Introduction
In an era where cyber threats are increasingly prevalent, the necessity of a robust incident response plan is paramount. Organizations encounter a growing spectrum of risks, making it essential not only to prepare but also to respond effectively to incidents. This article explores four best practices aligned with NIST guidelines that can significantly bolster an organization’s incident response capabilities.
How can organizations ensure they are not merely reacting to incidents but are also proactively strengthening their defenses against future threats?
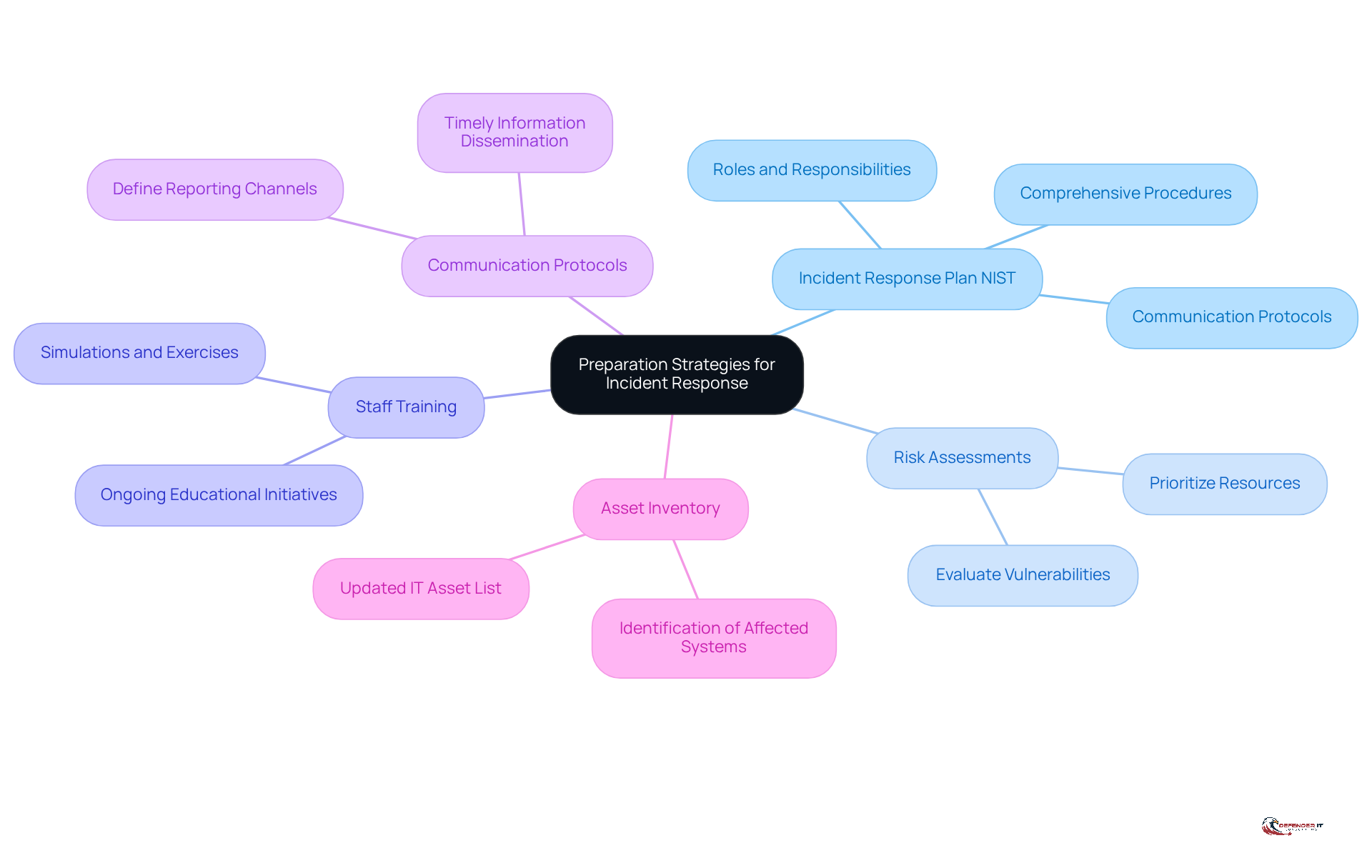
Establish Preparation Strategies for Incident Response
To enhance incident response preparedness, organizations should focus on the following strategies:
-
Develop an incident response plan NIST: Formulate a comprehensive incident response plan NIST that outlines procedures for addressing various types of incidents. This strategy must encompass roles, responsibilities, and communication protocols.
-
Conduct Risk Assessments: Regularly evaluate the organization’s risk landscape to pinpoint vulnerabilities and potential threats. This assessment aids in prioritizing resources and concentrating efforts on critical areas.
-
Train Staff: Implement ongoing educational initiatives for all personnel to ensure they understand their roles in crisis management. This training should include simulations and tabletop exercises to practice response scenarios effectively.
-
Establish Communication Protocols: Define explicit communication channels for reporting incidents and disseminating information during an event. This clarity ensures timely and effective communication among stakeholders.
-
Maintain an Asset Inventory: Keep an updated inventory of all IT assets, including hardware and software, to enable swift identification of affected systems during an incident.
By focusing on these preparation strategies, organizations can significantly enhance their readiness and resilience against cyber threats.
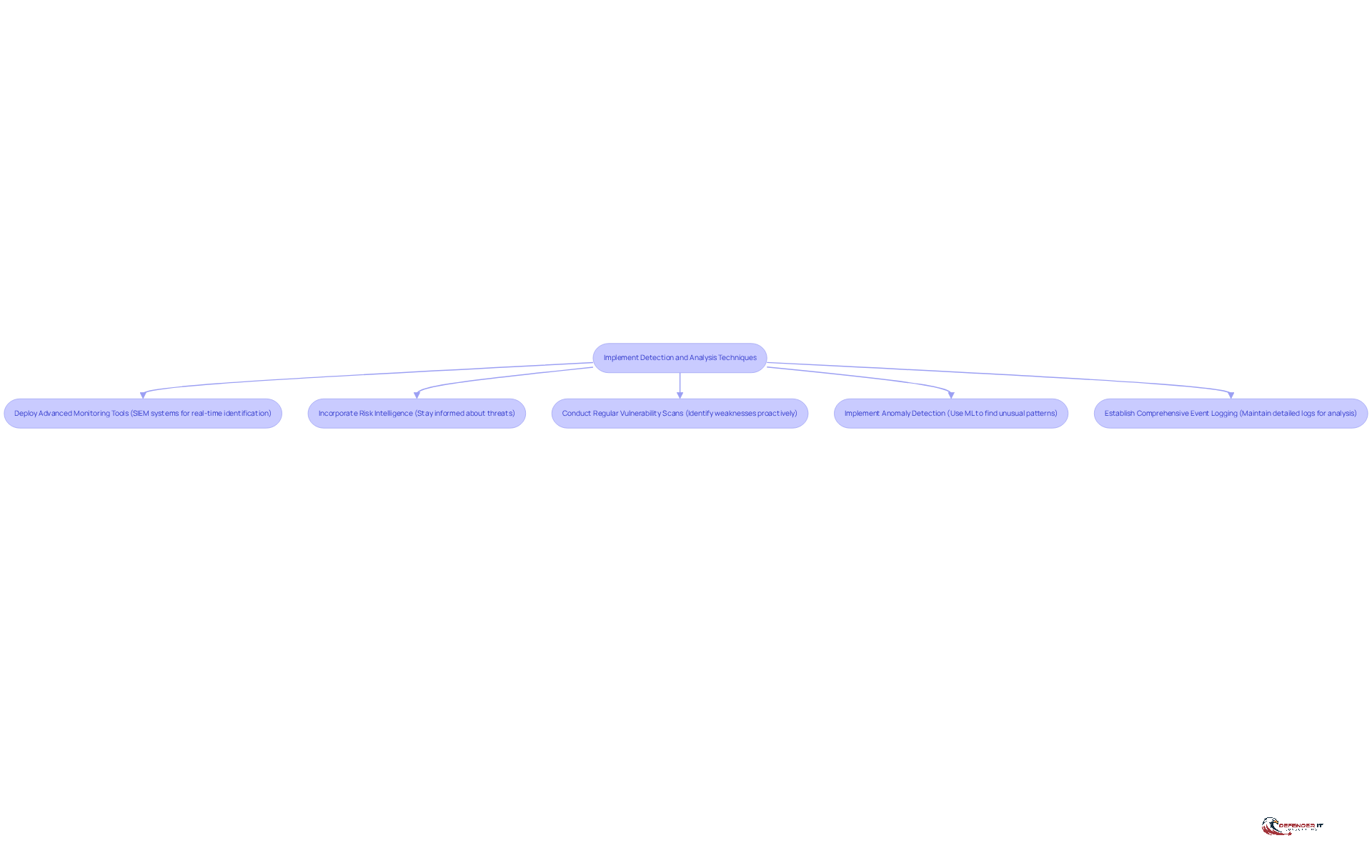
Implement Detection and Analysis Techniques
To effectively implement detection and analysis techniques, organizations should consider the following strategies:
-
Deploy Advanced Monitoring Tools: Implement security information and event management (SIEM) systems to aggregate and analyze security data across the organization. This strategy facilitates real-time identification of suspicious activities, thereby enhancing the overall security posture. Notably, the average cost of a data breach in healthcare reached $10.93 million per incident in 2023, highlighting the critical need for robust monitoring.
-
Incorporate Risk Intelligence: Utilize risk intelligence feeds to remain informed about emerging threats and vulnerabilities. This proactive measure not only enhances detection capabilities but also informs response strategies, allowing organizations to adapt swiftly to evolving cyber risks. Experts indicate that approximately 90% of all cyber incidents originate from phishing emails, underscoring the vital role of threat intelligence in preventing breaches.
-
Conduct Regular Vulnerability Scans: Implement routine vulnerability assessments to identify weaknesses within the IT infrastructure. This proactive approach enables organizations to address vulnerabilities before they can be exploited, significantly reducing risk exposure. Regular scans are essential in mitigating the impact of the 4,000 cyber attacks that occur daily.
-
Implement Anomaly Detection: Leverage machine learning algorithms to identify unusual patterns in network traffic or user behavior. This advanced technique can uncover potential incidents that traditional methods may overlook, thereby improving detection rates. As the cybersecurity landscape evolves, organizations must adapt to new threats, including sophisticated social engineering tactics.
-
Establish Comprehensive Event Logging: Maintain detailed logs of all security incidents and events. This documentation is crucial for post-event analysis, helping organizations understand the nature and impact of incidents, and informing future prevention strategies. Effective logging practices can significantly reduce the average time to resolve cybersecurity issues, which was reported as 20 days across federal agencies.
By implementing these detection and analysis methods, organizations can substantially enhance their ability to recognize and respond to cybersecurity events, ultimately safeguarding their operations and reputation.
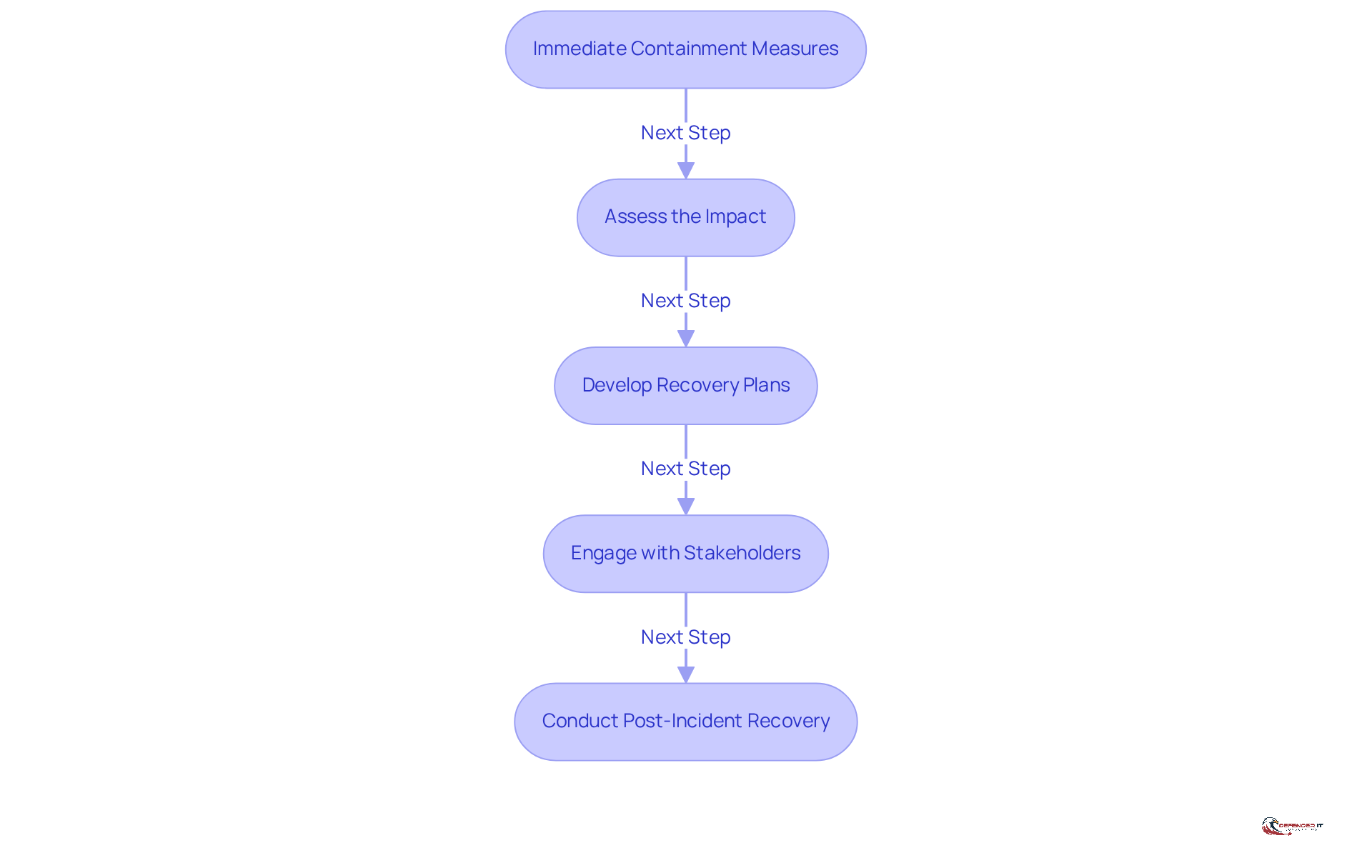
Execute Containment and Recovery Procedures
To execute effective containment and recovery procedures, organizations should follow these key steps:
-
Implement Immediate Containment Measures: Upon detection of an occurrence, it is imperative to take immediate steps to contain the threat. This may involve isolating affected systems or blocking malicious traffic to prevent further damage.
-
Assess the Impact: A thorough evaluation of the occurrence is essential to understand which systems and data have been affected. This assessment is crucial for determining the appropriate recovery actions and prioritizing efforts.
-
Develop Recovery Plans: Organizations should create detailed recovery plans that outline the necessary steps to restore affected systems and data. This includes establishing data backups and restoration procedures to ensure business continuity and minimize downtime.
-
Engage with Stakeholders: Keeping all relevant stakeholders informed about the occurrence and the actions being taken to resolve it is vital. Clear communication helps manage expectations and maintain trust among all parties involved.
-
Conduct Post-Incident Recovery: After containment, the focus should shift to restoring normal operations while ensuring that all systems are secure before bringing them back online. This may involve implementing additional security measures to prevent future occurrences.
By adhering to the containment and recovery protocols specified in the incident response plan NIST, organizations can effectively manage incidents and mitigate their impact on operations.
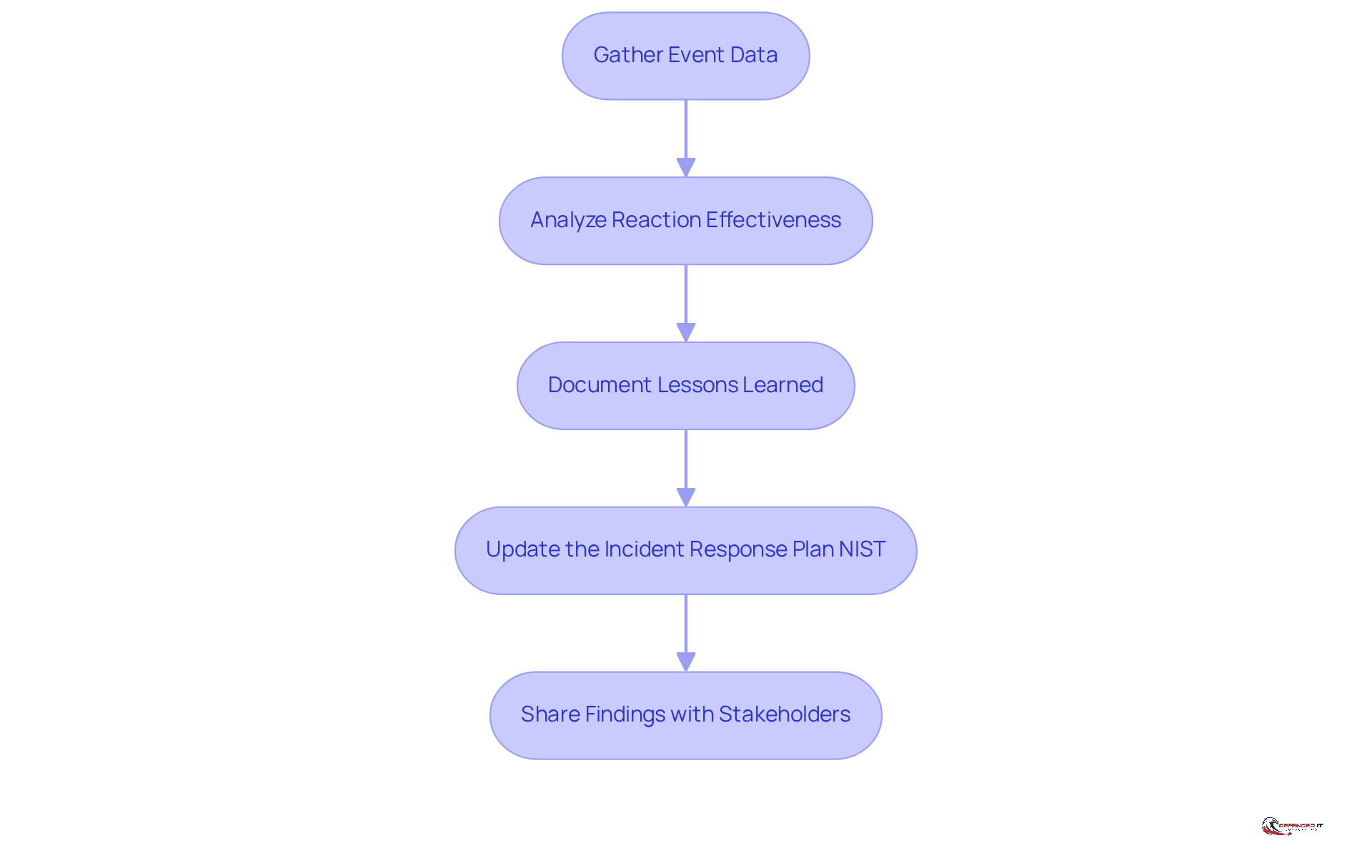
Conduct Post-Incident Reviews and Improvements
To enhance incident response capabilities and reduce the likelihood of future incidents, organizations must conduct effective post-incident reviews and implement improvements in their incident response plan NIST. The following best practices are essential:
-
Gather Event Data: Collect all relevant data related to the event, including logs, reports, and communications. This information is crucial for a comprehensive analysis, providing the foundation for understanding the context and impact of the situation.
-
Analyze Reaction Effectiveness: Assess the occurrence management process to identify successful actions and areas needing enhancement. This analysis should involve all team members who participated in the response, ensuring diverse perspectives are acknowledged. Research indicates that only about 30% of organizations document lessons learned from events, highlighting the need for a systematic approach to this critical phase.
-
Document Lessons Learned: Create a detailed report outlining the findings from the post-incident review. This report should emphasize successes, challenges, and actionable recommendations for future improvements. Effective documentation not only aids in refining strategies but also serves as a resource for training and awareness initiatives. Timely evaluations lead to more accurate assessments and practical insights that can enhance future responses.
-
Update the Incident Response Plan NIST: The organization developed an incident response plan NIST to effectively manage potential security breaches. Revise the incident response plan NIST based on the lessons learned to integrate new insights and strategies. This ensures that the organization is better prepared for future occurrences, adapting to evolving threats and vulnerabilities.
-
Share Findings with Stakeholders: Communicate the results of the post-incident review with relevant stakeholders to promote a culture of transparency and continuous improvement. Engaging stakeholders in discussions about the event and its implications can bolster organizational resilience and readiness. Involving diverse stakeholders in the post-incident review process enriches the analysis and ensures that lessons learned are operationally relevant.
By conducting thorough post-incident reviews and implementing improvements, organizations can significantly enhance their incident response capabilities, ultimately strengthening their overall cybersecurity posture.
Conclusion
Enhancing an organization’s incident response capabilities is critical in the current cybersecurity landscape. Establishing a robust incident response plan based on NIST guidelines allows organizations to effectively prepare for, detect, and respond to incidents, ultimately safeguarding their operations and reputation.
This article outlines several best practices that form the foundation of a successful incident response strategy. Key recommendations include:
- Developing a comprehensive incident response plan.
- Conducting regular risk assessments.
- Training staff.
- Deploying advanced monitoring tools.
- Implementing effective containment and recovery procedures.
Additionally, conducting thorough post-incident reviews enables organizations to learn from past events and continuously improve their response strategies.
The significance of these practices cannot be overstated. As cyber threats evolve, organizations must remain vigilant and proactive in their approach to incident response. By embracing these best practices, businesses not only enhance their resilience against potential breaches but also foster a culture of continuous improvement and preparedness. Investing in an effective incident response plan today ensures a more secure tomorrow, ultimately protecting both assets and stakeholder trust.
Frequently Asked Questions
What is the first step organizations should take to enhance incident response preparedness?
Organizations should develop a comprehensive incident response plan that outlines procedures for addressing various types of incidents, including roles, responsibilities, and communication protocols.
Why is conducting risk assessments important for incident response?
Regular risk assessments help organizations evaluate their risk landscape, identify vulnerabilities and potential threats, and prioritize resources to focus efforts on critical areas.
How can staff training improve incident response?
Ongoing educational initiatives ensure that all personnel understand their roles in crisis management. This training should include simulations and tabletop exercises to practice response scenarios effectively.
What should organizations establish regarding communication during an incident?
Organizations should define explicit communication protocols for reporting incidents and disseminating information, ensuring timely and effective communication among stakeholders.
Why is maintaining an asset inventory crucial for incident response?
Keeping an updated inventory of all IT assets, including hardware and software, allows for swift identification of affected systems during an incident, enhancing response efficiency.
How do these preparation strategies contribute to an organization’s resilience against cyber threats?
By focusing on these preparation strategies, organizations can significantly enhance their readiness and resilience against cyber threats, ensuring better management of incidents when they occur.