Introduction
In today’s rapidly evolving cyber threat landscape, organizations are increasingly relying on specialized Red Teams to strengthen their defenses. These expert groups simulate real-world attacks and provide critical insights into vulnerabilities that malicious actors may exploit. By understanding the strategies employed by Red Teams, businesses can significantly enhance their cybersecurity posture and cultivate a culture of resilience.
However, as the nature of cyber threats continues to change, organizations must consider how to effectively integrate these insights into their defensive strategies. This integration often involves overcoming inherent challenges related to collaboration and resource limitations. Addressing these challenges is essential for organizations aiming to fortify their defenses against an ever-changing array of cyber threats.
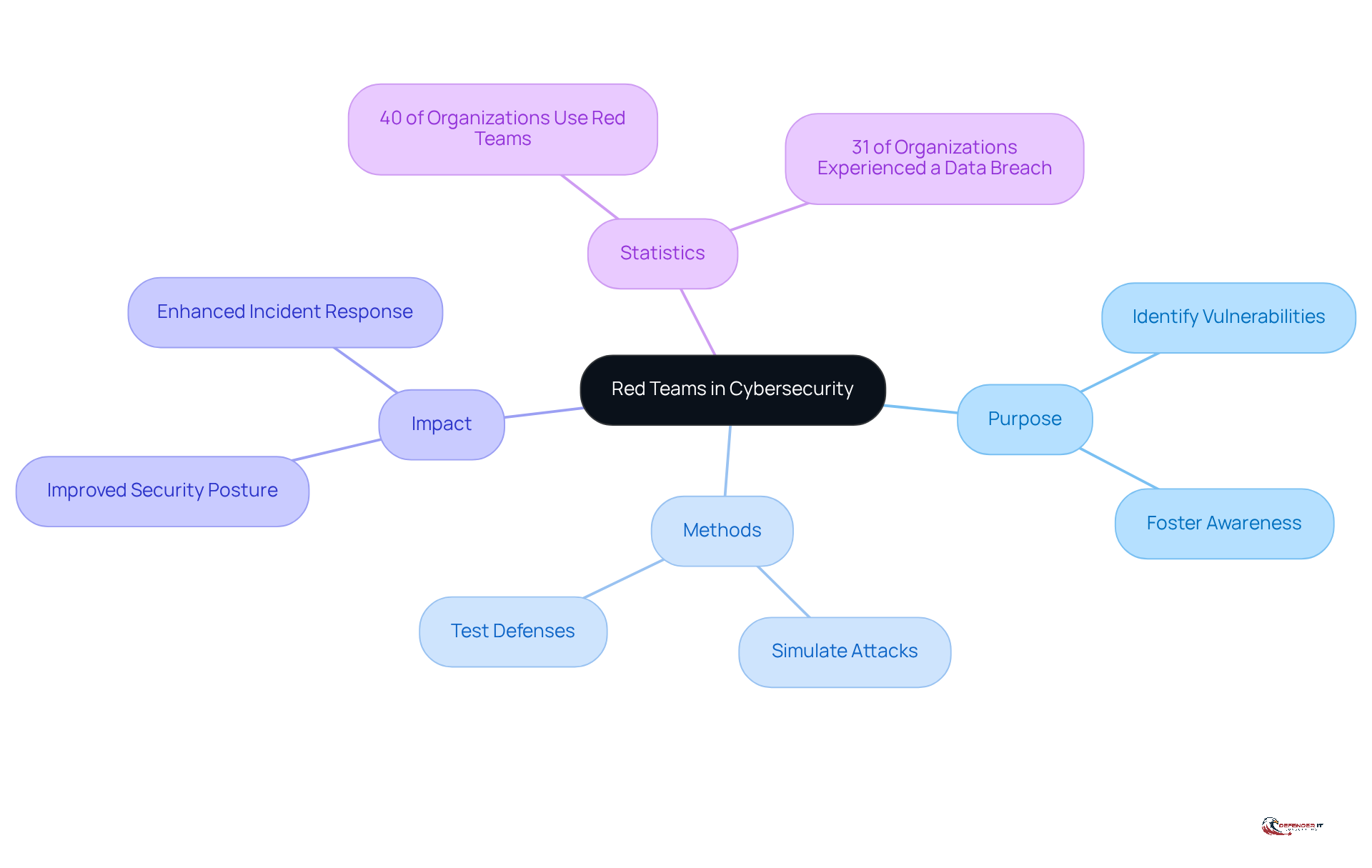
Define Red Teams and Their Purpose in Cybersecurity
consists of specialized groups of that simulate the tactics, techniques, and procedures (TTPs) of real-world adversaries to rigorously test a company’s defenses. Their primary objective is to uncover weaknesses within a company’s defense posture by mimicking the actions of potential intruders. This , as it allows organizations to gain a comprehensive and enhance their overall security measures. Approximately 40% of organizations utilize Red Teams for cybersecurity assessments, reflecting a growing recognition of their value in fortifying defenses. Moreover, with 31% of organizations experiencing a data breach, the urgency for effective is evident.
Successful engagements of have proven essential in identifying , with numerous organizations reporting following these evaluations. emphasize that the purpose of Red Teams extends beyond mere testing; they play a vital role in fostering a culture of awareness and resilience within organizations. As noted by specialists, “There’s no silver bullet solution with cybersecurity; ,” highlighting the necessity for continuous enhancement of protective strategies and prioritization of vulnerability remediation.
By conducting realistic attack simulations, provides invaluable insights that inform protective strategies and enhance . Their role in identifying vulnerabilities is increasingly recognized as a cornerstone of effective cybersecurity, ensuring that organizations are better prepared to defend against evolving threats in a rapidly changing digital landscape.
Explore Red Team Methodologies and Processes
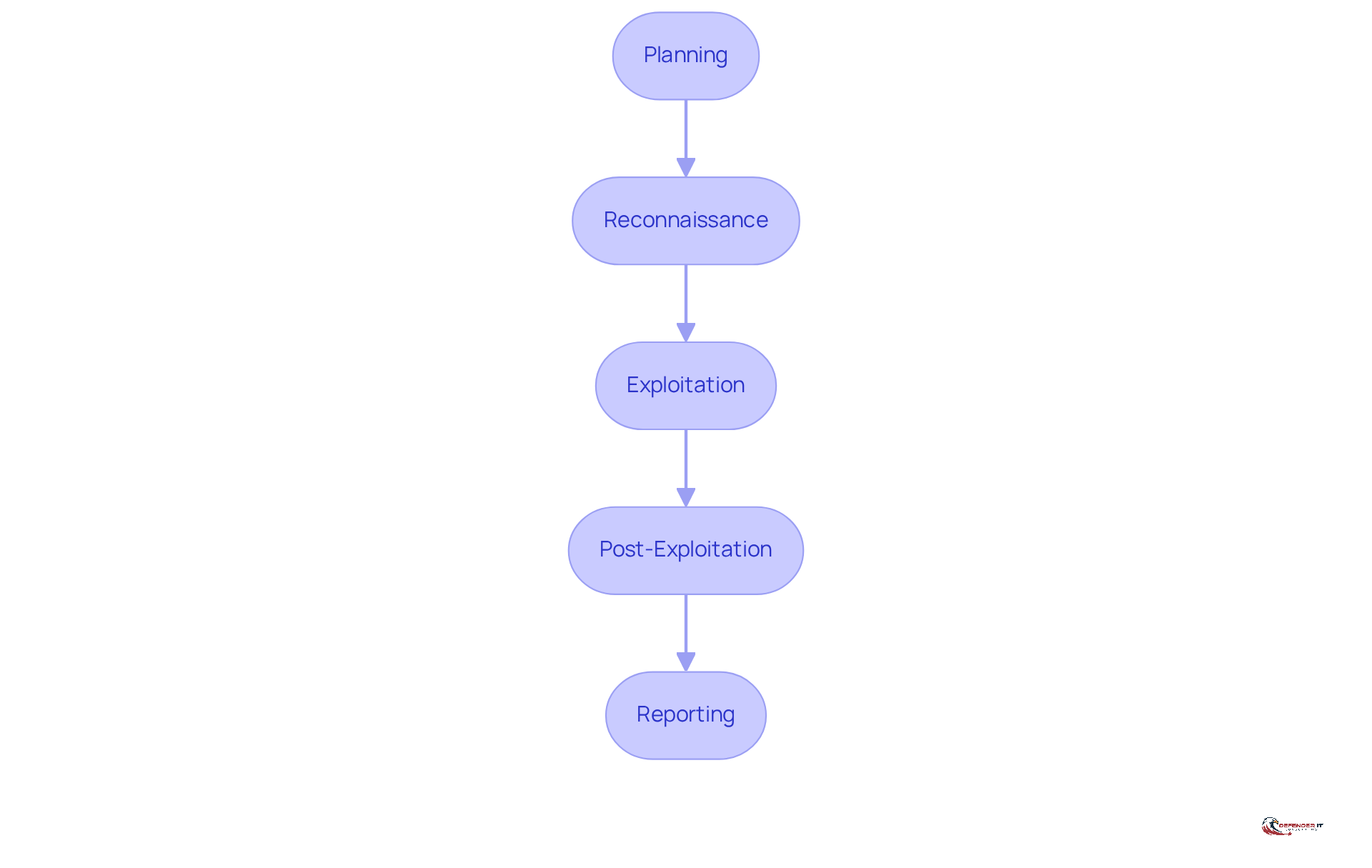
adhere to a structured approach, encompassing several key phases:
- Planning: This initial phase involves establishing clear objectives and defining the scope of the engagement.
- Reconnaissance: In this phase, intelligence is gathered about the target environment to identify potential vulnerabilities.
- Exploitation: Here, attempts are made to breach defenses using various attack vectors.
- Post-Exploitation: This phase assesses the impact of the breach while maintaining access to gather further intelligence.
- Reporting: Finally, findings are documented, and are provided.
This organized methodology ensures that Red Teams can effectively simulate attacks, offering organizations a .
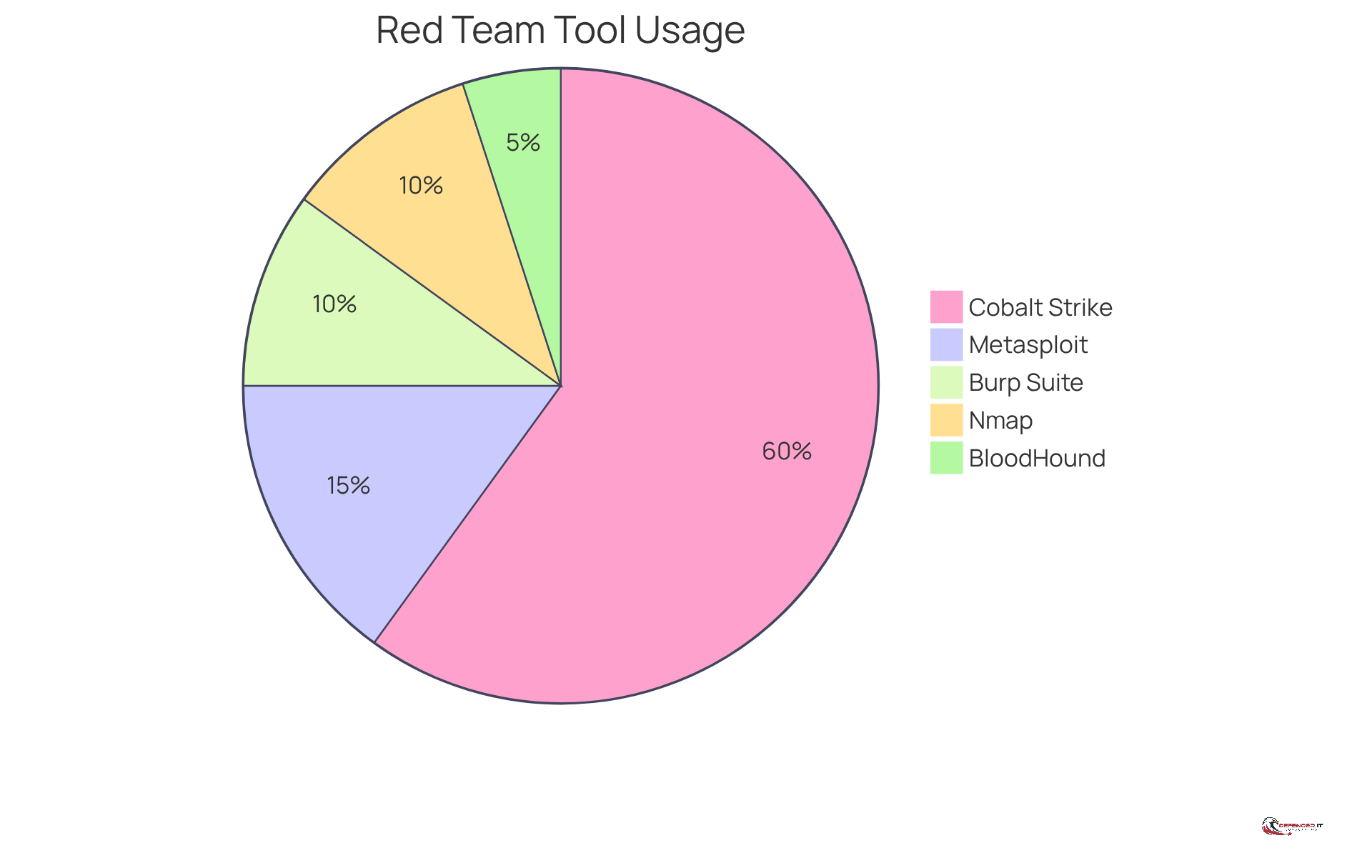
Identify Tools and Techniques Used by Red Teams
The it security red team utilizes a diverse array of tools and techniques to effectively simulate attacks and evaluate vulnerabilities. Among the most widely employed tools are:
- : This commercial platform is renowned for its capabilities in adversary simulations and post-exploitation activities. Approximately 60% of red teams globally leverage , which is pivotal for simulating advanced persistent threats (APTs) and includes features for command-and-control operations. As Joe Pettit, Managing Director, states, “Nothing offers a better comprehension of your protective stance like allowing a red team to engage in your environment to replicate a real-world attack.”
- Metasploit: An open-source framework that facilitates the development and execution of exploit code against remote targets. It is particularly valued for its extensive exploit library and post-exploitation modules, making it a staple in . Adam Fletcher, CISO, emphasizes that “Cybersecurity isn’t about avoiding risk – it’s about managing it intelligently. The future belongs to leaders who make a competitive advantage.”
- Burp Suite: A comprehensive designed to identify vulnerabilities within web applications, thereby enhancing the security posture of online services.
- Nmap: A powerful that discovers hosts and services on a network, providing critical insights into potential entry points for attackers.
- BloodHound: A specialized tool for analyzing Active Directory permissions and relationships, assisting teams in understanding and mitigating risks associated with user access.
Red teams frequently employ methods such as , phishing, and leveraging known vulnerabilities to gain unauthorized access to systems, thereby exposing significant flaws in a company’s defenses. The integration of tools like and into it security red team exercises not only enhances the realism of simulations but also ensures that organizations are better prepared to defend against evolving cyber threats. As of 2026, Cobalt Strike continues to receive updates, maintaining its relevance in the ever-changing landscape of cybersecurity.
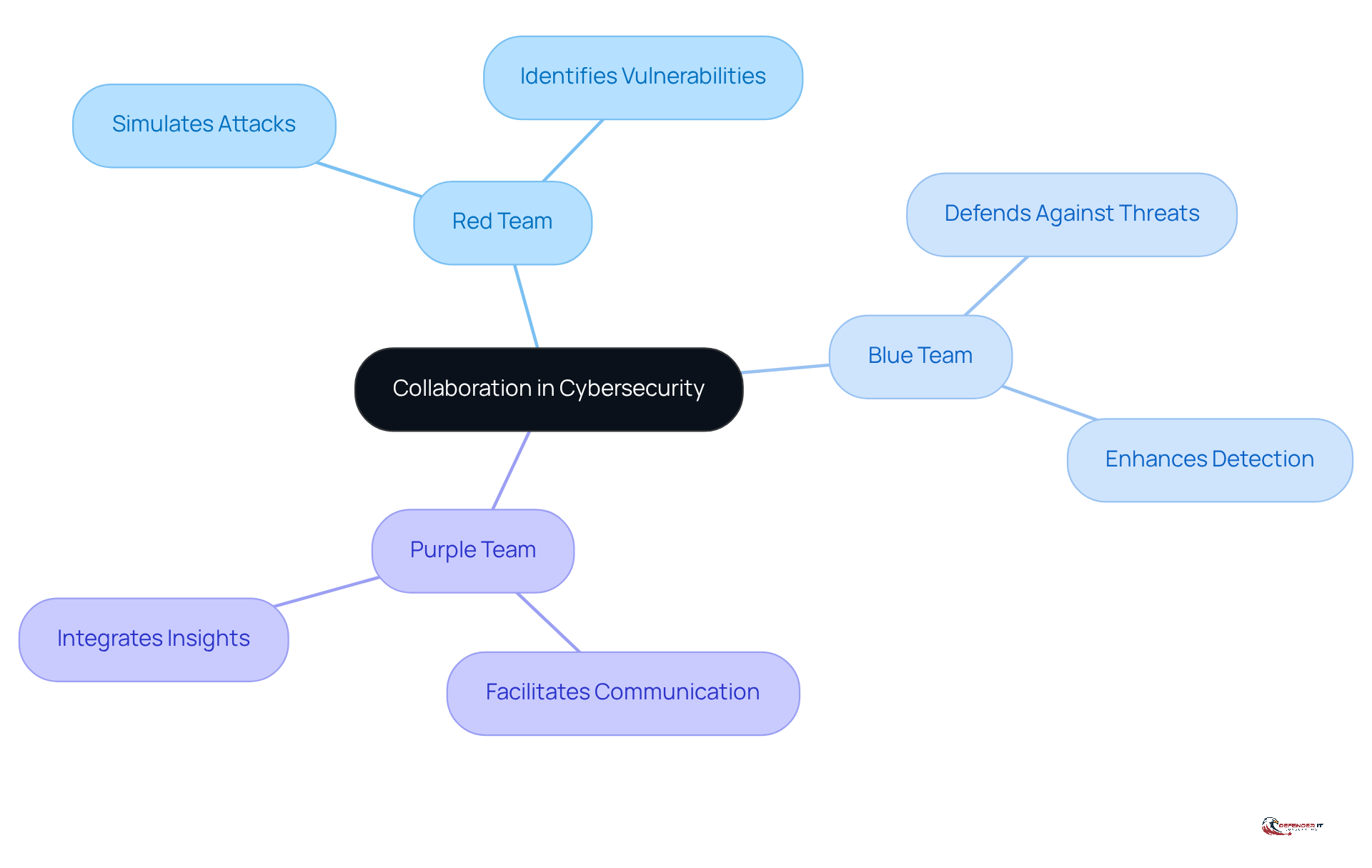
Understand Collaboration Between Red, Blue, and Purple Teams
Collaboration among Red, Blue, and Purple groups is crucial for establishing a robust . The IT security to identify vulnerabilities, while Blue Groups concentrate on defending against these threats and enhancing detection and response capabilities. Purple Teams serve as a bridge between these two groups, facilitating communication and ensuring that insights from Red Team exercises are effectively integrated into Blue Team operations. This cooperative approach not only but also fosters a culture of continuous improvement and shared knowledge.
Organizations that implement Purple Teaming experience a , with studies indicating a 40% improvement in security performance. Successful case studies, such as those highlighted in research on the , demonstrate that this integration leads to more and a proactive stance against . Consequently, Purple Collaborators emerge as a vital component of contemporary cybersecurity strategies.
However, it is essential to recognize the , including siloed data and limited resources. in addressing these issues, further underscoring their significance in the cybersecurity landscape.
Conclusion
The integration of IT security Red Teams is essential in the ongoing fight against cyber threats, acting as a proactive strategy to identify and mitigate vulnerabilities within an organization’s defenses. By emulating the tactics of real-world adversaries, these specialized teams not only reveal weaknesses but also cultivate a culture of resilience and awareness, which is critical for effective cybersecurity. The growing reliance on Red Teams is underscored by the fact that 40% of organizations currently utilize them, highlighting their increasing significance in strengthening defenses amid a rise in data breaches.
Key insights from this analysis illustrate the structured methodologies employed by Red Teams, encompassing:
- Planning
- Reconnaissance
- Exploitation
- Post-exploitation
- Reporting
Each phase is meticulously designed to provide comprehensive insights into an organization’s security posture, ensuring that vulnerabilities are identified and addressed with actionable recommendations. Moreover, the collaboration between Red, Blue, and Purple Teams enhances the overall effectiveness of cybersecurity strategies, emphasizing that teamwork is crucial in establishing a robust defense against evolving threats.
Ultimately, incorporating Red Team strategies into an organization’s cybersecurity framework is vital for staying ahead of potential attacks. As the digital landscape evolves, adopting these methodologies and fostering collaboration among security teams will be essential in building a resilient and effective defense. Organizations are urged to prioritize the implementation of Red Team assessments and to nurture a culture of continuous improvement to protect against the persistent risks posed by cyber threats.
Frequently Asked Questions
What is a Red Team in cybersecurity?
A Red Team consists of specialized groups of cybersecurity experts who simulate the tactics, techniques, and procedures (TTPs) of real-world adversaries to rigorously test a company’s defenses.
What is the primary purpose of a Red Team?
The primary objective of a Red Team is to uncover weaknesses within a company’s defense posture by mimicking the actions of potential intruders, enabling organizations to understand their vulnerabilities and enhance their security measures.
How prevalent is the use of Red Teams among organizations?
Approximately 40% of organizations utilize Red Teams for cybersecurity assessments, indicating a growing recognition of their value in strengthening defenses.
Why is the role of Red Teams considered crucial in cybersecurity?
Red Teams are crucial because they help identify critical vulnerabilities, foster a culture of awareness and resilience, and provide insights that inform protective strategies and enhance incident response capabilities.
What percentage of organizations have experienced a data breach?
About 31% of organizations have reported experiencing a data breach, highlighting the urgency for effective vulnerability identification.
Do Red Teams only focus on testing security measures?
No, Red Teams also play a vital role in fostering a culture of awareness and resilience within organizations, emphasizing the need for continuous enhancement of protective strategies and prioritization of vulnerability remediation.
What approach do cybersecurity experts recommend for effective defense?
Cybersecurity experts recommend a layered defense approach, as there is no single solution to cybersecurity challenges. Continuous improvement of protective strategies is essential.
How do Red Teams contribute to an organization’s preparedness against threats?
By conducting realistic attack simulations, Red Teams provide invaluable insights that help organizations be better prepared to defend against evolving threats in a rapidly changing digital landscape.
List of Sources
- Define Red Teams and Their Purpose in Cybersecurity
- 25+ Best Cybersecurity Quotes (https://atera.com/blog/best-cybersecurity-quotes)
- omnicybersecurity.com (https://omnicybersecurity.com/case_studies/case-study-inside-a-red-team-engagement)
- 9 Quotes that Capture the State of Offensive Security (https://netspi.com/blog/executive-blog/security-industry-trends/quotes-on-the-state-of-offensive-security)
- 70 Cybersecurity Quotes Every Leader Should Know (https://deliberatedirections.com/cybersecurity-quotes)
- Identify Tools and Techniques Used by Red Teams
- Top 7 Red Teaming Tools in 2026 (https://aimultiple.com/red-team-tools)
- The Best Red Teaming Tools of 2026: What You Need to Know (https://itsecurityguru.org/2025/12/11/the-best-red-teaming-tools-of-2026-what-you-need-to-know)
- The top 20 expert quotes from the Cyber Risk Virtual Summit (https://diligent.com/resources/blog/top-20-quotes-cyber-risk-virtual-summit)
- Understand Collaboration Between Red, Blue, and Purple Teams
- The top 20 expert quotes from the Cyber Risk Virtual Summit (https://diligent.com/resources/blog/top-20-quotes-cyber-risk-virtual-summit)
- Understanding Purple Teaming: Enhancing Enterprise Cybersecurity Through Collaborative Defense (https://mad20.com/mad20-updates/copilot-not-autopilot-0-0-0-0)
- The 20 Best Quotes from Cyber Risk Leaders (https://revival-holdings.com/20-best-quotes-from-cyber-risk-leaders)
- Red + Blue Team: How Purple Teaming enhances cyber security (https://insights.integrity360.com/red-blue-team-how-purple-teaming-enhances-cyber-security)
- plextrac.com (https://plextrac.com/survey-says-improve-your-security-posture-by-purple-teaming)