Introduction
Understanding the complexities of a SOC 3 audit is crucial for organizations seeking to enhance their security and compliance frameworks. This third-party evaluation not only demonstrates a company’s dedication to protecting sensitive information but also builds trust among clients and stakeholders. However, navigating the intricate landscape of SOC 3 compliance presents significant challenges. Businesses must prepare effectively for this essential audit, ensuring they meet all necessary requirements while maximizing the benefits it provides.
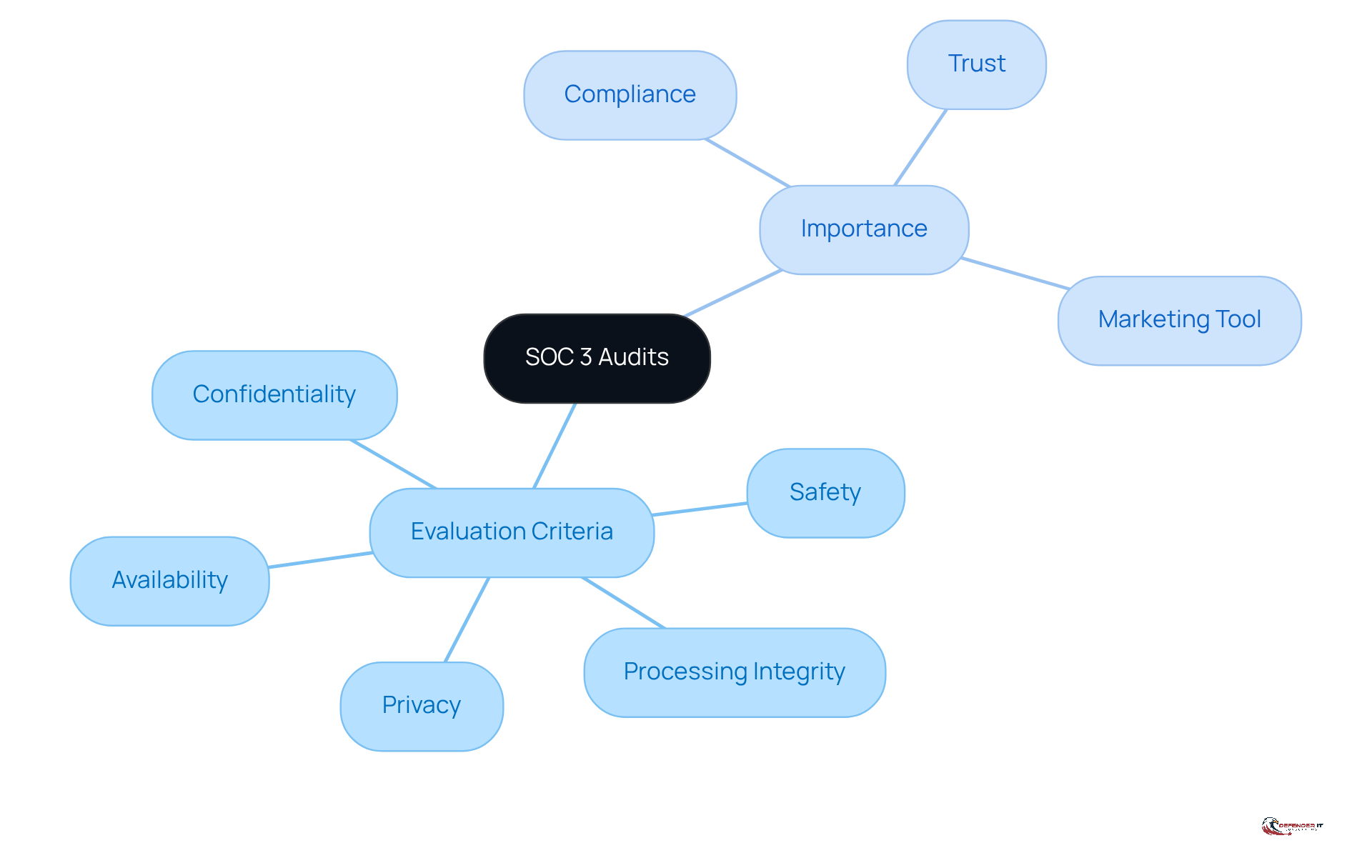
Understand SOC 3 Audits and Their Importance
A , or , represents a third-party assessment that scrutinizes a company’s controls concerning safety, availability, processing integrity, confidentiality, and privacy. In contrast to SOC 2 reports, which are comprehensive and limited in scope, SOC 3 reports are designed for public dissemination. They provide a of a company’s commitment to maintaining .
Understanding the is essential for companies. These evaluations not only but also . Furthermore, the serves as a , showcasing a company’s dedication to and ensuring operational integrity.
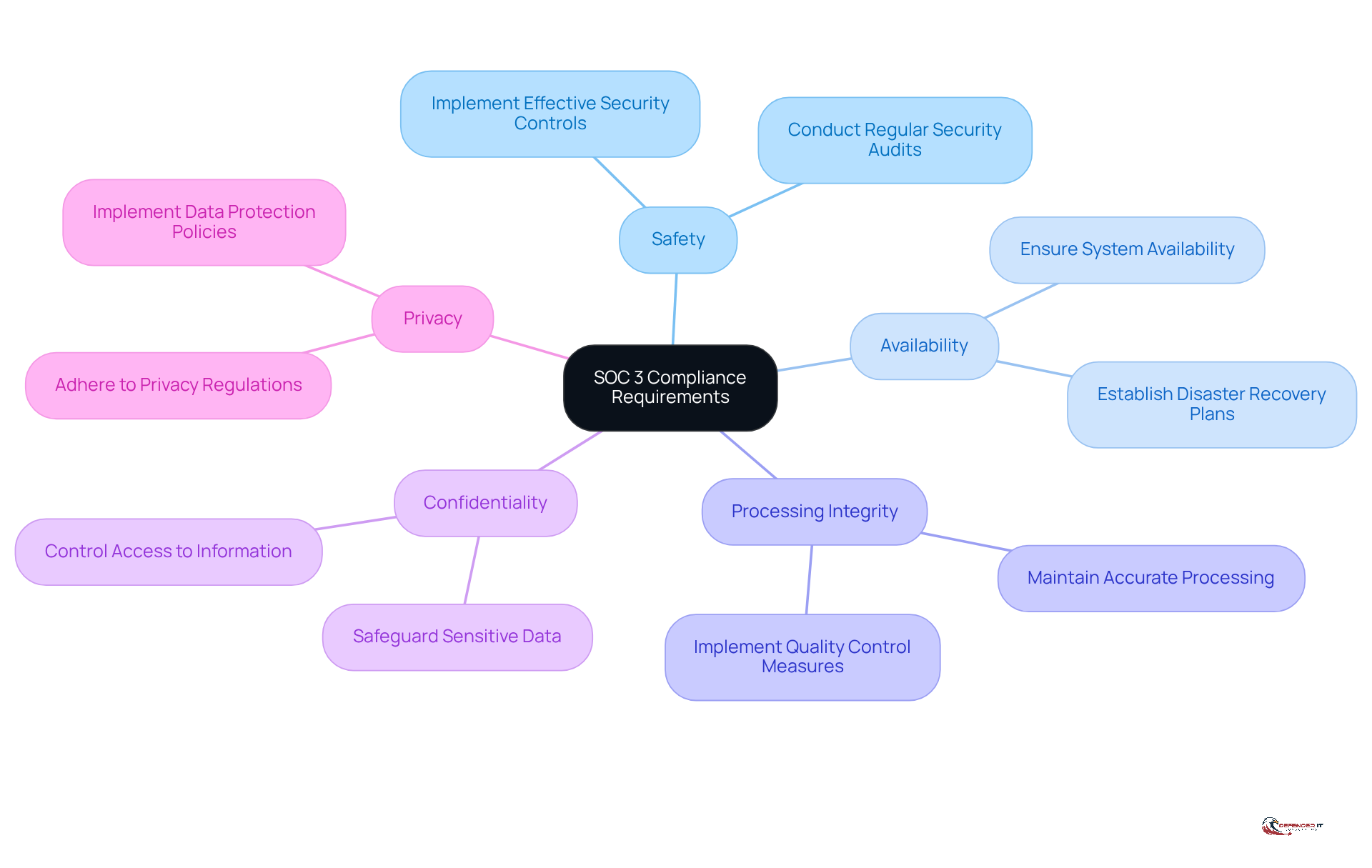
Identify SOC 3 Compliance Requirements
To achieve , entities must adhere to the AICPA’s (TSC), which include:
- Safety
- Availability
- Processing integrity
- Confidentiality
- Privacy
Each criterion outlines specific requirements that organizations must fulfill, such as implementing effective , ensuring system availability, and safeguarding .
Organizations should conduct a comprehensive review of their existing policies and procedures to identify any . This process may involve consulting with compliance experts or utilizing to ensure that all criteria are adequately addressed. Notably, obtaining a SOC 3 audit necessitates an existing , highlighting the interconnectedness of these .
By thoroughly understanding these requirements, companies can streamline their readiness for evaluation. As highlighted, the SOC 3 audit is becoming a standard for entities that process, store, or manage , reinforcing its importance in fostering trust with stakeholders.
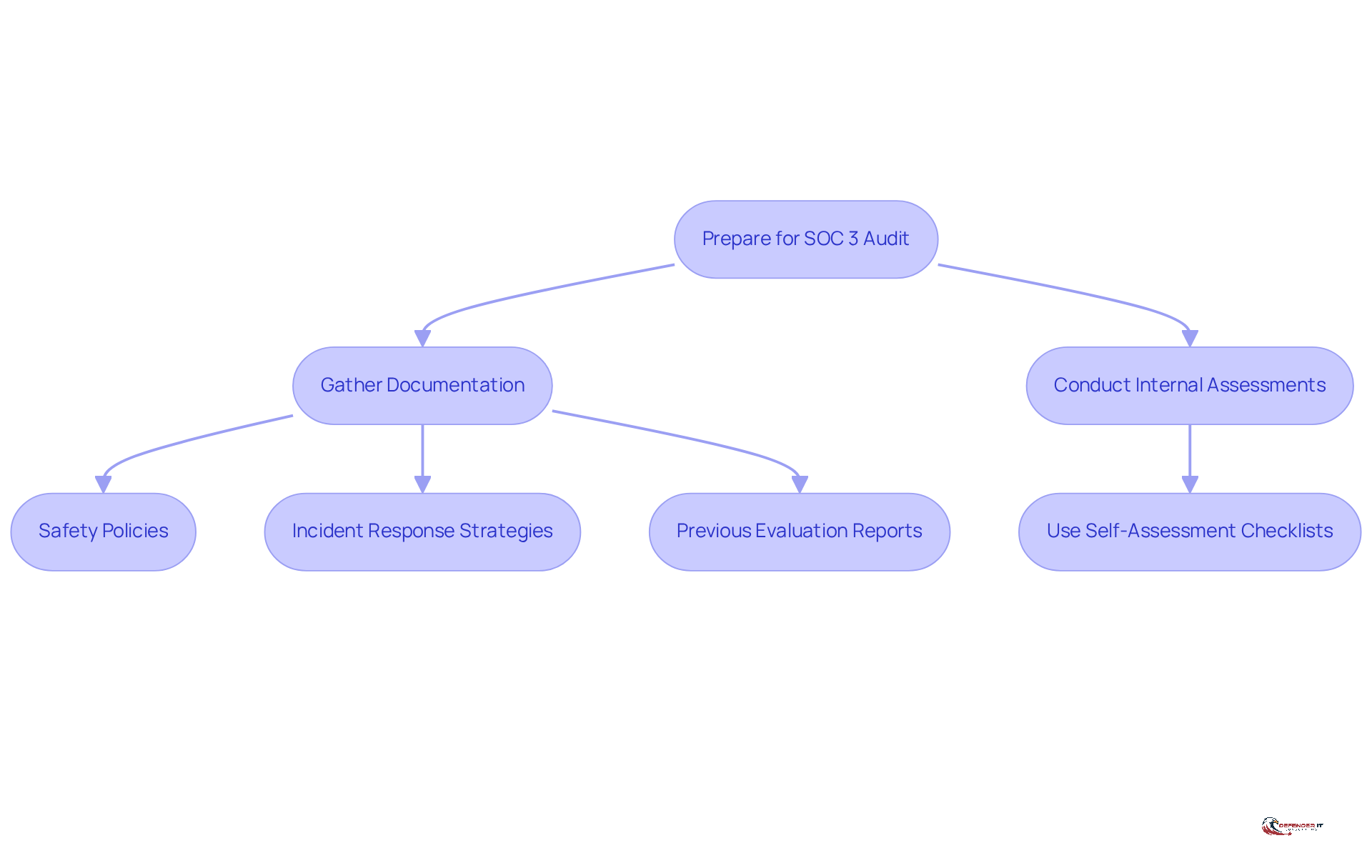
Gather Documentation and Conduct Internal Assessments
To prepare for a in 2026, entities should begin by gathering all relevant documentation, including:
- Safety policies
- Incident response strategies
- Previous evaluation reports
An is essential; this process involves evaluating existing controls against the requirements of a . Organizations can utilize or frameworks, such as those developed by Jacques Boucher, to identify strengths and weaknesses in their . This proactive approach not only readies entities for the review but also allows them to before the formal assessment. Notably, research indicates that approximately 70% of organizations conduct internal evaluations prior to reviews, underscoring the significance of this practice in enhancing and operational resilience. As Brett Shavers aptly states, “,” highlighting in the review preparation process. Regular in security practices, which is vital in today’s rapidly evolving threat landscape.
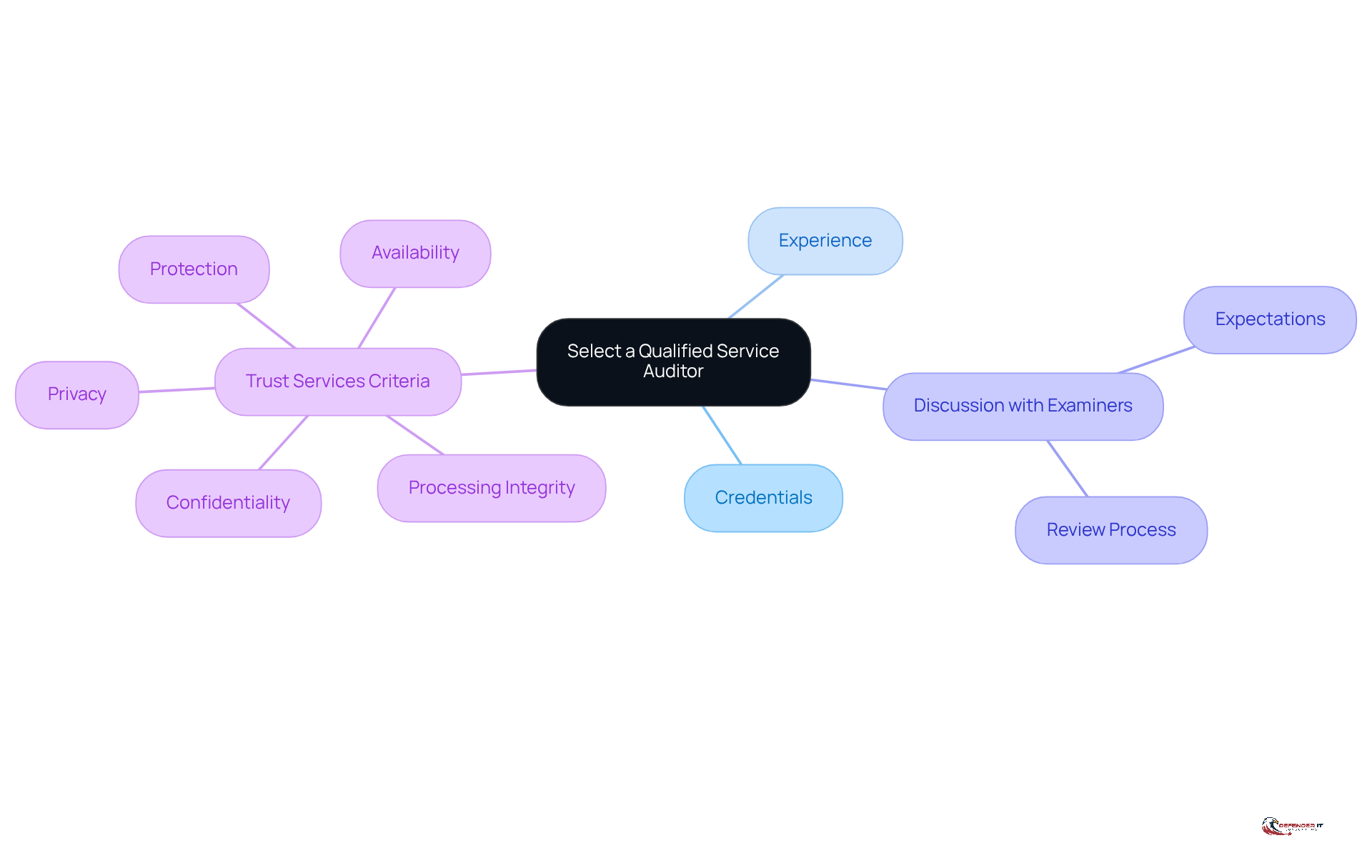
Select a Qualified Service Auditor
Choosing a competent service auditor is crucial for achieving a successful . Organizations should prioritize (CPAs) who have demonstrated experience in conducting SOC evaluations, particularly within their specific industry. It is essential to verify the auditor’s credentials, reputation, and track record; organizations can request references or case studies to assess their expertise. Engaging in discussions about the review process and expectations with prospective examiners fosters alignment and clarity.
A certified examiner not only conducts the evaluation but also offers valuable insights and recommendations for . s usually take between 3 to 12 months, depending on the complexity and sensitivity of data processing. The auditor’s expertise significantly impacts the quality of the , as auditors assess controls based on the five (TSCs):
- Protection
- Processing integrity
- Availability
- Confidentiality
- Privacy
Organizations that invest time in are better equipped to navigate the complexities of a and improve their overall . A favorable evaluation from the auditor allows the entity to claim compliance, while failing to secure such assessments can lead to challenges in attracting future sign-ups and potential penalties under PCI-DSS regulations. Resources like Microsoft’s Service Trust Portal can also assist entities in preparing for the evaluation.
Navigate the SOC 3 Audit Process
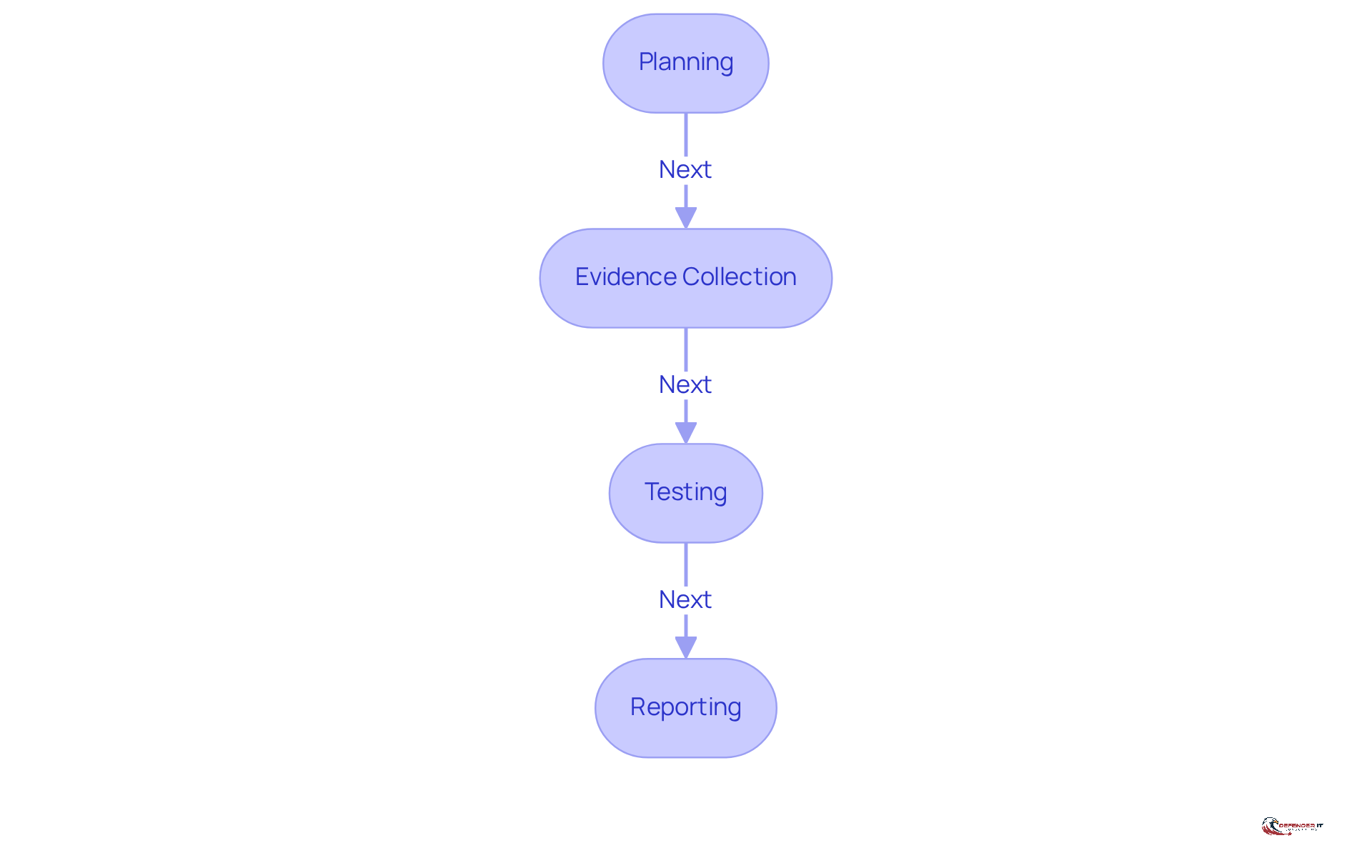
The consists of several key phases:
- Planning
- Testing
- Reporting
Initially, organizations must collaborate closely with their auditor to define the scope and objectives of the evaluation. This planning stage is crucial for setting clear expectations and ensuring alignment between the organization and the auditor.
Following planning, the phase involves gathering necessary documentation and data to substantiate the audit findings. This may include various forms of evidence, such as policies, procedures, and records that demonstrate .
Next, auditors will test the effectiveness of the controls in place. This may involve conducting interviews with staff and reviewing to assess how well the organization adheres to the Trust Services Criteria.
Finally, the auditor compiles a comprehensive report that summarizes the findings and provides an opinion on the entity’s compliance with the . Throughout this process, it is essential for organizations to maintain open communication with their auditor to address any issues that may arise, ensuring a smooth .
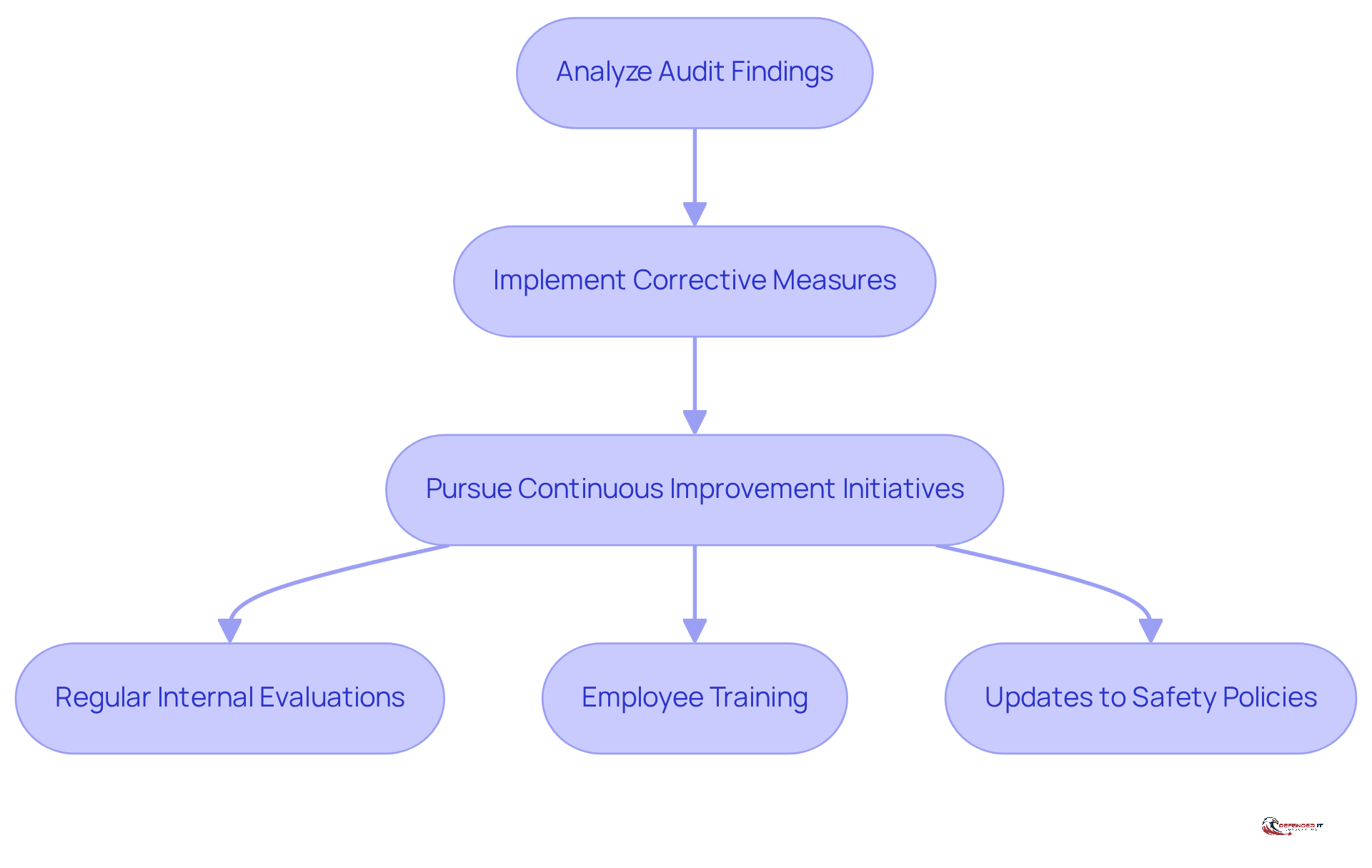
Implement Post-Audit Actions and Continuous Improvement
After a soc 3 audit, it is essential for entities to thoroughly analyze the findings and recommendations of the auditor. Implementing corrective measures for any identified weaknesses is crucial for enhancing protective practices. Notably, 76% of entities plan to pursue following the audit, recognizing that a robust is vital. This plan should encompass:
- Regular
- Updates to
For instance, companies can introduce that highlight emerging and best practices, ensuring that all staff members are equipped to bolster the entity’s defensive posture.
This not only aids in but also fortifies the entity’s overall safety framework. By treating the , organizations can better prepare for future audits and adapt to the constantly evolving landscape of . As Robin Sharma aptly stated, ‘Small daily improvements over time lead to stunning results.’ Embracing this mindset can yield significant advancements in security and compliance, ultimately enhancing organizational resilience.
Conclusion
Mastering the SOC 3 audit is essential for organizations that wish to demonstrate their commitment to security and compliance. This process not only reinforces a company’s credibility but also fosters trust among clients and stakeholders. By recognizing the significance of SOC 3 audits, organizations can position themselves as leaders in data protection and operational integrity, ultimately enhancing their marketability and reputation.
Key steps for achieving SOC 3 compliance include:
- Identifying compliance requirements
- Gathering necessary documentation
- Selecting a qualified service auditor
- Navigating the audit process
- Implementing post-audit actions
Each step is vital in ensuring that organizations are prepared for the audit and capable of addressing any weaknesses identified during the evaluation. Proactive measures, such as conducting internal assessments and fostering a culture of continuous improvement, are essential for maintaining compliance and enhancing security practices.
In a landscape where data breaches and compliance failures can have severe consequences, embracing the SOC 3 audit process transcends mere regulatory compliance; it represents a strategic initiative that can lead to sustained organizational resilience. Companies should view the SOC 3 audit as an ongoing journey rather than a one-time event. By committing to continuous improvement and regularly updating safety protocols, organizations can better protect themselves against evolving threats and ensure long-term success in a competitive environment.
Frequently Asked Questions
What is a SOC 3 audit?
A SOC 3 audit, or System and Controls 3 evaluation, is a third-party assessment that evaluates a company’s controls related to safety, availability, processing integrity, confidentiality, and privacy. Unlike SOC 2 reports, SOC 3 reports are designed for public dissemination and provide a high-level summary of a company’s security practices.
Why are SOC 3 audits important for companies?
SOC 3 audits are significant as they demonstrate compliance with industry standards, enhance trust among clients and stakeholders, and serve as a marketing tool to showcase a company’s commitment to protecting sensitive information and ensuring operational integrity.
What are the compliance requirements for a SOC 3 audit?
To achieve SOC 3 audit compliance, organizations must adhere to the AICPA’s Trust Services Criteria (TSC), which include safety, availability, processing integrity, confidentiality, and privacy. Each criterion has specific requirements that organizations must fulfill.
How can organizations prepare for a SOC 3 audit?
Organizations should conduct a comprehensive review of their existing policies and procedures to identify compliance gaps. This may involve consulting with compliance experts or using compliance management tools to ensure all criteria are adequately addressed.
Is a SOC 2 report necessary for obtaining a SOC 3 audit?
Yes, obtaining a SOC 3 audit requires an existing SOC 2 report, highlighting the interconnectedness of these compliance frameworks.
Who benefits from a SOC 3 audit?
Companies that process, store, or manage customer data benefit from SOC 3 audits, as they reinforce trust with stakeholders and demonstrate a commitment to security and operational integrity.
List of Sources
- Understand SOC 3 Audits and Their Importance
- SOC 3: compliance (https://cloud.google.com/security/compliance/soc-3)
- What You Need to Know About SOC 3 Reports | Schellman (https://schellman.com/blog/soc-examinations/soc-3-reports-explained)
- SOC 3 report: What it is and why it matters | ScalePad (https://scalepad.com/blog/soc-3-report-what-it-is-and-why-it-matters)
- What Is a SOC 3 Compliance Report? Everything You Need to Know (https://ispartnersllc.com/blog/when-to-consider-soc-3-audit)
- Identify SOC 3 Compliance Requirements
- SOC 3 report: What it is and why it matters | ScalePad (https://scalepad.com/blog/soc-3-report-what-it-is-and-why-it-matters)
- What You Need to Know About SOC 3 Reports | Schellman (https://schellman.com/blog/soc-examinations/soc-3-reports-explained)
- 115 Compliance Statistics You Need To Know in 2023 – Drata (https://drata.com/blog/compliance-statistics)
- 110 security and compliance statistics for tech leaders to know in 2025 (https://vanta.com/resources/compliance-statistics)
- 130+ Compliance Statistics & Trends to Know for 2026 (https://secureframe.com/blog/compliance-statistics)
- Gather Documentation and Conduct Internal Assessments
- Importance of Documentation – Expert and Influential Leader Quotes : Erase Your Risk with Proper Documentation (https://forensicnotes.com/importance-of-documentation-expert-and-influential-leader-quotes)
- isorobot.io (https://isorobot.io/blog/key-internal-audit-management-trends-and-statistics)
- Select a Qualified Service Auditor
- Comprehensive SOC 3 Guide: Trust, Security, & Compliance (https://nordlayer.com/learn/soc/soc-3)
- Not All SOC Audits Are Created Equal: How to Select a Quality Auditor – Moore Colson (https://moorecolson.com/news-insights/not-all-soc-audits-are-created-equal-how-to-select-a-quality-auditor)
- Audit Quotes (8 quotes) (https://goodreads.com/quotes/tag/audit)
- Quotes for Auditors and Investigators | Famous and Factual Quotations (https://projectauditors.com/Company/Auditor_Quotes_Investigator_Investigations.php)
- Implement Post-Audit Actions and Continuous Improvement
- tallyfy.com (https://tallyfy.com/continuous-improvement-quotes)
- 85 Quotes – Operational Excellence and Continuous Improvement | Rever (https://reverscore.com/85-quotes-operational-excellence-and-continuous-improvement)
- 130+ Compliance Statistics & Trends to Know for 2026 (https://secureframe.com/blog/compliance-statistics)
- 26 Quotes About Improving Processes That Will Inspire Change (https://niagarainstitute.com/blog/quotes-improving-processes)