Introduction
The evolving landscape of cybersecurity regulations poses a significant challenge for manufacturers involved in defense contracting. The introduction of CMMC 2.0 by the Department of Defense has streamlined compliance into a more manageable framework; however, the stakes have never been higher. By effectively navigating the intricacies of this updated model, manufacturing leaders can safeguard sensitive information while enhancing their competitive edge in a crowded marketplace.
Yet, a critical question persists: how can organizations prepare for compliance effectively and avoid the pitfalls that could jeopardize their contracts and reputation?
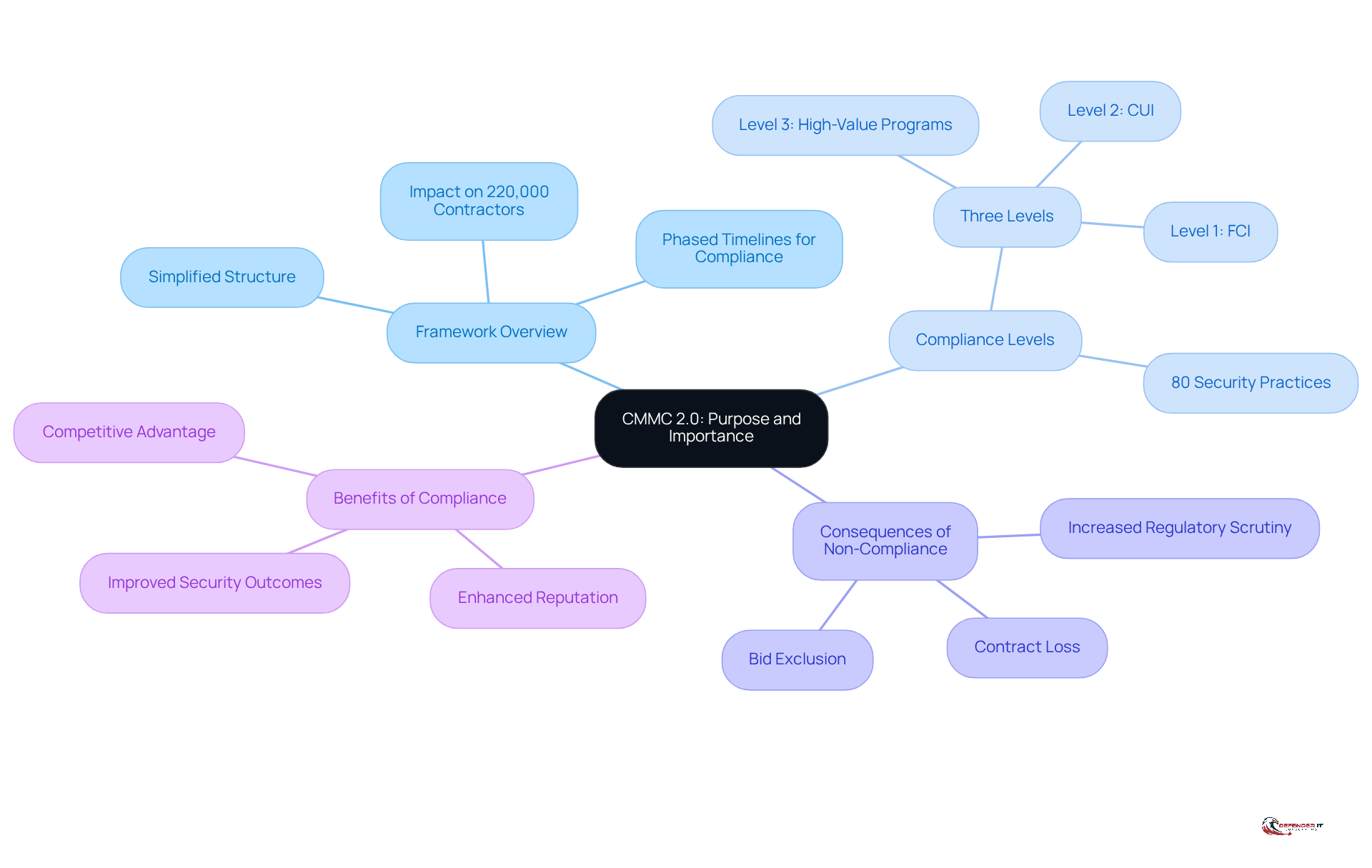
Clarify CMMC 2.0: Purpose and Importance
The CMMC2 is a crucial framework established by the Department of Defense (DoD) to ensure that defense contractors and subcontractors implement robust cybersecurity measures to safeguard sensitive information. This updated model simplifies the original five-level structure into three distinct levels, streamlining the certification process and introducing phased timelines for compliance, which will affect over 220,000 contractors and subcontractors. By January 14, 2026, these significant changes will underscore the urgency for manufacturers aiming to secure contracts with the DoD.
The primary objective of the CMMC2 framework 2.0 is to bolster the protective measures of entities managing Controlled Unclassified Information (CUI) and Federal Contract Information (FCI). By meeting the required standards, manufacturers not only protect their digital assets but also enhance their reputation and competitiveness within the defense contracting sector. Data indicates that mid-market organizations (5,000-9,999 employees) achieve a 59% success rate in top-tier encryption, illustrating the tangible benefits of compliance in improving security outcomes.
Real-world examples underscore the importance of implementing 2.0. Organizations are required to complete evaluations based on their designated compliance level, with a mandate to achieve at least 80% of weighted security practices during initial assessments. This stringent approach ensures that manufacturers are adequately equipped to defend against cyber threats, which are increasingly common in today’s digital environment.
Furthermore, industry experts emphasize that organizations delaying compliance risk exclusion from bids, loss of contracts, and increased regulatory scrutiny. As noted by Accorian, ‘Those who delay risk bid exclusion, contract loss, and regulatory exposure.’ With regulatory enforcement intensifying, manufacturers must view compliance not merely as a checkbox task but as a strategic initiative to secure their position in the defense supply chain. The evolving landscape of 2.0 presents both challenges and opportunities, making it imperative for manufacturers to prioritize their CMMC2 cybersecurity readiness.
Explore CMMC 2.0 Compliance Requirements by Level
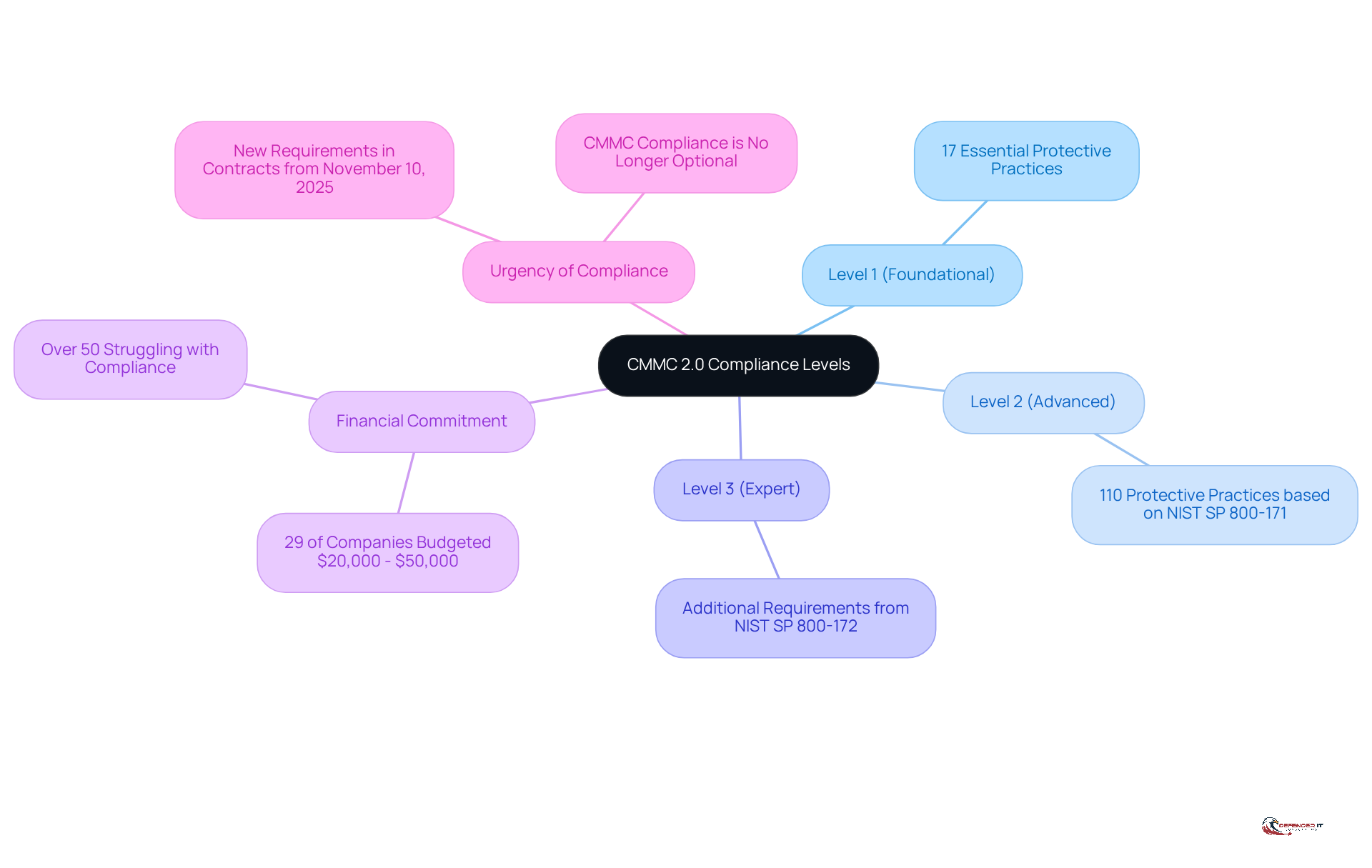
CMMC 2.0 establishes three distinct compliance levels, each designed to address varying degrees of cybersecurity needs within the manufacturing sector:
-
Level 1 (Foundational): This level emphasizes fundamental safeguarding requirements for Federal Contract Information (FCI), mandating 17 essential protective practices aligned with FAR 52.204-21. It serves as the entry point for manufacturers beginning their compliance journey.
-
Level 2 (Advanced): Targeted at organizations managing Controlled Unclassified Information (CUI), Level 2 necessitates compliance with 110 protective practices based on NIST SP 800-171. This level emphasizes advanced cyber hygiene, requiring a more robust protective framework to effectively safeguard sensitive data.
-
Level 3 (Expert): Crafted for organizations handling the most sensitive information, Level 3 includes additional protection requirements from NIST SP 800-172. It demands comprehensive security practices and continuous monitoring, ensuring that organizations maintain a high level of security resilience.
As of 2025, approximately 29% of companies in the defense sector have allocated budgets between $20,000 and $50,000 towards achieving regulatory standards, illustrating the financial commitment necessary to meet these criteria. Notably, over 50% of defense contractors are struggling to fulfill their certification obligations, highlighting the challenges faced by these enterprises. Understanding these levels is crucial for manufacturers to outline their adherence strategy and implement the necessary actions for cmmc2 compliance. The Department of Defense has emphasized that compliance with these standards is no longer optional, stating that “these standards are a vital safeguard to ensure the resilience and security of the supply chain that supports our national defense.” Furthermore, contracting officers will begin incorporating new cybersecurity maturity model certification requirements in solicitations and contracts starting November 10, 2025, underscoring the urgency for manufacturers to align with these standards.
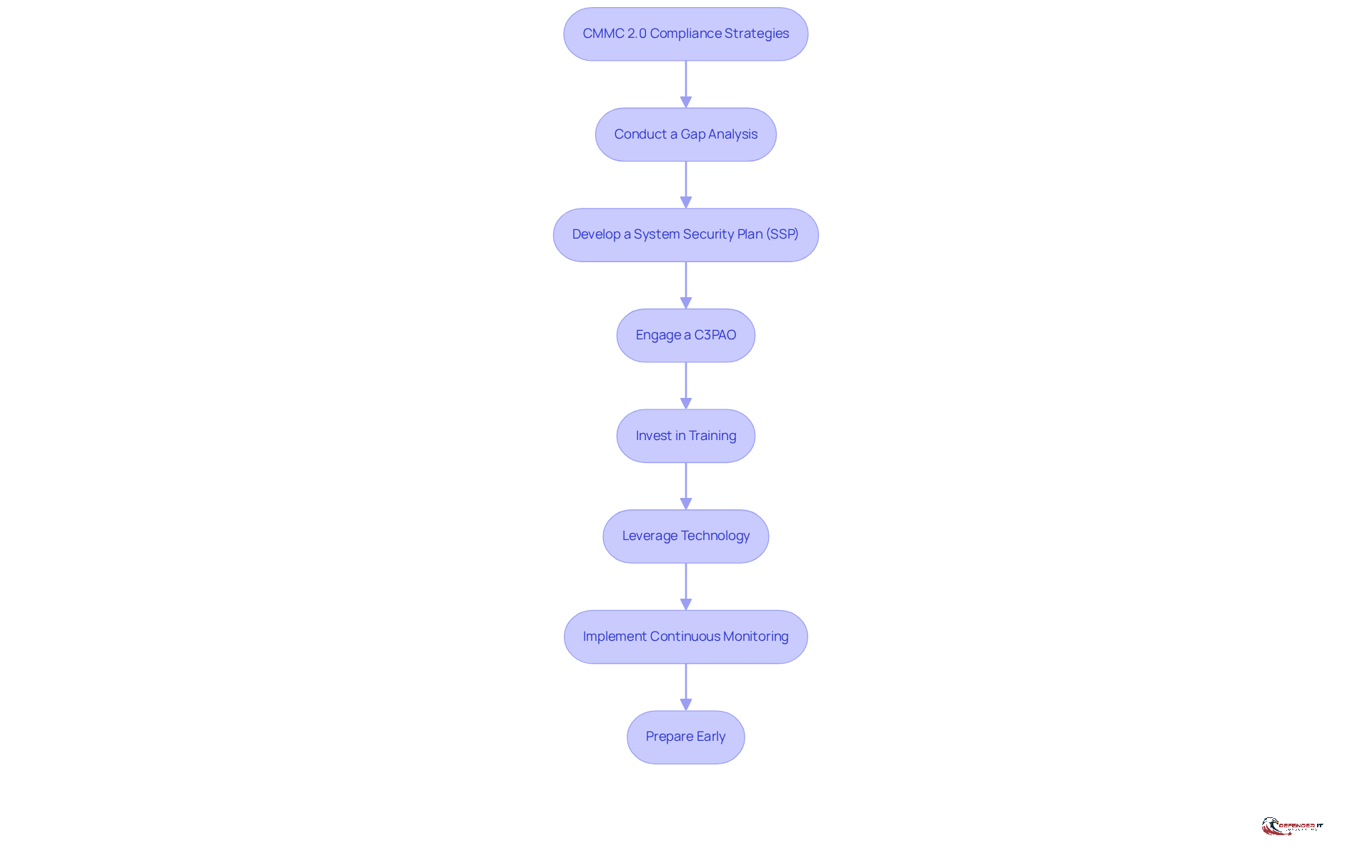
Implement CMMC 2.0: Strategies for Compliance Success
To effectively implement CMMC 2.0 compliance, manufacturing leaders should adopt the following strategies:
-
Conduct a Gap Analysis: Evaluate existing cybersecurity practices against compliance standards to pinpoint areas requiring enhancement. This analysis is essential for understanding regulatory gaps and prioritizing remediation efforts based on risk levels and resource availability.
-
Develop a System Security Plan (SSP): Formulate a detailed SSP that articulates how your organization will fulfill CMMC requirements. This document should include policies, procedures, and controls essential for protecting Controlled Unclassified Information (CUI) and sensitive data, including Plans of Action & Milestones (POA&Ms) to tackle regulatory gaps in compliance with CMMC 2.0.
-
Engage a C3PAO: Partner with a Certified Third-Party Assessment Organization (C3PAO) to facilitate your adherence journey. Their expertise will be invaluable in navigating the complexities of CMMC 2.0 assessments and ensuring that your organization meets all necessary standards.
-
Invest in Training: Implement ongoing training programs for employees to ensure they are well-versed in their responsibilities regarding regulations and the protection of sensitive information. This investment not only boosts awareness of safety but also cultivates a culture of adherence within the organization.
-
Leverage Technology: Adopt cybersecurity tools and solutions that align with CMMC requirements. Employing advanced technologies can greatly enhance your security stance and simplify regulatory processes, making it easier to meet the evolving requirements of CMMC 2.0.
-
Implement Continuous Monitoring: Establish continuous monitoring systems and conduct regular reviews to maintain adherence and adapt to evolving threats. This proactive approach is essential for ensuring that your cybersecurity measures remain effective over time.
-
Prepare Early: Organizations are encouraged to get ready for certification adherence now, as delaying until solicitation release is no longer feasible. Delaying preparation can lead to compressed timelines and higher remediation costs, underscoring the urgency of these strategies.
By adopting these strategies, manufacturing leaders can improve their adherence efforts and gain a competitive advantage in the defense procurement landscape.
Prepare for CMMC 2.0 Assessments: Best Practices
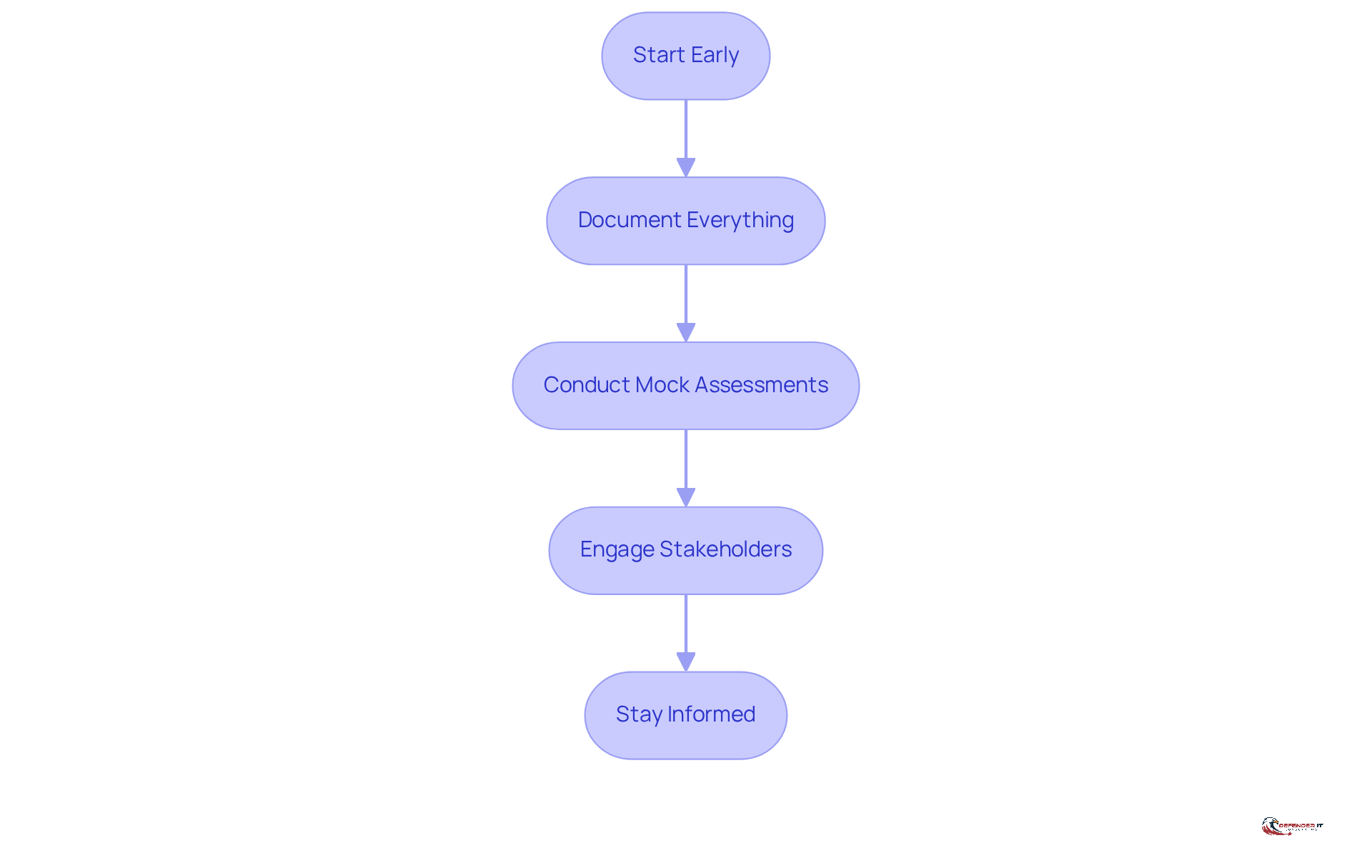
To effectively prepare for CMMC 2.0 assessments, manufacturing leaders should implement several best practices:
-
Start Early: Begin preparations well in advance of the assessment date. Organizations typically require 6 to 18 months to achieve certification, making early action crucial. The cmmc2 regulation, released on September 10, 2025, emphasizes the importance of readiness efforts.
-
Document Everything: Maintain comprehensive documentation of all cybersecurity practices, policies, and evidence of adherence. This documentation is essential for illustrating compliance with security standards during the evaluation process. Notably, 64% of legal and regulatory leaders are prioritizing stronger privacy controls this year, highlighting the critical role of thorough documentation in the current landscape.
-
Conduct Mock Assessments: Simulate the assessment process with internal or external experts to identify weaknesses and enhance readiness. Scheduling a mock assessment ahead of the official CMMC2 assessment in Q3/Q4 2025 can significantly boost confidence and preparedness.
-
Engage Stakeholders: Involve key stakeholders throughout the organization to ensure a comprehensive understanding of regulatory obligations and responsibilities. This collaborative approach fosters a culture of adherence and accountability.
-
Stay Informed: Keep abreast of any changes to cybersecurity maturity model requirements and best practices. Continuous monitoring and adaptation are essential for maintaining compliance and readiness for future assessments, especially as the Department of Defense has indicated that CMMC2 enforcement is a priority and is expected to require third-party validated certifications for higher-risk contracts by late 2026.
Conclusion
The CMMC 2.0 framework is a critical requirement for manufacturing leaders involved in defense contracting, ensuring robust cybersecurity measures are established to protect sensitive information. Understanding and adhering to the CMMC 2.0 standards transcends mere compliance; it is a strategic necessity for securing contracts and maintaining a competitive edge in the industry.
This article provided essential insights into the structure of CMMC 2.0, detailing its three compliance levels:
- Foundational
- Advanced
- Expert
Each designed to address distinct cybersecurity needs. Key strategies for successful implementation were outlined, including:
- Conducting gap analyses
- Developing comprehensive System Security Plans
- Leveraging technology
- Preparing early for assessments
These steps are crucial for manufacturers to effectively navigate the complexities of compliance and position themselves favorably within the defense supply chain.
The urgency of CMMC 2.0 compliance is paramount. As regulatory enforcement intensifies, manufacturers must prioritize their cybersecurity readiness and integrate compliance into their operational strategy. By taking proactive measures today, organizations can not only meet the requirements but also bolster their resilience against cyber threats, ensuring they remain viable players in the defense contracting arena. Embracing this framework is essential for safeguarding sensitive data and securing the future of manufacturing in the defense sector.
Frequently Asked Questions
What is CMMC 2.0 and why is it important?
CMMC 2.0 is a cybersecurity framework established by the Department of Defense (DoD) to ensure that defense contractors and subcontractors implement strong cybersecurity measures to protect sensitive information. Its importance lies in safeguarding Controlled Unclassified Information (CUI) and Federal Contract Information (FCI), which is critical for national security.
How has the CMMC 2.0 framework changed from the previous version?
CMMC 2.0 simplifies the original five-level structure into three distinct levels, making the certification process more straightforward and introducing phased timelines for compliance.
What is the deadline for compliance with CMMC 2.0?
Organizations must comply with CMMC 2.0 by January 14, 2026, to continue securing contracts with the DoD.
What are the benefits of achieving compliance with CMMC 2.0?
Achieving compliance helps manufacturers protect their digital assets, enhances their reputation, and improves competitiveness within the defense contracting sector. Data shows that mid-market organizations experience a 59% success rate in top-tier encryption when compliant.
What are the compliance requirements for organizations under CMMC 2.0?
Organizations must complete evaluations based on their designated compliance level and achieve at least 80% of weighted security practices during initial assessments to be adequately equipped against cyber threats.
What are the risks of delaying compliance with CMMC 2.0?
Delaying compliance can lead to exclusion from bids, loss of contracts, and increased regulatory scrutiny, as emphasized by industry experts.
How should manufacturers view compliance with CMMC 2.0?
Manufacturers should view compliance as a strategic initiative rather than a mere checkbox task, as it is essential for securing their position in the defense supply chain.
What are the current challenges and opportunities presented by CMMC 2.0?
The evolving landscape of CMMC 2.0 presents challenges in meeting compliance standards but also opportunities for organizations to enhance their cybersecurity readiness and competitiveness in the defense sector.