Introduction
Understanding the complexities of the Cybersecurity Maturity Model Certification (CMMC) is crucial for organizations seeking to secure federal contracts and safeguard sensitive information. As cybersecurity regulations continue to evolve, selecting the appropriate CMMC IT provider becomes increasingly vital for ensuring compliance and gaining a competitive edge. With a multitude of providers available, how can organizations guarantee they choose a partner that not only fulfills their compliance requirements but also strengthens their security posture? This guide delineates five clear steps to navigate the selection process, equipping businesses to excel in a demanding regulatory landscape.
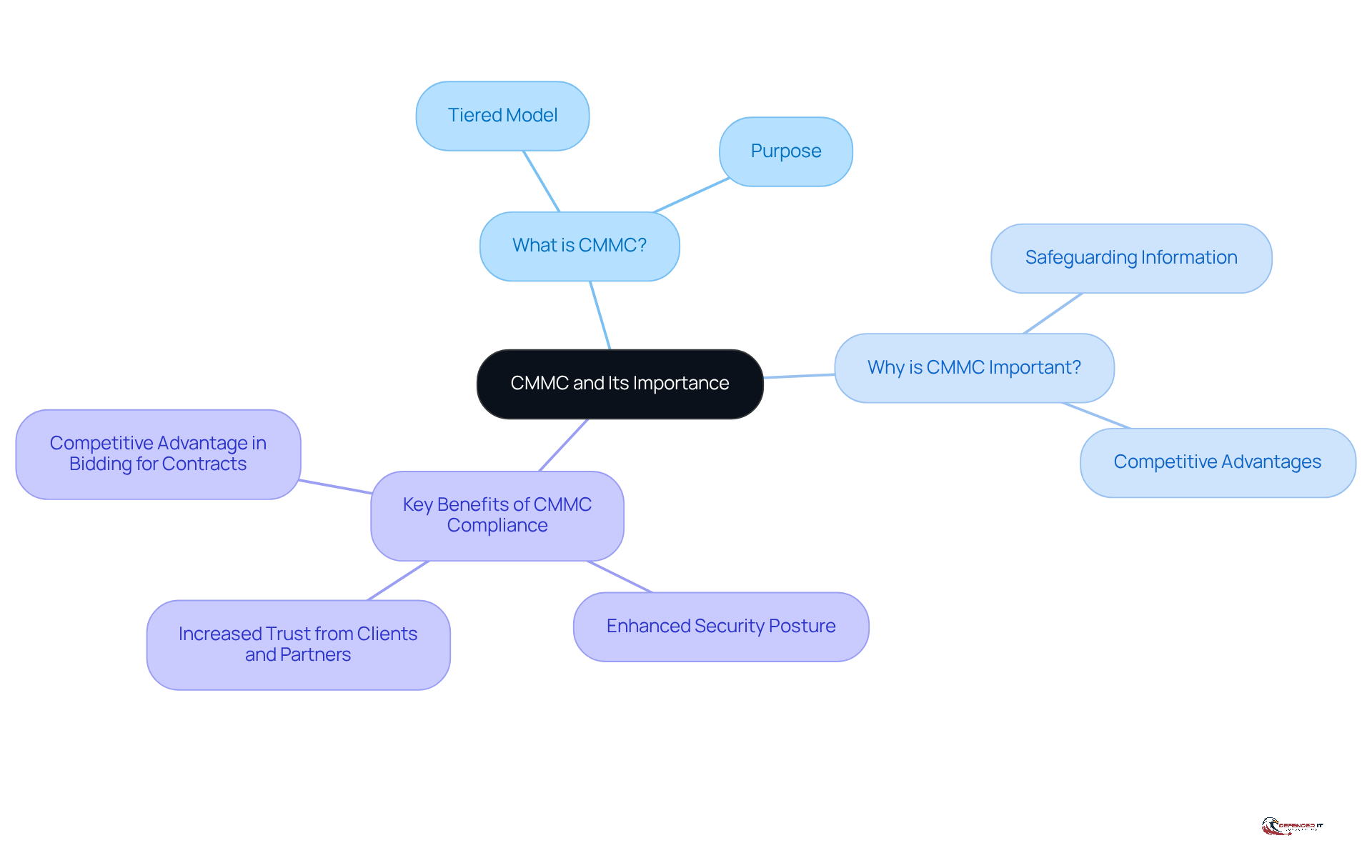
Understand CMMC and Its Importance for Your Organization
The Cybersecurity Maturity Model Certification (CMMC) serves as a crucial framework established by the Department of Defense (DoD) to enhance the cybersecurity posture of organizations managing Controlled Unclassified Information (CUI). For any entity seeking to engage with the DoD or secure federal contracts, a thorough understanding of the CMMC is imperative.
-
What is the Cybersecurity Maturity Model Certification?
The CMMC is structured as a tiered model that evaluates a company’s cybersecurity practices across various levels, each imposing progressively stringent requirements. This tiered approach not only ensures compliance but also equips organizations to defend against evolving cyber threats. -
Why is the Cybersecurity Maturity Model Certification important?
Adhering to the required standards is vital for safeguarding sensitive information and maintaining eligibility for federal contracts. Organizations that fail to meet these standards risk losing valuable contracts and may encounter legal repercussions, highlighting the framework’s critical role in the defense sector. Notably, contractors who invest early in readiness are better positioned to secure contracts that competitors may not qualify for, underscoring the competitive advantage of early compliance. -
Key Benefits of CMMC Compliance:
- Enhanced Security Posture: Organizations that comply with CMMC can significantly strengthen their defenses against cyber threats, thereby reducing the likelihood of data breaches.
- Increased Trust from Clients and Partners: Demonstrating compliance builds confidence among stakeholders, fostering stronger relationships and expanding business opportunities.
- Competitive Advantage in Bidding for Contracts: Adherence to compliance standards can set entities apart in a competitive bidding landscape, making them more attractive to potential clients.
Moreover, it is essential to acknowledge that new DoD regulations, effective November 2025, will introduce heightened cybersecurity standards for forthcoming contracts. Consequently, it is vital for businesses to stay informed and prepared. By grasping the nuances of the CMMC framework, entities can strategically navigate their compliance journey, ensuring they are well-equipped to meet the criteria necessary for obtaining federal contracts.
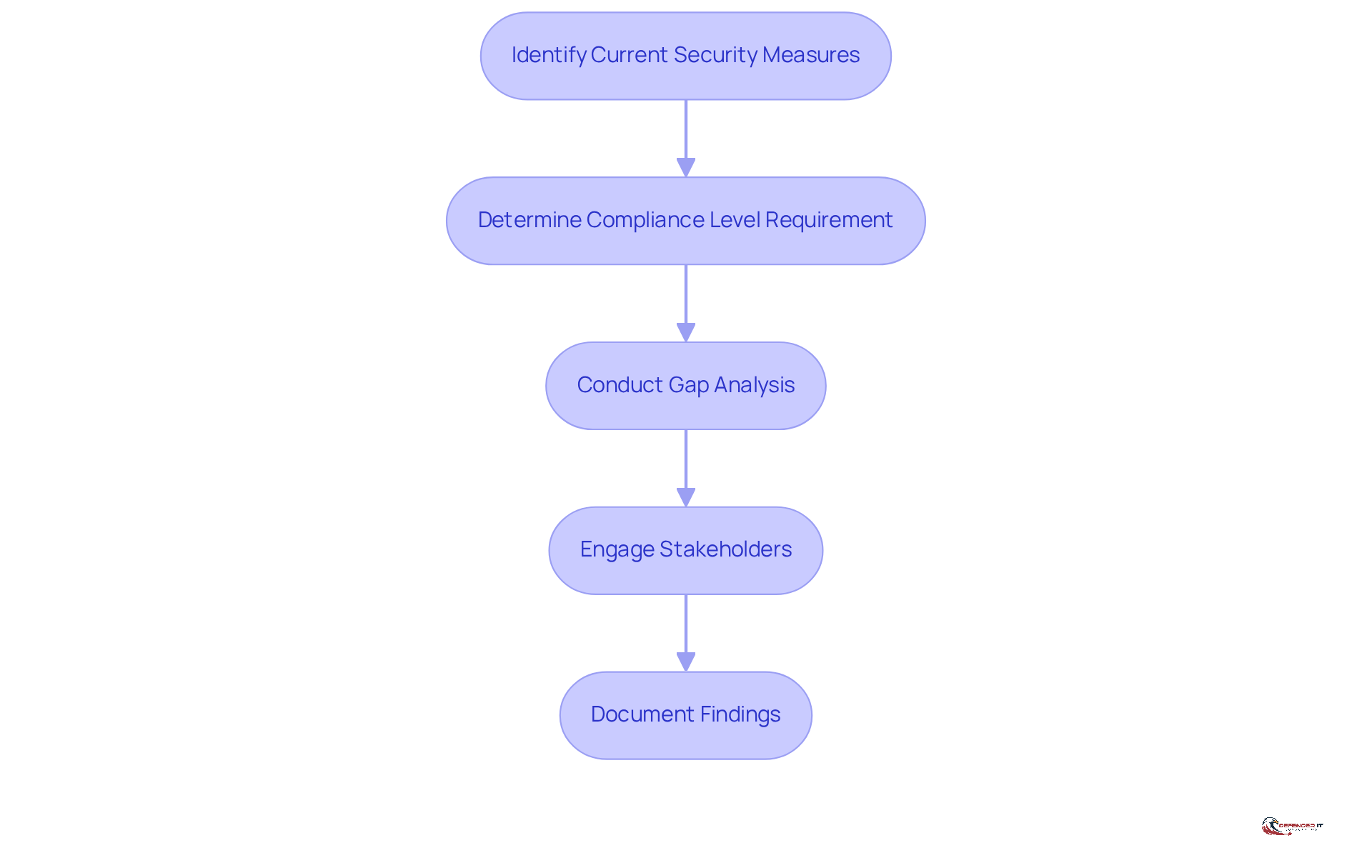
Assess Your Organization’s CMMC Compliance Needs
To effectively navigate the cybersecurity framework landscape, entities must first evaluate their current security posture. This foundational assessment is crucial for establishing a baseline for adherence to compliance standards.
- Identify Your Current Security Measures: Begin by reviewing existing policies, procedures, and technologies in place. This step is essential for understanding your current security landscape.
- Determine Your Compliance Level Requirement: Based on the type of data you manage, identify which compliance level (1, 2, or 3) applies to your organization. Understanding your compliance level is vital for focused adherence efforts.
- Conduct a Gap Analysis: Compare your current security measures against compliance requirements to identify any gaps. Notably, only 28% of entities conduct formal third-party risk evaluations, slightly above the 25% industry average. This statistic underscores the necessity for comprehensive assessments to ensure regulatory preparedness. Additionally, 39% of organizations cite vendor adherence as a significant challenge, highlighting the importance of addressing regulatory challenges in the context of CMMC evaluations.
- Engage Stakeholders: Involve key personnel from IT, regulatory, and management teams to ensure a thorough assessment. Collaboration across departments fosters a comprehensive understanding of security requirements and regulatory challenges. Organizations that implement effectiveness measurement tend to achieve significantly better results, reinforcing the importance of this collaborative approach.
- Document Findings: Create a report that outlines your current adherence status and identifies areas needing enhancement. This documentation will serve as a roadmap for your adherence journey, guiding necessary actions and adjustments.
By following these steps, organizations can enhance their readiness for certification standards, addressing potential vulnerabilities and strengthening their overall security posture. It is crucial to recognize that mandatory Level 2 certification by a C3PAO will be required starting November 10, 2026, which adds urgency to these adherence efforts.
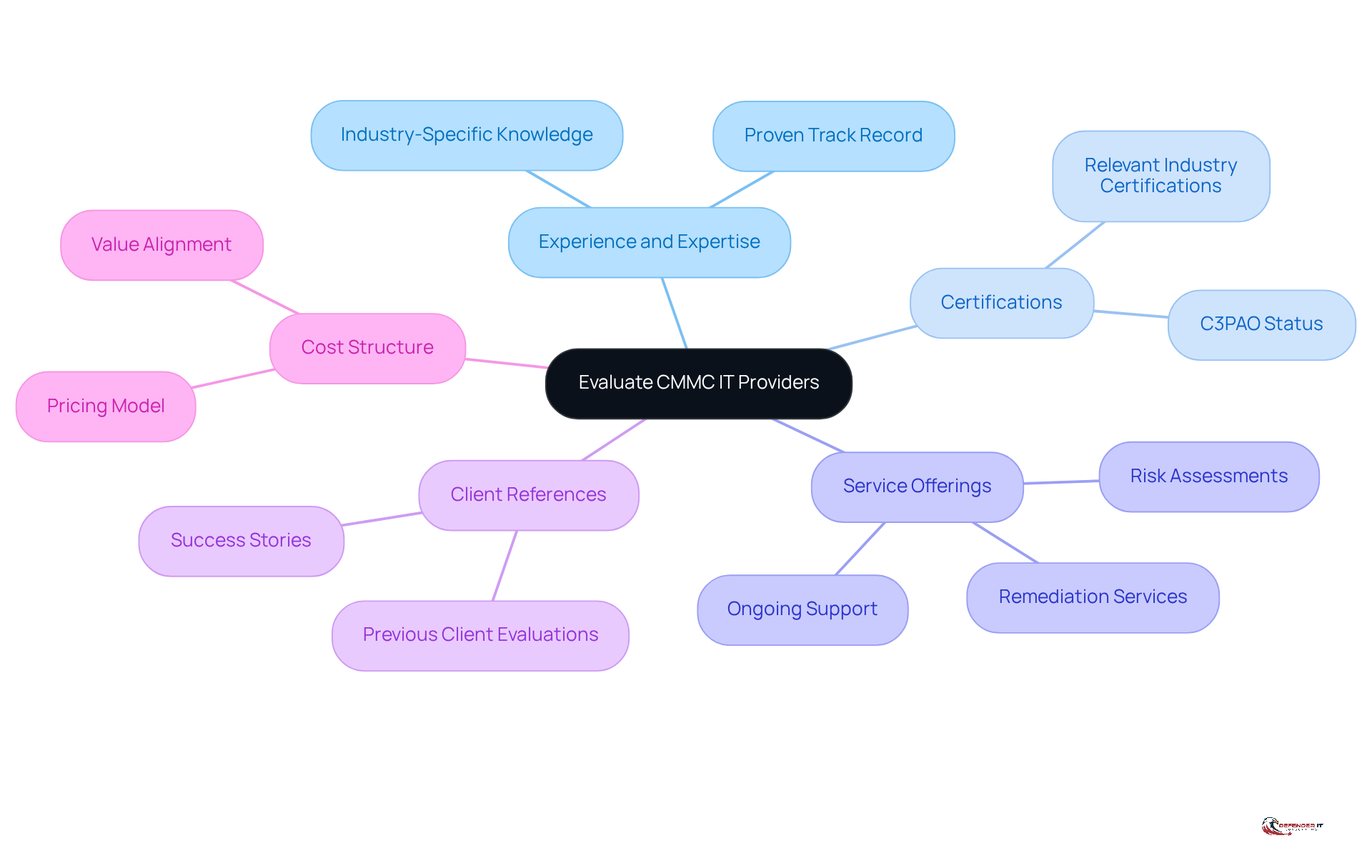
Evaluate Potential CMMC IT Providers Based on Key Criteria
Choosing the right CMMC IT provider is crucial for ensuring successful compliance. Organizations should consider the following criteria:
- Experience and Expertise: Look for a CMMC IT provider with a proven track record in CMMC compliance, particularly within your specific industry.
- Certifications: Verify that the company holds relevant certifications, such as C3PAO (Certified Third-Party Assessment Organization) status.
- Service Offerings: Assess the range of services provided, including risk assessments, remediation, and ongoing support.
- Client References: Request references from previous clients to evaluate the effectiveness and reliability of the service.
- Cost Structure: Understand the pricing model to ensure it aligns with your budget while delivering value.
By thoroughly evaluating potential partners against these criteria, organizations can select a CMMC IT provider that aligns with their regulatory objectives.
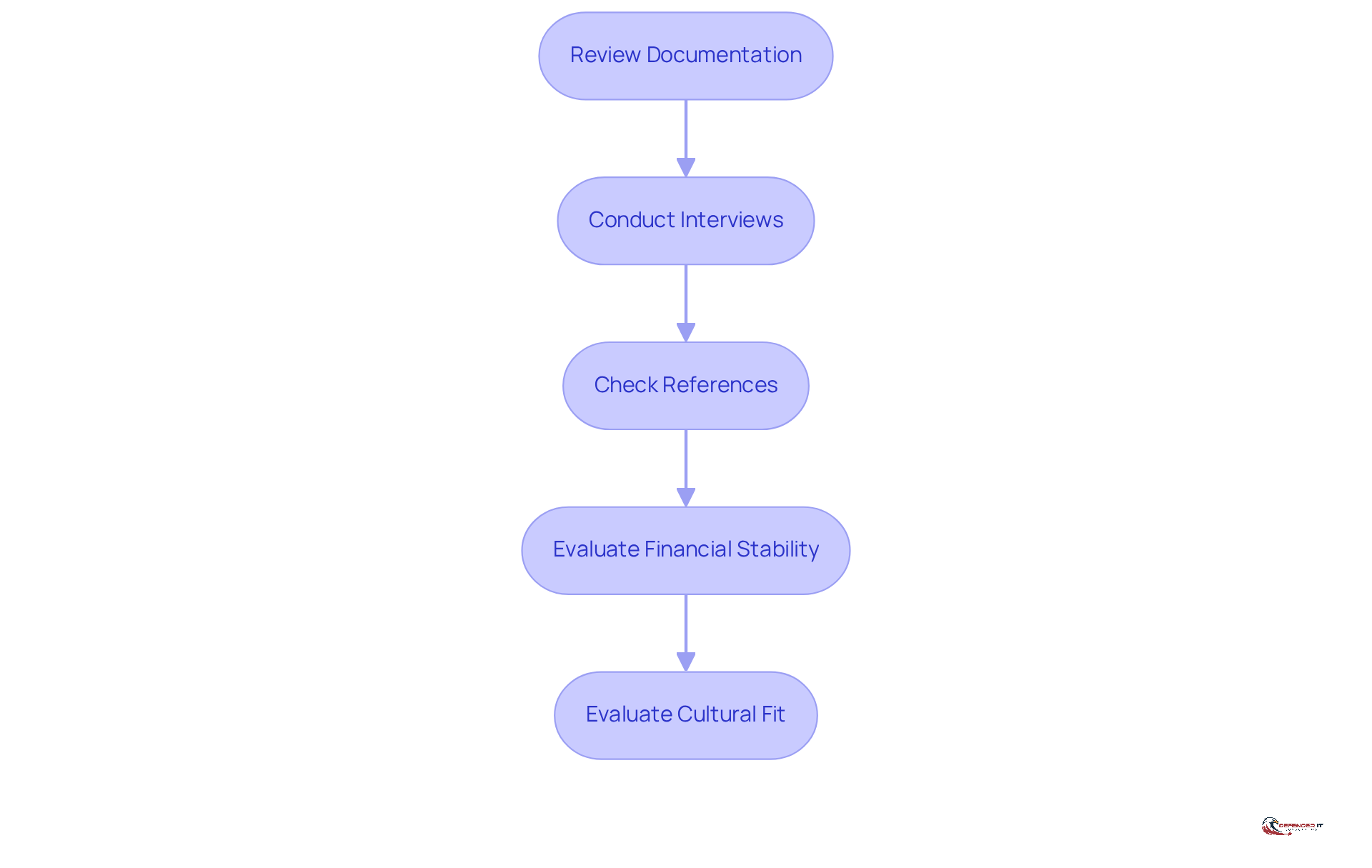
Conduct Due Diligence on Shortlisted CMMC IT Providers
Once you have narrowed down potential IT vendors, conducting due diligence is essential. This process involves several key steps:
-
Review Documentation: Begin by requesting and examining documentation related to the supplier’s adherence processes, methodologies, and past performance. As noted by the Department of Defense, “successful CMMC adherence requires documented controls, ongoing monitoring, and periodic assessment.” This highlights the importance of thorough documentation in evaluating a supplier’s readiness.
-
Conduct Interviews: Arrange interviews with essential staff from the supplier to assess their knowledge and approach regarding compliance. Engaging directly with their team allows you to gauge their understanding of the complexities surrounding CMMC requirements.
-
Check References: Reach out to the contacts provided by the supplier to gain insights into their performance and reliability. This step is particularly crucial given that fewer than 100 Certified Third-Party Assessment Organizations (C3PAOs) are currently accredited, making it vital to choose wisely.
-
Evaluate Financial Stability: Assess the financial health of the supplier to ensure they can support your regulatory efforts in the long term. A stable financial position is critical, especially as the landscape of cybersecurity regulations increasingly ties to financial viability.
-
Evaluate Cultural Fit: Consider whether the supplier’s values and culture align with your organization’s, as this alignment can significantly influence collaboration. A strong cultural fit can enhance the partnership and facilitate smoother interactions.
Conducting comprehensive due diligence is crucial to ensure that you select a supplier capable of meeting your regulatory requirements. This is particularly pressing given that readiness for audits has decreased from 8% in 2023 to a mere 1% in 2025, underscoring the urgency of this process.
Establish a Partnership for Ongoing Support and Compliance
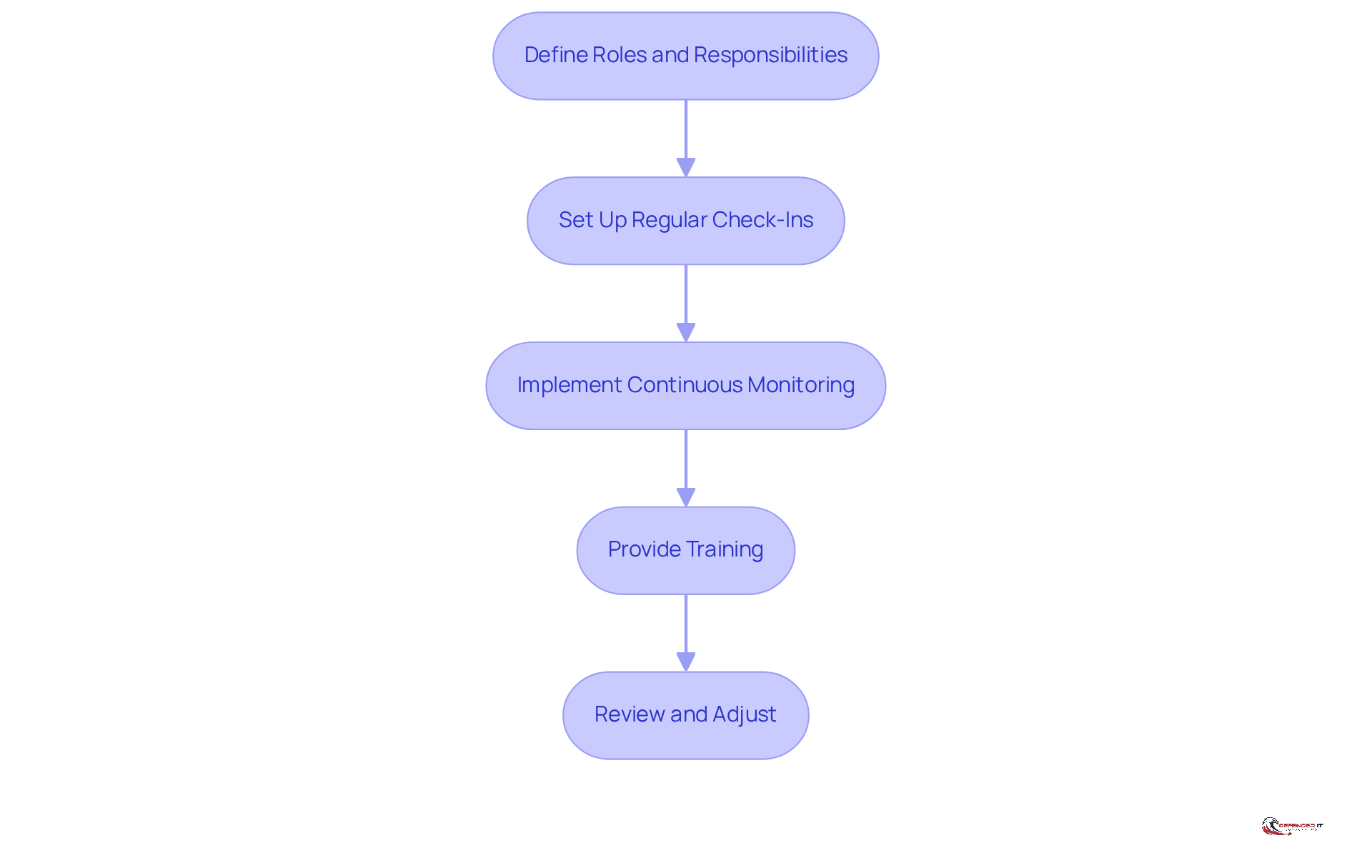
After selecting a CMMC IT provider, establishing a strong partnership is crucial for ensuring ongoing compliance. Consider the following steps:
-
Define Roles and Responsibilities: Clearly outline the duties of both your organization and the provider in maintaining adherence to standards. This clarity is essential, as organizations with defined roles are better positioned to manage regulatory compliance effectively when working with a CMMC IT provider. Notably, only 22% of CMMC organizations incorporate security requirements into supplier contracts, revealing a significant governance gap that needs to be addressed.
-
Set Up Regular Check-Ins: Schedule consistent meetings to review compliance status, discuss updates, and address any emerging threats. Regular communication with a CMMC IT provider fosters transparency and proactive management of regulatory challenges.
-
Implement Continuous Monitoring: Work with your provider to establish continuous monitoring practices. This proactive approach is vital, as organizations that utilize a CMMC IT provider for continuous monitoring are more adept at identifying and rectifying compliance gaps. In fact, only 38% of organizations pursuing certification have established comprehensive governance controls, highlighting the need for effective monitoring systems. As noted by Kiteworks, “CMMC 2.0 success depends more on governance maturity than technical sophistication or organizational resources.”
-
Provide Training: Ensure that your staff receives ongoing education on regulatory requirements and best practices. Continuous training is key for a CMMC IT provider to ensure a knowledgeable workforce capable of navigating evolving regulations.
-
Review and Adjust: Regularly assess the partnership and implement necessary changes to ensure alignment with regulatory objectives. Organizations that adapt their strategies in response to changing needs are more likely to succeed in achieving and maintaining compliance.
By fostering a robust alliance and focusing on these critical areas, organizations can enhance their resilience against evolving cyber threats and ensure ongoing adherence to CMMC standards through a CMMC IT provider. For instance, organizations that have adopted continuous monitoring practices have reported significant improvements in their compliance posture, demonstrating the effectiveness of proactive governance.
Conclusion
Choosing the right CMMC IT provider is a critical decision for organizations seeking compliance with the Cybersecurity Maturity Model Certification. This guide presents a structured approach to navigating the complexities of CMMC compliance, highlighting the importance of understanding the model and its essential role in securing federal contracts. By adhering to the outlined steps, organizations can effectively prepare to meet the stringent requirements established by the Department of Defense.
Key strategies discussed include:
- Assessing current compliance needs
- Evaluating potential IT providers against essential criteria
- Conducting thorough due diligence
- Establishing robust partnerships for ongoing support
Each of these steps is designed to enhance an organization’s cybersecurity posture, ensuring compliance while maintaining competitiveness in the federal contracting arena. The urgency of these actions is amplified by impending regulatory changes, making it essential for organizations to act swiftly and strategically.
The importance of selecting the right CMMC IT provider cannot be overstated. This decision influences not only compliance but also the organization’s resilience against cyber threats. By prioritizing due diligence, fostering effective partnerships, and committing to continuous improvement, organizations can confidently navigate the evolving cybersecurity landscape. Taking these proactive steps today will empower entities to secure their future in an increasingly competitive environment, equipping them to meet both current and future compliance challenges.
Frequently Asked Questions
What is the Cybersecurity Maturity Model Certification (CMMC)?
The CMMC is a framework established by the Department of Defense (DoD) designed to enhance the cybersecurity posture of organizations that manage Controlled Unclassified Information (CUI). It evaluates a company’s cybersecurity practices across various levels, each with progressively stringent requirements.
Why is CMMC important for organizations?
CMMC is crucial for safeguarding sensitive information and maintaining eligibility for federal contracts. Organizations that do not meet the standards risk losing contracts and facing legal repercussions. Early compliance can provide a competitive advantage in securing contracts that others may not qualify for.
What are the key benefits of CMMC compliance?
Key benefits include: Enhanced Security Posture: Strengthened defenses against cyber threats and reduced likelihood of data breaches. Increased Trust: Compliance builds confidence among clients and partners, fostering stronger relationships. Competitive Advantage: Adherence to CMMC standards makes organizations more attractive in bidding for contracts.
What steps should organizations take to assess their CMMC compliance needs?
Organizations should: 1. Identify Current Security Measures: Review existing policies, procedures, and technologies. 2. Determine Compliance Level Requirement: Identify which compliance level (1, 2, or 3) applies to their data. 3. Conduct a Gap Analysis: Compare current measures against compliance requirements to identify gaps. 4. Engage Stakeholders: Involve key personnel from IT, regulatory, and management teams. 5. Document Findings: Create a report outlining adherence status and areas for enhancement.
What is the significance of the new DoD regulations effective November 2025?
New DoD regulations will introduce heightened cybersecurity standards for upcoming contracts, making it vital for businesses to stay informed and prepared to meet these standards.
When will mandatory Level 2 certification by a C3PAO be required?
Mandatory Level 2 certification by a C3PAO will be required starting November 10, 2026. Organizations must enhance their readiness for certification standards before this deadline.