Introduction
Manufacturing today faces a landscape filled with cybersecurity challenges, where the stakes have never been higher. With compliance rates for critical standards such as ISO/IEC 27001 on the rise, manufacturers have a unique opportunity to strengthen their defenses while navigating complex regulatory frameworks. However, the pressing question is: how can organizations effectively implement best practices for IT security compliance to not only meet these standards but also safeguard themselves against evolving threats?
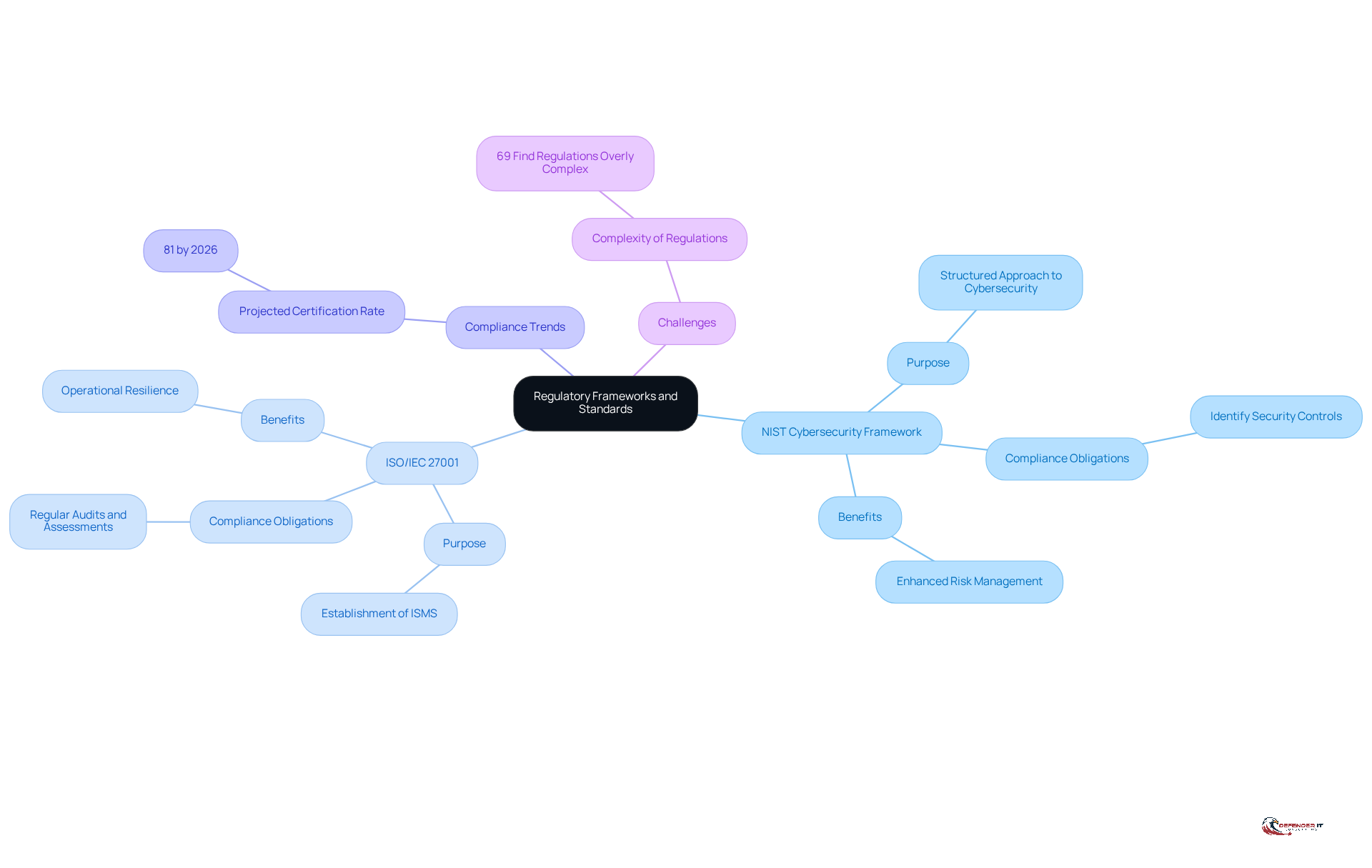
Understand Regulatory Frameworks and Standards
Manufacturers must have a comprehensive understanding of the regulatory frameworks and standards governing cybersecurity practices, particularly the NIST Cybersecurity Framework and ISO/IEC 27001. These frameworks are essential for identifying compliance obligations and implementing necessary security controls. The NIST framework offers a structured approach to managing cybersecurity challenges, while ISO/IEC 27001 emphasizes the establishment of an Information Security Management System (ISMS).
As we look toward 2026, compliance rates for ISO/IEC 27001 within the manufacturing sector are projected to rise significantly, with 81% of entities indicating current or planned certification. This trend reflects an increasing recognition of the importance of robust cybersecurity measures. Regularly reviewing and updating strategies for IT security compliance in accordance with these standards is vital for mitigating risks and avoiding penalties.
Cybersecurity specialists note that organizations frequently face challenges in applying ISO/IEC 27001 due to its evolving nature and the need for continuous improvement. For example, 69% of organizations report that regulations are overly complex or numerous, highlighting the necessity for effective compliance practices. Case studies from the manufacturing sector illustrate that companies adopting these frameworks not only enhance their defensive posture but also achieve greater operational resilience against emerging threats.
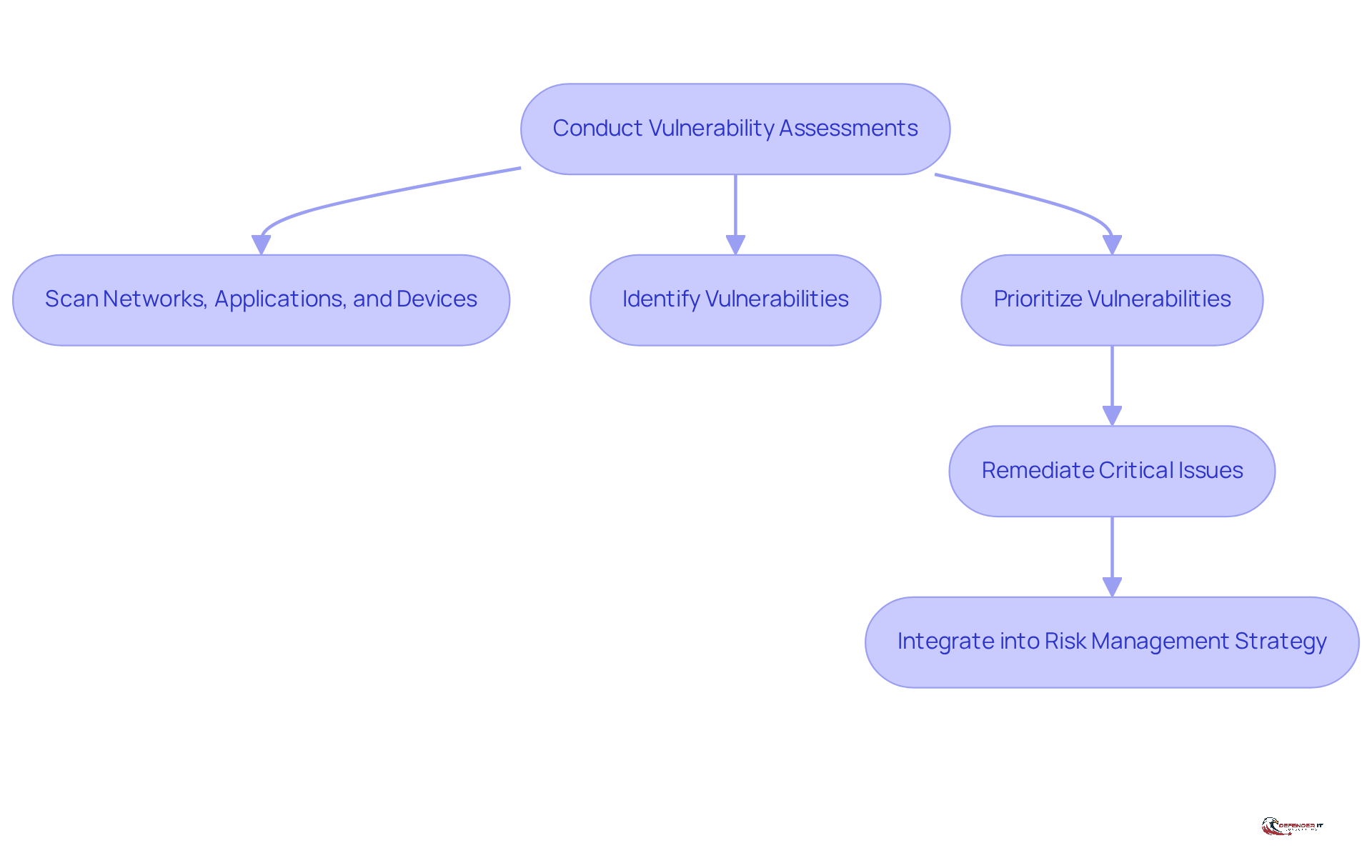
Conduct Regular Vulnerability Assessments
Manufacturers must establish a routine for conducting vulnerability assessments to identify potential security gaps within their systems. This critical process involves scanning networks, applications, and devices for known vulnerabilities and misconfigurations. Tools such as Nessus and Qualys effectively streamline these assessments, enabling organizations to efficiently pinpoint weaknesses.
Once vulnerabilities are identified, prioritizing them according to their threat level and potential impact is essential. This ensures that critical issues are addressed promptly. For instance, if a manufacturer discovers outdated software that poses a risk, swift remediation can significantly reduce the likelihood of a breach.
Furthermore, integrating vulnerability assessments into a broader risk management strategy allows security measures to adapt and evolve in response to emerging threats. This proactive approach enhances the overall cybersecurity posture of the organization.
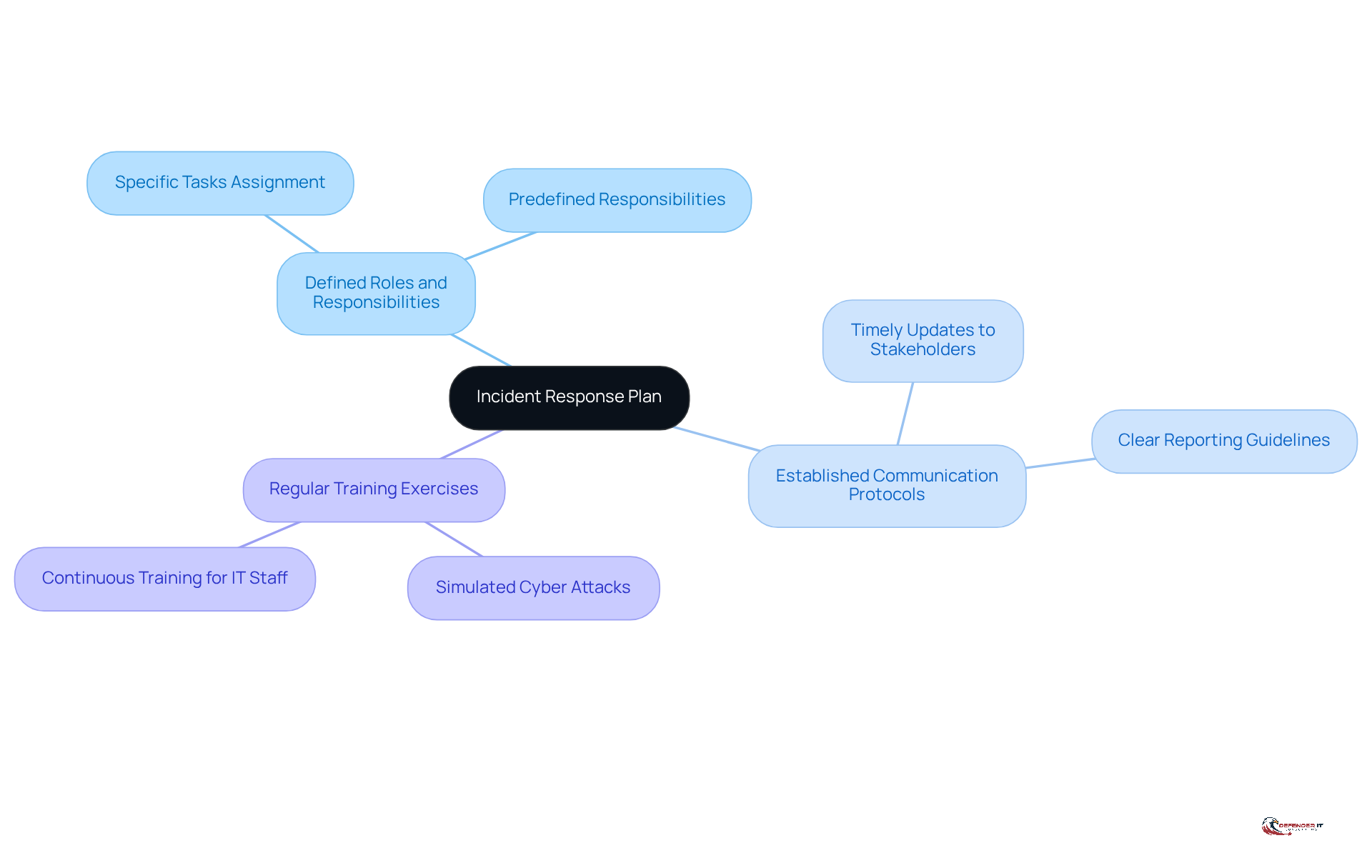
Establish a Comprehensive Incident Response Plan
A robust incident response plan is essential for effectively managing cybersecurity incidents in manufacturing. This plan must clearly outline procedures for detecting, responding to, and recovering from incidents. Key components include:
- Defined roles and responsibilities
- Established communication protocols
- Regular training exercises
For example, entities can conduct simulated cyber attacks to assess their response capabilities, identify vulnerabilities, and enhance their strategies.
Recent data indicates that organizations in manufacturing took an average of 33 days to complete forensic investigations in 2023, with some taking up to 60 days to notify affected parties during a crisis. This underscores the need for timely and efficient incident management. Furthermore, the Cybersecurity and Infrastructure Security Agency (CISA) emphasizes that clear reporting guidelines to regulatory bodies are crucial for IT security compliance.
By proactively preparing for potential incidents, manufacturers can significantly reduce the impact of breaches, ensuring operational continuity and safeguarding their reputation in an increasingly digital landscape. As Eric Neas, CPA Partner at Assurance Services, states, "The key is finding a balance between digital transformation, along with integration and workforce development." This highlights the necessity of ongoing practice and simulations to uphold an effective incident response plan.
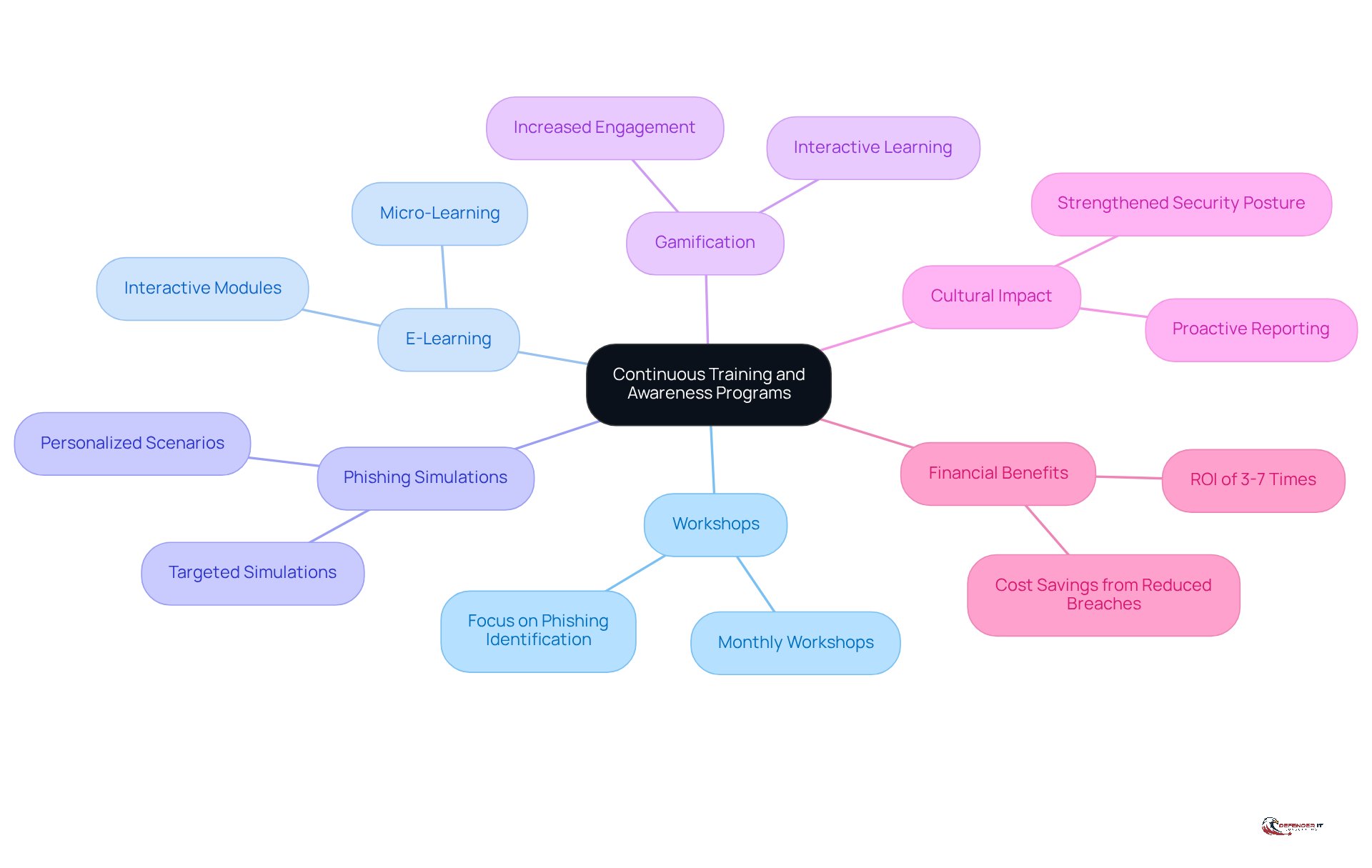
Implement Continuous Training and Awareness Programs
Manufacturers must prioritize continuous education and awareness initiatives to equip employees with the knowledge necessary to recognize and respond effectively to cybersecurity risks. This approach can take various forms, including:
- Regular workshops
- Interactive e-learning modules
- Targeted phishing simulations designed to assess and enhance employees’ responses to potential threats
For example, a manufacturing firm could implement monthly workshops that specifically focus on identifying phishing emails and adopting secure password practices. Furthermore, cultivating a culture of security awareness is crucial; it encourages employees to proactively report suspicious activities, thereby strengthening the organization’s overall security posture.
By committing to ongoing development, which has been shown to yield better results than annual programs, manufacturers empower their workforce to serve as the first line of defense against evolving cyber threats. Notably, human actions account for 60% of breaches, underscoring the need for effective education.
Incorporating gamification elements can increase engagement by 60%, making learning more interactive and enjoyable. Additionally, well-structured development programs can yield returns of 3 to 7 times their investment, providing a compelling financial incentive for manufacturers to invest in education.
By addressing the common perception that training can be boring or ineffective, organizations can design more engaging programs that resonate with employees, significantly reducing the risk of incidents that could lead to costly breaches.
Conclusion
Manufacturers today must prioritize IT security compliance to safeguard their operations and sensitive data. Understanding regulatory frameworks such as the NIST Cybersecurity Framework and ISO/IEC 27001 enables organizations to navigate compliance obligations effectively and implement necessary security controls. This proactive approach not only protects against potential threats but also positions manufacturers to excel in an increasingly digital landscape.
The article identified four essential practices for enhancing IT security compliance in manufacturing. Key strategies include:
- Conducting regular vulnerability assessments to pinpoint and address security gaps.
- Establishing a comprehensive incident response plan to manage potential cyber incidents effectively.
- Prioritizing continuous training and awareness programs to empower employees.
Each of these practices is critical in strengthening an organization’s cybersecurity posture, ensuring resilience against evolving threats.
As the manufacturing sector progresses toward higher compliance and security standards in the coming years, it is vital for organizations to adopt these best practices. By fostering a culture of security awareness and continuous improvement, manufacturers not only protect their assets but also contribute to a more secure industry overall. Embracing these strategies will ultimately enhance operational resilience, reduce the risk of breaches, and provide a stronger competitive edge in the marketplace.