Introduction
In today’s digital landscape, the threat of cyberattacks is more pronounced than ever, necessitating that organizations prioritize their cybersecurity measures. Mastering cybersecurity risk assessment tools is crucial for identifying vulnerabilities and strengthening defenses against potential breaches. This guide explores the essential components of these tools, providing insights into their selection and evaluation. It raises a vital question: how can organizations ensure they choose the right tools to effectively mitigate risks and enhance their security posture?
Understand Cybersecurity Risk Assessment Tools
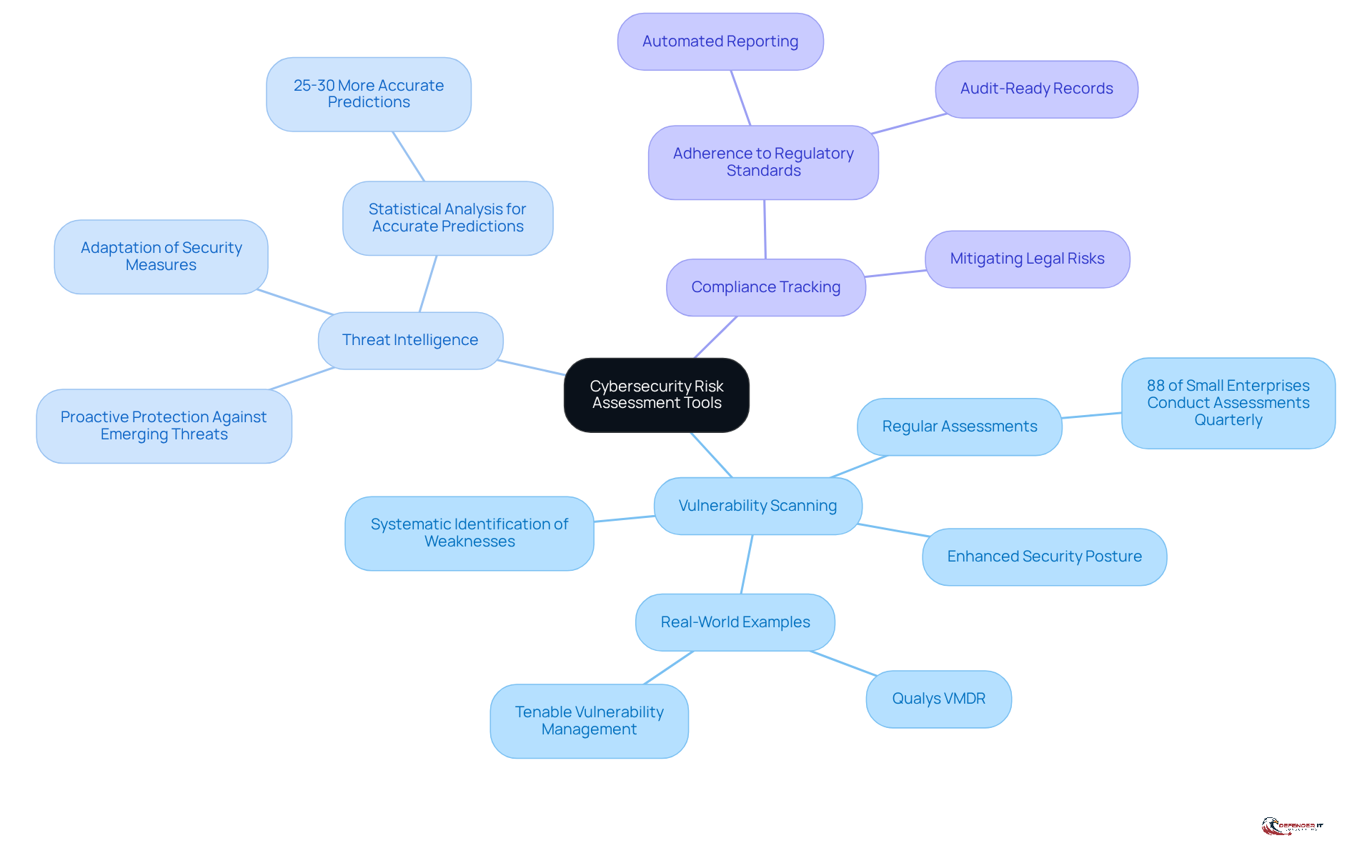
The cybersecurity risk assessment tool is crucial for identifying vulnerabilities and threats within a company’s IT infrastructure. These tools range from automated questionnaires to comprehensive frameworks like the NIST Cybersecurity Framework. Understanding these resources involves recognizing their key functions:
- Vulnerability Scanning: This process systematically identifies weaknesses in systems and applications, enabling organizations to prioritize remediation efforts. Regular vulnerability scanning is essential for maintaining a robust security posture and complying with industry regulations. Notably, 88% of small enterprises conduct assessments at least quarterly to evaluate their cybersecurity threats.
- Threat Intelligence: By gathering information on potential threats derived from current trends, organizations can proactively protect against emerging dangers. This intelligence is vital for adapting security measures to counteract evolving cyber threats.
- Compliance Tracking: These resources help ensure adherence to regulatory standards, such as GDPR and HIPAA, by automating reporting and maintaining audit-ready records.
By 2026, a significant number of organizations are expected to employ a cybersecurity risk assessment tool, reflecting a growing awareness of its importance in safeguarding digital assets. For instance, companies utilizing vulnerability scanning tools have reported enhanced security postures and improved incident response times. Real-world examples include platforms like Qualys VMDR and Tenable Vulnerability Management, which offer continuous scanning and threat prioritization, enabling organizations to address critical vulnerabilities swiftly. Furthermore, organizations employing statistical analysis for threat assessment achieve 25-30% more accurate predictions, underscoring the effectiveness of these tools.
As Richard Seiersen notes, effective vulnerability scanning not only identifies threats but also fosters improved decision-making and resource allocation in cybersecurity strategies. He emphasizes that statistical analysis provides more precise predictions of potential issues with specific probability percentages, rather than vague qualitative ratings. By familiarizing yourself with these resources, you can gain a deeper understanding of their role in protecting your organization against cyber threats.
Identify Key Selection Criteria for Tools
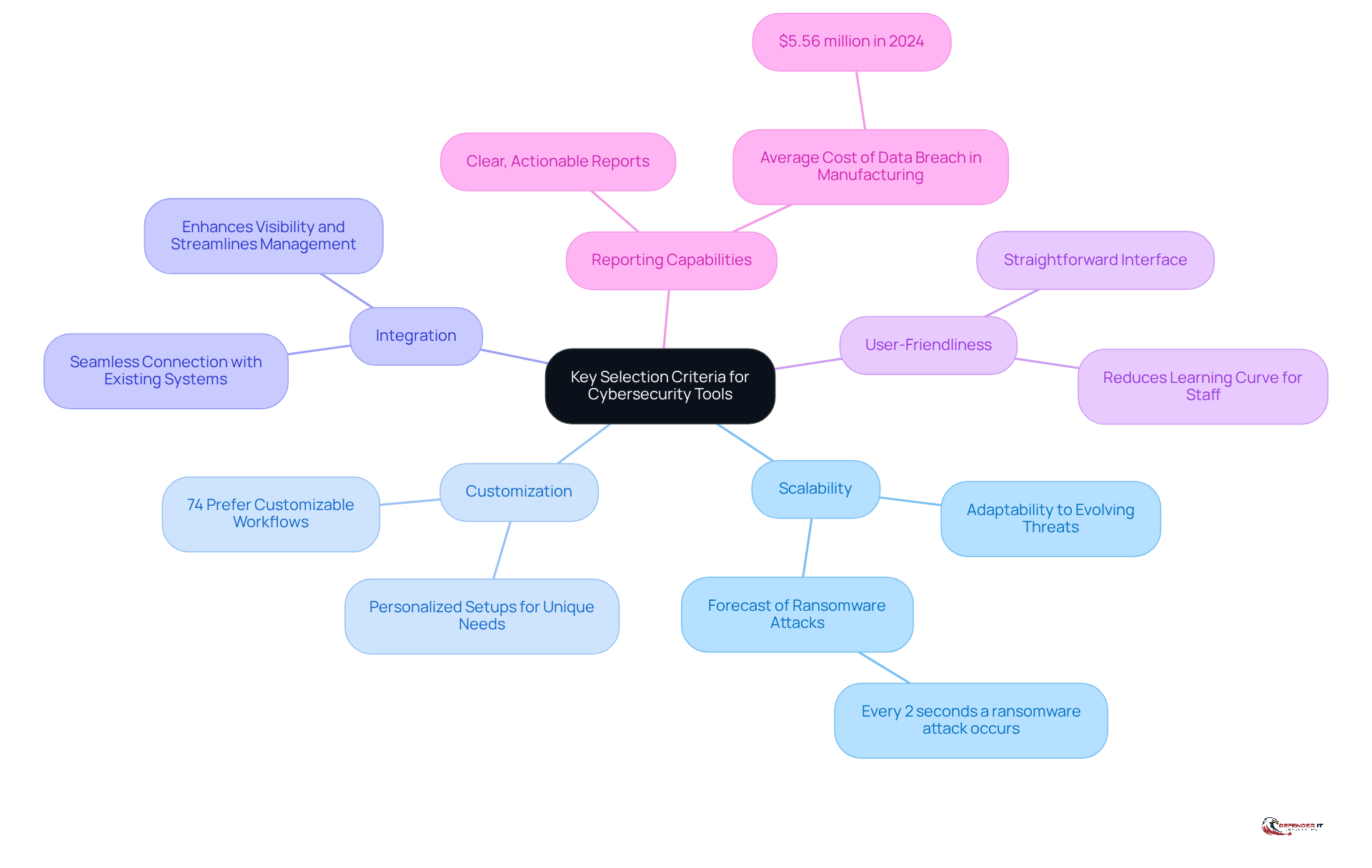
When selecting cybersecurity risk assessment tools, organizations should prioritize the following key criteria:
-
Scalability: It is essential to choose tools that can adapt and grow alongside your organization. As cyber threats evolve, scalable solutions ensure that your defenses remain robust, accommodating increased data and user demands. Cybersecurity Ventures forecasts that a ransomware assault will affect a business or individual every 2 seconds, underscoring the necessity for adaptable solutions to match evolving threats.
-
Customization: Opt for resources that enable personalized setups to address specific organizational requirements. Customizable features enhance the relevance of the resource, allowing it to effectively address unique vulnerabilities. Statistics indicate that 74% of entities prefer solutions that provide customizable workflows for managing uncertainties, facilitating smoother management processes.
-
Integration: The chosen solution should seamlessly connect with existing systems to enhance visibility and streamline management efforts. Effective integration minimizes disruption and maximizes the utility of current security measures.
-
User-Friendliness: A straightforward interface is crucial for usability. Tools that are easy to navigate reduce the learning curve for staff and encourage consistent usage throughout the organization.
-
Reporting Capabilities: Effective security tools offer clear, actionable reports that assist entities in comprehending their risk landscape. Automated reporting features can significantly enhance compliance efforts, ensuring entities remain audit-ready. The typical expense of a data breach in the manufacturing sector reached $5.56 million in 2024, highlighting the financial consequences of insufficient protective measures.
By utilizing a cybersecurity risk assessment tool to assess resources against these standards, entities can select options that not only address their urgent security requirements but also promote enduring strength against emerging dangers.
Evaluate and Choose the Right Tool
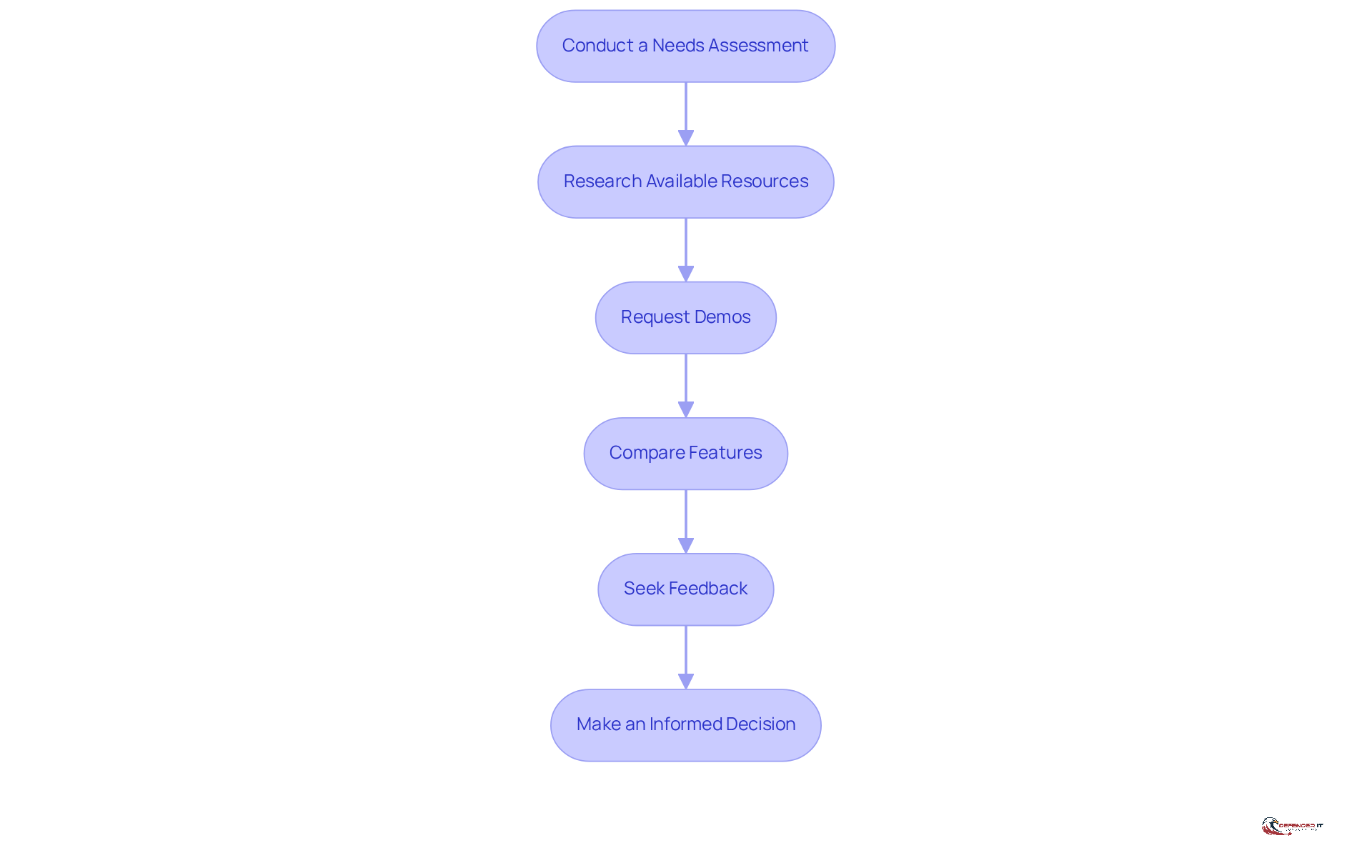
To effectively evaluate and select the right cybersecurity risk assessment tool, organizations should follow these structured steps:
- Conduct a Needs Assessment: Begin by identifying your entity’s specific cybersecurity requirements. This involves understanding the unique threats faced and the regulatory compliance needs relevant to your industry. For instance, entities in the manufacturing sector may need to consider compliance with standards such as ISO 27001 or NIST.
- Research Available Resources: Compile a comprehensive list of potential resources that align with your identified needs. Consider factors such as scalability, integration capabilities, and vendor support. According to industry data, organizations typically use a cybersecurity risk assessment tool to assess approximately five to seven cybersecurity solutions before making a decision.
- Request Demos: Engage with vendors to request demonstrations of their products. This enables you to evaluate usability, features, and how well the resource integrates into your existing IT infrastructure. Feedback from cybersecurity professionals suggests that hands-on experience is crucial in this phase.
- Compare Features: Analyze how each resource meets your selection criteria. Look for features that enhance threat visibility, automate compliance, and provide real-time risk insights. For instance, resources that provide automated reporting can greatly decrease the time dedicated to compliance documentation.
- Seek Feedback: Consult with stakeholders, including IT teams and security experts, to gather their insights and experiences with the solutions being considered. Their input can be invaluable in the evaluation process, as they may highlight practical considerations that are not immediately apparent.
- Make an Informed Decision: Choose the resource that best aligns with your organizational goals and budget. Keep in mind that the typical entity assesses several security tools-usually about five to seven-before reaching a final choice. This thorough evaluation process can be enhanced by using a cybersecurity risk assessment tool, leading to better long-term security outcomes.
By following this structured method, entities can guarantee they choose a tool that not only addresses their urgent security requirements but also improves their overall defense stance in a progressively intricate threat environment.
Explore Additional Resources and Tools
To enhance your understanding and application of cybersecurity risk assessment, consider the following resources:
-
NIST Cybersecurity Framework: This framework provides a structured approach for managing cybersecurity risks, aligning with industry standards and regulatory requirements. Its adoption has been shown to improve security postures and compliance, particularly in sectors such as healthcare and finance. For example, organizations that implement the NIST CSF have reported improved incident response capabilities and cost savings by reducing the financial impact of cyber incidents.
-
CISA Resources: The Cybersecurity and Infrastructure Security Agency (CISA) offers a variety of tools and guidance designed to enhance protective practices. Recent updates in 2026 have introduced new resources aimed at addressing emerging threats, making them essential for organizations striving to stay ahead of cyber challenges. Notably, the average cost of a data breach globally is increasing to approximately $4.88 million, highlighting the urgency of utilizing CISA resources.
-
Online Courses: Platforms such as Coursera and Udemy provide a range of courses focused on security threat evaluation. These courses equip teams with the necessary skills to effectively implement management strategies for potential challenges.
-
Industry Reports: Regularly reviewing reports from security companies can keep organizations informed about the latest trends, tools, and best practices in the field. For instance, groups utilizing CISA’s resources have reported improved team coordination and enhanced management capabilities.
Incorporating these resources into your cybersecurity strategy can significantly enhance the effectiveness of a cybersecurity risk assessment tool and better prepare organizations for potential digital threats. Furthermore, insights from cybersecurity experts underscore the importance of these frameworks in fostering a proactive security culture.
Conclusion
Mastering cybersecurity risk assessment tools is crucial for organizations seeking to protect their digital assets in an increasingly complex threat landscape. Understanding the available tools and their functionalities enables businesses to identify vulnerabilities, prioritize threats, and ensure compliance with regulatory standards. This proactive approach not only enhances security but also supports informed decision-making and effective resource allocation.
Key components of cybersecurity risk assessment tools include:
- Vulnerability scanning
- Threat intelligence
- Compliance tracking
Selecting tools based on criteria such as:
- Scalability
- Customization
- Integration
- User-friendliness
- Reporting capabilities
is essential. By following a structured evaluation process that encompasses needs assessment, research, and stakeholder feedback, organizations can make informed decisions that bolster their cybersecurity posture.
The importance of utilizing robust cybersecurity risk assessment tools cannot be overstated. As cyber threats continue to evolve, organizations must remain vigilant and proactive in their defense strategies. Embracing these tools, alongside additional resources like the NIST Cybersecurity Framework and CISA guidelines, empowers entities to mitigate risks effectively and cultivate a culture of security awareness. Implementing these practices now will yield long-term benefits and resilience against future cyber challenges.
Frequently Asked Questions
What is the purpose of cybersecurity risk assessment tools?
Cybersecurity risk assessment tools are essential for identifying vulnerabilities and threats within a company’s IT infrastructure, helping organizations prioritize remediation efforts and enhance their security posture.
What are some key functions of cybersecurity risk assessment tools?
Key functions include vulnerability scanning to identify weaknesses, threat intelligence to gather information on potential threats, and compliance tracking to ensure adherence to regulatory standards.
How does vulnerability scanning contribute to cybersecurity?
Vulnerability scanning systematically identifies weaknesses in systems and applications, enabling organizations to address critical vulnerabilities swiftly and maintain compliance with industry regulations.
What is the significance of threat intelligence in cybersecurity?
Threat intelligence helps organizations proactively protect against emerging dangers by providing information on current trends and potential threats, allowing for the adaptation of security measures.
How do compliance tracking features benefit organizations?
Compliance tracking helps organizations adhere to regulatory standards such as GDPR and HIPAA by automating reporting and maintaining audit-ready records.
What is the expected trend regarding the use of cybersecurity risk assessment tools by 2026?
A significant number of organizations are expected to employ cybersecurity risk assessment tools, reflecting a growing awareness of their importance in safeguarding digital assets.
Can you provide examples of cybersecurity risk assessment tools?
Examples include Qualys VMDR and Tenable Vulnerability Management, which offer continuous scanning and threat prioritization to help organizations improve their security postures.
How does statistical analysis enhance threat assessment accuracy?
Organizations employing statistical analysis for threat assessment achieve 25-30% more accurate predictions, leading to better-informed decision-making in cybersecurity strategies.
What insights does Richard Seiersen provide regarding vulnerability scanning?
Richard Seiersen notes that effective vulnerability scanning not only identifies threats but also improves decision-making and resource allocation in cybersecurity strategies, emphasizing the value of precise predictions over vague qualitative ratings.