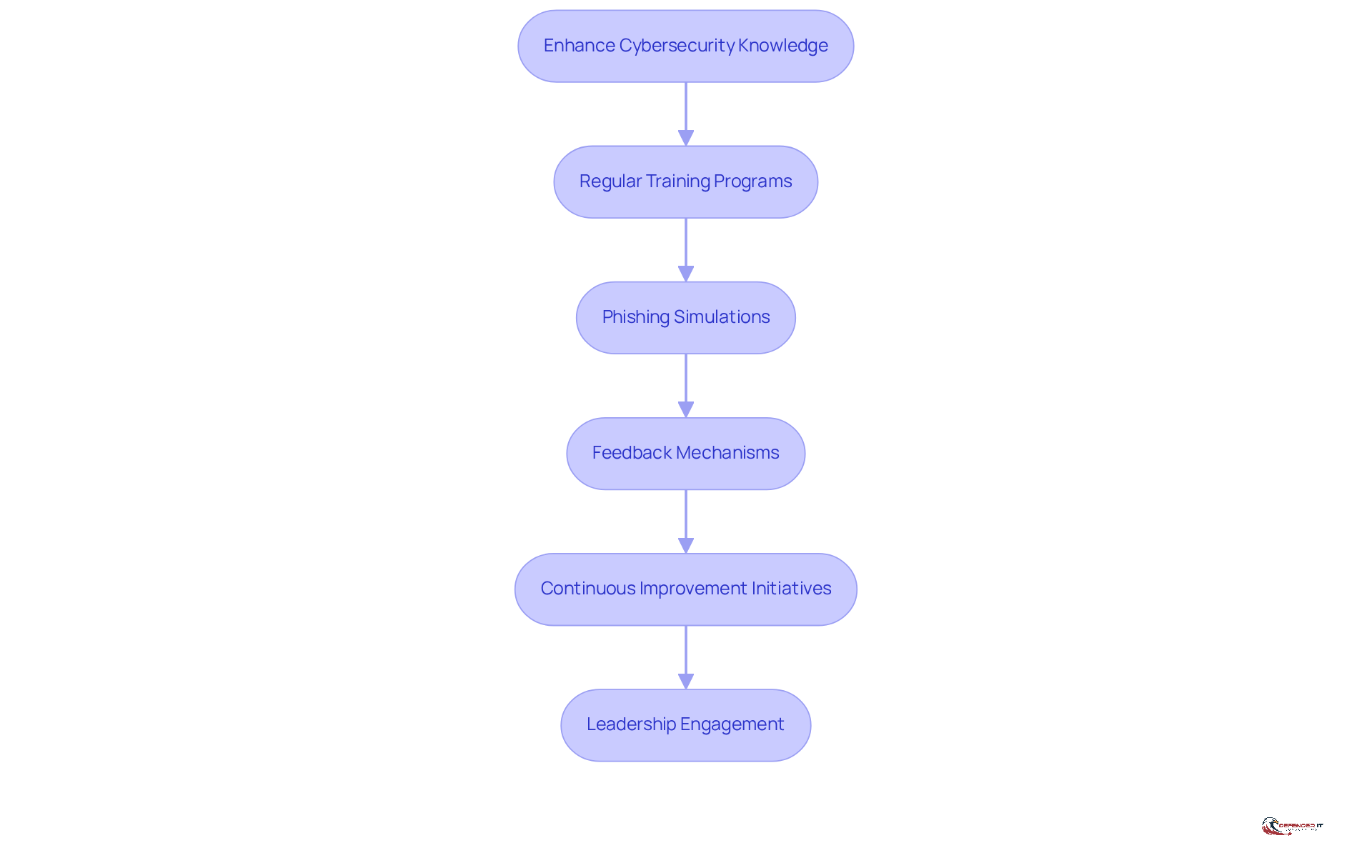
Enhance Cybersecurity Knowledge: The Role of Training and Continuous Improvement
To cultivate a security-aware culture, organizations must prioritize several key initiatives:
-
Regular Training Programs: Ongoing training sessions are essential to cover the latest threats, security best practices, and incident response protocols. These programs ensure that employees are well-informed and prepared to handle potential security challenges.
-
Phishing Simulations: Conducting simulated phishing attacks serves as an effective educational tool, helping employees recognize and respond appropriately to phishing attempts. This proactive approach enhances their ability to identify threats in real-time.
-
Feedback Mechanisms: Establishing clear channels for employees to report suspicious activities is crucial. Additionally, gathering feedback on the effectiveness of training initiatives allows organizations to refine their programs continuously.
-
Continuous Improvement Initiatives: Regular reviews and updates of training materials are necessary to reflect the evolving risk landscape. Incorporating lessons learned from past incidents ensures that the training remains relevant and effective.
-
Leadership Engagement: Active participation from organizational leaders in training initiatives underscores the importance of cybersecurity. Their involvement not only demonstrates commitment but also encourages a culture of security awareness throughout the organization.
By prioritizing these training and continuous improvement efforts, organizations empower their employees to serve as the first line of defense against cyber threats.
Conclusion
The imperative for security leaders is unequivocal: proactive engagement in cybersecurity practices is essential. As the landscape of cybercrime continues to evolve, organizations must prioritize adaptive strategies and foster a culture of security awareness. This approach not only enhances resilience against threats but also equips businesses to navigate the increasingly perilous environment characterized by data breaches and cyber incidents.
Key insights reveal pressing trends that security leaders face today, including:
- The rise of Ransomware-as-a-Service
- AI-enhanced attacks
- Vulnerabilities within supply chains
Each of these factors contributes to a reality where data breaches are not merely possible but expected. To combat these threats effectively, organizations must implement strategies such as:
- Regular risk assessments
- Robust response plans
- Continuous employee training
Ultimately, the collective effort to understand, prepare for, and respond to these threats will shape the security landscape of tomorrow. It is critical for businesses to act decisively and with foresight, ensuring they are well-equipped to address the ever-growing tide of cybercrime.
Frequently Asked Questions
What is the historical context of cybercrime?
Cybercrime has a rich history that began in the 1970s with the emergence of computer viruses, evolving through various key milestones in subsequent decades.
What notable events occurred in the 1970s related to cybercrime?
The 1970s saw the emergence of computer viruses, with early examples like the Creeper virus laying the groundwork for future cyber threats.
How did the 1980s contribute to the evolution of cybercrime?
The 1980s marked the flourishing of hacking culture, highlighted by notorious figures like Kevin Mitnick, who exemplified the challenges of that era.
What significant developments in cybercrime took place in the 1990s?
The introduction of the internet in the 1990s catalyzed a surge in cybercrime, leading to the first major financial fraud cases and notable risks such as the Melissa Virus, which caused around $80 million in damages.
How did cybercrime evolve in the 2000s?
The 2000s saw the rise of organized cybercrime groups that executed large-scale attacks, exemplified by incidents like the SolarWinds attack, which impacted approximately 18,000 networks.
What trends in cybercrime emerged in the 2010s?
The 2010s experienced a proliferation of ransomware and data violations, with the average cost of a data breach rising to $4.45 million, highlighting the financial and reputational risks of cyber incidents.
What is the current state of cybercrime in the 2020s?
The 2020s have seen cybercrime increasingly driven by AI technologies, complicating detection and prevention efforts. Ginni Rometty noted that cybercrime poses the largest danger to companies globally, emphasizing the need for businesses to adapt.
Why is understanding the history of cybercrime important for security leaders?
Understanding the milestones of cybercrime is vital for security leaders as it provides insight into today’s cyber challenges and underscores the necessity for adaptive strategies to protect against evolving risks.