Introduction
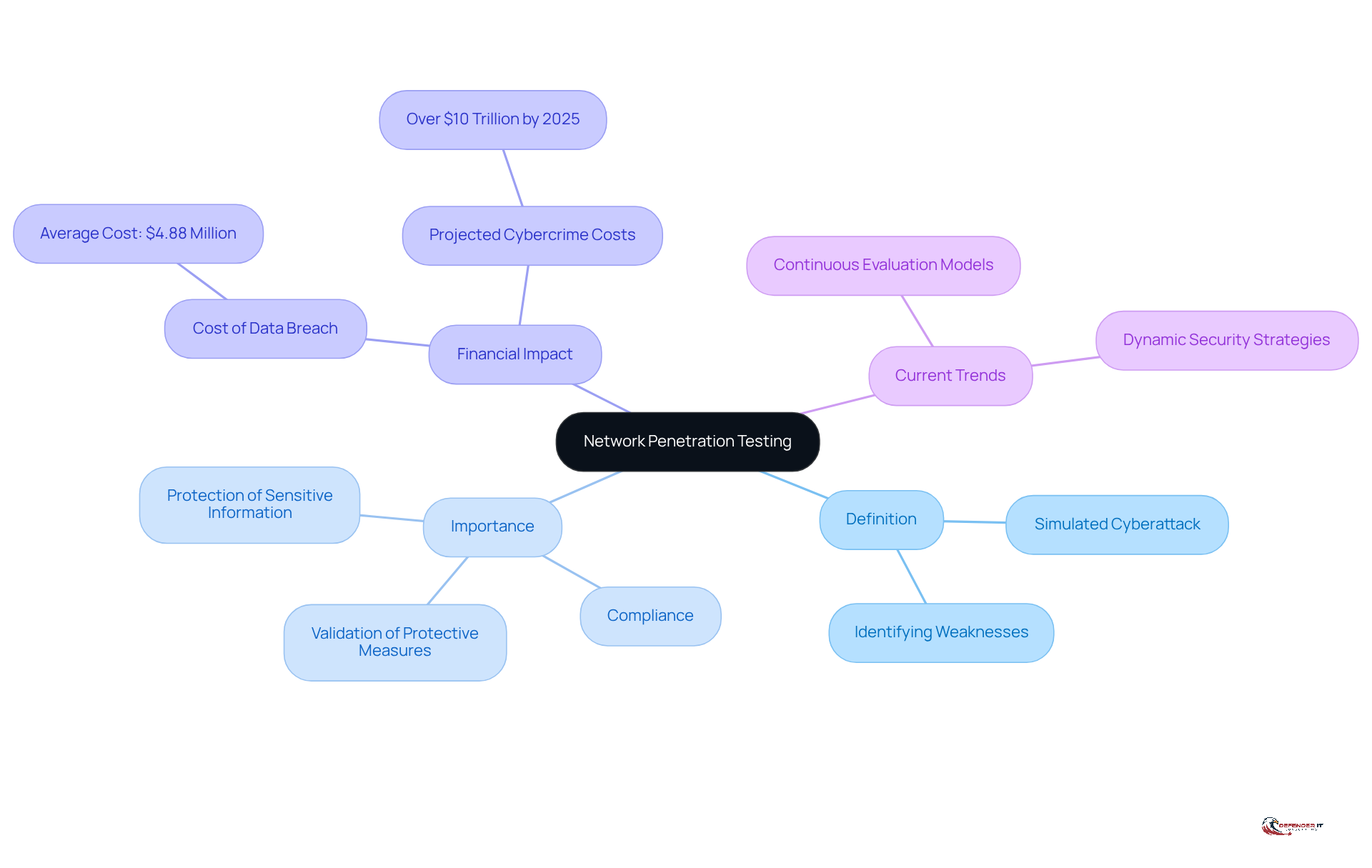
Understanding the financial implications of network penetration testing is essential for security leaders navigating a landscape filled with cyber threats. Organizations are increasingly confronted with rising costs associated with data breaches, which average nearly $4.88 million. Therefore, investing in effective security assessments is not merely a precaution; it has become a necessity.
However, the challenge lies in comprehending the various factors that influence penetration testing costs. These factors range from the complexity of the environment to the specific type of evaluation required. Organizations must consider how to effectively budget for these essential services while ensuring they receive comprehensive protection against potential vulnerabilities.
Define Network Penetration Testing and Its Importance
, commonly referred to as , represents a , network, or web application aimed at identifying weaknesses that could be exploited by malicious actors. This proactive approach is essential for organizations to understand their security posture and to uncover vulnerabilities before they can be taken advantage of.
The importance of lies in their ability to validate the effectiveness of existing protective measures, ensure compliance with regulatory requirements, and ultimately protect sensitive information from breaches. Regular security assessments enable organizations to stay ahead of evolving , making them a critical component of a robust cybersecurity strategy.
With the now exceeding $4.88 million, investing in security assessments not only mitigates risks but also serves as a . Furthermore, as cybercrime is projected to cost businesses over $10 trillion by 2025, the necessity for routine security assessments becomes increasingly apparent.
Current trends indicate a shift towards continuous evaluation models, reflecting the dynamic nature of cyber threats and the need for organizations to adapt their security strategies accordingly. Insights from industry experts, such as Mikella Marley, who highlights the , underscore the vital role of in maintaining a strong security posture.
Explore Factors Influencing Penetration Testing Costs
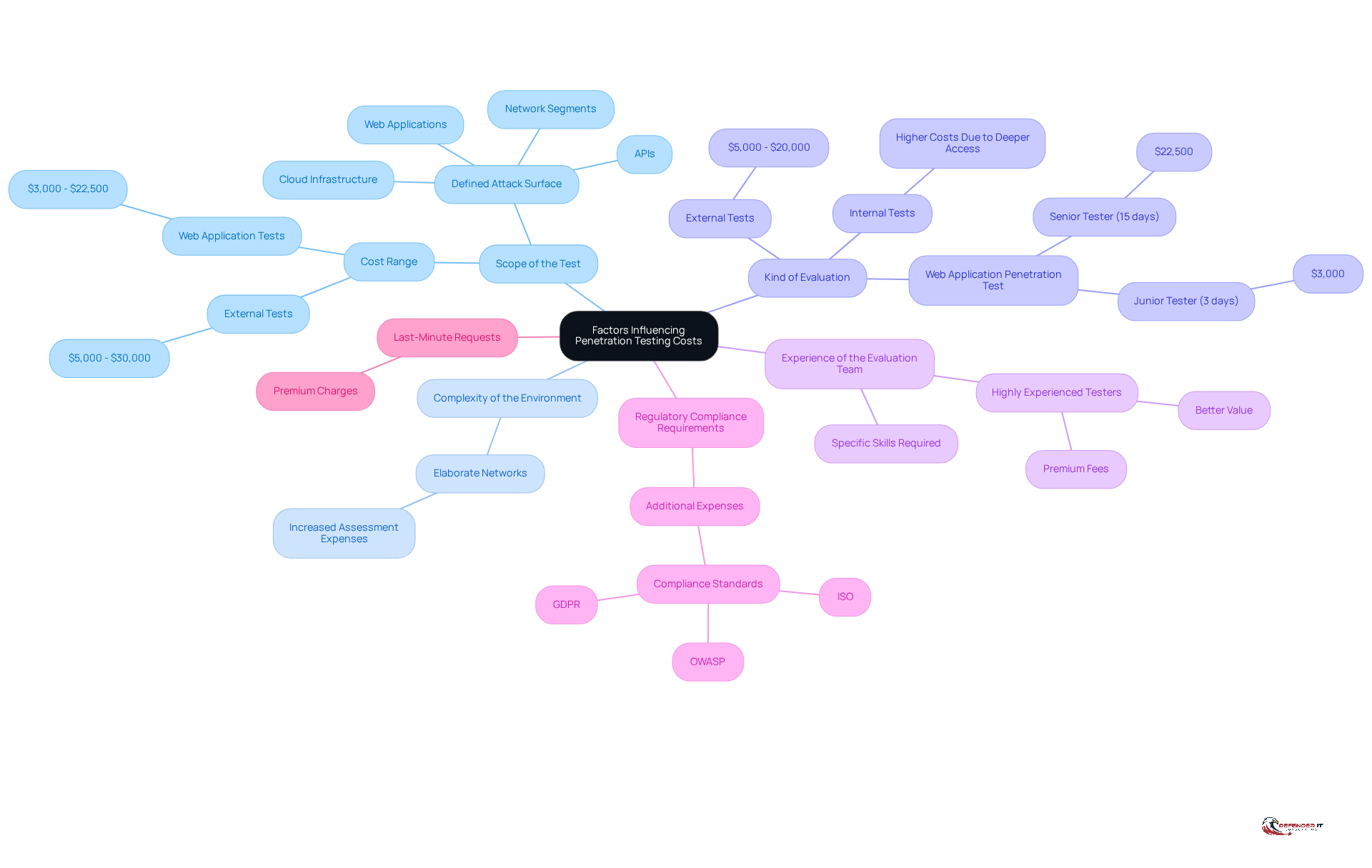
The cost of is influenced by several key factors that organizations must consider when budgeting for these essential services:
- : The extent of systems and applications included in the testing significantly affects costs. A broader scope necessitates more resources and time, leading to higher expenses. For instance, , requiring on-site presence and comprehensive network mapping based on the defined attack surface, which may encompass network segments, web applications, APIs, or cloud infrastructure.
- : Organizations with elaborate networks containing numerous devices and configurations will face increased assessment expenses. Complex environments often require more extensive assessments, which can elevate the overall price.
- Kind of Evaluation: Various forms of security assessments incur different expenses. External tests generally range from $5,000 to $20,000, while internal tests may be more costly due to the need for deeper access and thorough evaluations. For example, the price of a web application penetration test varies from $3,000 to $22,500, and a large, intricate web application evaluation performed by a senior tester might require up to 15 days, amounting to approximately $22,500.
- Experience of the Evaluation Team: The knowledge of the evaluation team plays a crucial role in determining expenses. Highly experienced testers or reputable firms may charge premium fees, but they often deliver more comprehensive and reliable assessments, ultimately providing better value. Not all experience is equal; specific skills may be required for certain technologies, which can also influence pricing.
- : Organizations operating in regulated sectors, such as finance or healthcare, may incur additional expenses to adhere to specific compliance standards during evaluation. Compliance mandates often require detailed reporting, including evidence, risk scoring, and remediation advice, which are essential for adhering to frameworks like OWASP, GDPR, and ISO.
- Last-Minute Requests: It is important to note that last-minute security assessment requests often incur a premium, which can significantly impact budgeting considerations.
Understanding these elements allows companies to budget efficiently and choose the most appropriate tailored to their specific security requirements. By evaluating the scope, complexity, type of evaluation, team experience, compliance requirements, and potential last-minute expenses, businesses can make informed choices that strengthen their .
Examine Types of Penetration Testing and Their Cost Implications
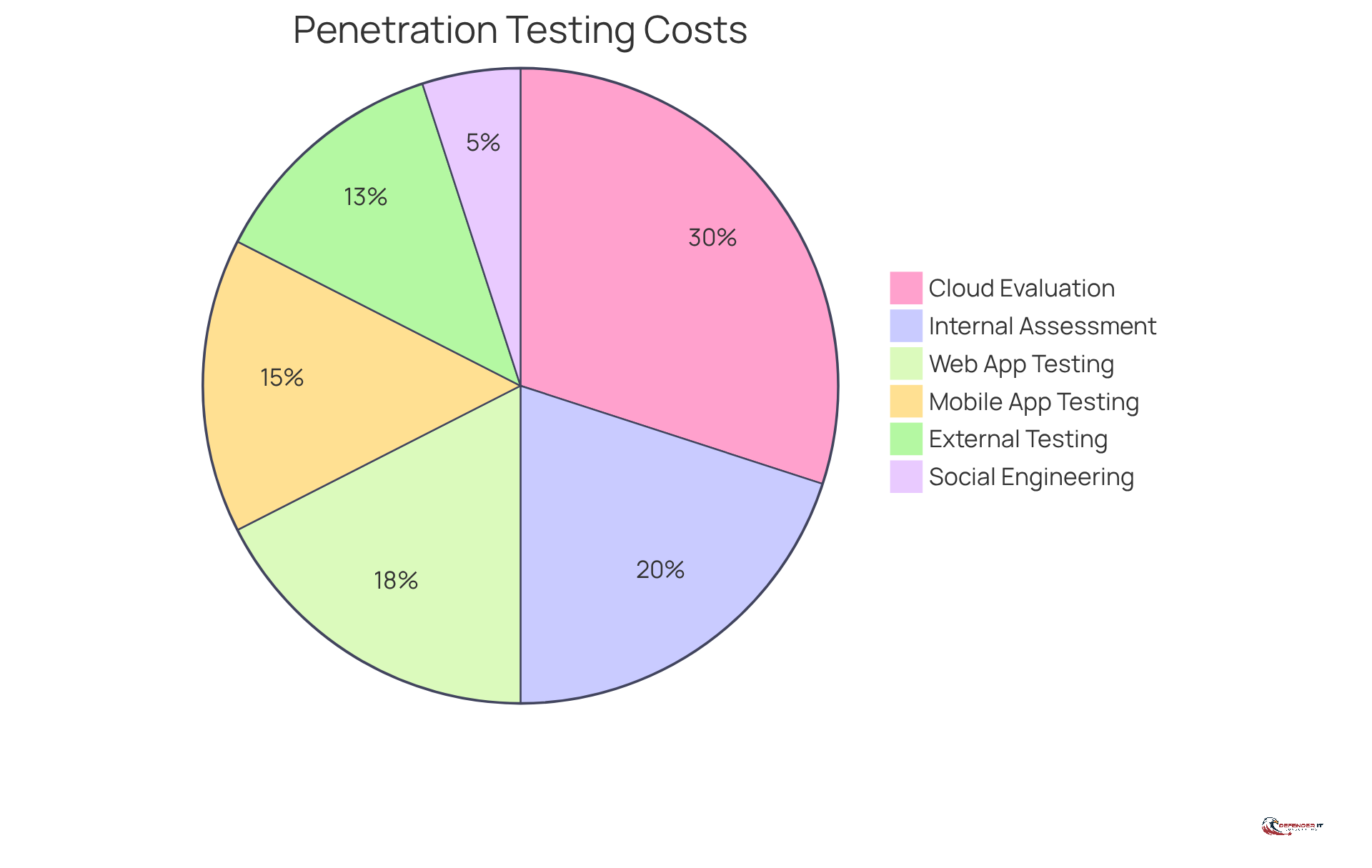
encompasses several types, each with unique :
- : This type focuses on assessing an organization’s external-facing assets, typically costing between $5,000 and $20,000. The price can vary based on the complexity of the systems involved and the specific requirements of the test.
- Internal Penetration Assessment: Evaluating the internal network and systems, this assessment often incurs higher expenses due to its complexity, ranging from $10,000 to $30,000. , as internal evaluations usually necessitate on-site presence and complete network mapping.
- : This assessment focuses on web applications to reveal weaknesses, with expenses ranging from $5,000 to $30,000, influenced by the application’s features and complexity. As web applications grow more advanced, comprehensive evaluation is essential, particularly given that .
- Mobile Application Penetration Evaluation: This evaluation can vary from $7,000 to $25,000, depending on the number of features and integrations within the mobile application. Considering that 95% of mobile applications have at least one security flaw, this assessment is essential for protecting user information.
- : Priced between $10,000 and $50,000, this evaluation addresses the unique security challenges posed by cloud environments, making it a significant investment for enterprises utilizing cloud services.
- Social Engineering Evaluation: Focusing on human factors, this assessment ranges from $2,000 to $10,000, depending on the scope of the engagement. It is essential for evaluating the effectiveness of a company’s .
Understanding these types of and the enables entities to select the most suitable approaches that align with their security requirements and financial limitations. Furthermore, organizations are urged to consider combining assessments to reduce expenses and to ensure that the evaluators they select possess pertinent certifications, which can enhance the quality and reliability of the evaluation process.
Detail the Stages of the Penetration Testing Process and Their Costs
The process encompasses several , each associated with :
- : This initial phase defines the objectives, scope, and methodology of the test. The costs for typically range from $1,000 to $5,000, depending on the complexity of the engagement.
- Reconnaissance: In this stage, testers gather information about the target systems, with costs ranging from $1,000 to $3,000.
- Scanning: This phase involves identifying live hosts, open ports, and services running on the target systems, costing approximately $2,000 to $5,000.
- Exploitation: Testers attempt to exploit identified vulnerabilities to gain access, with expenses usually varying from $3,000 to $10,000.
- Reporting: The documents findings and offers recommendations, which may range from $1,000 to $5,000.
Overall, the total can vary significantly based on the scope and complexity, typically ranging from $5,000 to over $50,000. Understanding these stages equips organizations to prepare for the .
Conclusion
Investing in network penetration testing is essential for organizations seeking to strengthen their cybersecurity defenses. By simulating potential cyberattacks, businesses can pinpoint vulnerabilities before they are exploited, thereby safeguarding sensitive data. This proactive approach not only bolsters security measures but also acts as a financial safeguard against the escalating costs associated with data breaches, which can reach millions.
The article examined several key factors that influence the costs of penetration testing. These factors include:
- The scope of the test
- The complexity of the environment
- The type of evaluation
- The experience of the testing team
- Compliance requirements
Each element significantly impacts the overall investment necessary for effective security assessments. Furthermore, understanding the various types of penetration testing – such as external, internal, web application, and cloud assessments – equips organizations with the insights needed to allocate budgets effectively and select the most appropriate testing strategies.
Ultimately, the importance of network penetration testing cannot be overstated. As cyber threats continue to evolve, organizations must prioritize regular security assessments to maintain a robust security posture. By acknowledging the costs associated with different types of testing and the stages involved in the process, security leaders can make informed decisions that not only enhance their defenses but also contribute to the long-term sustainability of their operations. Embracing a proactive approach to cybersecurity is crucial in today’s digital landscape, where the cost of inaction can far exceed the investment in preventive measures.
Frequently Asked Questions
What is network penetration testing?
Network penetration testing, also known as a network vulnerability assessment, is a simulated cyberattack on a computer system, network, or web application aimed at identifying weaknesses that could be exploited by malicious actors.
Why is penetration testing important for organizations?
Penetration testing is important because it helps organizations understand their security posture, uncovers vulnerabilities before they can be exploited, validates the effectiveness of existing protective measures, ensures compliance with regulatory requirements, and protects sensitive information from breaches.
What are the financial implications of not conducting security assessments?
The average cost of a data breach exceeds $4.88 million, making security assessments a financial safeguard against potential losses. Additionally, cybercrime is projected to cost businesses over $10 trillion by 2025, highlighting the necessity for routine security assessments.
What current trends are influencing penetration testing practices?
Current trends indicate a shift towards continuous evaluation models, reflecting the dynamic nature of cyber threats and the need for organizations to adapt their security strategies accordingly.
Who emphasizes the importance of security evaluations in cybersecurity?
Industry experts, such as Mikella Marley, emphasize the growing concern over vulnerabilities leading to breaches and underscore the vital role of security evaluations in maintaining a strong security posture.
. The costs listed indicate the typical range for that stage. Follow the arrows to understand the sequence of the process. Each box represents a stage in the penetration testing process. The costs listed indicate the typical range for that stage. Follow the arrows to understand the sequence of the process.](https://images.tely.ai/telyai/kbskzifx-each-box-represents-a-stage-in-the-penetration-testing-process-the-costs-listed-indicate-the-typical-range-for-that-stage-follow-the-arrows-to-understand-the-sequence-of-the-process.webp)