Introduction
The increasing frequency of cyber incidents necessitates that organizations adopt structured frameworks for effective incident management. The NIST Incident Response Framework serves as a comprehensive guide, providing essential components and strategies that significantly enhance an organization’s security posture. Despite this, only 45% of companies currently possess a robust incident response strategy. This raises a critical question: how can organizations not only implement this framework but also ensure it evolves to address the ever-changing landscape of cybersecurity threats?
Understand the NIST Incident Response Framework Components
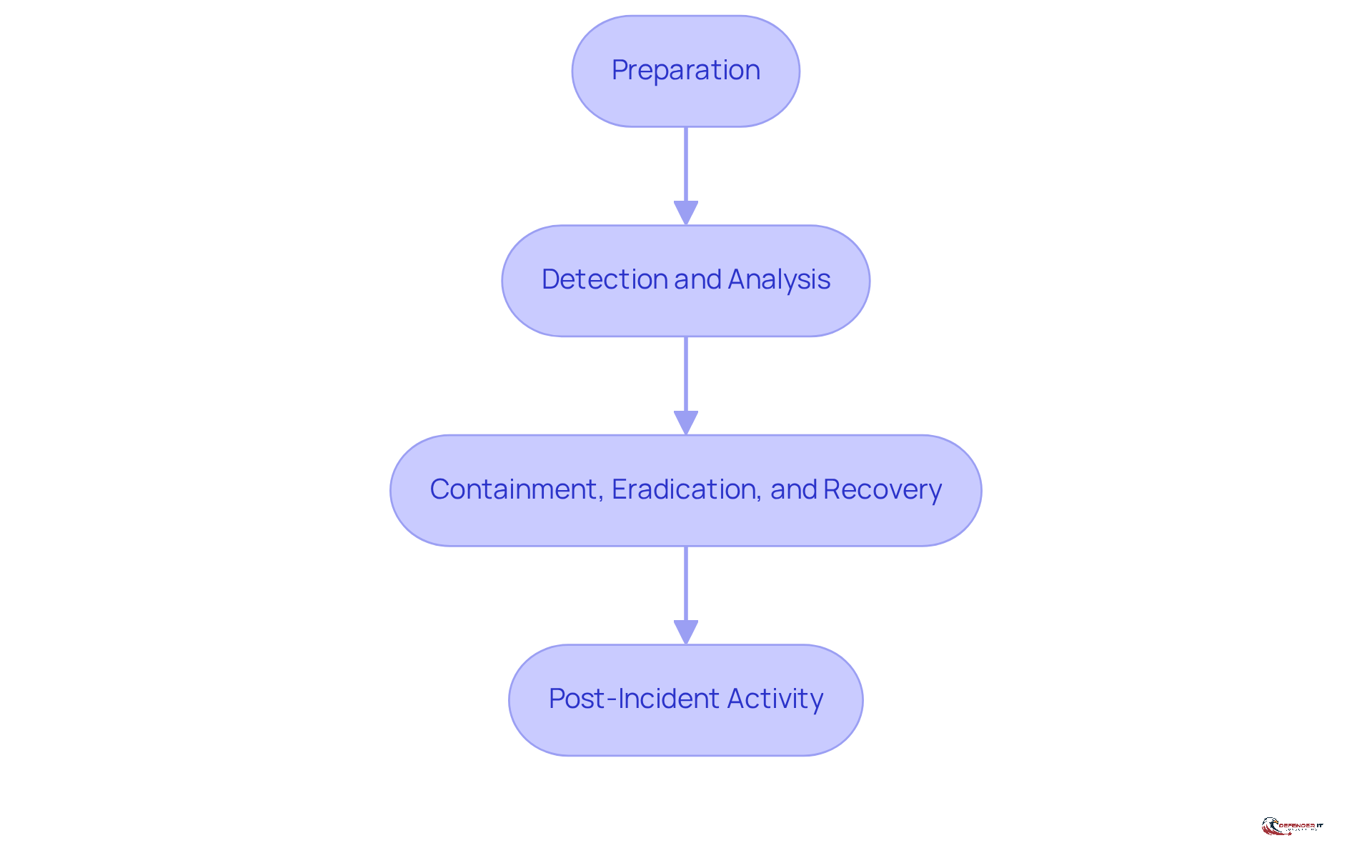
The structured approach provided by the NIST Incident Response Framework helps organizations effectively manage cybersecurity incidents. It consists of several key components:
-
Preparation: This involves establishing essential policies, procedures, and tools to ensure a robust response capability. Organizations should regularly assess and update their response plans to maintain effectiveness. Notably, proactive responders increased to 68% in 2024, reflecting a growing trend toward proactive event management.
-
Detection and Analysis: Timely identification of incidents is critical. This phase requires continuous monitoring of systems and thorough analysis of alerts to understand the nature and scope of incidents as they unfold. The SolarWinds cyberattack underscores the necessity of rapid asset inventory and effective detection strategies.
-
Containment, Eradication, and Recovery: Upon detecting an incident, immediate actions must be taken to contain the threat, eliminate it, and restore systems to normal operations. Effective containment strategies can significantly reduce the impact of incidents; for instance, companies that manage a breach in under 30 days save over $1 million compared to those that take longer. Furthermore, statistics reveal that 88% of firms with emergency management plans also have cyber insurance, highlighting the connection between preparedness and risk management.
-
Post-Incident Activity: After an incident, organizations should conduct a thorough assessment to extract lessons learned and enhance future efforts. This reflective practice is vital for continuous improvement in incident management.
Understanding these components is crucial for organizations aiming to develop a comprehensive response strategy in accordance with the NIST Incident Response Framework that meets their specific needs and complies with regulatory standards. Current statistics indicate that only 45% of companies have a strategy for managing incidents, emphasizing the urgent need for proactive measures in cybersecurity preparedness.
Implement the NIST Incident Response Lifecycle Phases
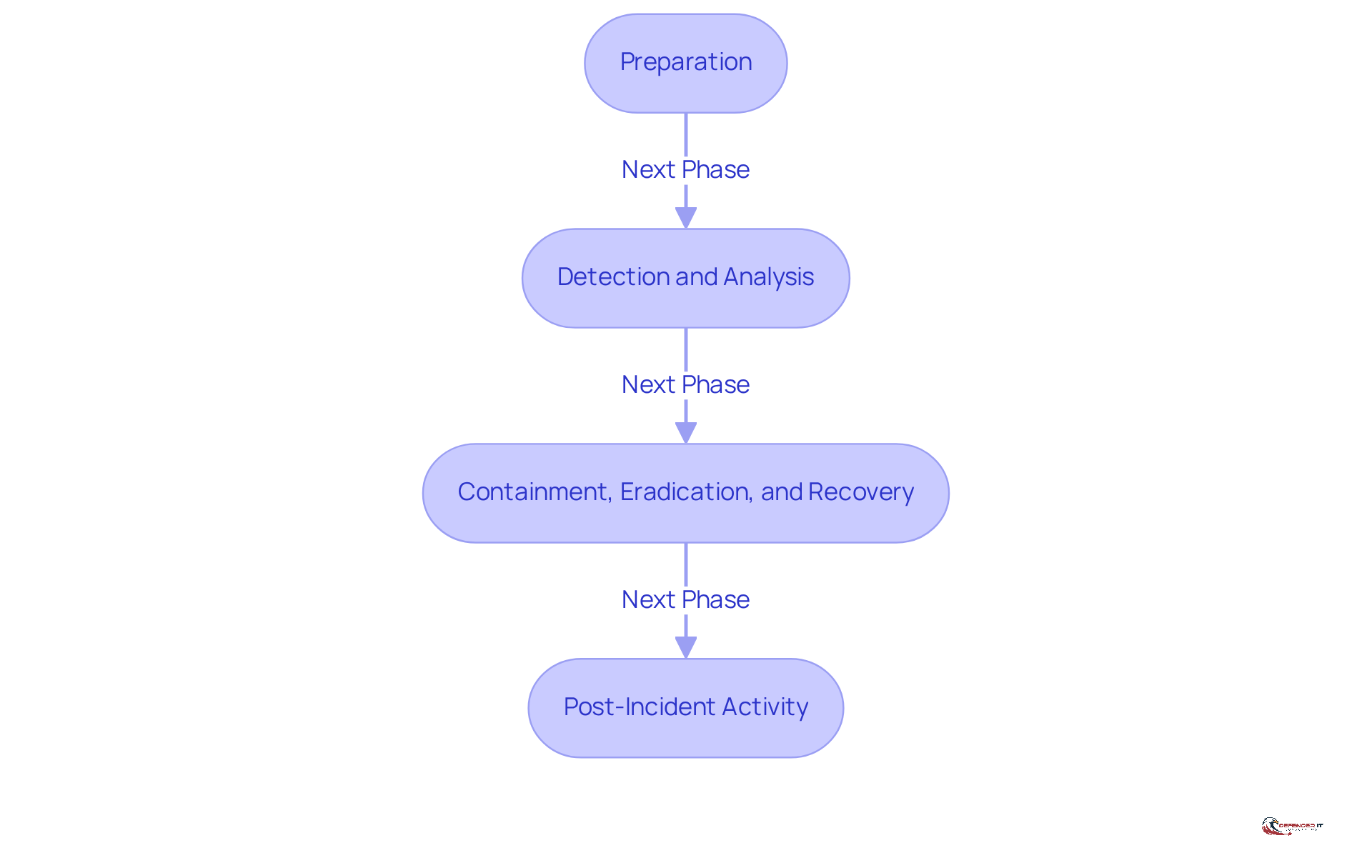
The NIST Incident Response Lifecycle consists of four interconnected phases that are essential for effective cybersecurity management:
-
Preparation: This foundational phase involves creating a robust plan for managing incidents, training staff on their roles, and establishing clear communication protocols. Organizations that prioritize preparation can significantly reduce their mean time to detect (MTTD) and mean time to respond (MTTR) during actual events. As Aaron Bandzes notes, "Creating and enhancing response playbooks assists in lowering the overall expenses of occurrences when they take place."
-
Detection and Analysis: Utilizing advanced monitoring tools is crucial for identifying anomalies and evaluating incidents. This phase emphasizes the examination of identified occurrences to assess their extent and potential impact, enabling organizations to respond promptly and effectively. The mean time to detect (MTTD) captures the average duration it takes for security teams to identify a security event, which is critical for facilitating quicker containment and remediation.
-
Containment, Eradication, and Recovery: Once an incident is detected, implementing containment strategies is vital to limit damage. This phase involves eradicating the threat and restoring systems to normal operations. Efficient containment can significantly decrease the average time to contain (MTTC), thereby minimizing the overall impact of the event. Bandzes emphasizes that "the sixth and final function area of the framework addresses what to do after an attack in order to minimize any long-term damage."
-
Post-Incident Activity: Following an incident, conducting a comprehensive evaluation is crucial for recognizing lessons learned and enhancing future incident management efforts. This phase emphasizes continuous improvement, which is essential for maintaining a strong security posture and ensuring compliance with industry standards. Organizations must consider their unique security risk profile to avoid misallocating resources on low-risk threats.
By systematically adhering to these stages, entities can develop a proactive incident management strategy using the NIST incident response framework that not only mitigates risks but also strengthens their overall cybersecurity framework. The significance of preparation cannot be overstated, as it lays the groundwork for effective detection, containment, and recovery, ultimately leading to improved resilience against cyber threats. Furthermore, organizations must navigate challenges such as cross-border data compliance to ensure comprehensive crisis management planning.
Integrate NIST Framework with Compliance and Security Practices
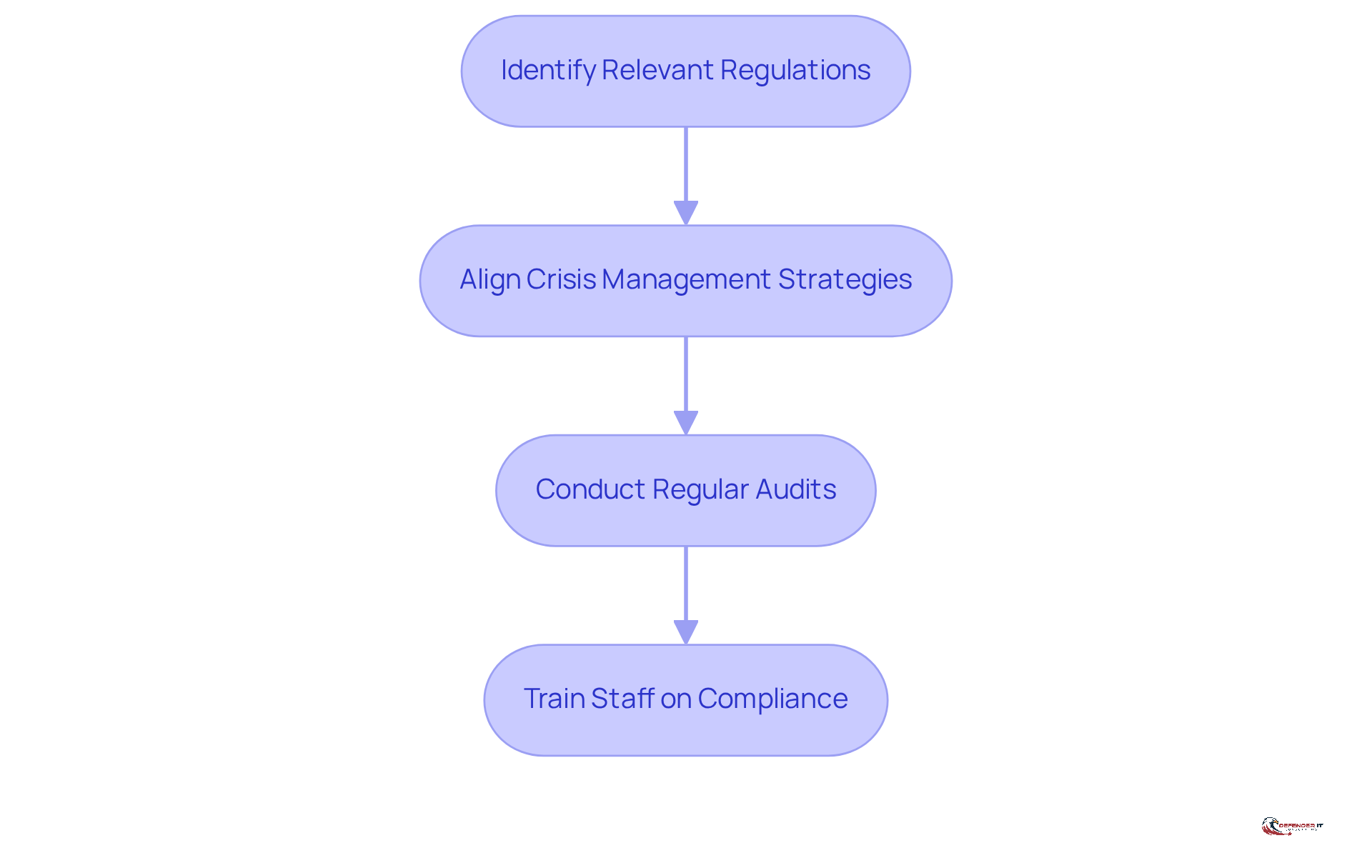
Combining the NIST Incident Response Framework with compliance and security practices requires aligning crisis management strategies with regulatory requirements. This integration enhances an organization’s ability to respond effectively while ensuring adherence to the NIST Incident Response Framework and other essential regulations. Key steps in this process include:
- Identify Relevant Regulations: It is crucial to understand the compliance landscape pertinent to your industry, including regulations such as GDPR, HIPAA, or PCI DSS.
- Align Crisis Management Strategies: Your crisis management strategy must incorporate compliance requirements, including reporting timelines and data protection measures.
- Conduct Regular Audits: Regular assessments and revisions of your crisis management plan are necessary to ensure continuous adherence to evolving regulations.
- Train Staff on Compliance: Providing education to personnel on event handling protocols and compliance requirements fosters a culture of security and accountability.
By implementing these practices, organizations can enhance their response capabilities while ensuring compliance with critical regulations.
Enhance Incident Response Through Continuous Improvement
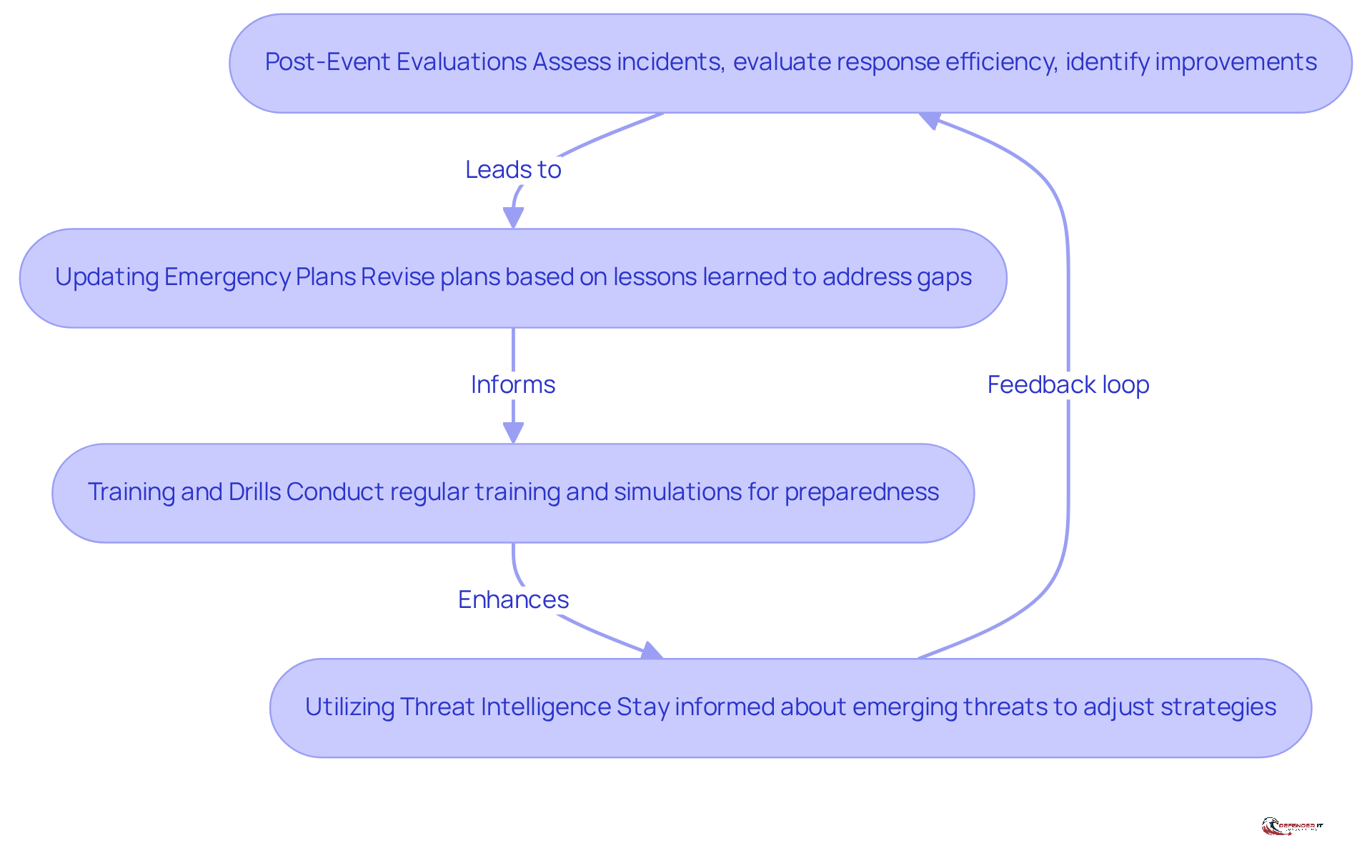
To enhance incident response capabilities, organizations should adopt a continuous improvement approach that includes the following key strategies:
- Performing Post-Event Evaluations: After each incident, it is crucial to assess what transpired, evaluate the efficiency of the response, and identify areas for improvement.
- Updating Emergency Plans: Organizations must revise their emergency plans based on lessons learned to address identified gaps and bolster overall readiness.
- Training and Drills: Regular training sessions and simulation exercises should be conducted to ensure staff are prepared for potential incidents and to reinforce best practices.
- Utilizing Threat Intelligence: Staying informed about emerging threats and vulnerabilities is essential for adjusting response strategies accordingly.
By committing to continuous improvement, organizations can establish a more resilient incident response framework based on the nist incident response framework that evolves in tandem with the changing threat landscape.
Conclusion
The NIST Incident Response Framework is essential for organizations aiming to enhance their cybersecurity posture and manage incidents effectively. By adopting this structured approach, companies can significantly improve their preparedness, detection, containment, and recovery processes, thereby fostering a more resilient security environment.
Key components of the framework include:
- Preparation
- Timely detection
- Effective containment
- Thorough post-incident evaluation
Each phase is interconnected, highlighting that a proactive stance not only mitigates the impact of cyber threats but also aligns with compliance requirements and established practices in security management. Alarmingly, statistics indicate that only 45% of organizations possess a robust incident management strategy, underscoring the urgent need for action.
Integrating the NIST Incident Response Framework into an organization’s security practices transcends mere compliance; it is a strategic imperative. Organizations should embrace continuous improvement methodologies to remain agile and responsive to the ever-evolving threat landscape. By prioritizing incident response readiness, companies can protect their assets and maintain stakeholder trust, ultimately reinforcing their commitment to cybersecurity excellence.