Introduction
Achieving compliance with the Cybersecurity Maturity Model Certification (CMMC) Level 2 is not merely a regulatory requirement; it represents a vital step in protecting sensitive information within organizations that handle Controlled Unclassified Information (CUI). Currently, only a small fraction of defense contractors hold this certification, underscoring the urgent need for effective strategies to meet these standards. Organizations must navigate the complexities of CMMC Level 2 compliance, ensuring they not only fulfill regulatory demands but also bolster their overall cybersecurity posture.
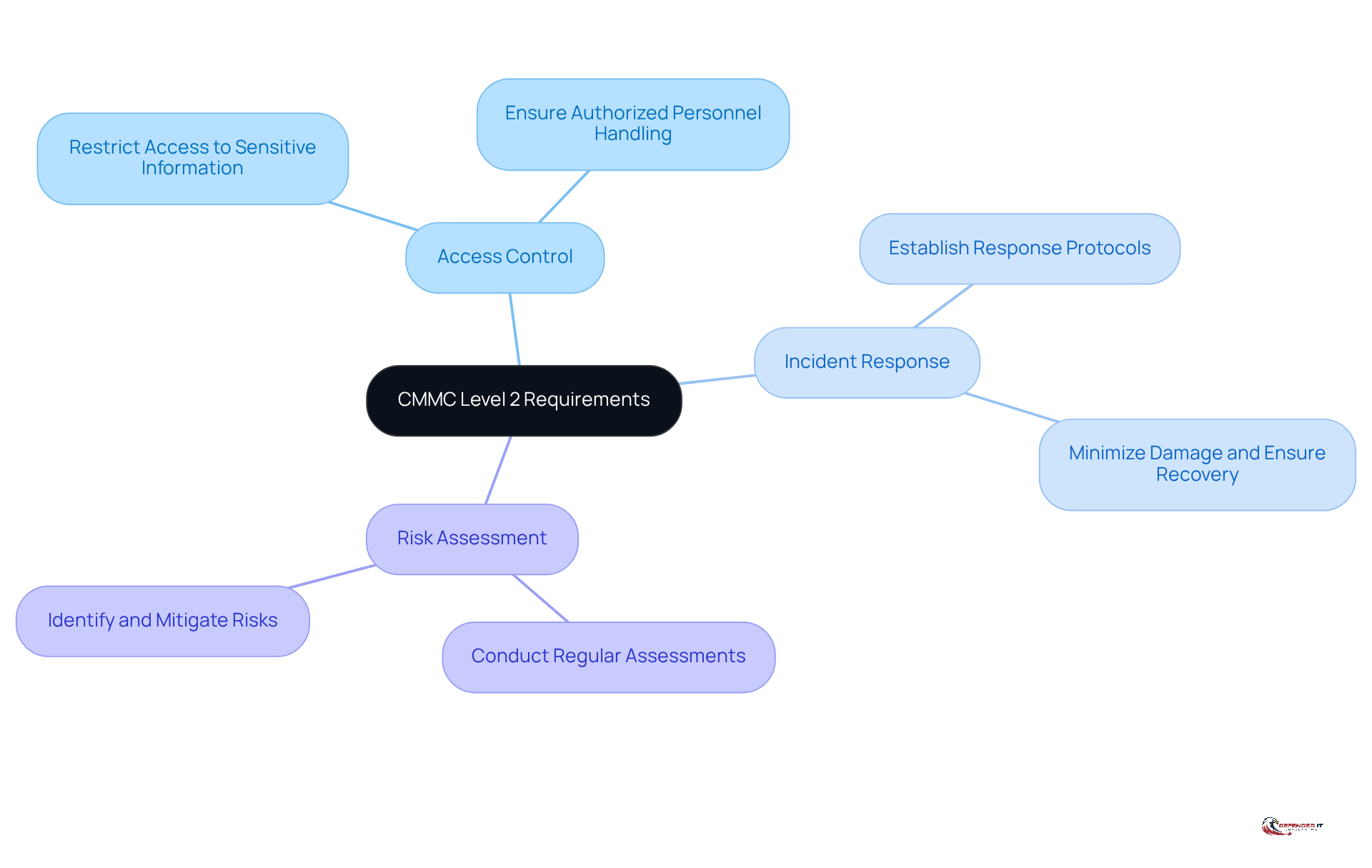
Understand CMMC Level 2 Requirements and Objectives
CMMC L2 adherence aims to enhance the cybersecurity posture of entities managing Controlled Unclassified Information (CUI). This framework includes 110 security controls derived from NIST SP 800-171, organized into 14 distinct domains. The primary objectives are as follows:
- Access Control: Implement measures to restrict access to sensitive information, ensuring that only authorized personnel can view or handle CUI.
- Incident Response: Establish protocols for responding to cybersecurity incidents, thereby minimizing potential damage and ensuring swift recovery.
- Risk Assessment: Conduct regular assessments to identify and mitigate risks, which is essential for maintaining a proactive security posture.
Organizations must grasp these requirements to formulate a robust adherence strategy, ensuring compliance with necessary standards for safeguarding sensitive information. As of February 2026, only 8% of defense contractors have achieved CMMC L2 certification, highlighting a significant demand for authorized C3PAO assessments prior to the November 2026 enforcement deadline. Furthermore, entities should prioritize ongoing oversight for adherence, as neglecting this aspect can lead to substantial financial repercussions, with non-adherence costs potentially reaching $14.82 million. Additionally, executing Plans of Action and Milestones (POA&Ms) is crucial for CMMC L2 compliance, as it aids entities in monitoring their progress and addressing any deficiencies effectively.
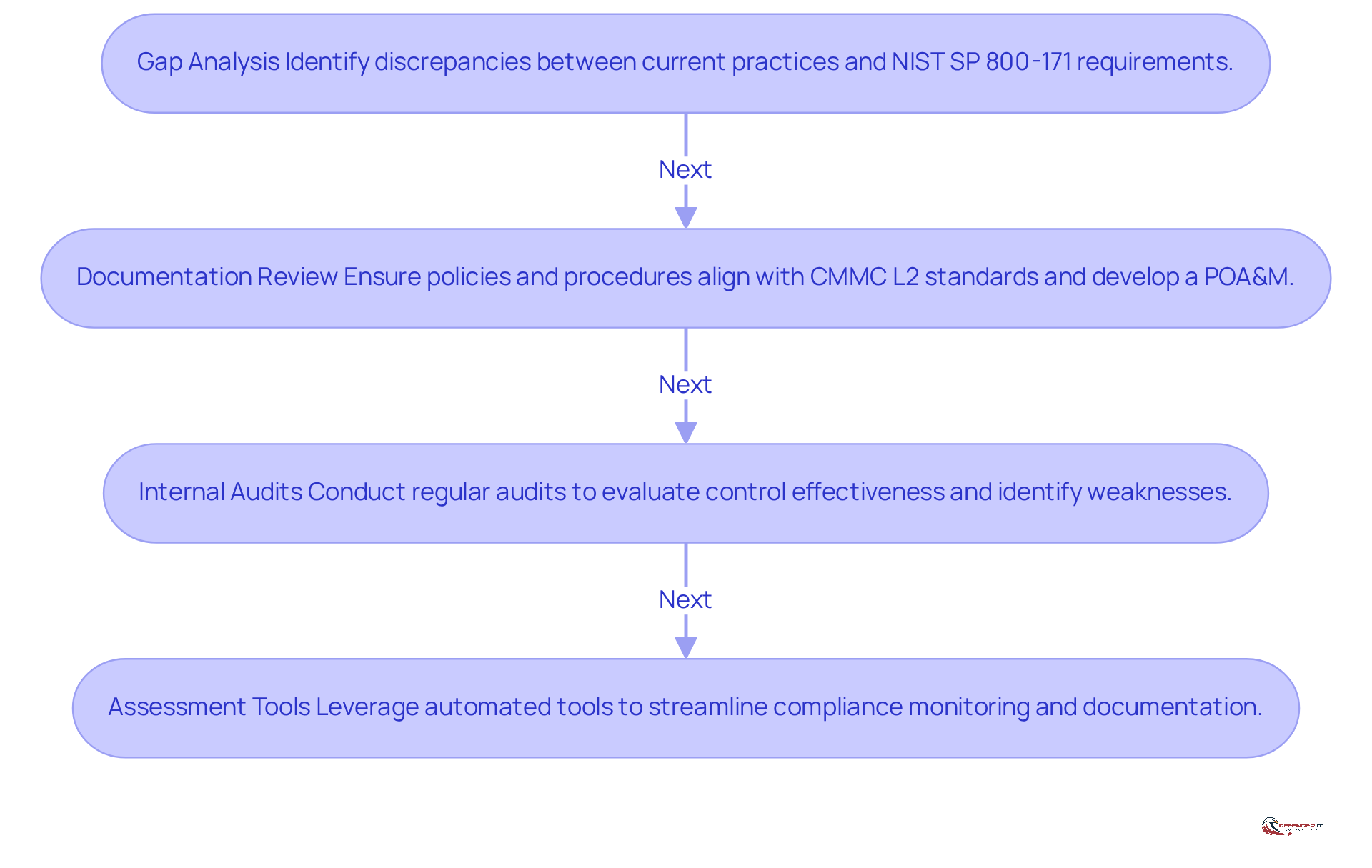
Implement Effective Assessment Criteria and Methodologies
To achieve CMMC Level 2 compliance, organizations must adopt a structured assessment approach that encompasses several key methodologies:
- Gap Analysis: Begin with a comprehensive gap analysis to identify discrepancies between current practices and the 110 requirements outlined in NIST SP 800-171 Rev 2. This analysis highlights areas needing immediate attention and provides a preliminary SPRS score, essential for understanding the regulatory landscape.
- Documentation Review: Ensure that all policies, procedures, and controls are meticulously documented and aligned with CMMC L2 standards. Develop a well-structured Plan of Action and Milestones (POA&M) to address identified gaps, detailing the specific finding, its root cause, the planned remediation approach, the responsible owner, and a realistic target date.
- Internal Audits: Conduct regular internal audits to evaluate the effectiveness of implemented controls and identify potential weaknesses. These audits should occur at least annually or whenever significant changes take place in the environment, viewing adherence as a continuous process rather than a one-time effort.
- Assessment Tools: Leverage automated assessment tools to streamline the regulatory process. These tools facilitate monitoring adherence progress and managing documentation, ensuring that organizations can maintain a strong security posture while effectively navigating the complexities of regulatory requirements.
By applying these methodologies, organizations can establish a clear plan for achieving regulatory standards and maintaining a robust cybersecurity framework, ultimately safeguarding their operations and reputation.
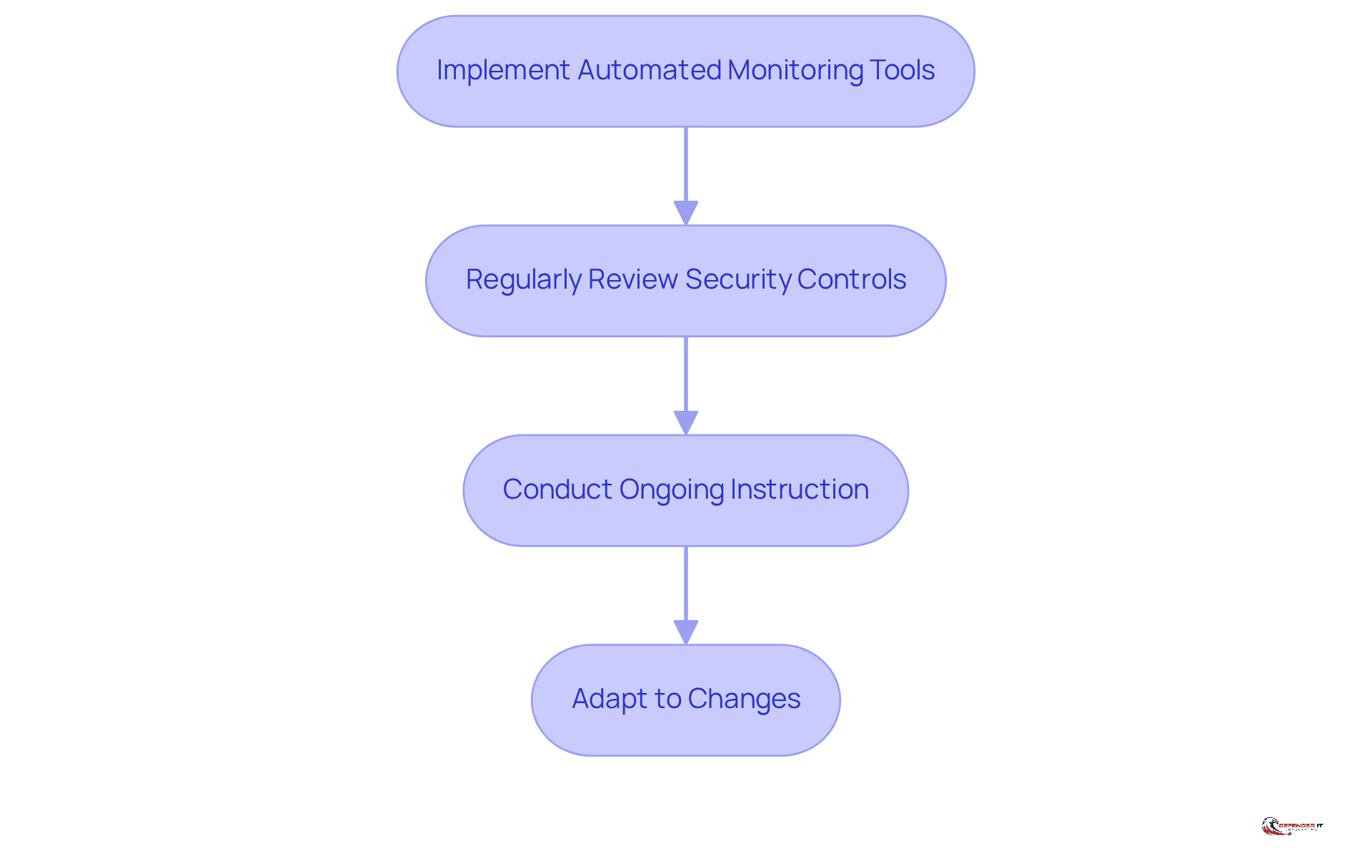
Establish Continuous Monitoring and Improvement Processes
Continuous monitoring is essential for maintaining CMMC L2 compliance. Organizations should take the following steps:
- Implement Automated Monitoring Tools: Utilize Security Information and Event Management (SIEM) systems to continuously monitor network activity and detect anomalies.
- Regularly Review Security Controls: Schedule periodic reviews of security controls to ensure they remain effective and relevant to current threats.
- Conduct Ongoing Instruction: Provide regular sessions for employees to keep them informed about the latest cybersecurity threats and best practices.
- Adapt to Changes: Be prepared to update policies and procedures in response to new threats or changes in regulatory requirements.
By establishing these processes, organizations can ensure compliance and enhance their resilience against cyber threats.
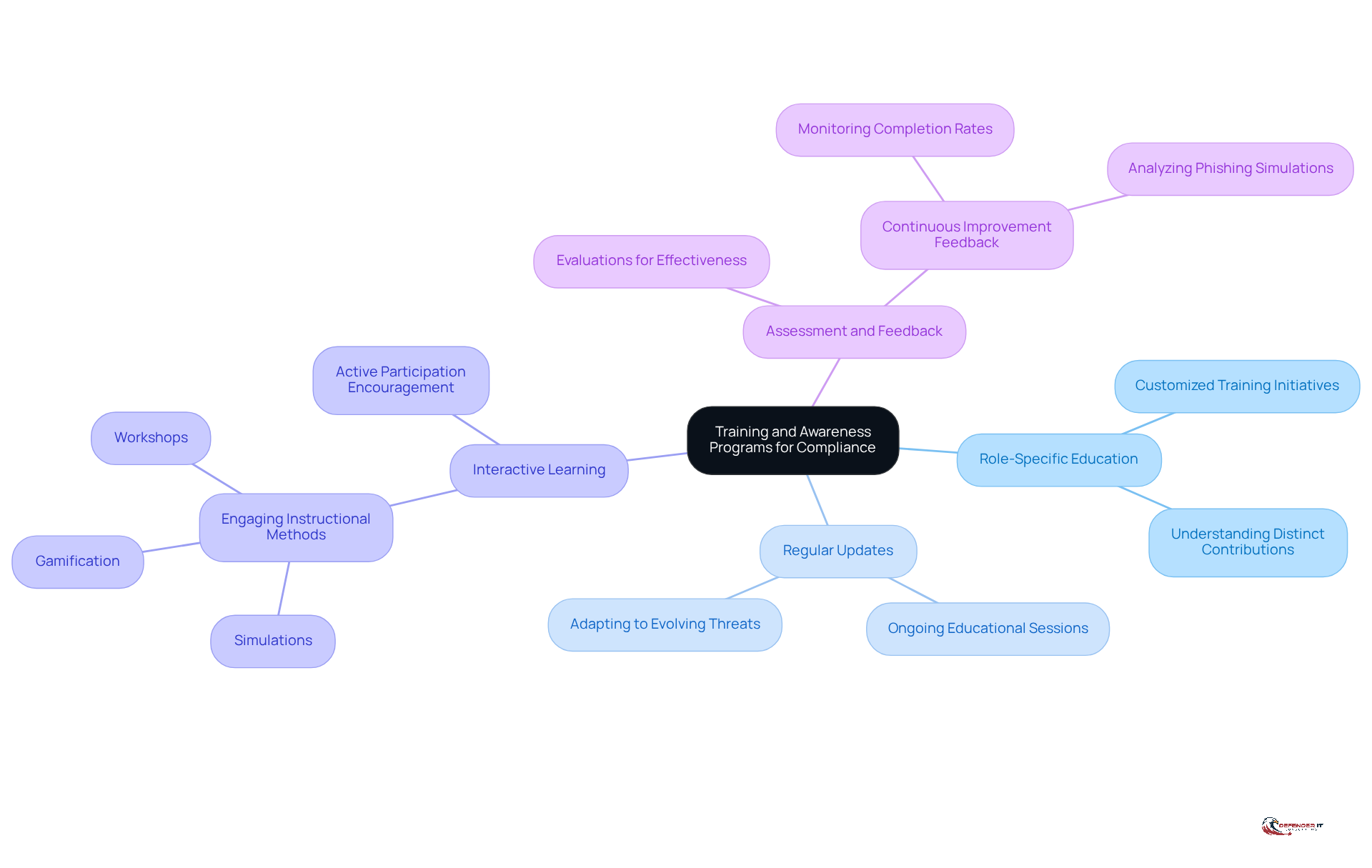
Develop Training and Awareness Programs for Compliance Personnel
To achieve compliance with CMMC Level 2, organizations must prioritize comprehensive training and awareness programs that encompass the following key elements:
- Role-Specific Education: Educational initiatives should be customized to align with the specific roles and responsibilities of employees. This approach ensures that each individual understands their distinct contributions to upholding regulations and mitigating cybersecurity risks.
- Regular Updates: Ongoing educational sessions are essential to keep staff informed about evolving compliance requirements and emerging cybersecurity threats. Regular updates are crucial for adapting to the dynamic nature of cyber risks and regulatory changes.
- Interactive Learning: Engaging instructional methods, such as simulations, gamification, and workshops, should be utilized to reinforce learning and encourage active participation. Interactive formats enhance retention and make the learning experience more relevant to employees’ daily tasks.
- Assessment and Feedback: Evaluations must be implemented to measure the effectiveness of development programs and gather feedback for continuous improvement. Monitoring completion rates and analyzing outcomes from phishing simulations can assist organizations in refining their instructional approaches and strengthening overall security awareness.
By emphasizing these training and awareness components, organizations can cultivate a knowledgeable workforce capable of upholding compliance with CMMC Level 2 and effectively responding to cybersecurity challenges.
Conclusion
Achieving CMMC Level 2 compliance is not just a regulatory obligation; it is a crucial step in enhancing the cybersecurity resilience of organizations that handle Controlled Unclassified Information (CUI). By comprehensively understanding the CMMC Level 2 requirements and implementing established best practices, businesses can effectively safeguard their sensitive data and mitigate associated risks.
This article outlines several best practices essential for achieving compliance. These include:
- A thorough understanding of CMMC Level 2 requirements
- Effective assessment methodologies
- Continuous monitoring processes
- The development of comprehensive training programs
Each component plays a vital role in establishing a robust cybersecurity framework that not only meets regulatory standards but also cultivates a culture of security awareness among employees.
As organizations navigate the complexities of CMMC Level 2 compliance, prioritizing these best practices is imperative. By doing so, they can protect themselves from potential cyber threats and position themselves as trustworthy partners within the defense contracting landscape. Embracing a proactive approach to compliance will ultimately lead to a more secure and resilient operational environment, ensuring that businesses are well-prepared to meet the challenges posed by the evolving cybersecurity landscape.
Frequently Asked Questions
What is the purpose of CMMC Level 2 adherence?
CMMC Level 2 adherence aims to enhance the cybersecurity posture of entities managing Controlled Unclassified Information (CUI) by implementing specific security controls.
How many security controls are included in CMMC Level 2, and where are they derived from?
CMMC Level 2 includes 110 security controls derived from NIST SP 800-171, organized into 14 distinct domains.
What are the primary objectives of CMMC Level 2?
The primary objectives of CMMC Level 2 include Access Control, Incident Response, and Risk Assessment.
What is the significance of Access Control in CMMC Level 2?
Access Control involves implementing measures to restrict access to sensitive information, ensuring that only authorized personnel can view or handle CUI.
Why is Incident Response important in CMMC Level 2?
Incident Response is crucial for establishing protocols to respond to cybersecurity incidents, minimizing potential damage, and ensuring swift recovery.
How does Risk Assessment contribute to CMMC Level 2 compliance?
Risk Assessment involves conducting regular assessments to identify and mitigate risks, which is essential for maintaining a proactive security posture.
What is the current status of CMMC Level 2 certification among defense contractors?
As of February 2026, only 8% of defense contractors have achieved CMMC Level 2 certification, indicating a significant demand for authorized C3PAO assessments before the November 2026 enforcement deadline.
What are the potential financial repercussions of non-adherence to CMMC Level 2?
Neglecting adherence to CMMC Level 2 can lead to substantial financial repercussions, with non-adherence costs potentially reaching $14.82 million.
What role do Plans of Action and Milestones (POA&Ms) play in CMMC Level 2 compliance?
POA&Ms are crucial for monitoring progress and addressing deficiencies effectively, aiding entities in achieving CMMC Level 2 compliance.
List of Sources
- Understand CMMC Level 2 Requirements and Objectives
- CMMC 2.0 Level 2 & NIST 800-171 Compliant | Manufacturo (https://manufacturo.com/resources/pr-news/manufacturo-achieves-cmmc-20-level-2-compliance-aligned-with-nist-800-171)
- CMMC 2.0 in 2026: What Defense Contractors Must Do Now (https://trustconsultingservices.com/cmmc-2-0-in-2026-defense-compliance-guide)
- Over 300k businesses impacted by CMMC 2.0 enforcement: Here’s what MSPs need to know | ScalePad CMMC 2.0 Enforcement (https://scalepad.com/blog/cmmc-enforcement-for-msps)
- CIO – About CMMC (https://dodcio.defense.gov/cmmc/About)
- Cybersecurity Compliance Statistics: Federal Contractor Data Hub 2025-2026 – IBSSCORP (https://ibsscorp.com/cybersecurity-compliance-statistics-federal-contractor-data-hub-2025-2026)
- Implement Effective Assessment Criteria and Methodologies
- CMMC Level 2 Gap Analysis: How to Prepare for Your Assessment (https://secureframe.com/blog/cmmc-gap-analysis)
- Assessing Cybersecurity Under CMMC: The First Step on the Path to Compliance (https://cybersheath.com/resources/blog/assessing-cybersecurity-under-cmmc-the-first-step-on-the-path-to-compliance)
- Your Step-by-Step CMMC Level 2 Checklist for 2026 (https://redriver.com/security/your-step-by-step-cmmc-level-2-checklist-for-2026)
- What’s It Really Like to Go Through a CMMC Assessment? (https://mxdusa.org/news/whats-it-really-like-to-go-through-a-cmmc-assessment)
- CMMC 2.0 in 2026: What Defense Contractors Must Do Now (https://trustconsultingservices.com/cmmc-2-0-in-2026-defense-compliance-guide)
- Establish Continuous Monitoring and Improvement Processes
- CMMC 2.0 in 2026: What Defense Contractors Must Do Now (https://trustconsultingservices.com/cmmc-2-0-in-2026-defense-compliance-guide)
- AI and Cybersecurity: Latest Stats on AI-Driven Threat Detection and Attacks (https://patentpc.com/blog/ai-and-cybersecurity-latest-stats-on-ai-driven-threat-detection-and-attacks)
- Top 10 SIEM Tools For 2026 (https://sentinelone.com/cybersecurity-101/data-and-ai/siem-tools)
- Security Information and Event Management (SIEM) (https://infosecurity-magazine.com/security-information-and-event-management-(siem))
- SIEM — Latest News, Reports & Analysis | The Hacker News (https://thehackernews.com/search/label/SIEM)
- Develop Training and Awareness Programs for Compliance Personnel
- Federal News Network’s Risk & Compliance Exchange 2026 | Federal News Network (https://federalnewsnetwork.com/cme-event/exchanges/federal-news-networks-risk-compliance-exchange-2026)
- How To Use Role-Based Security Awareness Training (https://securitycompass.com/kontra/role-based-security-awareness-training)
- ISACA Now Blog 2026 CMMC Program Provides New Career Pathways for ISACA Members (https://isaca.org/resources/news-and-trends/isaca-now-blog/2026/cmmc-program-provides-new-career-pathways-for-isaca-members)
- Best Practices for Security Awareness Training Programs | Huntress (https://huntress.com/cybersecurity-training-guide/best-practices-for-effective-security-awareness-training-programs)
- CMMC Phase 2: What to Expect and How to Prepare [2026] (https://secureframe.com/blog/cmmc-phase-2-preparation)