Introduction
The Cybersecurity Maturity Model Certification (CMMC) is a vital safeguard in defense contracting, ensuring the protection of sensitive information against evolving cyber threats. As organizations seek to secure government contracts, grasping the complexities of CMMC compliance is essential. This understanding not only provides regulatory assurance but also offers a competitive advantage in the marketplace. However, with impending enforcement deadlines and the intricate nature of compliance requirements, businesses must effectively navigate the CMMC landscape to overcome the challenges ahead.
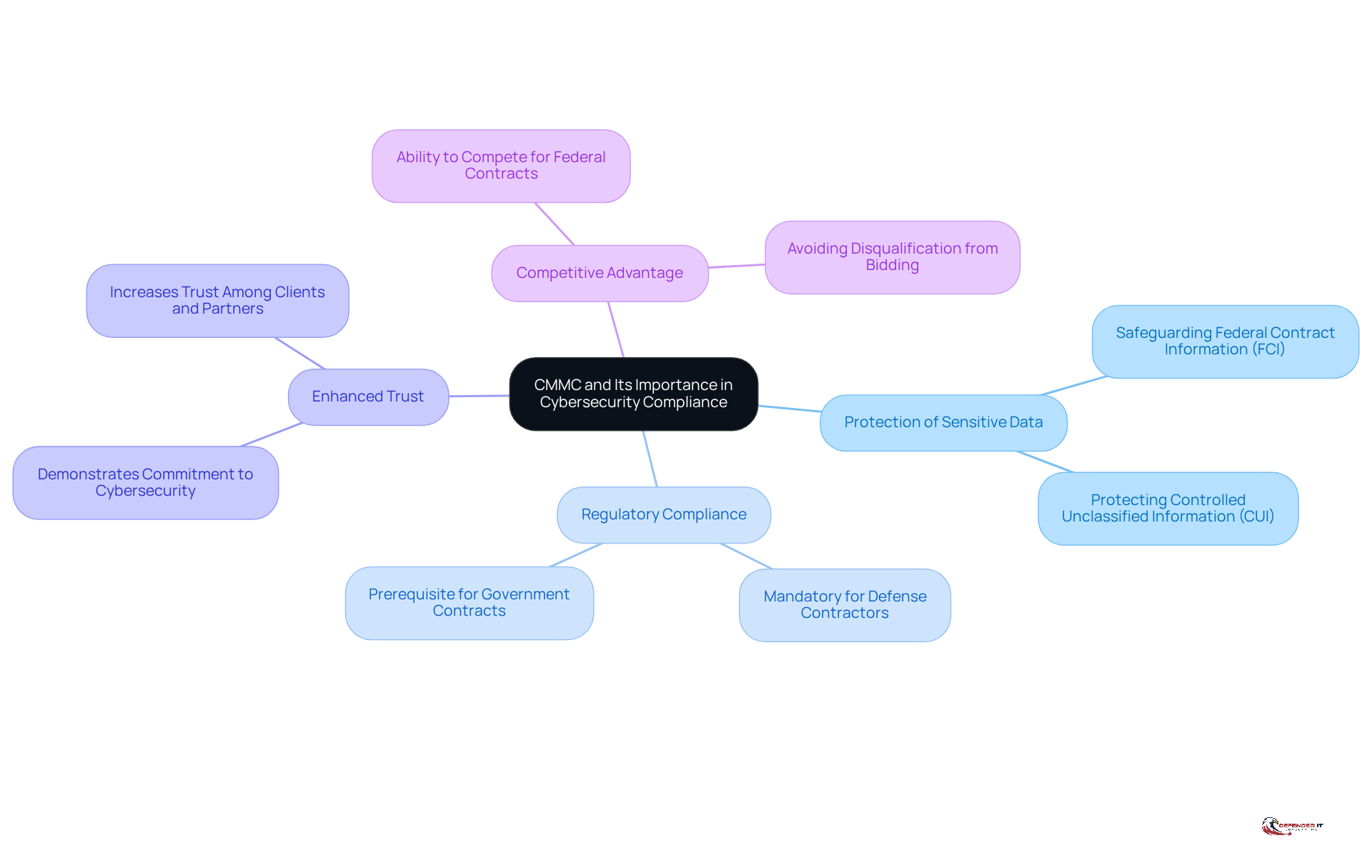
Define CMMC and Its Importance in Cybersecurity Compliance
The Cybersecurity Maturity Model Certification (CMMC) is a framework established by the U.S. Department of Defense (DoD) to ensure that contractors adequately protect sensitive information. This certification is crucial for several reasons:
- Protection of Sensitive Data: CMMC is designed to safeguard Federal Contract Information (FCI) and Controlled Unclassified Information (CUI) from cyber threats.
- Regulatory Compliance: Compliance with the CMMC compliance requirements is mandatory for defense contractors, serving as a prerequisite for securing government contracts.
- Enhanced Trust: Achieving this certification demonstrates a commitment to cybersecurity, thereby increasing trust among clients and partners.
- Competitive Advantage: Organizations that comply with these standards can compete more effectively for federal contracts, as non-compliance may lead to disqualification from bidding.
Understanding the cybersecurity maturity model framework is the first step in navigating the complexities of cybersecurity regulations, particularly for companies operating in regulated sectors.
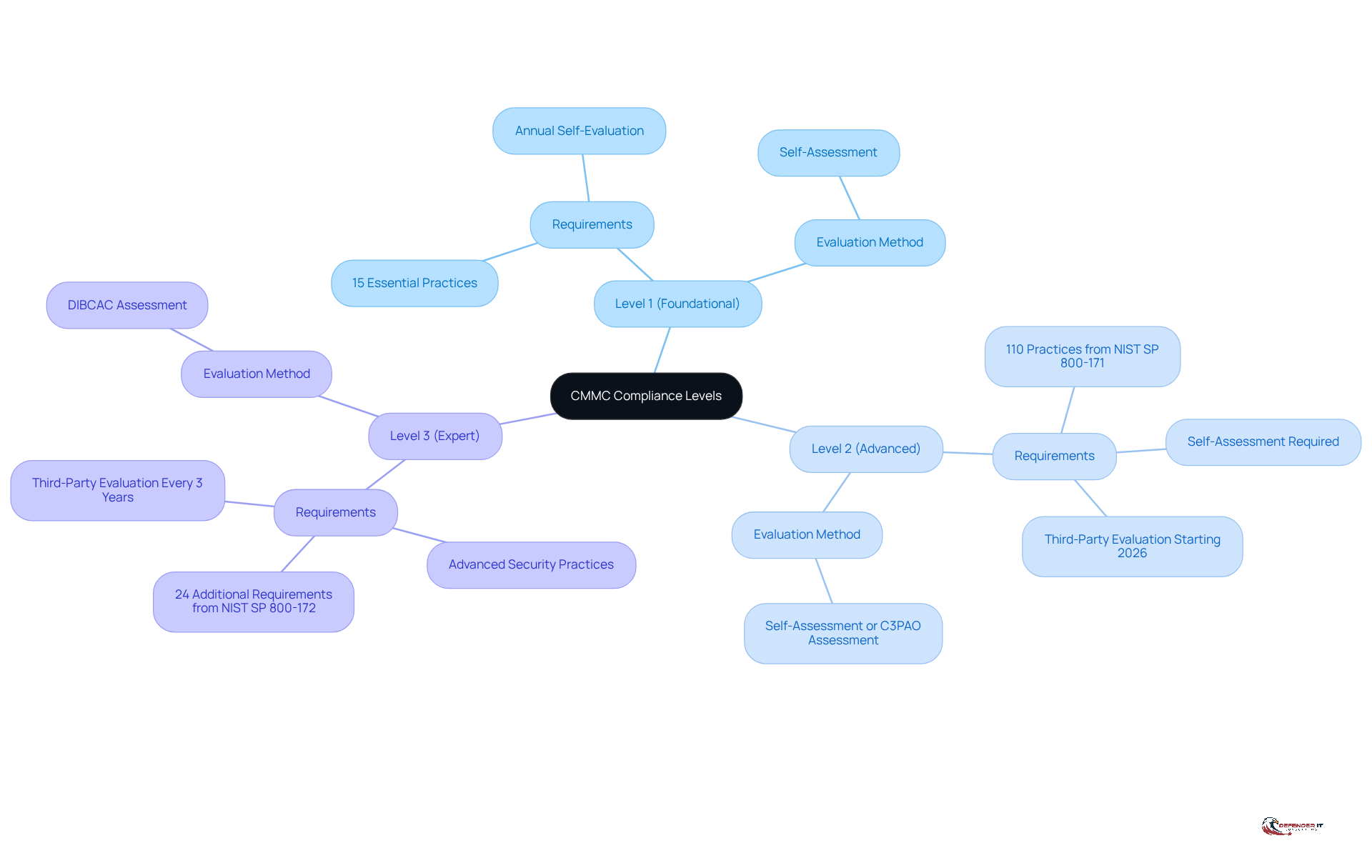
Explore CMMC Compliance Levels and Their Requirements
CMMC consists of three distinct compliance levels, each designed with specific requirements tailored to the sensitivity of the data handled:
-
Level 1 (Foundational): This level emphasizes basic safeguarding practices for Federal Contract Information (FCI). Organizations must implement 17 essential practices to ensure the protection of sensitive information, accompanied by an annual self-evaluation to confirm adherence.
-
Level 2 (Advanced): Targeted at organizations managing Controlled Unclassified Information (CUI), Level 2 requires compliance with 110 practices outlined in NIST SP 800-171. This level mandates a self-assessment to evaluate CMMC compliance requirements and is crucial for those aiming to handle more sensitive data. Starting November 10, 2026, external evaluations will become mandatory for Level 2 entities.
-
Level 3 (Expert): Designed for entities handling the most sensitive data, Level 3 necessitates advanced security practices and mandates third-party evaluations every three years. This level incorporates 24 additional requirements from NIST SP 800-172, ensuring robust protection against sophisticated cyber threats.
As of 2026, entities must remain vigilant regarding the evolving CMMC compliance requirements for each level, particularly the emphasis on self-assessments for Levels 1 and 2, which are vital for maintaining eligibility for Department of Defense contracts. Currently, only 1% of Defense Industrial Base contractors are fully prepared for audits, underscoring the importance of proactive compliance strategies.
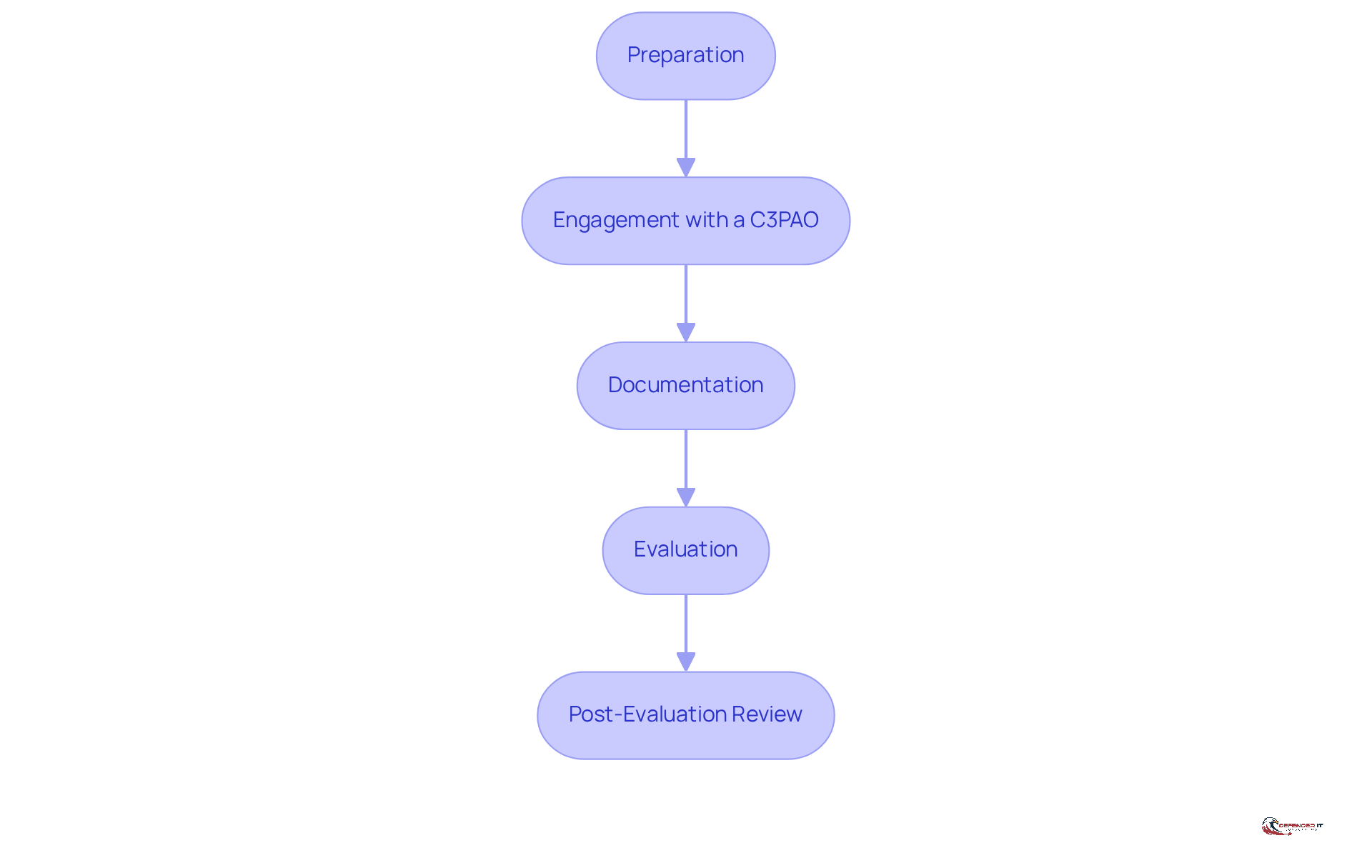
Navigate the CMMC Assessment Process: Steps and Expectations
The CMMC assessment process comprises several critical steps that organizations must adhere to for compliance:
-
Preparation: Conducting a self-assessment is essential for evaluating the current cybersecurity posture against CMMC compliance requirements. This initial step helps identify gaps and areas needing improvement. Industry leaders emphasize that meticulous preparation can significantly reduce the time required for CMMC evaluations, which can average 40 hours a week for 18 months for smaller organizations aiming for Level 2 certification.
-
Engagement with a C3PAO: Selecting a Certified Third-Party Assessment Organization (C3PAO) is crucial for formal assessments. Organizations should choose a C3PAO that aligns with their specific regulatory requirements and comprehends the nuances of their industry. Early interaction with C3PAOs can streamline efforts and ensure that organizations are well-prepared to meet regulatory standards.
-
Documentation: Organizations must prepare comprehensive documentation, including policies, procedures, and evidence demonstrating adherence to CMMC practices. This documentation serves as the foundation for the evaluation of CMMC compliance requirements.
-
Evaluation: The C3PAO will conduct the evaluation, which includes interviews, document reviews, and technical assessments to ensure all aspects of conformity are thoroughly examined.
-
Post-Evaluation Review: Following the evaluation, entities will receive feedback and recommendations for improvement. This step is vital for addressing any deficiencies and enhancing the overall cybersecurity posture. As Jeff Barney, Ecommerce & IT Manager at Scientific Sales, noted, adapting to changes is essential for maintaining compliance even after the initial evaluation.
By adhering to these steps, companies can effectively manage the assessment process and position themselves for success.
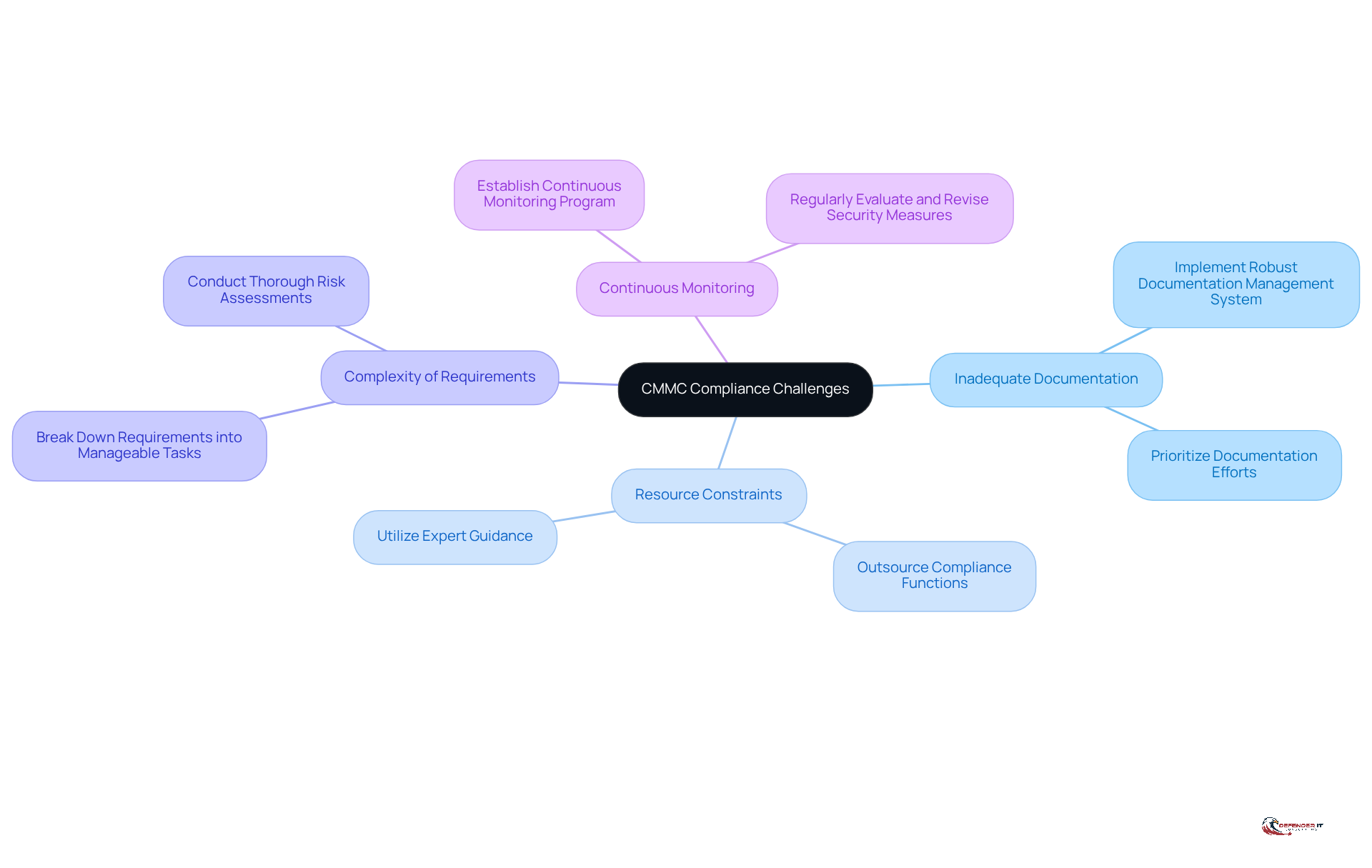
Identify Challenges in CMMC Compliance and Strategies to Overcome Them
Organizations encounter several significant challenges in achieving CMMC compliance:
-
Inadequate Documentation: Many organizations find it difficult to maintain comprehensive documentation of their cybersecurity practices. A robust documentation management system is essential for effectively tracking policies and procedures.
-
Resource Constraints: Limited personnel and budget can significantly hinder adherence efforts. Outsourcing certain compliance functions to specialized firms, such as Defenderit Consulting, can alleviate these constraints and provide expert guidance. Notably, entities utilizing partners achieve results comparable to those operating independently when both uphold measurement systems.
-
The intricate nature of the CMMC compliance requirements can make the complexity of requirements overwhelming. To manage this complexity, organizations should break down the requirements into manageable tasks and prioritize them based on a thorough risk assessment. As emphasized by Kiteworks, ‘CMMC 2.0 success relies more on governance maturity than technical sophistication or organizational resources.’
-
Continuous Monitoring: Compliance is not a one-time effort but an ongoing process. Establishing a continuous monitoring program is vital for consistently evaluating and revising security measures to ensure ongoing adherence.
With CMMC enforcement beginning to phase in on November 10, 2025, recognizing these challenges and implementing effective strategies is essential for organizations to enhance their compliance efforts and significantly reduce the risk of non-compliance.
Conclusion
Achieving compliance with the Cybersecurity Maturity Model Certification (CMMC) is essential for organizations engaged in defense contracting. This framework not only protects sensitive information but also ensures adherence to mandatory regulatory standards, thereby enhancing trust and competitiveness within the industry. A thorough understanding of CMMC’s intricacies, including its compliance levels and assessment processes, is crucial for any organization seeking to secure government contracts and defend against cyber threats.
The article outlines the various levels of CMMC compliance, each with specific requirements that increase in complexity, reflecting the sensitivity of the data involved. It details the assessment process, highlighting the significance of preparation, documentation, and collaboration with Certified Third-Party Assessment Organizations (C3PAOs). Additionally, it identifies common challenges organizations encounter, such as insufficient documentation and resource limitations, while providing strategic solutions to effectively navigate these obstacles.
In a landscape where CMMC compliance is becoming a competitive necessity, organizations must prioritize their cybersecurity posture and proactively address compliance requirements. The stakes are high; non-compliance could result in disqualification from lucrative government contracts. By implementing the steps and strategies outlined in this tutorial, companies can achieve CMMC compliance and strengthen their defenses against evolving cyber threats, ultimately securing their position within the defense industrial base.