Introduction
In today’s landscape, where cyber threats are more pronounced than ever, the manufacturing sector stands at a pivotal juncture. The convergence of operational technology and information technology introduces distinct challenges, underscoring the necessity of a Security Operations Center (SOC) to protect critical infrastructure.
By examining effective strategies for improving SOC monitoring, organizations can enhance their security posture while effectively managing compliance and operational efficiency.
As cyberattacks become increasingly sophisticated, manufacturers must consider how to ensure their SOC is equipped to confront these evolving threats directly.
Define the Role and Importance of a Security Operations Center (SOC)
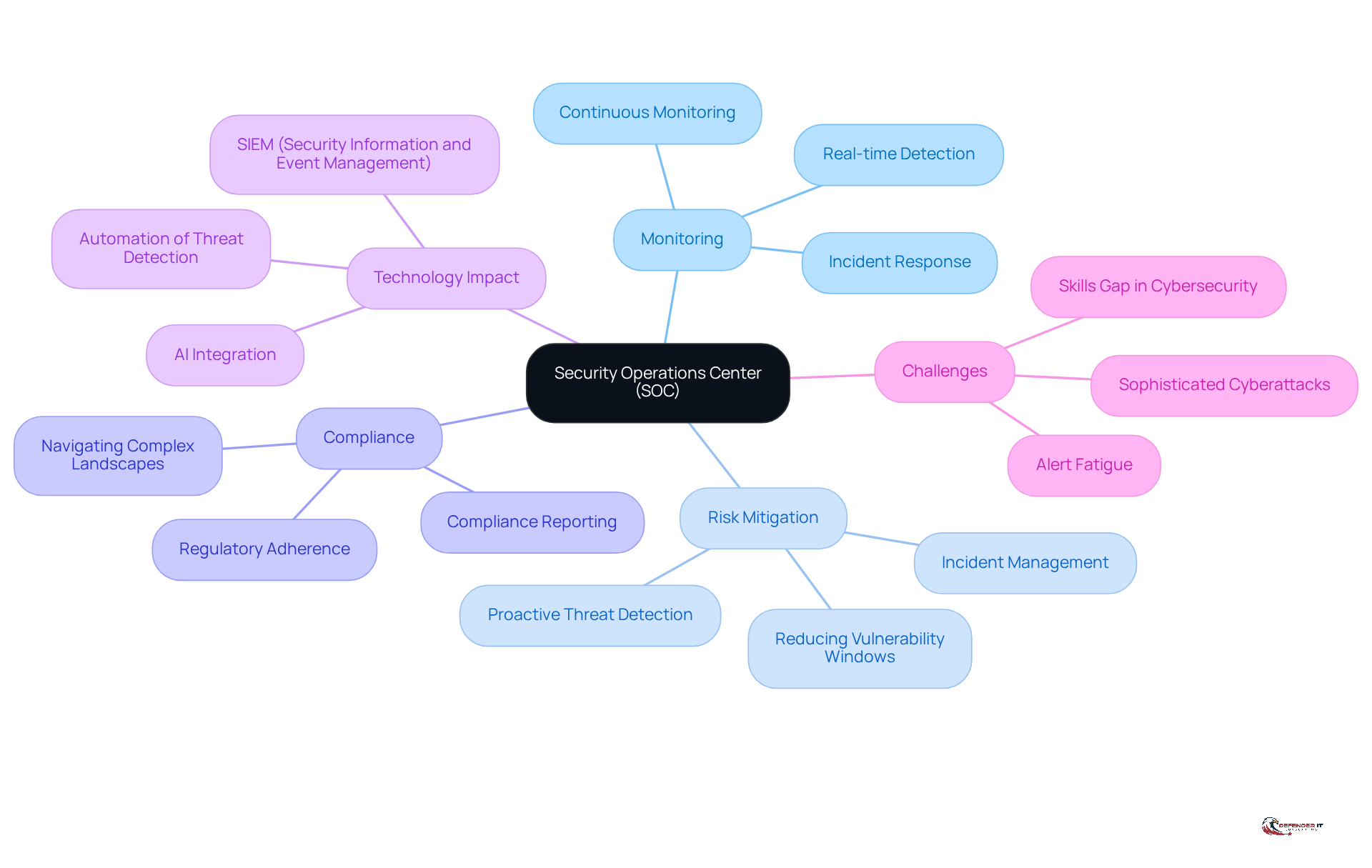
A Security Operations Center (SOC) is essential for an organization’s cybersecurity strategy, acting as its nerve center. It is responsible for SOC monitoring, including the real-time detection, analysis, and response to security events. In the manufacturing sector, where operational technology (OT) often merges with information technology (IT), the SOC is crucial for protecting critical infrastructure from cyber threats. By providing continuous SOC monitoring and response capabilities, the SOC helps organizations mitigate risks, comply with industry regulations, and ensure operational continuity.
The importance of a SOC cannot be overstated; it not only protects sensitive information but also enhances the overall security posture of the organization. As Ido Assaf states, "AI is reshaping the very foundation of SOC functionality," underscoring the impact of advanced technologies on SOC operations. A case study involving a large manufacturer demonstrates how a proactive SOC approach can improve visibility and decrease the mean time to detect and resolve incidents, thereby reducing potential damage.
Moreover, as Davies cautions, "Cry wolf too many times, and you lose credibility," highlighting the necessity of managing alert fatigue within SOC operations. Statistics indicate that 54% of businesses believe cyberattacks are too sophisticated for their internal teams to handle independently, emphasizing the critical role of SOCs in the manufacturing sector.
Establish SOC Readiness Through Resource Assessment and Preparation
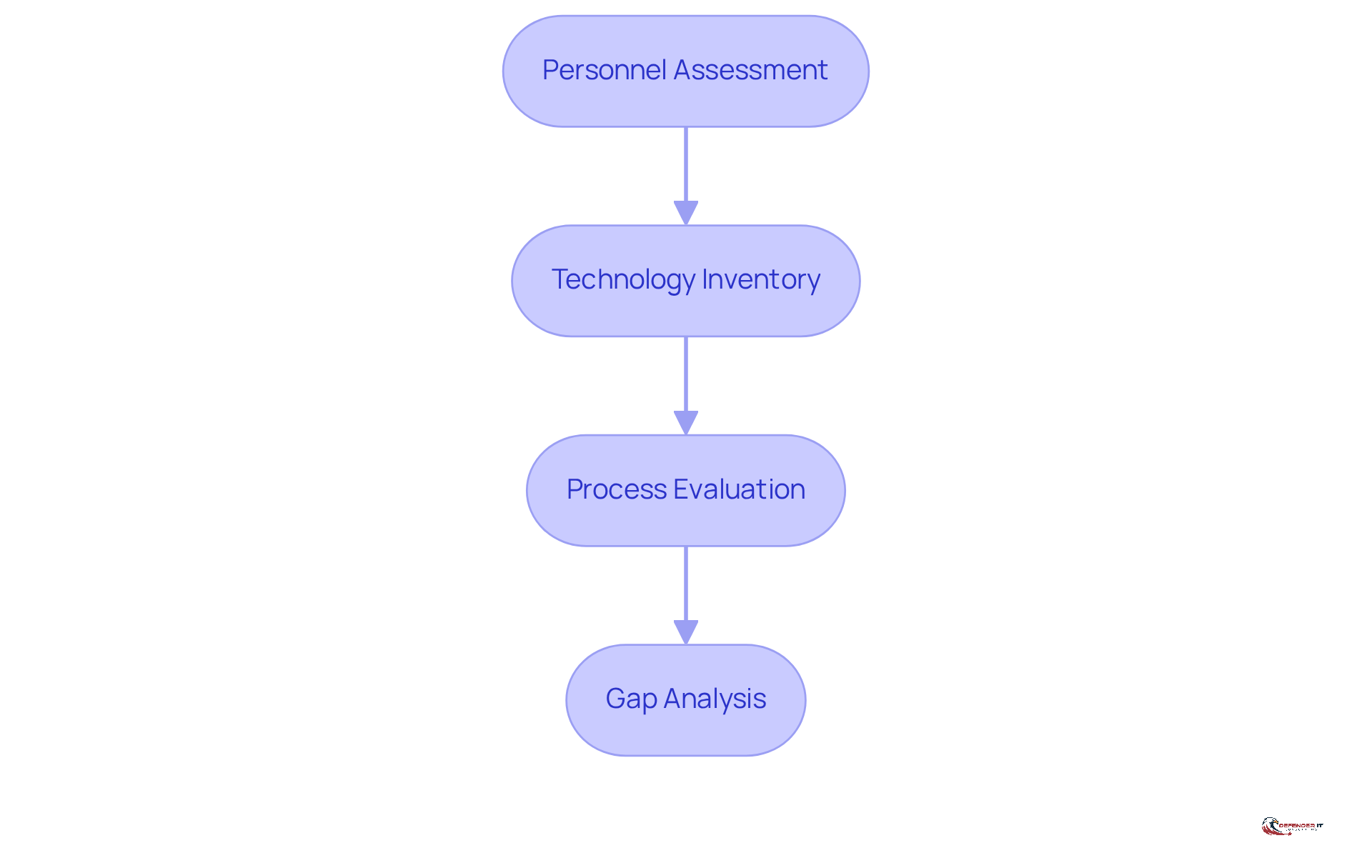
To effectively manage cybersecurity risks, organizations must conduct a thorough resource evaluation of their Security Operations Center (SOC). This evaluation should encompass existing personnel, technology, and processes to pinpoint strengths and weaknesses. The key steps in this process include:
-
Personnel Assessment: Assess the skills and expertise of SOC staff to ensure they are proficient in the latest cybersecurity practices and technologies. Training programs should focus on both foundational skills and advanced techniques to address evolving challenges, such as AI-driven phishing and other sophisticated attack vectors.
-
Technology Inventory: Perform a comprehensive assessment of current tools and technologies. Identify capability gaps in areas such as threat detection, incident response, and compliance monitoring. Consider integrating advanced solutions that utilize AI for enhanced risk analysis, ensuring continuous protection throughout the AI lifecycle to mitigate associated risks.
-
Process Evaluation: Review existing incident response protocols and workflows. It is crucial that these are well-documented and regularly updated to adapt to the changing risk landscape, incorporating lessons learned from previous incidents.
-
Gap Analysis: Conduct a gap analysis to identify areas requiring additional resources or improvements. This may involve hiring more staff, particularly entry-level professionals to cultivate a skilled workforce, investing in new technologies, or enhancing training programs to address specific vulnerabilities.
By systematically evaluating these elements, organizations can significantly bolster their SOC’s preparedness and resilience against cyber risks, ensuring they are equipped to respond effectively in a dynamic cybersecurity environment.
Implement Continuous Monitoring and Threat Response Protocols
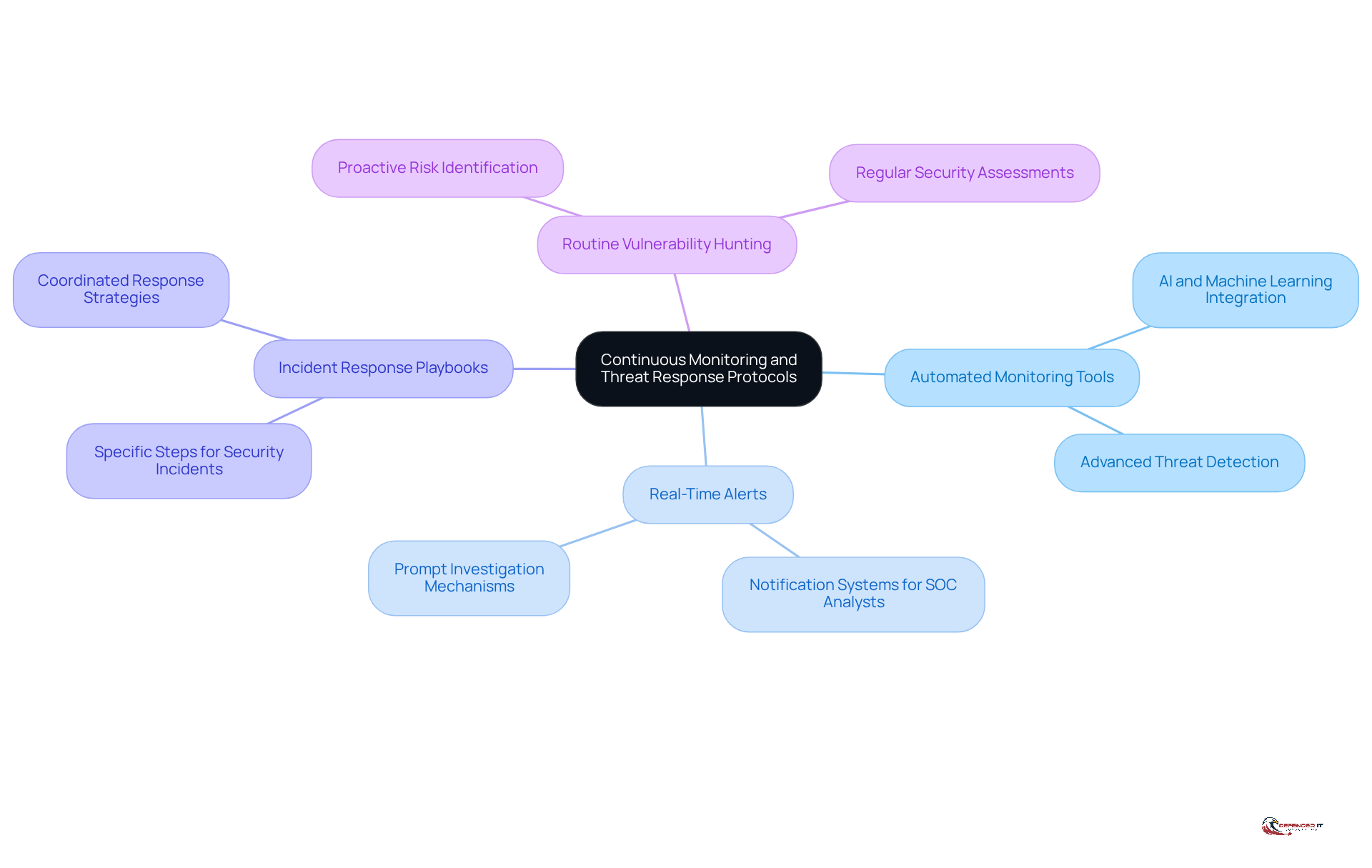
Continuous SOC monitoring serves as a cornerstone of effective Security Operations Center operations, allowing organizations to identify irregularities and potential risks in real-time. To implement robust monitoring and threat response protocols, organizations should consider the following best practices:
- Automated Monitoring Tools: Invest in advanced monitoring solutions that leverage artificial intelligence and machine learning to detect suspicious activities and potential threats.
- Real-Time Alerts: Establish a system for real-time notifications that alert SOC analysts to potential security events, facilitating prompt investigation and response.
- Incident Response Playbooks: Develop and maintain incident response playbooks that delineate specific steps to take during various types of security incidents, ensuring a swift and coordinated response.
- Routine Vulnerability Hunting: Conduct regular vulnerability hunting exercises to proactively identify weaknesses and potential risks within the network, helping to uncover hidden threats before they can be exploited.
By implementing these continuous SOC monitoring and response protocols, organizations can significantly enhance their capacity to detect and mitigate cyber threats.
Integrate Compliance Management into SOC Operations
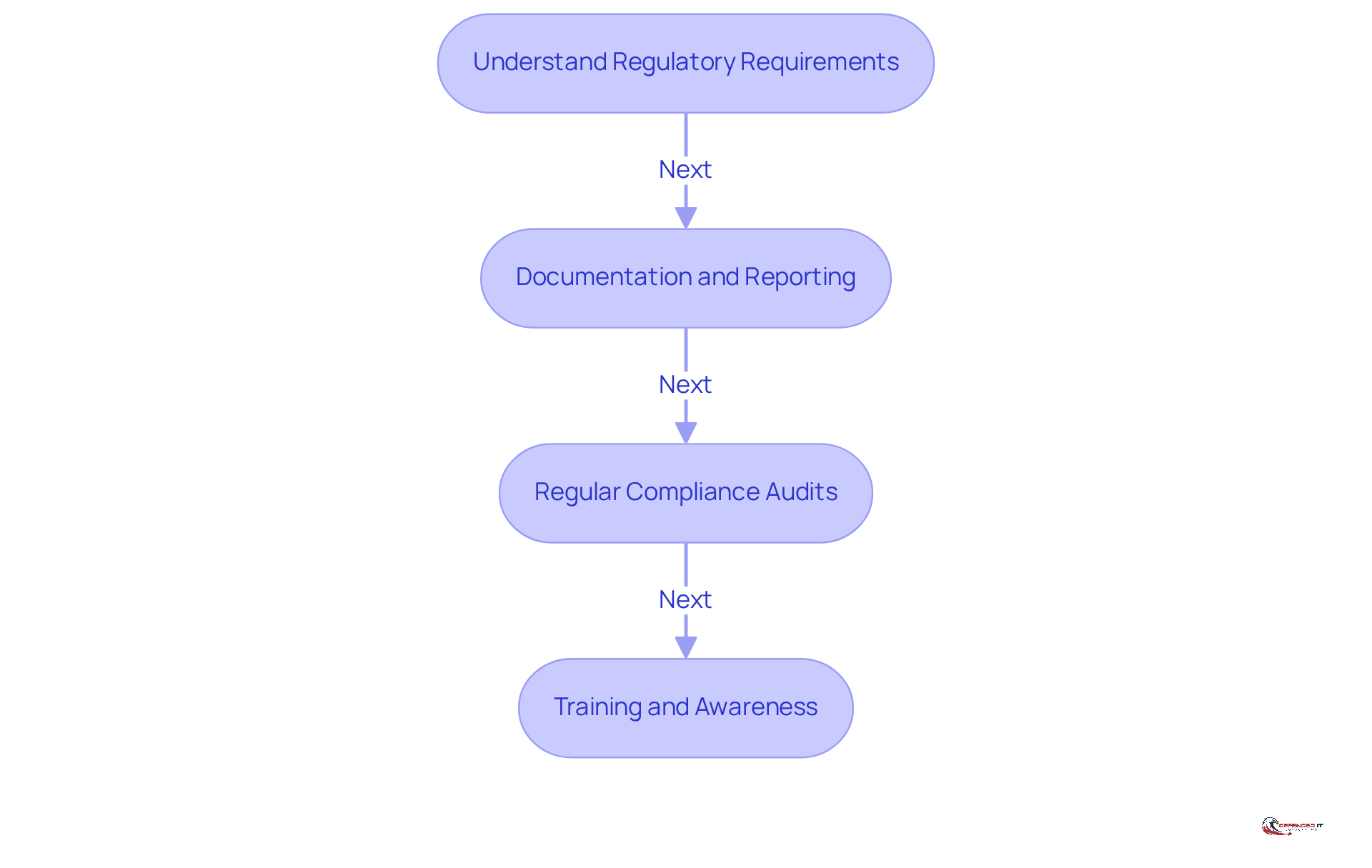
Compliance management is essential for effective SOC monitoring operations, especially in regulated sectors like manufacturing. By effectively integrating compliance into SOC monitoring, organizations can bolster their security posture while fulfilling regulatory obligations.
- Understand Regulatory Requirements: Organizations must familiarize themselves with relevant regulations and standards applicable to their industry, including ISO 27001, NIST, and specific manufacturing regulations. This foundational knowledge is crucial for compliance.
- Documentation and Reporting: It is imperative to maintain comprehensive documentation of all security policies, procedures, and incident responses. Such documentation is vital for compliance audits and assessments, ensuring that organizations can demonstrate adherence to regulations.
- Regular Compliance Audits: Conducting regular audits is necessary to evaluate compliance with established policies and regulatory requirements. These audits help identify areas for improvement and ensure ongoing adherence to standards.
- Training and Awareness: Ongoing training for SOC staff regarding compliance requirements and best practices is essential. This training ensures that all team members understand their responsibilities in maintaining compliance.
By integrating compliance management into SOC monitoring, organizations not only enhance their security posture but also ensure they meet their regulatory obligations.
Conclusion
The significance of a Security Operations Center (SOC) in manufacturing security is paramount, acting as the cornerstone of an organization’s cybersecurity framework. A well-functioning SOC not only safeguards sensitive data but also bolsters the overall security posture, enabling manufacturers to operate without the persistent threat of cyberattacks. By harnessing advanced technologies and adopting a proactive approach, organizations can markedly enhance their resilience against the ever-evolving landscape of threats.
This article has outlined essential practices to strengthen SOC monitoring within the manufacturing sector. Key practices include:
- Conducting comprehensive resource assessments
- Implementing continuous monitoring and threat response protocols
- Integrating compliance management into SOC operations
Each of these strategies is tailored to address specific challenges faced by manufacturers, ultimately fostering a more robust and effective cybersecurity strategy.
As the manufacturing landscape evolves, the necessity of a well-prepared SOC cannot be overstated. Organizations are urged to prioritize their SOC readiness, invest in cutting-edge monitoring technologies, and cultivate a culture of compliance among their teams. By doing so, they not only mitigate risks but also position themselves for sustained success in an increasingly complex digital environment. Adopting these best practices will ensure that manufacturers remain vigilant and equipped to defend against the multitude of cyber threats that lie ahead.