Introduction
Mastering enterprise risk management in IT security is essential as organizations face a complex digital landscape rife with cyber threats. This guide presents a systematic approach to identifying, assessing, and managing risks that could jeopardize digital assets and overall business objectives. Given the rapid evolution of cyber threats, organizations must ensure their risk management strategies are both effective and relevant. This guide outlines critical steps and best practices for developing a robust framework that not only protects against current vulnerabilities but also adapts to future challenges.
Define Enterprise Risk Management in the Context of IT Security
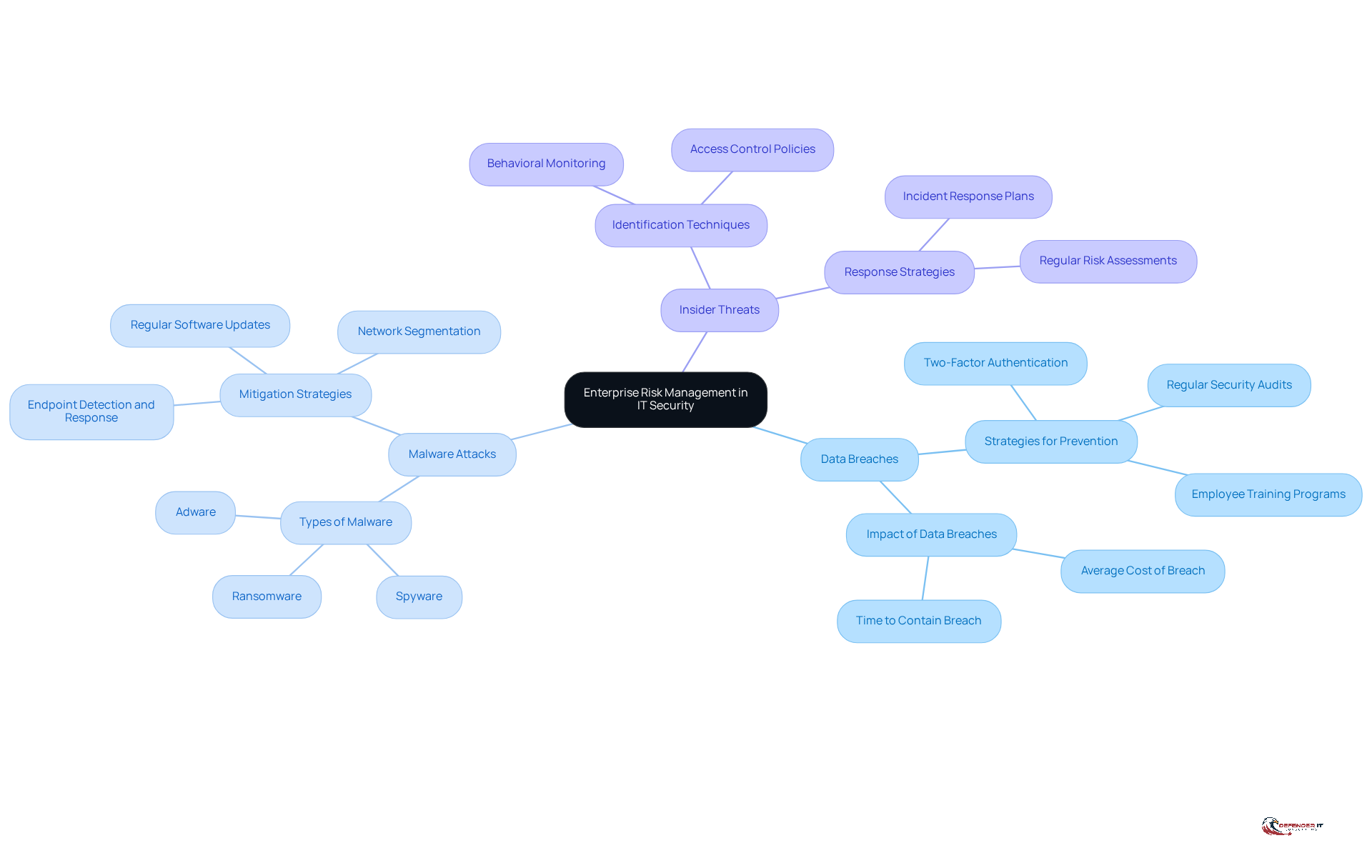
Enterprise Risk Management (ERM) is a systematic approach to identifying, evaluating, and managing uncertainties that may affect a company’s ability to achieve its objectives. In the context of , the processes and strategies organizations implement are aimed at protecting their from . This includes understanding the various types of risks that can impact IT systems, such as:
By integrating cybersecurity into the enterprise risk management IT security framework, organizations can ensure that their are . This foundational understanding is crucial for developing effective strategies that tackle the .
Identify and Assess IT Security Risks
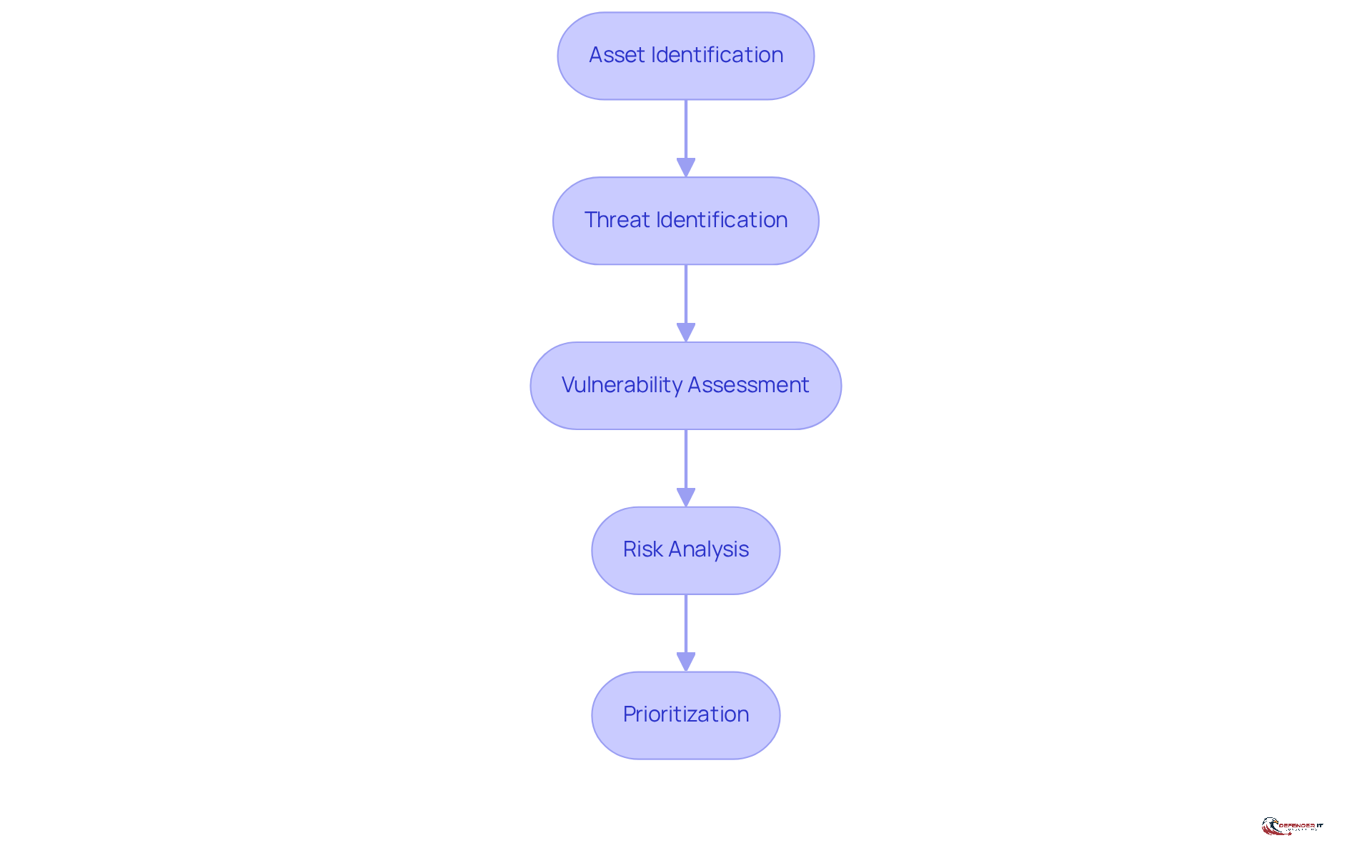
To effectively manage IT security risks, organizations must first identify and assess potential threats through a structured approach that includes several key steps:
- Asset Identification: Catalog all critical IT assets, including hardware, software, and data. Understanding what requires safeguarding is essential in handling uncertainties. In 2026, organizations increasingly recognize that is crucial, as 64% of cybersecurity leaders evaluate the security of AI tools prior to deployment, underscoring the necessity for comprehensive asset management.
- Threat Identification: Identify potential threats to these assets, such as , natural disasters, or insider threats. The evolving threat landscape indicates that adversaries exploit vulnerabilities in identity, cloud, and virtual environments, necessitating a thorough examination of both external and internal sources of risk.
- : Evaluate the vulnerabilities associated with each asset. This includes identifying outdated software, weak passwords, or lack of encryption. The indicates a 42% rise in zero-day vulnerabilities exploited before public disclosure, highlighting the urgency for companies to enhance their defenses against undisclosed weaknesses.
- : Assess the likelihood and potential impact of each identified threat exploiting a vulnerability. This can be accomplished using qualitative or quantitative methods. With rising fourfold since 2021, organizations must prioritize understanding the potential financial and operational effects of these threats.
- Prioritization: Rank the threats based on their potential effect on the organization’s operations and goals. This prioritization will guide the development of the hazard control strategy. As businesses face an average cost of $3.48 million per data breach in the retail sector, effective prioritization is crucial for allocating resources efficiently.
By adhering to these steps, organizations can achieve a thorough understanding of their enterprise risk management IT security environment, which enables informed decisions regarding threat mitigation and enhances their overall cybersecurity posture.
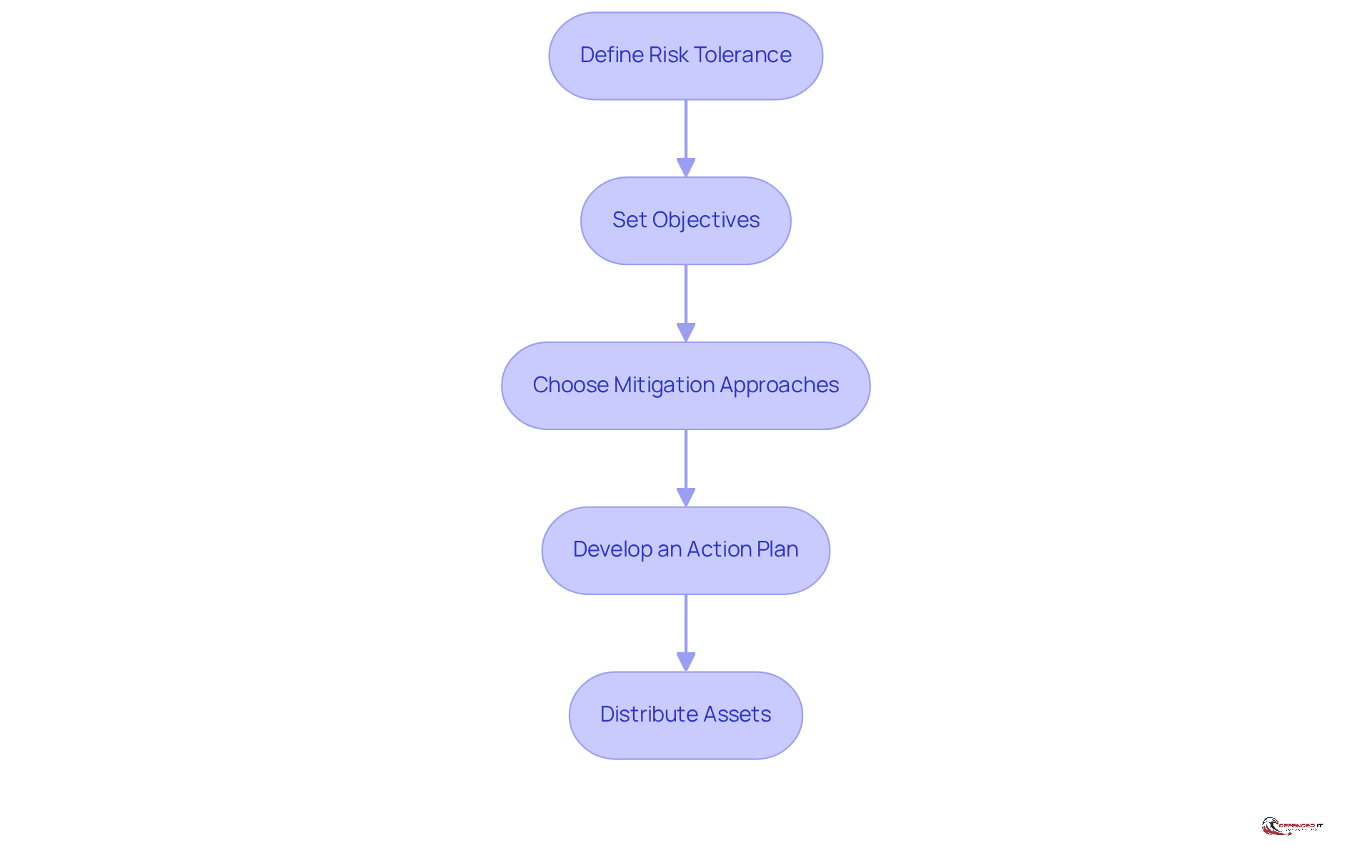
Develop a Tailored Risk Management Strategy
Once hazards have been identified and evaluated, the next step is to create a customized management plan that aligns with the entity’s overall business goals and tolerance for uncertainty. This structured approach is essential for effectively addressing the challenges of IT security.
- : Determine the degree of uncertainty the entity is prepared to accept. This assessment will guide decision-making and resource allocation effectively.
- Set Objectives: Clearly define the goals of the . These objectives should align with the organization’s mission and address the identified challenges directly.
- : Select appropriate measures for each identified hazard. This may include implementing , conducting employee training, or investing in technology solutions.
- : Create a detailed action plan that outlines the necessary steps to execute the chosen approaches, including timelines and responsible parties.
- Distribute Assets: Ensure that adequate resources, including budget and personnel, are allocated to support the execution of the threat handling plan.
By following these steps, organizations can develop a comprehensive strategy for to effectively manage their unique .
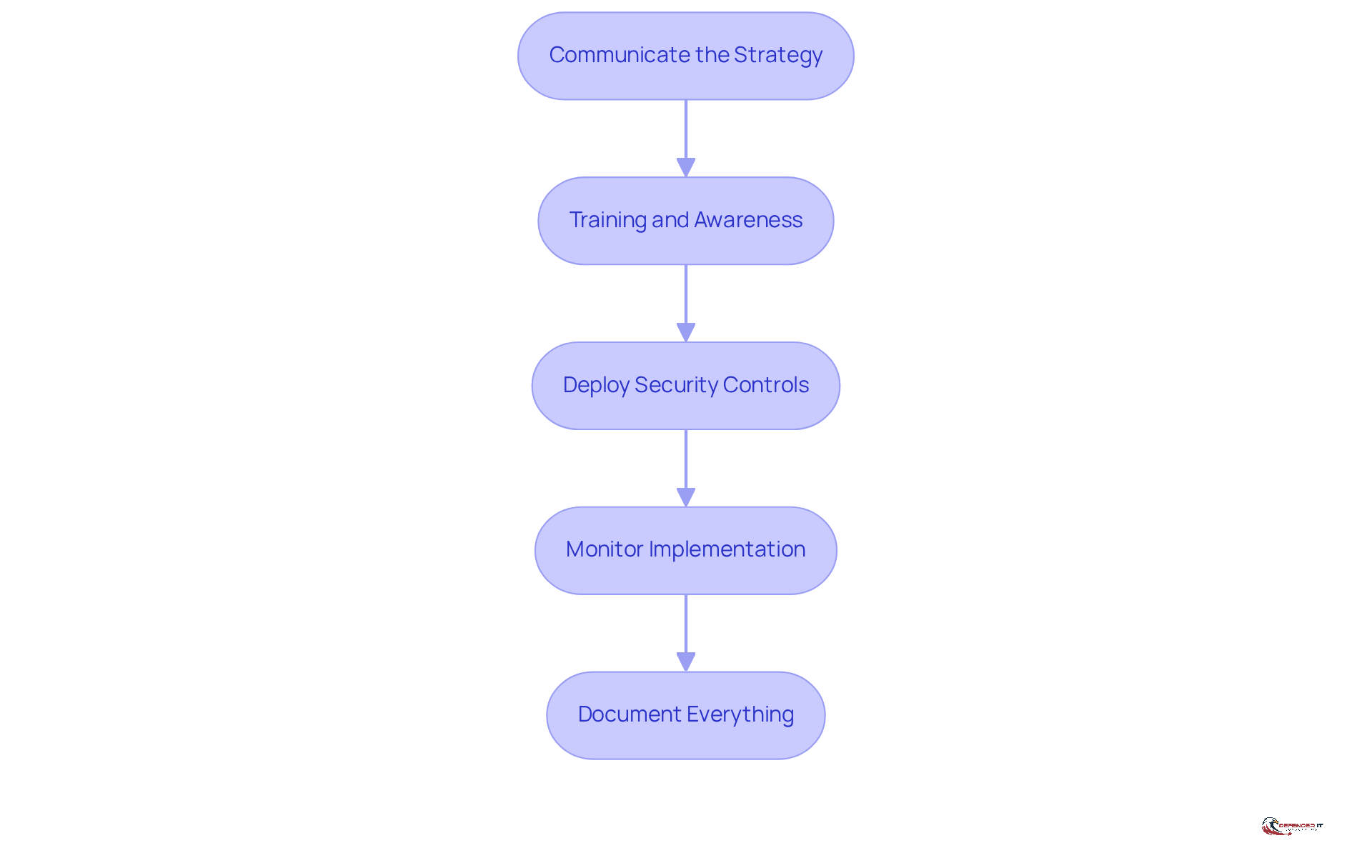
Implement the Risk Management Strategy
Implementing a robust involves several critical steps to ensure its effectiveness:
- Communicate the Strategy: Clearly articulate the management approach to all stakeholders, including employees, management, and relevant partners. It is essential that everyone understands their roles and responsibilities in to effectively maintain cybersecurity.
- Training and Awareness: Conduct sessions to enhance awareness of and the measures being implemented. This not only informs employees but also promotes a culture of enterprise risk management IT security within the company. Research indicates that entities participating in regular experience a remarkable , underscoring the value of continuous education. Additionally, companies can receive when they prove they train employees regularly, highlighting the financial benefits of such training.
- Deploy : Implement the selected security controls and measures as outlined in the action plan. This may involve deploying software, hardware, or procedural changes tailored to the entity’s specific needs. Modern platforms should cover multiple attack channels, including phishing and deepfake threats, to ensure comprehensive protection. Notably, fewer than 20% of organizations provide training to recognize voice phishing or deepfakes, emphasizing the need for comprehensive training.
- Monitor Implementation: Continuously process to ensure it aligns with the established plan. Address any issues or obstacles that arise promptly to maintain momentum and effectiveness.
- Document Everything: Keep thorough records of the implementation process, including decisions made, alterations to the plan, and challenges faced. This documentation is essential for future evaluations and audits, offering insights into the efficiency of the approach.
By adhering to these steps, entities can efficiently execute their threat mitigation plans within the framework of enterprise risk management IT security, ensuring they are well-prepared to address potential cybersecurity dangers. Engaging employees as the first line of defense and promoting a positive cybersecurity culture are crucial for long-term success.
Monitor and Review the Risk Management Strategy
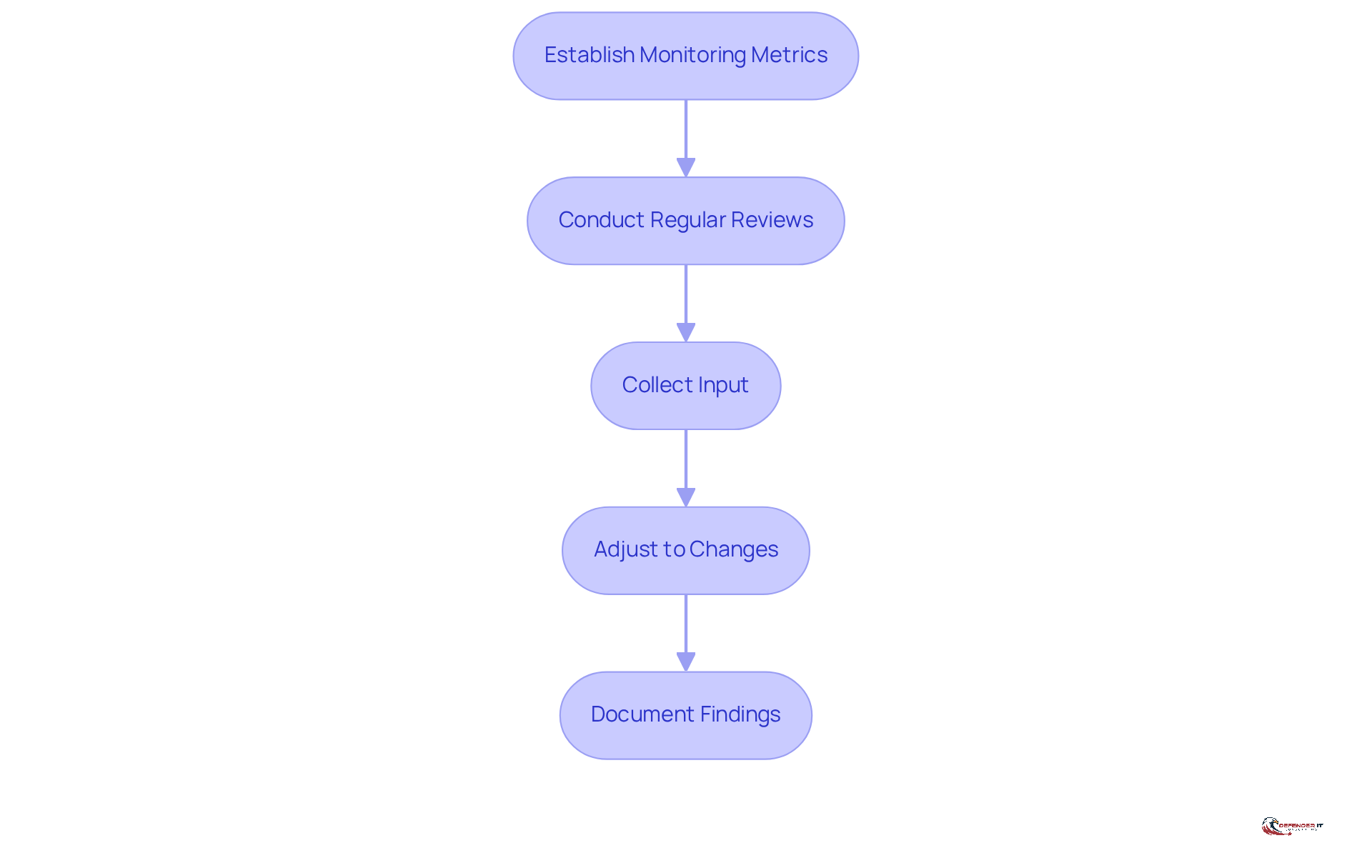
To ensure the ongoing efficiency of the threat control approach, organizations must establish a robust . This process is critical for adapting to the evolving .
- Establish Monitoring Metrics: Organizations should define that assess the effectiveness of their hazard supervision strategy. These metrics must align with the organization’s objectives and risk tolerance. Common KPIs include incident detection and response times, patch update frequencies, and the percentage of systems running current software.
- Conduct Regular Reviews: It is essential to schedule frequent evaluations of the to determine its effectiveness and relevance. This involves assessing the efficacy of implemented controls and identifying new threats, such as the rise of that have already exposed over 1,800 API keys, credentials, and histories.
- Collect Input: Gathering feedback from , is vital for understanding the approach’s effectiveness and identifying areas for improvement. Engaging non-technical stakeholders can significantly enhance the overall security posture.
- Adjust to Changes: Organizations must be ready to modify their management strategies in response to changes in the threat landscape, business objectives, or regulatory requirements. Recognizing scams and fraud as critical cyber threats is essential in 2026, as cybersecurity strategies must treat these issues as primary hazards, reflecting the integration of deception into standard business operations.
- Document Findings: Maintaining , assessments, and any adjustments made to the approach is crucial. This documentation supports accountability and serves as a reference for future actions. Notably, the rose from $16.2 million in 2023 to $17.4 million in 2024 for each organization, underscoring the financial implications of insufficient mitigation strategies.
By implementing a strong monitoring and review process, organizations can ensure that their remain effective and responsive to the ever-evolving challenges in cybersecurity.
Conclusion
Mastering enterprise risk management in IT security is crucial for organizations that seek to protect their digital assets and ensure operational continuity. By systematically identifying, assessing, and managing risks, businesses can safeguard against cyber threats while aligning their security strategies with overarching business objectives. This comprehensive approach is essential in today’s rapidly evolving digital landscape, where vulnerabilities can emerge unexpectedly and lead to significant repercussions.
Key steps for effective enterprise risk management in IT security include:
- Defining risk tolerance
- Identifying critical assets
- Assessing potential threats
- Developing tailored risk management strategies
- Implementing robust monitoring processes
Each step builds upon the previous one, creating a cohesive framework that enhances an organization’s cybersecurity posture. Continuous training and stakeholder engagement are also emphasized, as these elements significantly contribute to fostering a culture of security awareness.
The significance of this structured approach cannot be overstated. As cyber threats continue to evolve, organizations must remain vigilant and proactive in their risk management efforts. By adopting these best practices, businesses can mitigate potential risks and position themselves to thrive in an increasingly complex digital environment. Embracing enterprise risk management in IT security is not merely a defensive strategy; it represents a critical investment in the future resilience and success of any organization.
Frequently Asked Questions
What is Enterprise Risk Management (ERM) in the context of IT security?
Enterprise Risk Management (ERM) is a systematic approach to identifying, evaluating, and managing uncertainties that may affect a company’s ability to achieve its objectives, particularly in protecting digital assets from cyber threats.
What types of risks are addressed in IT security within ERM?
The types of risks addressed include data breaches, malware attacks, and insider threats.
Why is integrating cybersecurity into ERM important?
Integrating cybersecurity into ERM ensures that strategies for addressing vulnerabilities are comprehensive and aligned with the organization’s overall business goals, which is crucial for tackling challenges in the digital landscape.
What are the key steps to identify and assess IT security risks?
The key steps include: 1. Asset Identification: Cataloging all critical IT assets. 2. Threat Identification: Identifying potential threats to these assets. 3. Vulnerability Assessment: Evaluating vulnerabilities associated with each asset. 4. Risk Analysis: Assessing the likelihood and potential impact of threats exploiting vulnerabilities. 5. Prioritization: Ranking threats based on their potential effect on operations and goals.
How does asset identification contribute to IT security risk management?
Asset identification helps organizations understand what requires safeguarding, which is essential for effectively managing uncertainties and protecting critical IT assets.
What is the significance of threat identification in the risk management process?
Threat identification allows organizations to recognize potential threats, including cyber attacks and natural disasters, which is vital for a comprehensive understanding of both external and internal sources of risk.
Why is vulnerability assessment important?
Vulnerability assessment is important because it helps identify weaknesses such as outdated software or weak passwords, enabling organizations to enhance their defenses against potential threats.
How is risk analysis conducted in the context of IT security?
Risk analysis can be conducted using qualitative or quantitative methods to assess the likelihood and potential impact of identified threats exploiting vulnerabilities.
What role does prioritization play in managing IT security risks?
Prioritization helps rank threats based on their potential impact on the organization’s operations and goals, guiding the development of an effective hazard control strategy and resource allocation.
What are the financial implications of data breaches in the retail sector?
The average cost of a data breach in the retail sector is approximately $3.48 million, highlighting the importance of effective prioritization in risk management.
List of Sources
- Define Enterprise Risk Management in the Context of IT Security
- Cyber threats to watch in 2026 – and other cybersecurity news (https://weforum.org/stories/2026/02/2026-cyberthreats-to-watch-and-other-cybersecurity-news)
- 50+ Risk Management Statistics to Know in 2026 (https://secureframe.com/blog/risk-management-statistics)
- Key Cyber Security Statistics for 2026 (https://sentinelone.com/cybersecurity-101/cybersecurity/cyber-security-statistics)
- 2026 Cyber Risk Management Strategies To Adopt Now (https://forbes.com/councils/forbestechcouncil/2026/03/02/2026-cyber-risk-management-strategies-to-adopt-now)
- Enterprise Risk Management News – Risk & Compliance Journal – WSJ (https://deloitte.wsj.com/riskandcompliance/tag/enterprise_risk_management?gaa_at=eafs&gaa_n=AWEtsqeWY1rYdJv-E1aTdZVtzdXUy0fpDeHeBpjIZiFUbDLnz92LkPLNFeaB&gaa_ts=69d05920&gaa_sig=nNDWgC6hPXAL2b44C0-FcsLdwnTcwH7VbZJ2wp4bUp2iemKagF2HRokIB5jwGTxfnTqeegb1hCSCtUP09fbIeA%3D%3D)
- Identify and Assess IT Security Risks
- Cyber threats to watch in 2026 – and other cybersecurity news (https://weforum.org/stories/2026/02/2026-cyberthreats-to-watch-and-other-cybersecurity-news)
- 2026 Global Threat Report | Latest Cybersecurity Trends & Insights | CrowdStrike (https://crowdstrike.com/en-us/global-threat-report)
- 205 Cybersecurity Stats and Facts for 2026 (https://vikingcloud.com/blog/cybersecurity-statistics)
- 2026 Cyber Risk Management Strategies To Adopt Now (https://forbes.com/councils/forbestechcouncil/2026/03/02/2026-cyber-risk-management-strategies-to-adopt-now)
- Risk Intelligence security lessons from 2025 that will shape 2026 (https://securitas.com/en/newsroom/blog/the-top-5-emerging-security-threats-and-risks-for-2026)
- Develop a Tailored Risk Management Strategy
- Industry News 2026 The 6 Cybersecurity Trends That Will Shape 2026 (https://isaca.org/resources/news-and-trends/industry-news/2026/the-6-cybersecurity-trends-that-will-shape-2026)
- 50+ Risk Management Statistics to Know in 2026 (https://secureframe.com/blog/risk-management-statistics)
- 205 Cybersecurity Stats and Facts for 2026 (https://vikingcloud.com/blog/cybersecurity-statistics)
- Cybersecurity Trends 2026 | IBM (https://ibm.com/think/insights/more-2026-cyberthreat-trends)
- Preparing for looming national cyber security threats in 2026 and beyond | Federal News Network (https://federalnewsnetwork.com/commentary/2026/01/preparing-for-looming-national-cyber-security-threats-in-2026-and-beyond)
- Implement the Risk Management Strategy
- How Cybersecurity Training Lowers Risk Among Employees (https://forbes.com/councils/forbestechcouncil/2023/10/24/how-cybersecurity-training-lowers-risk-among-employees)
- [Updated 2026] Security Awareness Training Statistics – Keepnet (https://keepnetlabs.com/blog/security-awareness-training-statistics)
- Security Awareness Training Statistics 2025 [100+ Studies] | Brightside AI Blog (https://brside.com/blog/security-awareness-training-statistics-2025-100-studies)
- Fortinet Report Finds Nearly 70% of Organizations Say Their Employees Lack Fundamental Security Awareness (https://fortinet.com/corporate/about-us/newsroom/press-releases/2024/fortinet-report-finds-70-percent-of-organizations-lack-fundamental-security-awareness-for-employees)
- Cyber Risk Management Statistics 2025-2026 (https://c-risk.com/statistics)
- Monitor and Review the Risk Management Strategy
- The top 20 expert quotes from the Cyber Risk Virtual Summit (https://diligent.com/resources/blog/top-20-quotes-cyber-risk-virtual-summit)
- 2026 Cyber Risk Management Strategies To Adopt Now (https://forbes.com/councils/forbestechcouncil/2026/03/02/2026-cyber-risk-management-strategies-to-adopt-now)
- Common Cybersecurity Metrics: Key KPIs to Measure | Kiuwan (https://kiuwan.com/blog/common-cybersecurity-metrics-key-kpis-to-measure)