Introduction
The rising number of cybersecurity incidents impacting contractors underscores the vital necessity of NIST 800-171 compliance for organizations managing Controlled Unclassified Information (CUI). This framework, developed by the National Institute of Standards and Technology, offers a systematic approach to protecting sensitive data and ensuring operational integrity, especially for those engaged in federal contracts. However, achieving compliance can be a formidable challenge. This raises an important question: what essential steps must organizations undertake not only to fulfill these requirements but also to bolster their cybersecurity posture in an increasingly complex threat landscape?
Understand NIST 800-171 Compliance
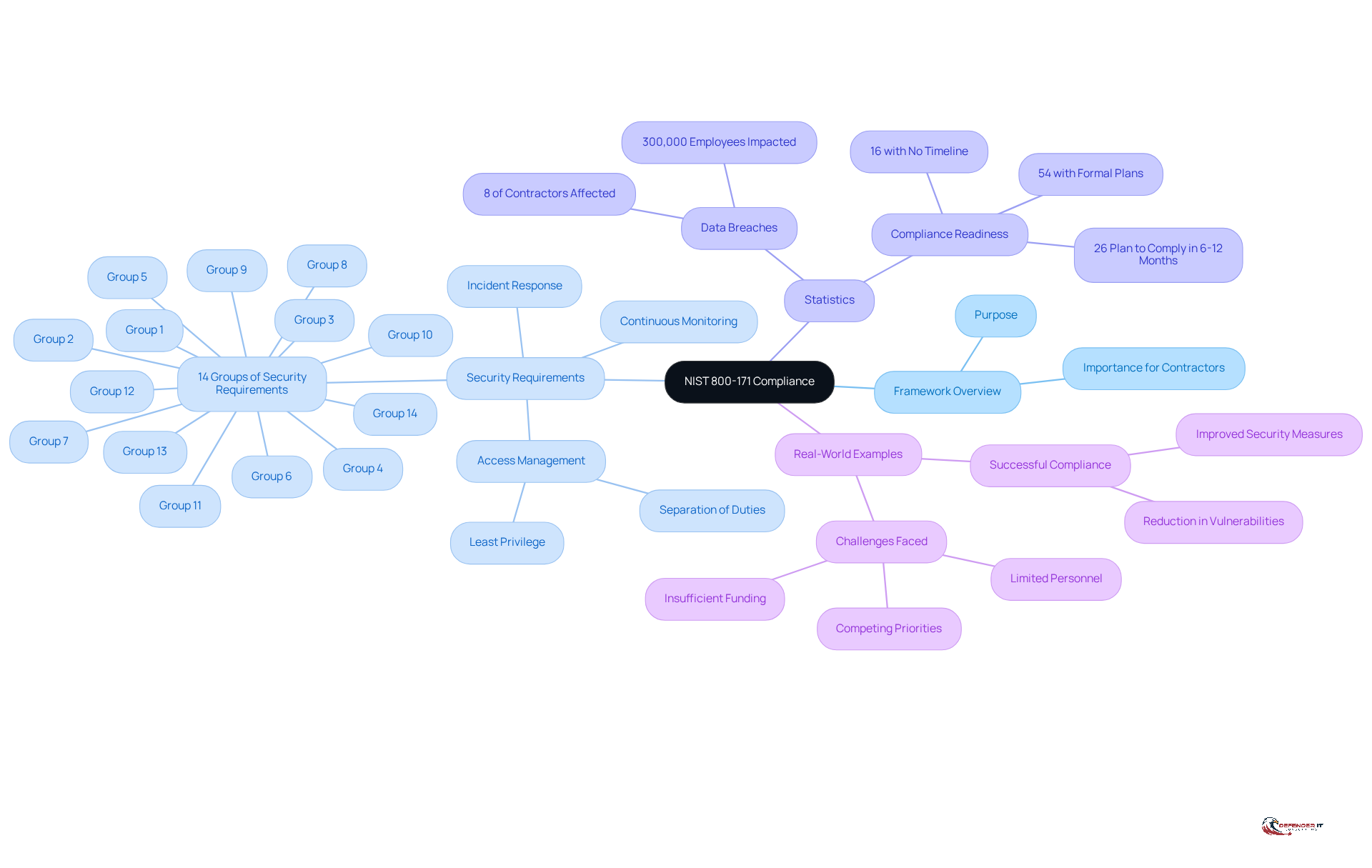
The framework known as nist-800-171, established by the National Institute of Standards and Technology (NIST), is vital for protecting (CUI) within non-federal systems. For organizations handling sensitive information, especially those engaged in federal contracts, compliance with this standard is essential. The framework comprises 14 groups of security requirements, encompassing 110 specific measures that organizations must implement to effectively safeguard CUI.
The significance of is highlighted by the rising number of cybersecurity incidents impacting contractors. Since 2016, around 8% of commercial contractors have reported data breaches, affecting nearly 300,000 employees. These breaches underscore the urgent need for , as noncompliance can result in severe consequences, including disqualification from contracts and potential breaches of contract.
Key elements of the nist-800-171 framework include:
- Continuous monitoring
mandates that organizations restrict access to CUI to authorized individuals only, employing principles such as ‘least privilege’ and ‘separation of duties.’ Regular system evaluations and the implementation of protective measures are crucial for maintaining compliance and enhancing overall cybersecurity posture.
Real-world examples demonstrate the framework’s effectiveness. Organizations that have successfully adopted the often report improved security measures and a reduction in vulnerabilities. For instance:
- 54% of institutions have developed formal plans for compliance
- 44% have not, revealing a notable disparity in preparedness
- 62% prioritize investing in cybersecurity tools as a strategy to fulfill these requirements
In conclusion, achieving compliance with NIST 800-171 is a fundamental step for organizations to protect sensitive information and mitigate risks associated with . As the federal contracting landscape evolves, adherence to this framework will become increasingly critical for maintaining operational integrity and securing business opportunities.
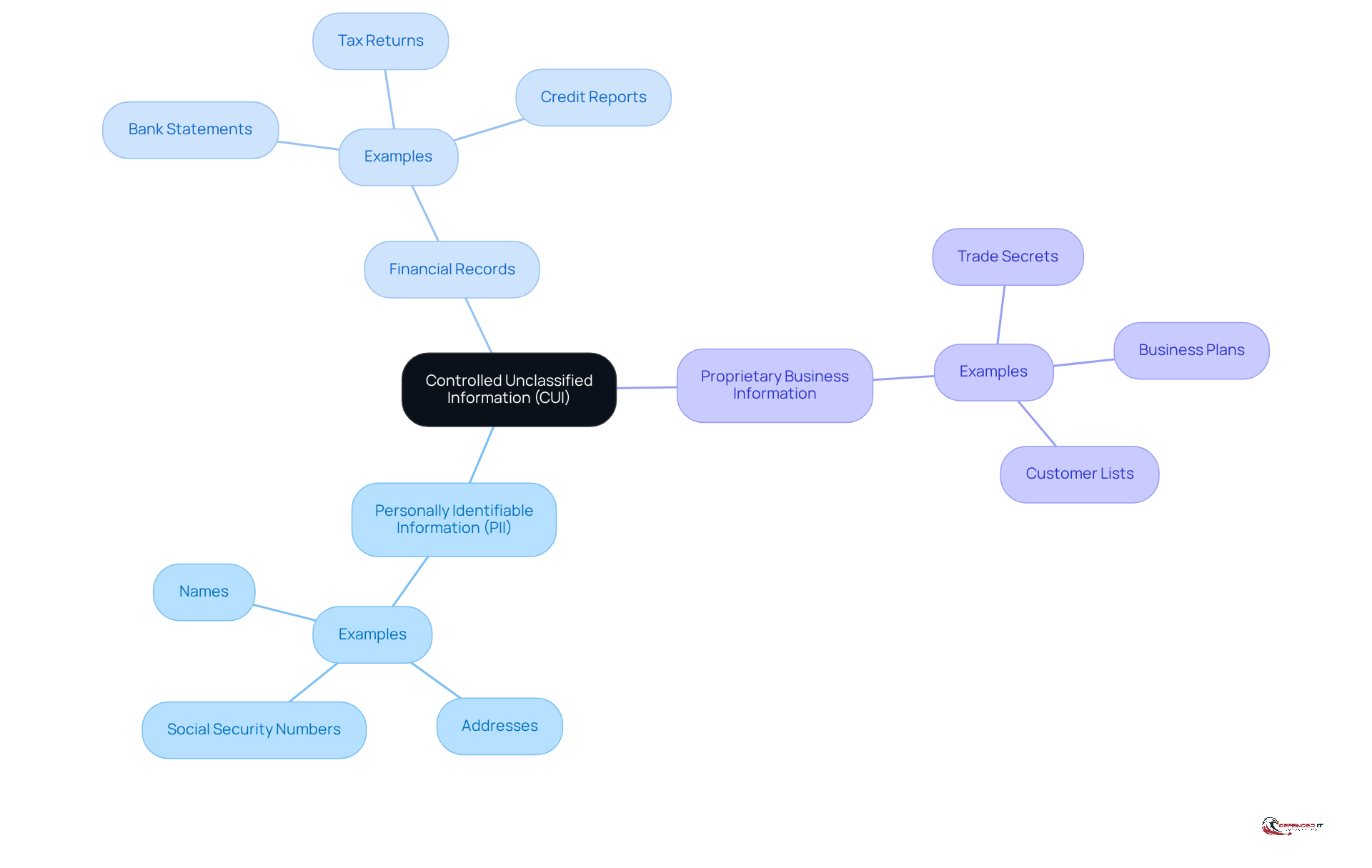
Identify Controlled Unclassified Information (CUI)
To achieve compliance with , entities must first accurately identify what constitutes (CUI). CUI includes sensitive data that requires protection but does not meet the criteria for classified status. Examples of CUI encompass:
Organizations are encouraged to refer to the , which provides a comprehensive list of CUI categories and subcategories, including recent updates for 2026 that align with the . This identification process is essential, as it lays the groundwork for subsequent steps in the compliance journey with , ensuring that entities can effectively safeguard their and adhere to regulatory mandates. In light of the , which was released without a formal comment period, it is imperative for entities to act promptly to align their practices with these new standards, reflecting the broader federal trend towards enforceable cybersecurity measures for contractors.
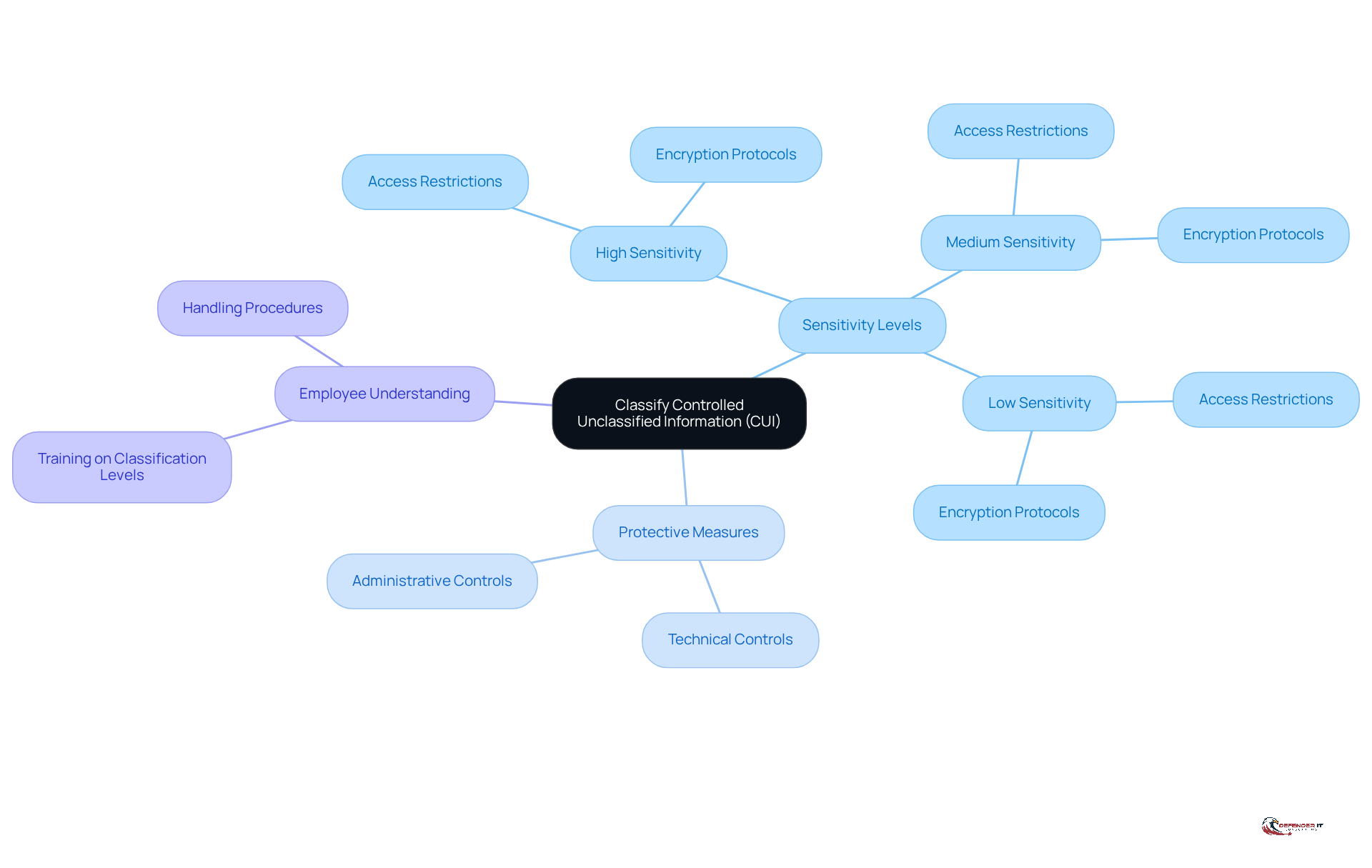
Classify Controlled Unclassified Information (CUI)
Once CUI has been identified, organizations must classify it according to its sensitivity and the . This classification is crucial as it helps in determining the to implement. For instance, may require more stringent access restrictions and encryption protocols.
Organizations should establish a and regulatory requirements. It is essential that all and the corresponding across the organization.
Perform a Security Assessment
A thorough security evaluation is essential for identifying vulnerabilities and assessing the effectiveness of existing security measures. Organizations should perform a . This process involves reviewing current policies, procedures, and technical measures to pinpoint compliance gaps. Utilizing evaluation tools and frameworks can streamline this process, providing a clear perspective on the organization’s and areas requiring remediation.
Recent statistics reveal that a significant 83% of companies have not established and enforced necessary security configuration settings, highlighting the critical role of self-assessments in uncovering such deficiencies. Furthermore, only 39% of defense contractors have implemented the required , underscoring an urgent need for .
Organizations, including universities, have demonstrated notable awareness and resource allocation towards adhering to nist-800-171, positioning them among the most secure entities evaluated. This underscores the in fostering a culture of compliance and safety.
emphasize the value of self-evaluation tools, noting that they not only facilitate adherence but also enhance overall resilience. Cheng Lim, a partner at King & Wood Mallesons, asserts, “Regulators expect businesses to demonstrate not just compliance, but a proactive approach to managing cyber risk. GCs are key to making that case.” By leveraging these tools, organizations can translate complex safety requirements into actionable insights, ensuring they meet regulatory expectations and protect sensitive information effectively.
In conclusion, a structured is not merely a regulatory requirement; it is a strategic imperative that enables organizations to manage cyber risks proactively and maintain a robust .
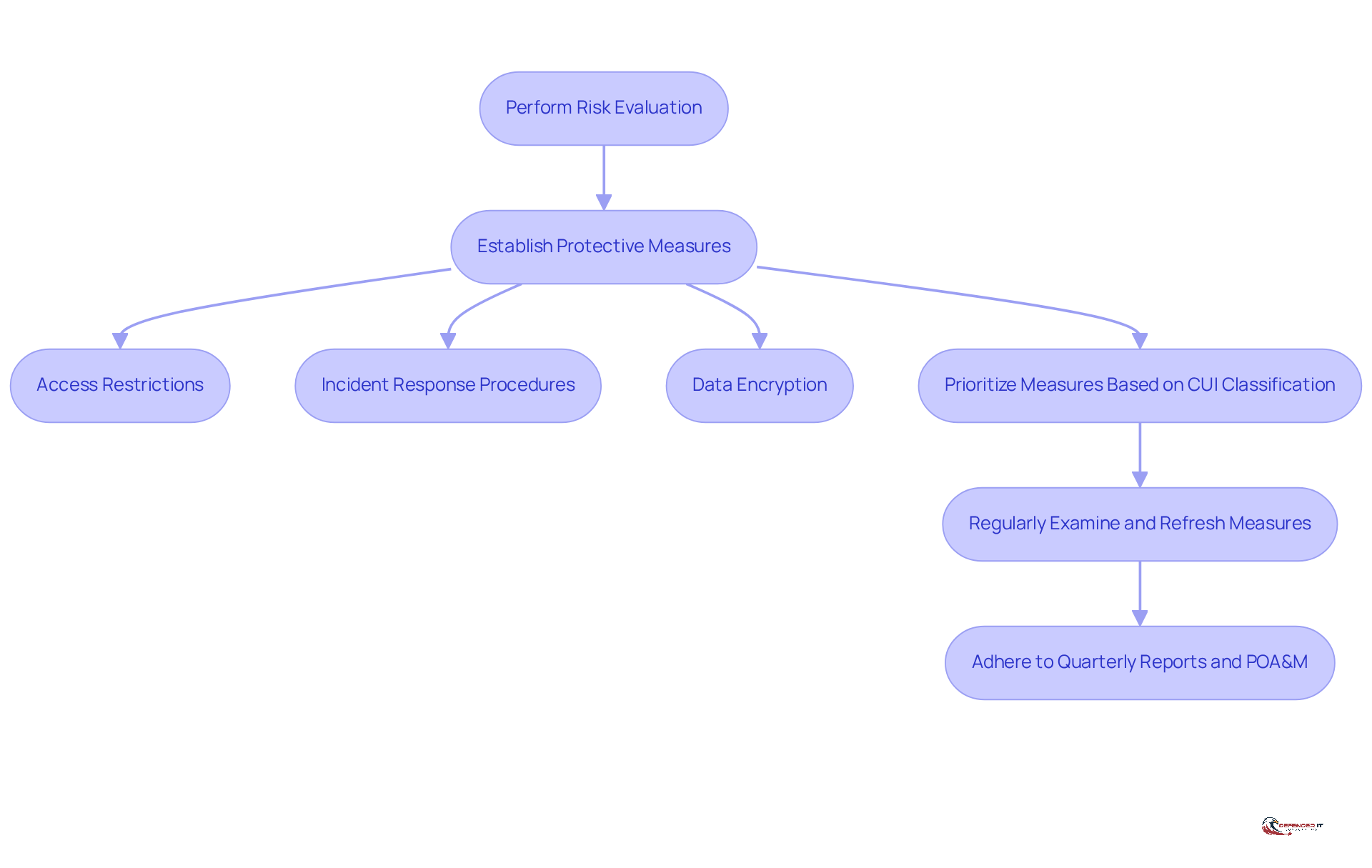
Install Baseline Security Controls
Organizations must establish fundamental protective measures after performing a risk evaluation to address identified weaknesses. These measures should align with the requirements of and may include:
- Access restrictions
Prioritization of these measures should be based on the classification of and the outcomes of the .
Consistently examining and refreshing these measures is crucial for upholding standards and adapting to changing risks. Notably, entities that have effectively executed these measures report , underscoring the efficacy of a . Recent data indicates that around [insert percentage] of entities have attained adherence to these fundamental controls, emphasizing the significance of a .
As highlighted by the Government Services Administration, regular updates and adherence to quarterly and Plans of Action and Milestones (POA&M) are essential for ongoing conformity.
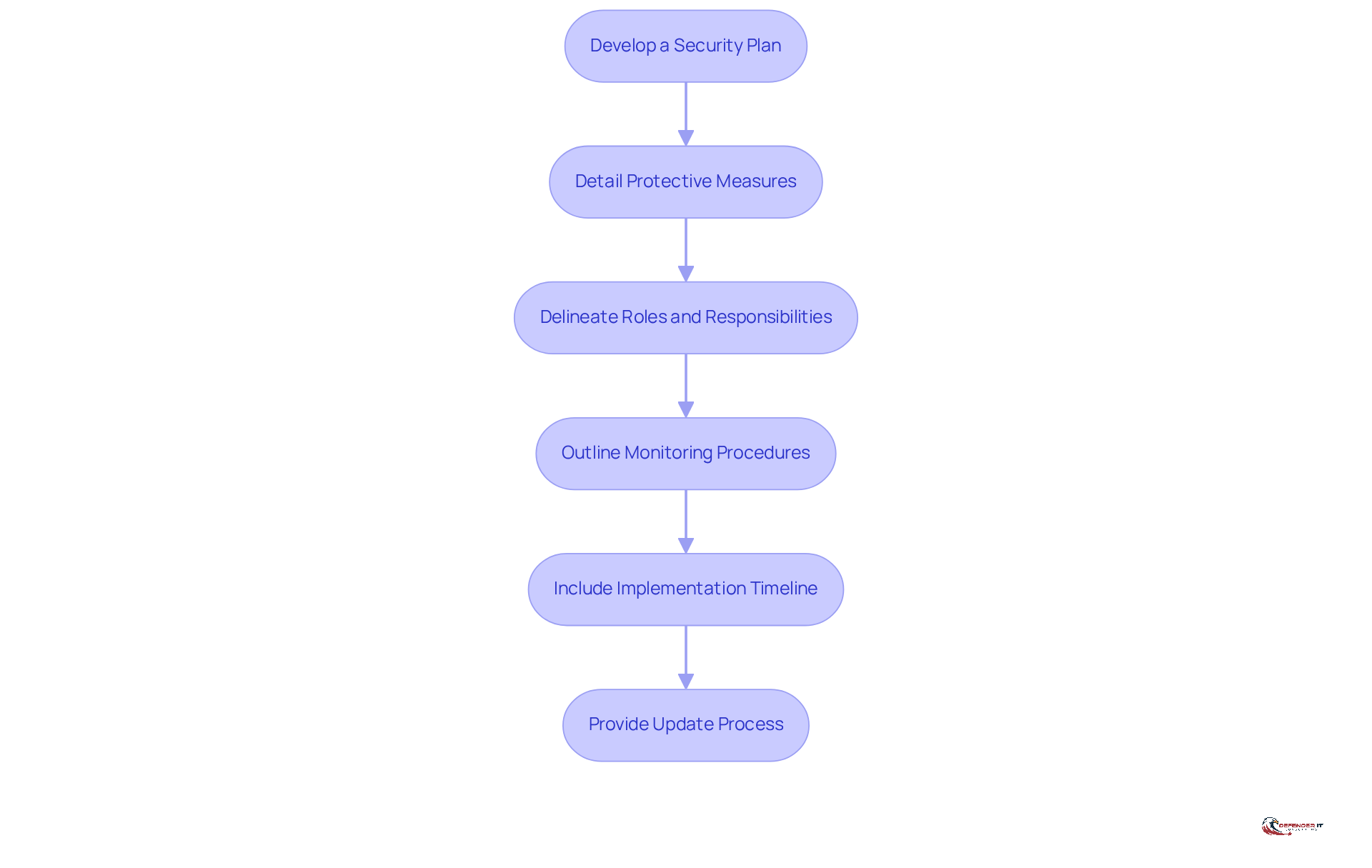
Develop a Security Plan
A protective strategy is essential for organizations aiming to enforce and maintain adherence to . This document must:
- Detail specific
- Delineate personnel roles and responsibilities
- Outline procedures for monitoring and assessing
- Include a timeline for implementing controls
- Provide a systematic process for updating the plan as necessary
Frequent evaluations of the protection plan are crucial, ensuring its relevance and effectiveness in mitigating . Notably, only a fraction of entities have documented , underscoring the need for comprehensive adherence strategies that encompass these vital components. With the introduction of , organizations must also ensure their protection plans are updated to reflect evolving contractual requirements.
Additionally, linking the to a (POA&M) is critical for ensuring adherence. This connection reinforces the organization’s commitment to maintaining and .
Educate Employees on Compliance
Employee education is crucial for achieving compliance with . Organizations must conduct regular to ensure that all employees grasp the significance of protecting (CUI) and their specific roles in upholding these regulations. Training should cover:
- Adhering to proper data handling procedures
- Following
Notably, 68% of cyberattacks stem from human error, highlighting the necessity for .
Furthermore, organizations should provide resources and ongoing support to reinforce training, fostering a culture of awareness. For example, integrating interactive formats and gamification can enhance engagement, with studies indicating that gamification . By prioritizing , businesses can substantially reduce their risk exposure and improve with , as trained employees are better equipped to identify and respond to potential threats.
Moreover, it is essential to incorporate derived requirement 3.2.3, which emphasizes , alongside fundamental requirements 3.2.1 and 3.2.2, which ensure personnel are aware of risks and trained to fulfill their responsibilities.
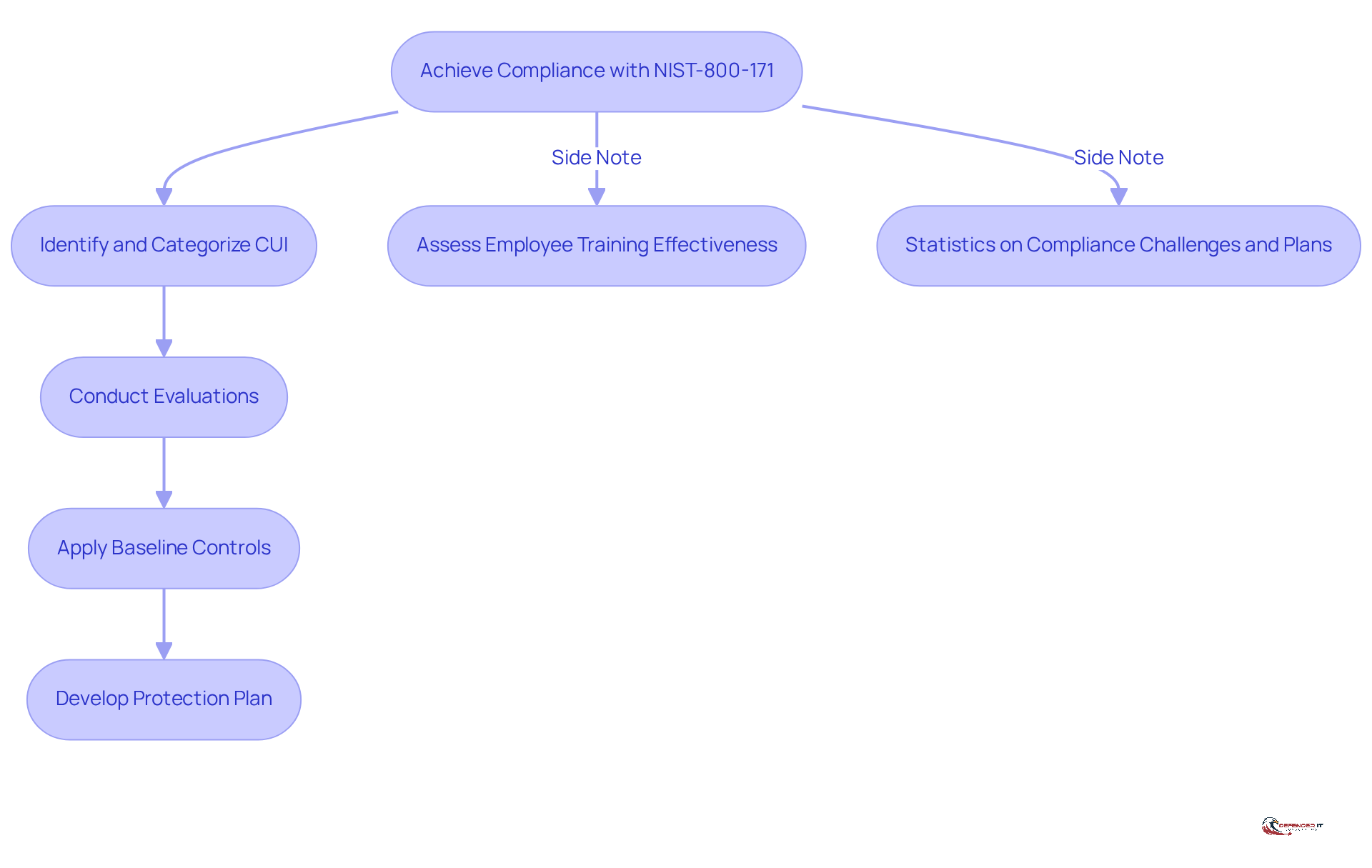
Review Key Steps for Compliance
To achieve , organizations must prioritize . This involves:
- Confirming that (CUI) has been accurately identified and categorized.
- Conducting thorough evaluations.
- Applying baseline controls.
- Developing a comprehensive protection plan.
Additionally, assessing the effectiveness of is essential, with necessary modifications made to enhance understanding and adherence to safety protocols. Notably, 41% of leaders indicate that educating employees on regulations is a primary focus for the upcoming year.
Frequent adherence assessments not only help companies maintain compliance but also enable them to adapt to evolving threats and regulatory changes. Furthermore, 74% of organizations struggle to , highlighting the challenges faced in maintaining standards. Importantly, 91% of companies plan to implement within the next five years, underscoring the growing recognition of its importance in and security resilience.
Organizations that actively engage in are better equipped to mitigate risks and , ultimately fostering trust among stakeholders and clients.
Conclusion
Achieving compliance with NIST 800-171 is essential for organizations handling Controlled Unclassified Information (CUI), particularly those engaged in federal contracts. This framework not only protects sensitive data but also reduces risks associated with cybersecurity threats. By adopting a structured approach, organizations can effectively navigate the complexities of compliance and bolster their overall security posture.
The article delineates critical steps for attaining NIST 800-171 compliance. These include:
- Identifying and classifying CUI
- Conducting security assessments
- Implementing baseline security controls
- Developing comprehensive security plans
- Educating employees about compliance
Each step is interconnected, underscoring the necessity of a proactive and systematic approach to cybersecurity. Organizations that prioritize these actions are better equipped to safeguard sensitive information and uphold operational integrity.
Ultimately, the importance of NIST 800-171 compliance transcends mere regulatory adherence; it cultivates trust among stakeholders and enhances an organization’s resilience against cyber threats. As the landscape of federal contracting evolves, organizations must commit to ongoing improvement in their compliance efforts. By doing so, they not only secure their business opportunities but also contribute to a safer digital environment for all.
Frequently Asked Questions
What is NIST 800-171 compliance?
NIST 800-171 compliance refers to a framework established by the National Institute of Standards and Technology for protecting Controlled Unclassified Information (CUI) within non-federal systems. It is essential for organizations handling sensitive information, particularly those engaged in federal contracts.
Why is NIST 800-171 compliance important?
Compliance is crucial due to the increasing number of cybersecurity incidents affecting contractors. Since 2016, around 8% of commercial contractors have reported data breaches, impacting nearly 300,000 employees. Noncompliance can lead to severe consequences, including disqualification from contracts and breaches of contract.
What are the key elements of the NIST 800-171 framework?
The key elements include access management, incident response, and continuous monitoring. Access management involves restricting CUI access to authorized individuals and implementing protective measures.
How many security requirements are included in the NIST 800-171 framework?
The framework comprises 14 groups of security requirements, which encompass a total of 110 specific measures that organizations must implement to safeguard CUI effectively.
What types of organizations are encouraged to adopt NIST 800-171 standards?
Organizations that handle sensitive information, especially those engaged in federal contracts, are encouraged to adopt NIST 800-171 standards to enhance their cybersecurity measures and reduce vulnerabilities.
What constitutes Controlled Unclassified Information (CUI)?
CUI includes sensitive data that requires protection but does not meet the criteria for classified status. Examples of CUI include personally identifiable information (PII), financial records, and proprietary business information.
Where can organizations find a list of CUI categories?
Organizations can refer to the CUI Registry, which provides a comprehensive list of CUI categories and subcategories, including updates that align with new requirements set forth by the GSA.
What should organizations do to align with the new standards for CUI?
Organizations are encouraged to act promptly to align their practices with the new standards published by the GSA, reflecting the broader federal trend towards enforceable cybersecurity measures for contractors.
What percentage of institutions have developed formal plans for NIST 800-171 compliance?
According to the article, 54% of institutions have developed formal plans for compliance, while 44% have not, indicating a disparity in preparedness.
How does achieving compliance with NIST 800-171 benefit organizations?
Achieving compliance helps organizations protect sensitive information, mitigate risks associated with cybersecurity threats, and maintain operational integrity, which is increasingly critical for securing business opportunities in the federal contracting landscape.
List of Sources
- Understand NIST 800-171 Compliance
- A Quiet Policy Shift Just Redefined Entire Federal Cybersecurity Landscape (https://forbes.com/sites/emilsayegh/2026/02/07/a-quiet-policy-shift-just-redefined-entire-federal-cybersecurity-landscape)
- The Complete Guide to NIST SP 800-171 | Peerless (https://getpeerless.com/complete-guide-nist-800-171)
- EDUCAUSE QuickPoll Results: NIST SP 800-171 Compliance Efforts and Challenges in Higher Education (https://er.educause.edu/articles/2025/3/educause-quickpoll-results-nist-sp-800-171-compliance-efforts-and-challenges-in-higher-education)
- NIST 800-171 Compliance Checklist: Tutorial & Best Practices – Device42 (https://device42.com/compliance-standards/nist-800-171-compliance-checklist)
- Identify Controlled Unclassified Information (CUI)
- CUI Category: Statistical Information (https://archives.gov/cui/registry/category-detail/statistical.html)
- GSA’s CMMC-like rules raise concerns in industry | Federal News Network (https://federalnewsnetwork.com/acquisition-policy/2026/03/gsas-cmmc-like-rules-raise-concerns-in-industry)
- GSA’s New CUI Requirements: What Government Contractors Need to Know | Insights | Holland & Knight (https://hklaw.com/en/insights/publications/2026/03/gsas-new-cui-security-requirements-what-government-contractors)
- GSA Updates Guide for Protecting CUI in Nonfederal Systems (https://executivegov.com/articles/gsa-guide-cui-protection-nonfederal-systems)
- GSA Issues New Framework for Protecting CUI in Contractor Systems | Blank Rome LLP (https://blankrome.com/publications/gsa-issues-new-framework-protecting-cui-contractor-systems)
- Classify Controlled Unclassified Information (CUI)
- FAR Proposed Controlled Unclassified Information Rule: A Path Toward Standardization (https://cozen.com/news-resources/publications/2025/far-proposed-controlled-unclassified-information-rule-a-path-toward-standardization)
- GSA’s CMMC-like rules raise concerns in industry | Federal News Network (https://federalnewsnetwork.com/acquisition-policy/2026/03/gsas-cmmc-like-rules-raise-concerns-in-industry)
- GSA’s New CUI Requirements: What Government Contractors Need to Know | Insights | Holland & Knight (https://hklaw.com/en/insights/publications/2026/03/gsas-new-cui-security-requirements-what-government-contractors)
- Data Classification Guide: Types, Levels & Best Practices (https://sentinelone.com/cybersecurity-101/data-and-ai/what-is-data-classification)
- A Quiet Policy Shift Just Redefined Entire Federal Cybersecurity Landscape (https://forbes.com/sites/emilsayegh/2026/02/07/a-quiet-policy-shift-just-redefined-entire-federal-cybersecurity-landscape)
- Perform a Security Assessment
- The Top 20 Expert Quotes On Cyber Risk and Security (https://surtech.co.za/20-expert-quotes-on-cyber-risk-and-security)
- Securing DoD Contracts: A Case Study in NIST SP 800-171 Compliance – Cleared Systems (https://clearedsystems.com/nist-sp-800-171-compliance-success-story?srsltid=AfmBOooGlQmDey36MN2TDca6-lXlNP7rubggfBMCprMaAJuCqeiTCUnT)
- NIST Issues Updated Security Requirements for Protecting CUI | CSRC (https://csrc.nist.gov/news/2024/updated-security-requirements-for-protecting-cui)
- Reality Check: Defense Industry’s Implementation of NIST SP 800-171 (https://cybersecurityventures.com/reality-check-defense-industrys-implementation-of-nist-sp-800-171)
- Install Baseline Security Controls
- Surprise! GSA Releases New Cybersecurity Requirements (https://doxnet.com/articles/surprise-gsa-releases-new-cybersecurity-requirements)
- NIST drafts enhanced security requirements to protect CUI in nonfederal systems, seeks feedback by Nov. 14 – Industrial Cyber (https://industrialcyber.co/nist/nist-drafts-enhanced-security-requirements-to-protect-cui-in-nonfederal-systems-seeks-feedback-by-nov-14)
- New GSA Guidance on Protecting CUI in Contractor Systems, Plus a Look Ahead at Pending FAR Changes | JD Supra (https://jdsupra.com/legalnews/new-gsa-guidance-on-protecting-cui-in-2838068)
- DOD Is Finally Leaning Into CMMC 2.0 Requirements for CUI (https://fedtechmagazine.com/article/2026/03/dod-finally-leaning-cmmc-20-requirements-cui)
- Cybersecurity Updates: NIST Publishes SP 800-171 Revision 3. What Changed, and What Comes Next? (https://wiley.law/newsletter-Cybersecurity-Updates-NIST-Publishes-SP-800-171-Revision-3-What-Changed-and-What-Comes-Next)
- Develop a Security Plan
- Why Every Defense Contractor Needs an Up-to-Date System Security Plan (SSP) – NIST SP 800 171 Compliance Experts – On Call Compliance Solutions (https://nist800171compliance.com/why-every-defense-contractor-needs-an-up-to-date-system-security-plan-ssp)
- 2026 Cyber Security Compliance Statistics | Swif (https://swif.ai/blog/cyber-security-compliance-statistics)
- Understanding NIST 800-171: How to Become Compliant (https://preveil.com/blog/nist-800-171)
- 110 security and compliance statistics for tech leaders to know in 2025 (https://vanta.com/resources/compliance-statistics)
- Reality Check: Defense Industry’s Implementation of NIST SP 800-171 (https://cybersecurityventures.com/reality-check-defense-industrys-implementation-of-nist-sp-800-171)
- Educate Employees on Compliance
- Why Employee Cybersecurity Awareness Training Is Important (https://sentinelone.com/platform/small-business/cybersecurity-awareness-training-for-employees)
- NIST SP 800-171 Requirement 3.2: Awareness and Training – NeQter Labs (https://neqterlabs.com/nist-sp-800-171-requirement-3-2-awareness-and-training)
- 115 Compliance Statistics You Need To Know in 2023 – Drata (https://drata.com/blog/compliance-statistics)
- The Importance of Cybersecurity Training for Employees | IP Pathways (https://ippathways.com/the-importance-of-cybersecurity-training-for-employees)
- Security Awareness Training Statistics 2025 [100+ Studies] | Brightside AI Blog (https://brside.com/blog/security-awareness-training-statistics-2025-100-studies)
- Review Key Steps for Compliance
- 4 Quotes that Underscore the Importance of Compliance (https://compliancebridge.com/4-quote-that-underscore-importance-of)
- The Top 20 Expert Quotes On Cyber Risk and Security (https://surtech.co.za/20-expert-quotes-on-cyber-risk-and-security)
- Cybersecurity Updates: NIST Publishes SP 800-171 Revision 3. What Changed, and What Comes Next? (https://wiley.law/newsletter-Cybersecurity-Updates-NIST-Publishes-SP-800-171-Revision-3-What-Changed-and-What-Comes-Next)
- Reality Check: Defense Industry’s Implementation of NIST SP 800-171 (https://cybersecurityventures.com/reality-check-defense-industrys-implementation-of-nist-sp-800-171)
- 115 Compliance Statistics You Need To Know in 2023 – Drata (https://drata.com/blog/compliance-statistics)
](https://defenderit.consulting/4-best-practices-for-effective-hipaa-consultation-in-compliance/).](https://images.tely.ai/telyai/veodalnf-each-box-represents-a-step-in-the-security-assessment-process-follow-the-arrows-to-see-how-each-action-leads-to-the-next-helping-organizations-identify-vulnerabilities-and-improve-their-security-posture.webp)