Introduction
Understanding the dynamics of a Security Operations Center (SOC) is crucial for security leaders navigating the complex cyber landscape today. The increasing frequency and sophistication of cyber threats make effective management of SOC costs not only a financial necessity but also a strategic imperative. Security leaders must find a way to balance the need for robust protection against the pressures of budget constraints, all while ensuring compliance with evolving regulations. This article explores the core components of SOC costs and presents actionable strategies to optimize expenses, enabling organizations to enhance their security posture without compromising quality.
Clarify SOC Fundamentals and Importance for Security Leaders
A Security Operations Center (SOC) serves as a centralized hub for addressing safety challenges at both organizational and technical levels. Its primary functions include monitoring, detecting, responding to, and mitigating incidents, which are essential for and ensuring compliance with regulatory standards.
Key aspects of a SOC include:
- : Continuous surveillance of networks and systems allows for the early detection of anomalies and potential threats, significantly reducing the risk of data breaches. Organizations with SOCs can manage cyber risks automatically within minutes of detection, thereby enhancing their overall defense posture.
- : A structured approach to handling incidents minimizes disruptions to business operations. SOC teams are equipped to implement plans that clearly define roles and responsibilities, ensuring efficient and effective reactions to risks. This structured methodology is vital for maintaining during incidents.
- : The SOC gathers and analyzes data regarding potential threats, guiding proactive protective measures. This intelligence is crucial for adapting to the evolving risk landscape, particularly in regulated industries where compliance with data privacy regulations is paramount. Furthermore, the SOC leverages insights gained from incidents to refine processes and prepare for emerging cybersecurity trends.
By understanding these fundamentals, leaders can align their strategies with the , ultimately enhancing their organization’s resilience against with industry standards.
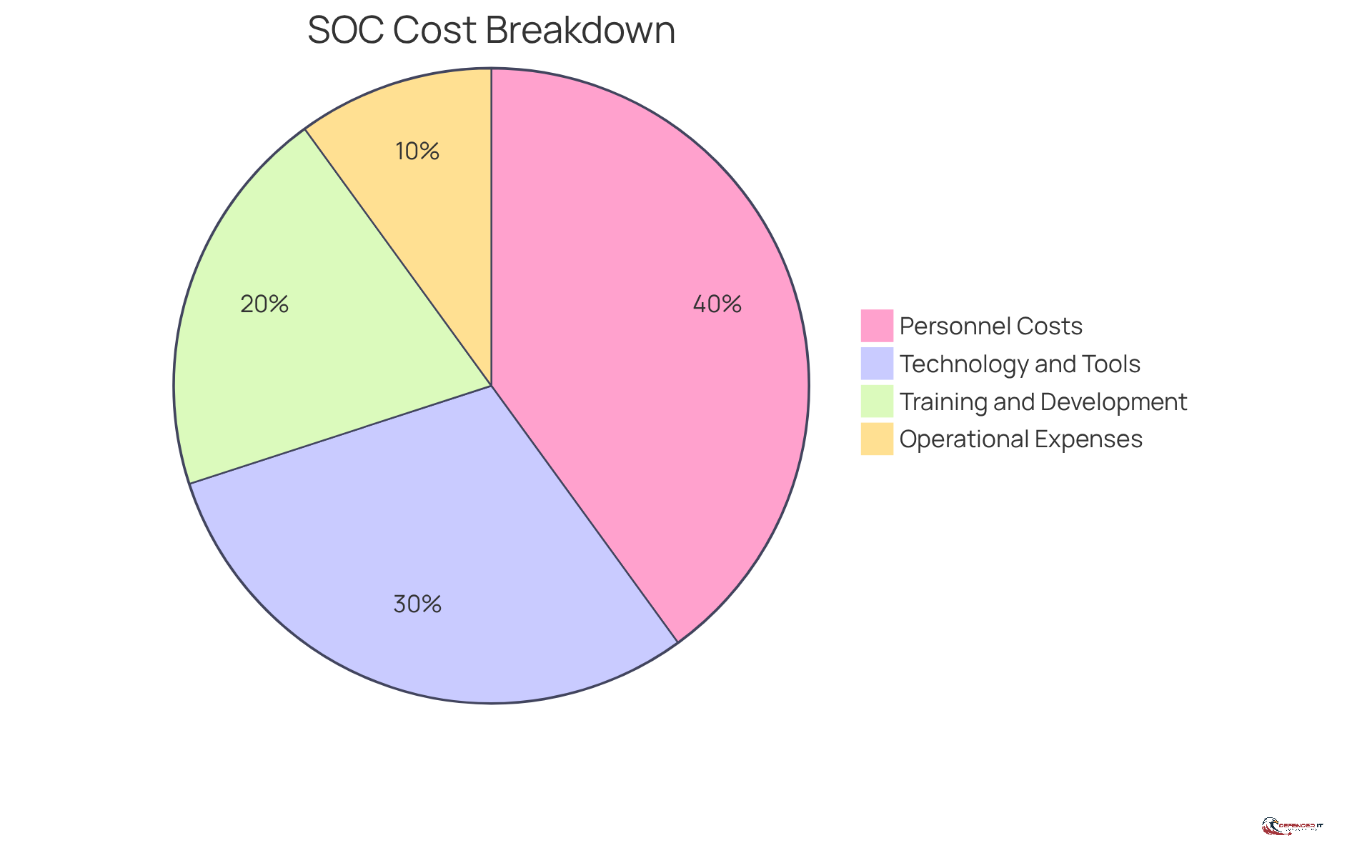
Analyze Key Components of SOC Cost Structure
Understanding the for a is crucial for effective budget management. The primary components of SOC costs typically encompass:
- Personnel Costs: This includes salaries for security analysts, incident responders, and management staff, which often represent the largest expense.
- Technology and Tools: Investments in security information and event management (SIEM) systems, risk intelligence platforms, and various other are essential.
- Training and Development: Continuous is necessary to keep pace with evolving threats and technologies.
- Operational Expenses: These are the costs associated with maintaining the SOC environment, including utilities, facilities, and administrative expenses.
By analyzing these components, leaders in security can identify potential savings opportunities and ensure that their operates efficiently.
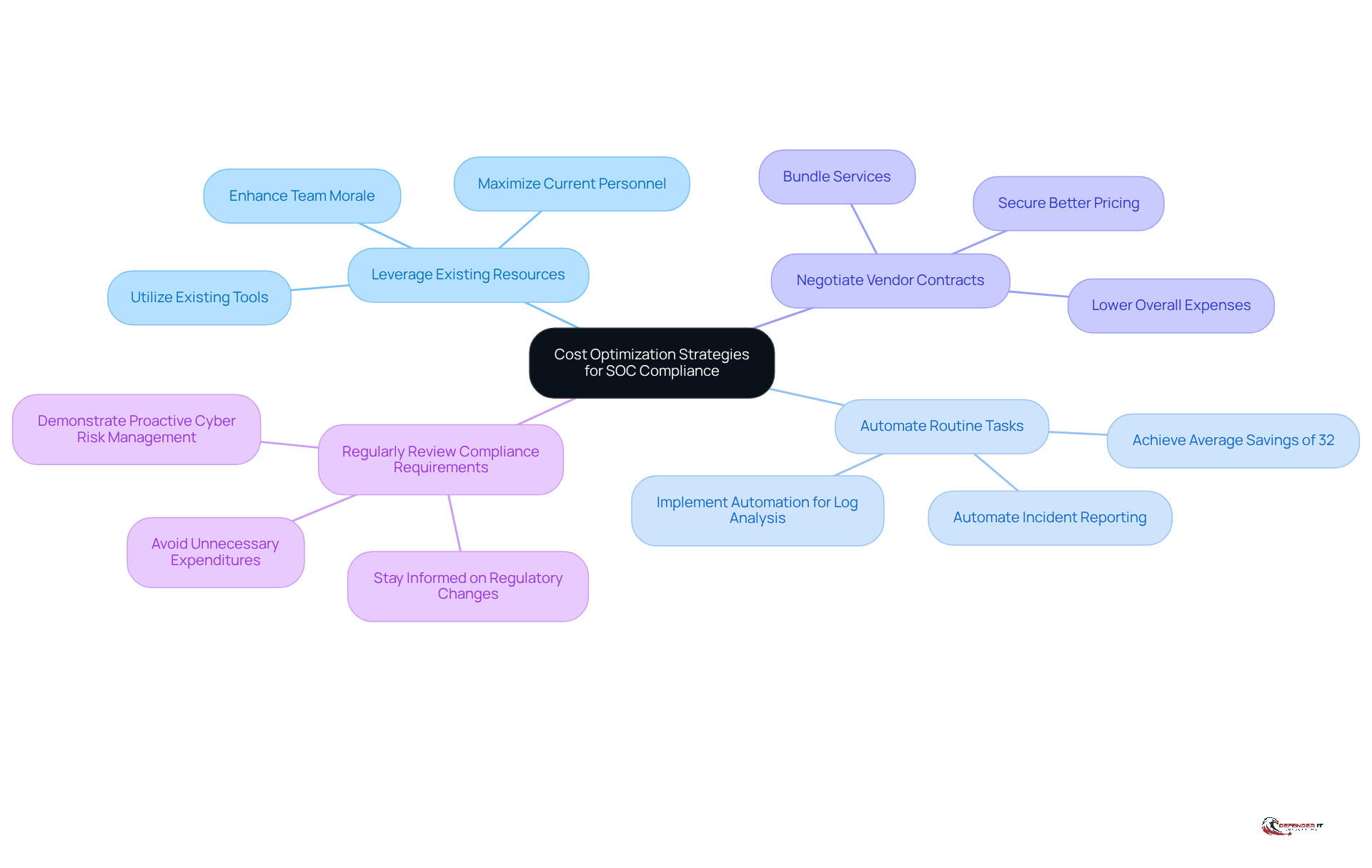
Implement Strategies for Cost Optimization in SOC Compliance
To optimize costs while ensuring , can adopt several effective strategies:
- : Maximize the potential of current personnel and tools before considering new investments. This approach not only conserves budget but also by utilizing their expertise.
- : Implement automation for repetitive processes such as log analysis and incident reporting. Organizations that have progressed past the initial testing phase of intelligent automation report an average savings of 32%. This frees up analysts to focus on more complex security challenges, ultimately improving operational efficiency.
- : Engage with vendors to secure better pricing or bundled services, which can significantly lower overall expenses without compromising service quality.
- : Stay informed about regulatory changes to avoid unnecessary expenditures on compliance measures that may no longer be applicable. Regulators expect businesses to demonstrate a proactive approach to managing , which helps maintain a lean compliance budget.
By applying these strategies, organizations can enhance their SOC’s compliance stance while incorporating a to efficiently manage expenses.
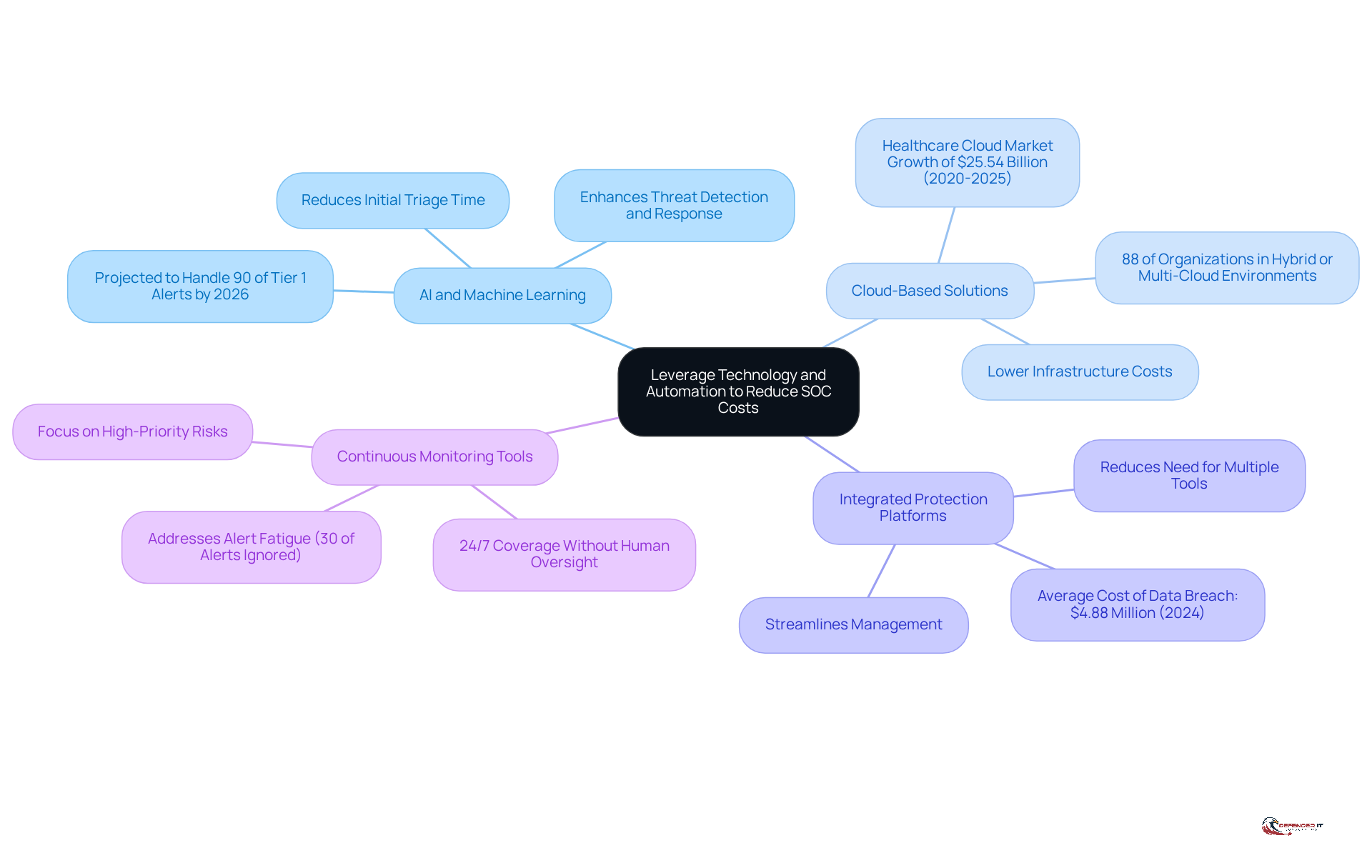
Leverage Technology and Automation to Reduce SOC Costs
Integrating technology and automation into Security Operations Center (SOC) operations can yield substantial savings and enhance efficiency. Key strategies include:
- : Utilizing AI-driven tools for threat detection and response facilitates the rapid analysis of extensive data sets, significantly surpassing the capabilities of human analysts. By 2026, AI automation is projected to autonomously manage over 90% of Tier 1 alerts, streamlining initial triage and categorization processes. This transition is vital, as 71% of business leaders reported a notable increase in attack frequency during 2025-26, highlighting the urgent need for improved .
- : Adopting cloud-based SOC services can substantially lower infrastructure costs while offering scalability. With 88% of organizations now functioning in , these solutions provide flexibility and alleviate the financial burden associated with traditional on-premises setups. The healthcare cloud market, anticipated to expand by $25.54 billion between 2020 and 2025, exemplifies the growing dependence on cloud solutions in regulated sectors.
- : Implementing integrated platforms that consolidate various protection functions reduces the necessity for multiple disparate tools, thereby minimizing associated costs. This approach not only streamlines management but also enhances the overall protective posture, which is critical given that the average cost of a data breach rose to $4.88 million in 2024.
- : Automated monitoring solutions provide 24/7 coverage without the constant need for human oversight, addressing the issue of alert fatigue that impacts up to 30% of incoming alerts. This allows SOC teams to focus on high-priority risks while maintaining operational efficiency.
By strategically leveraging these technologies, security leaders can significantly bolster their while ensuring a clear , positioning their organizations to better withstand the evolving landscape of cyber threats.
Conclusion
Understanding the complexities of a Security Operations Center (SOC) is crucial for security leaders who seek to enhance their organization’s cybersecurity posture. By comprehending the essential roles of monitoring, incident response, and threat intelligence, leaders can align their operational strategies with the capabilities of a SOC. This alignment not only strengthens defenses against cyber threats but also ensures compliance with regulatory standards, ultimately fostering organizational resilience.
The article examines the key components of SOC cost structures, emphasizing personnel expenses, technology investments, training, and operational costs. Organizations can optimize their SOC costs while maintaining robust security measures by implementing effective strategies such as:
- Leveraging existing resources
- Automating routine tasks
- Negotiating vendor contracts
- Regularly reviewing compliance requirements
Furthermore, integrating advanced technologies like AI, cloud solutions, and continuous monitoring tools streamlines operations and reduces expenses.
In a rapidly evolving cybersecurity landscape, the importance of a well-structured SOC cannot be overstated. Security leaders must prioritize cost optimization while ensuring compliance to establish a resilient defense framework. By adopting these insights and strategies, organizations can effectively manage SOC expenses and position themselves to navigate the complexities of cyber threats with confidence. Embracing these approaches is not merely a tactical decision; it is a strategic imperative for safeguarding digital assets in an increasingly interconnected world.
Frequently Asked Questions
What is the primary purpose of a Security Operations Center (SOC)?
The primary purpose of a SOC is to serve as a centralized hub for addressing safety challenges at both organizational and technical levels, focusing on monitoring, detecting, responding to, and mitigating incidents to protect digital assets and ensure compliance with regulatory standards.
Why is 24/7 monitoring important in a SOC?
24/7 monitoring is crucial as it allows for continuous surveillance of networks and systems, enabling early detection of anomalies and potential threats, which significantly reduces the risk of data breaches.
How does a SOC handle incident response?
A SOC handles incident response through a structured approach that minimizes disruptions to business operations. SOC teams implement incident response plans that clearly define roles and responsibilities for efficient and effective reactions to risks.
What role does threat intelligence play in a SOC?
Threat intelligence involves gathering and analyzing data regarding potential threats, guiding proactive protective measures. It is essential for adapting to the evolving risk landscape, particularly in regulated industries where compliance with data privacy regulations is critical.
How does understanding SOC fundamentals benefit security leaders?
By understanding SOC fundamentals, security leaders can align their strategies with the operational capabilities of a SOC, enhancing their organization’s resilience against cyber threats and improving compliance with industry standards.
List of Sources
- Clarify SOC Fundamentals and Importance for Security Leaders
- What Is a Security Operations Center (SOC)? | IBM (https://ibm.com/think/topics/security-operations-center)
- Global survey finds cyber incidents cost organizations $3.7M on average in the past year (https://redcanary.com/news/2025-security-operations-trends-report)
- The future of SOC: trends and innovations (https://authentic8.com/blog/future-soc-trends-and-innovations)
- 9 Key Benefits of Security Operations Center (SOC) in 2025 (https://radiantsecurity.ai/learn/soc-benefits)
- Implement Strategies for Cost Optimization in SOC Compliance
- Cybersecurity Quotes That Define the Future of Digital Protection (https://medium.com/@cyberpromagazine/cybersecurity-quotes-that-define-the-future-of-digital-protection-64897c07bfc6)
- The Top 20 Expert Quotes On Cyber Risk and Security (https://surtech.co.za/20-expert-quotes-on-cyber-risk-and-security)
- 29 Cybersecurity Quotes to Protect Your Digital Life (https://acecloudhosting.com/blog/cybersecurity-quotes)
- The Impact of Intelligent Automation on Cost Savings (https://integranxt.com/blog/impact-of-intelligent-automation-on-cost-savings)
- How to Optimize Cybersecurity Budget in 2026? (https://picussecurity.com/resource/blog/optimize-cybersecurity-budget)
- Leverage Technology and Automation to Reduce SOC Costs
- How Security Operations Will Fundamentally Change in 2026 (https://thefastmode.com/expert-opinion/47151-how-security-operations-will-fundamentally-change-in-2026)
- 49 Cloud Computing Statistics You Need to Know in 2026 (https://finout.io/blog/49-cloud-computing-statistics-in-2026)
- 50+ Cloud Security Statistics in 2026 (https://sentinelone.com/cybersecurity-101/cloud-security/cloud-security-statistics)
- Why 2026 will be the year of governed cybersecurity AI (https://thenextweb.com/news/why-2026-will-be-the-year-of-governed-cybersecurity-ai)
](https://radiantsecurity.ai/learn/soc-benefits)](https://radiantsecurity.ai/learn/soc-benefits)](https://radiantsecurity.ai/learn/soc-benefits)](https://radiantsecurity.ai/learn/soc-benefits)](https://radiantsecurity.ai/learn/soc-benefits)](https://radiantsecurity.ai/learn/soc-benefits)](https://radiantsecurity.ai/learn/soc-benefits), and [[[[[[[[[threat intelligence](https://authentic8.com/blog/future-soc-trends-and-innovations)](https://authentic8.com/blog/future-soc-trends-and-innovations)](https://authentic8.com/blog/future-soc-trends-and-innovations)](https://authentic8.com/blog/future-soc-trends-and-innovations)](https://authentic8.com/blog/future-soc-trends-and-innovations)](https://authentic8.com/blog/future-soc-trends-and-innovations)](https://authentic8.com/blog/future-soc-trends-and-innovations)](https://authentic8.com/blog/future-soc-trends-and-innovations)](https://authentic8.com/blog/future-soc-trends-and-innovations) contribute to security leadership and organizational resilience.](https://images.tely.ai/telyai/mvcqdwng-start-at-the-center-with-the-soc-fundamentals-then-explore-each-branch-to-see-how-monitoring-incident-response-and-threat-intelligence-contribute-to-security-leadership-and-organizational-resilience.webp)