Introduction
Achieving compliance with the Cybersecurity Maturity Model Certification (CMMC) Level 2 is a critical step for organizations handling Controlled Unclassified Information (CUI) to strengthen their cybersecurity defenses. As the defense industry prepares for mandatory compliance by 2026, understanding the intricacies of CMMC Level 2 requirements is essential for maintaining eligibility for lucrative Department of Defense contracts. However, with only a fraction of contractors fully prepared for audits, organizations must consider what strategic steps they need to take to navigate the complexities of compliance and safeguard their future in the defense marketplace.
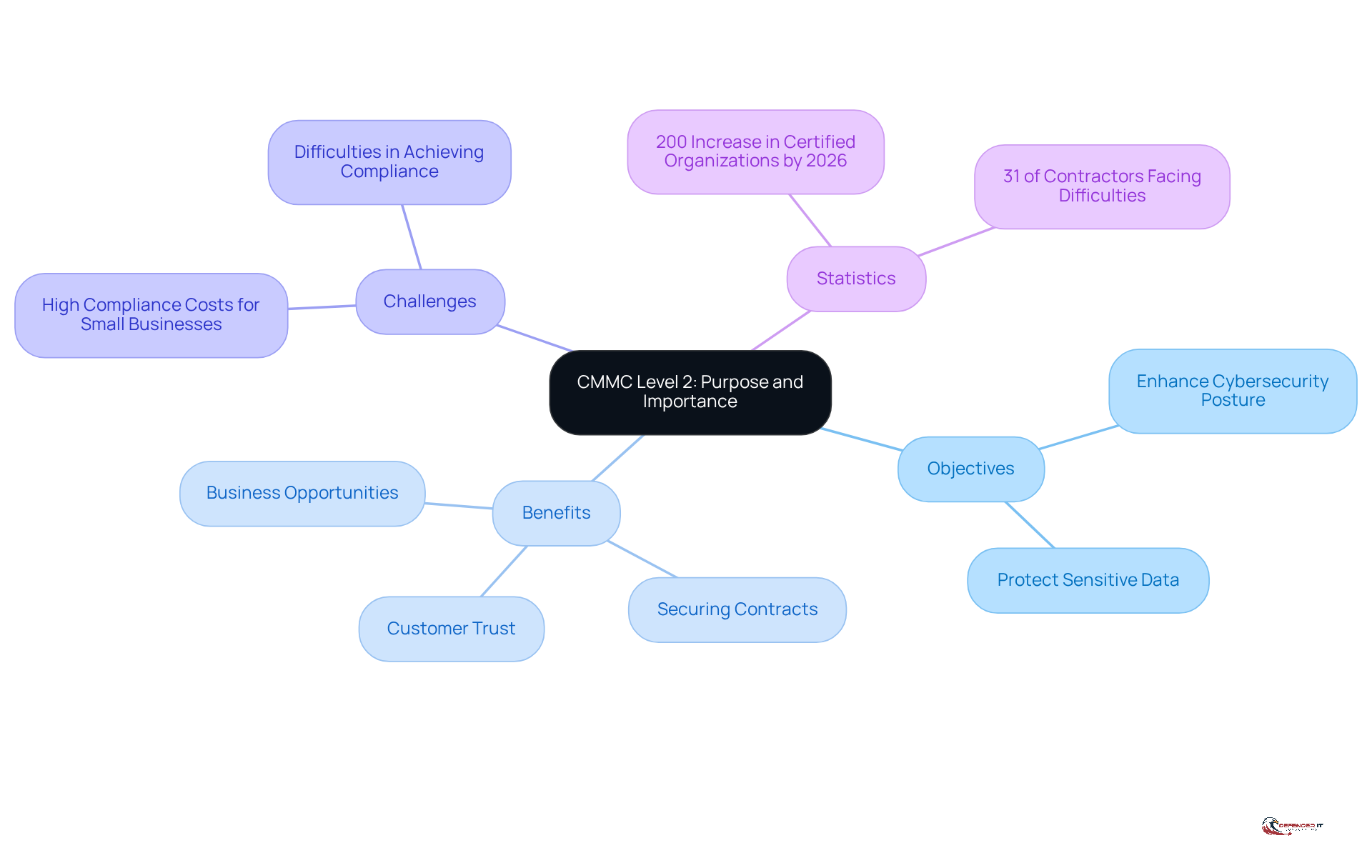
Clarify CMMC Level 2: Purpose and Importance
Cybersecurity Maturity Model Certification 2 is essential for entities managing Controlled Unclassified Information (CUI). Its primary objective is to enhance the cybersecurity posture of defense contractors, ensuring they implement robust practices to protect sensitive data from both internal and external threats.
Achieving the second tier of compliance is not merely a regulatory obligation; it is vital for maintaining eligibility for Department of Defense (DoD) contracts, which will become mandatory starting in 2026. Non-compliance can lead to significant financial repercussions and damage to reputation. For example, organizations that successfully navigate the certification process, such as DMI, demonstrate that timely adherence can secure future contracts and revenue streams, even under pressing deadlines. Notably, DMI achieved certification at Stage 2 with a perfect score in just two months, underscoring the feasibility of rapid compliance when approached strategically.
Furthermore, organizations that obtain this certification convey their commitment to cybersecurity, which can greatly enhance customer trust and create new business opportunities. The defense sector anticipates a nearly 200% increase in organizations certified at the second tier by late 2026. Those who invest early in compliance are better positioned to secure contracts, especially considering that only 1% of contractors report being fully prepared for an audit. Additionally, small businesses encounter considerable challenges in achieving compliance, with estimated costs reaching C$500,000, potentially deterring them from engaging in the defense marketplace.
In summary, the second tier of the cybersecurity maturity model, which encompasses CMMC Level 2 requirements, serves as a vital framework for organizations to protect sensitive information, comply with federal regulations, and maintain a competitive advantage in the evolving defense landscape. Moreover, with 31% of defense contractors facing difficulties in establishing effective protocols to prevent data breaches, the importance of the second tier of certification is paramount.
Outline CMMC Level 2 Requirements and Controls
The implementation of 110 security controls that align with the NIST SP 800-171 framework is necessary to meet the CMMC Level 2 requirements. These controls are categorized into 14 distinct domains, each addressing specific aspects of cybersecurity:
- Access Control: Ensures that only authorized users can access sensitive information.
- Awareness and Training: Provides essential security training to all employees, fostering a security-conscious culture.
- Audit and Accountability: Maintains comprehensive logs of user activities and system changes to ensure accountability.
- Configuration Management: Manages system configurations to prevent unauthorized alterations that could compromise security.
- Identification and Authentication: Verifies user identities before granting access to sensitive systems and data.
- Incident Response: Establishes clear procedures for effectively and efficiently responding to security incidents.
- Maintenance: Conducts regular maintenance on organizational systems to ensure optimal performance and security.
- Media Protection: Safeguards sensitive data stored on both physical and digital media to prevent unauthorized access.
- Physical Protection: Implements physical security measures to protect facilities and sensitive information from unauthorized access.
- Planning: Develops a comprehensive information security strategy detailing protective measures and procedures.
- Personnel Security: Ensures that personnel are trustworthy and adequately trained in security practices.
- Risk Assessment: Conducts regular assessments to identify and mitigate potential risks to the organization.
- System and Communications Protection: Protects data both in transit and at rest to maintain confidentiality and integrity.
- System and Information Integrity: Monitors systems for vulnerabilities and threats to ensure ongoing security.
Organizations must perform a thorough gap analysis to identify areas where they do not meet the CMMC Level 2 requirements. This examination should be followed by the creation of a remediation strategy to address identified gaps, ensuring compliance and enhancing overall security posture. As noted by cybersecurity professionals, effective implementation of these controls is crucial for safeguarding Controlled Unclassified Information (CUI) and maintaining eligibility for Department of Defense contracts. Furthermore, attaining the second tier of the compliance framework typically incurs costs ranging from $34,000 to $112,000 and may require six months to a year. Organizations are also mandated to conduct self-assessments every three years and submit their SPRS score to the DoD. Non-compliance with the CMMC Level 2 requirements can result in the loss of defense contracts, making it essential to adhere to these requirements.
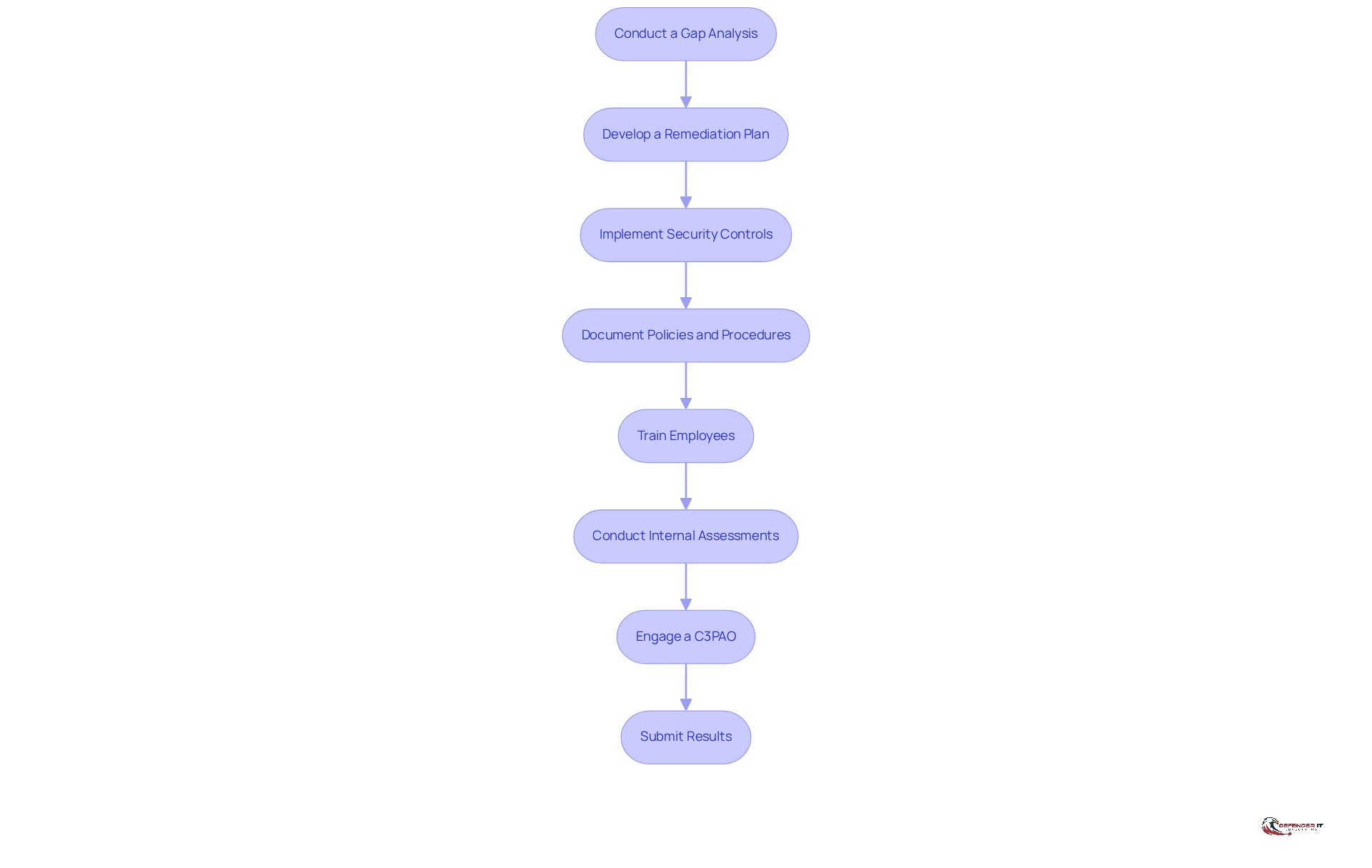
Implement Steps for Achieving CMMC Level 2 Compliance
To achieve CMMC Level 2 compliance, organizations should follow these steps:
-
Conduct a Gap Analysis: Begin by evaluating current security practices against the CMMC Level 2 requirements to identify deficiencies. Research indicates that 73% of companies that conduct thorough gap evaluations possess fully documented cybersecurity policies, positioning them better for adherence.
-
Develop a Remediation Plan: Create a detailed plan to address identified gaps, prioritizing critical areas based on risk. Effective remediation planning is essential for addressing regulatory gaps and ensuring robust security measures.
-
Implement security controls by deploying the necessary measures as outlined in the CMMC Level 2 requirements. Ensure these controls are properly configured and maintained to mitigate potential vulnerabilities.
-
Document Policies and Procedures: Maintain comprehensive documentation of all security policies, procedures, and controls implemented. Organizations with fully documented policies tend to score higher in achieving encryption standards and maintaining third-party access controls.
-
Train Employees: Provide training to all staff on cybersecurity best practices and the significance of adhering to regulations. Employee awareness is a critical factor in maintaining a secure environment.
-
Conduct Internal Assessments: Regularly evaluate the effectiveness of implemented controls through internal assessments and audits. Organizations that measure consistently achieve better outcomes, with a notable improvement in security effectiveness. As Danielle Barbour stated, "Organizations implementing any form of effectiveness measurement achieve demonstrably better results."
-
Engage a C3PAO: If necessary, engage a Certified Third-Party Assessment Organization (C3PAO) to conduct an official assessment for certification. This step is essential for organizations aiming to confirm their adherence status.
-
Submit Results: After passing the assessment, submit the results to the relevant authorities to demonstrate adherence. This final step is crucial for maintaining eligibility for contracts within the Defense Industrial Base.
By adhering to these steps, organizations can methodically progress towards attaining Stage 2 alignment and improving their overall security stance, particularly given the obstacles encountered, such as the 39% of organizations that mention vendor adherence among their top three difficulties.
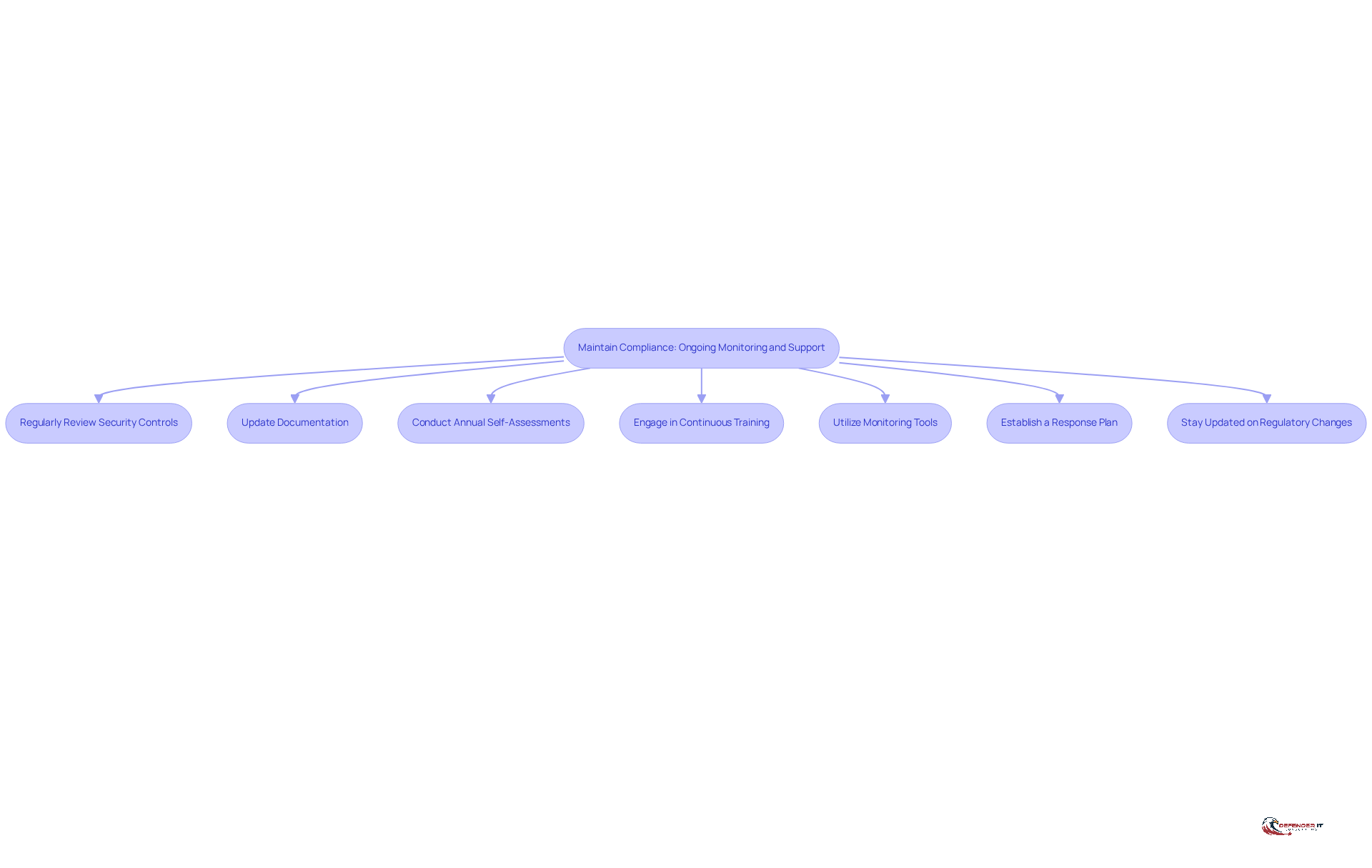
Maintain Compliance: Ongoing Monitoring and Support
Achieving CMMC Level 2 requirements requires ongoing supervision and proactive management of cybersecurity practices. Organizations should implement the following strategies:
- Regularly Review Security Controls: Conduct periodic reviews of security controls to ensure their effectiveness and alignment with CMMC requirements.
- Update Documentation: Maintain all security documentation, including the System Security Plan (SSP), to reflect any changes in practices or controls.
- Conduct Annual Self-Assessments: Perform self-assessments at least annually to evaluate compliance and identify areas for improvement.
- Engage in Continuous Training: Provide ongoing training for employees to keep them informed about the latest online security threats and best practices.
- Utilize Monitoring Tools: Implement cybersecurity monitoring tools to detect and respond to potential threats in real-time.
- Establish a Response Plan: Develop and maintain an incident response plan to address any security breaches swiftly and effectively.
- Stay Updated on Regulatory Changes: Remain aware of any modifications in security standards or related regulations to ensure continuous adherence.
By adopting these practices, organizations can ensure they meet the CMMC Level 2 requirements while enhancing their resilience against cyber threats.
Conclusion
Achieving compliance with CMMC Level 2 is not merely a regulatory requirement; it is a strategic necessity for organizations that handle Controlled Unclassified Information (CUI). Embracing this framework allows businesses to significantly enhance their cybersecurity posture, ensuring robust protection against potential data breaches while maintaining eligibility for critical Department of Defense contracts.
This article outlines essential steps for attaining CMMC Level 2 compliance. Key actions include:
- Conducting a thorough gap analysis
- Developing a remediation plan
- Implementing security controls
- Engaging in continuous training and monitoring
These measures not only mitigate risks but also foster a culture of security awareness among employees, which is vital in today’s evolving threat landscape. Organizations that prioritize compliance can experience increased customer trust and new business opportunities, positioning themselves favorably within the defense sector.
In light of impending regulatory changes and the anticipated rise in certified organizations, it is imperative for businesses to take proactive steps toward CMMC Level 2 compliance. Investing time and resources now will prepare organizations for future audits and secure their place in the defense marketplace. By prioritizing cybersecurity, organizations can safeguard sensitive information, enhance their reputation, and ensure long-term success in a competitive environment.