Introduction
In an industry where precision and efficiency are paramount, the stakes of cybersecurity incidents can be devastating for manufacturing firms. Effective incident detection and response are essential components of a resilient operational framework. This article explores best practices that empower organizations to swiftly identify and manage threats, minimizing potential damage and ensuring robust recovery.
How can manufacturing companies navigate the complexities of cyber threats while enhancing their preparedness and response capabilities?
Define Incident Detection and Response
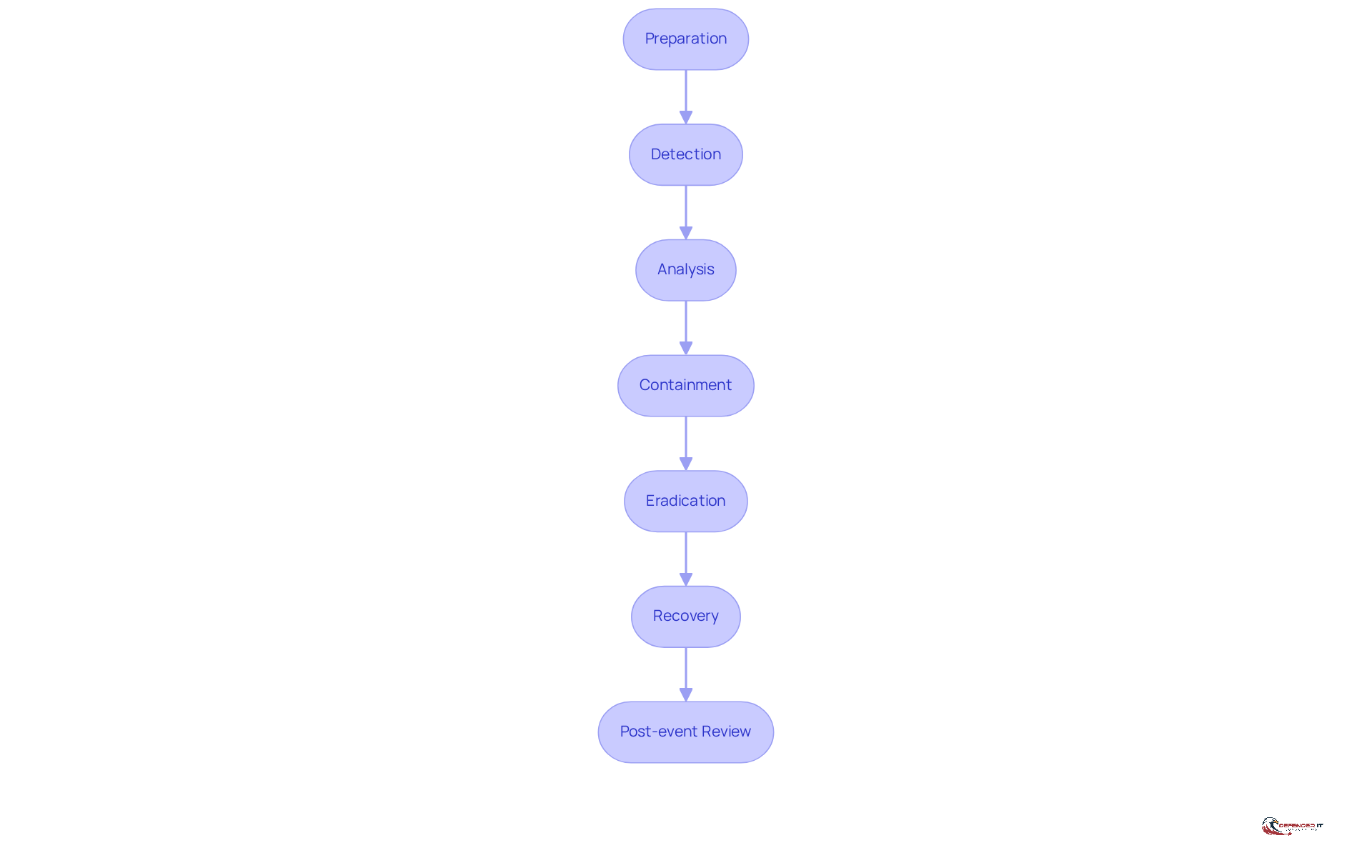
encompasses the systematic strategies organizations employ to recognize, manage, and mitigate cybersecurity incidents. In the manufacturing sector, this involves identifying threats such as , system failures, and unauthorized access to sensitive information. A well-defined occurrence management plan (OMP) is crucial, outlining the necessary actions to take when an event occurs, ensuring that all team members comprehend their roles and responsibilities. This clarity is essential for minimizing damage and facilitating a swift recovery. According to the NIST framework, effective includes:
- Preparation
- Detection
- Analysis
- Containment
- Eradication
- Recovery
- Post-event review
Real-world examples highlight the importance of in manufacturing. Organizations that conduct testing at least twice a year can reduce breach costs by an average of $1.49 million. Furthermore, those with a predetermined can decrease reaction times by 30%, underscoring the importance of organized communication during emergencies. Despite these advantages, 75% of small and medium-sized enterprises lack a , leaving them vulnerable to significant risks.
Experts stress the necessity of a . A recent report indicates that 68% of teams feel unprepared for actual cyberattacks due to insufficient practical training. This preparedness gap can lead to during incidents, with organizations averaging 258 days to identify and manage a breach. As the manufacturing industry faces increasing , the implementation of effective strategies is more critical than ever. Recent trends show a growing reliance on AI and automation to enhance situation management capabilities, with companies utilizing these technologies experiencing faster detection and shorter breach containment times. By prioritizing the development and regular revision of plans, manufacturing firms can significantly bolster their resilience against .
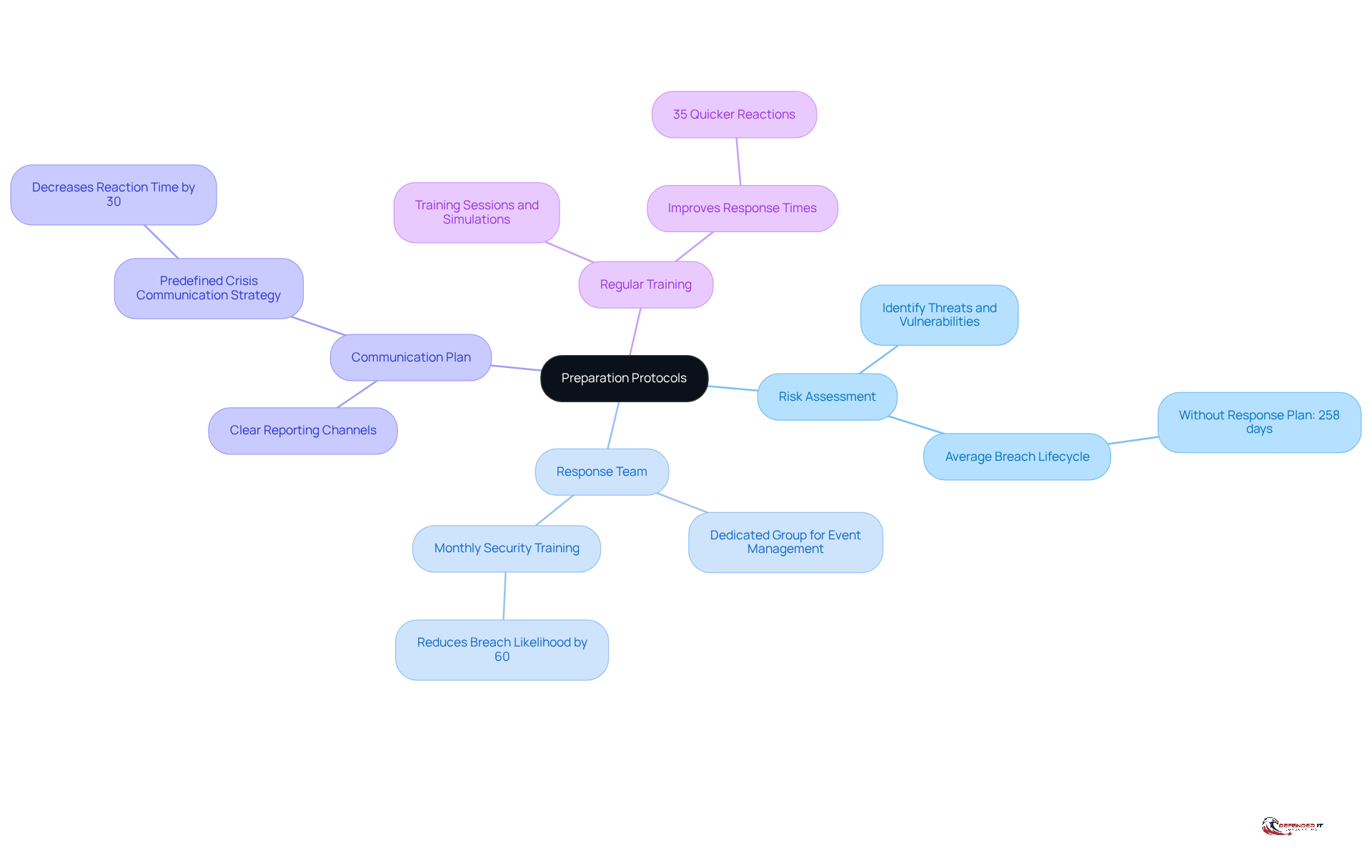
Establish Preparation Protocols
form the backbone of an effective event management strategy. Organizations must develop a comprehensive that includes personnel training, routine exercises, and clear communication pathways. The key components of preparation are as follows:
- : Identify potential threats and vulnerabilities specific to the manufacturing environment. This proactive strategy is essential; organizations without a face an average breach lifecycle of 258 days.
- : Establish a dedicated group responsible for managing events, ensuring they have the necessary training and resources. Companies that conduct monthly security training can reduce the likelihood of breaches by 60%, highlighting the importance of .
- Communication Plan: Create clear channels for reporting events and sharing information during a crisis. Organizations with a predefined can decrease reaction time by 30%.
- : Implement training sessions and simulations to ensure all employees understand the occurrence management plan and their roles within it. not only enhance readiness but also significantly improve response times, with entities that perform such exercises reacting 35% quicker to situations.
By investing time in preparation, companies can substantially reduce the time required for , ultimately minimizing potential harm.
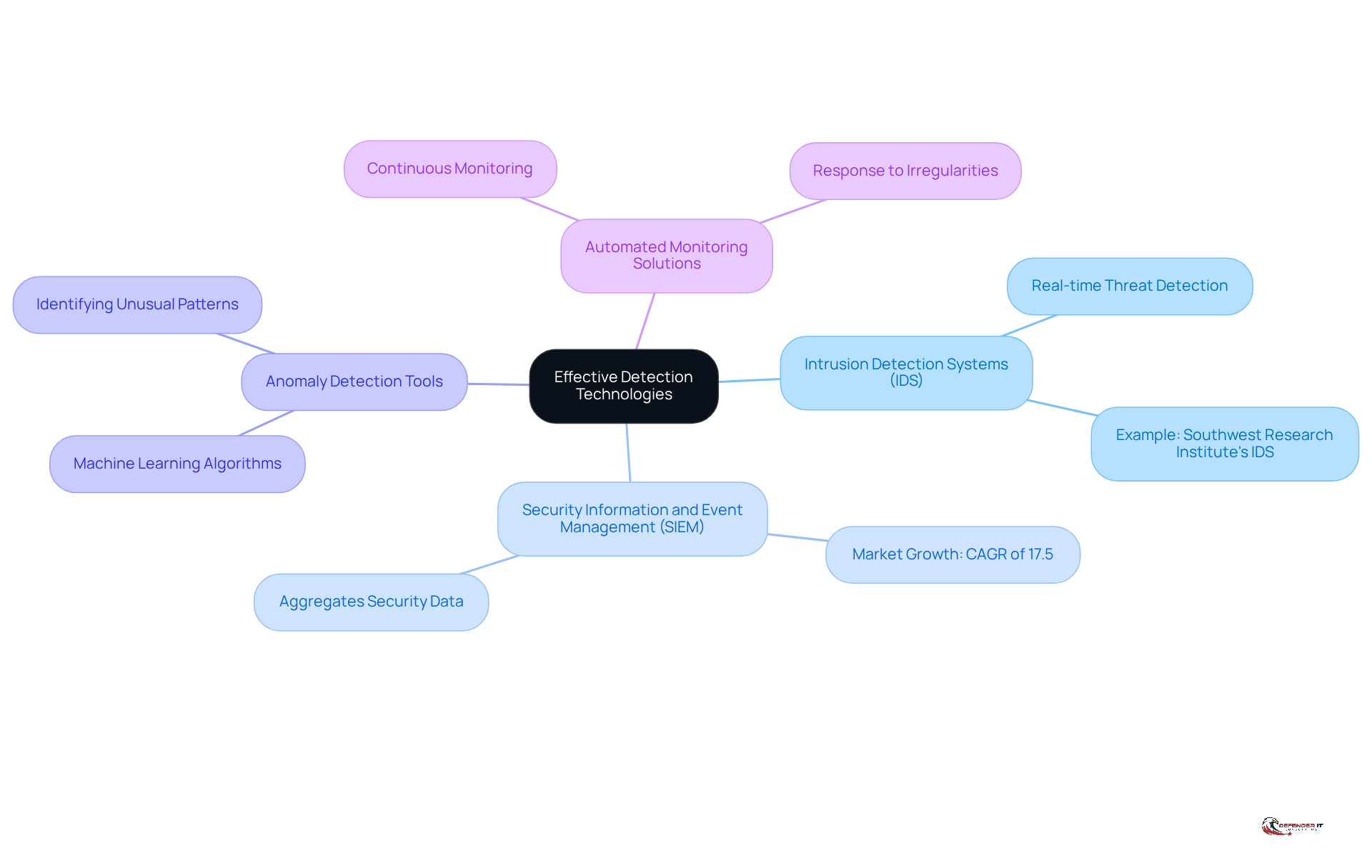
Implement Effective Detection Technologies
To effectively identify occurrences, organizations must leverage advanced technologies tailored to their specific needs. Key technologies include:
- monitor network traffic for suspicious activity, supporting the team by alerting them to potential threats. For example, the Southwest Research Institute developed an IDS specifically for industrial control systems, significantly enhancing the security of critical infrastructure by detecting cyber threats in real-time.
- : SIEM solutions aggregate and analyze security data from across the organization, facilitating real-time identification of potential threats. The global SIEM market is projected to grow at a CAGR of 17.5% from 2024 to 2033, underscoring the increasing reliance on these technologies in manufacturing.
- : Utilizing machine learning algorithms, these tools identify unusual patterns that may signal a security breach. As organizations increasingly adopt AI-driven defenses, the effectiveness of these tools in detecting sophisticated threats becomes crucial.
- Automated Monitoring Solutions: provide notifications for any irregularities or breaches, ensuring that organizations can respond promptly to incidents. With approximately , the implementation of is essential for maintaining a robust security posture.
By integrating these technologies, organizations can significantly enhance their ability to identify issues early, leading to faster response times and minimized impact on operations.
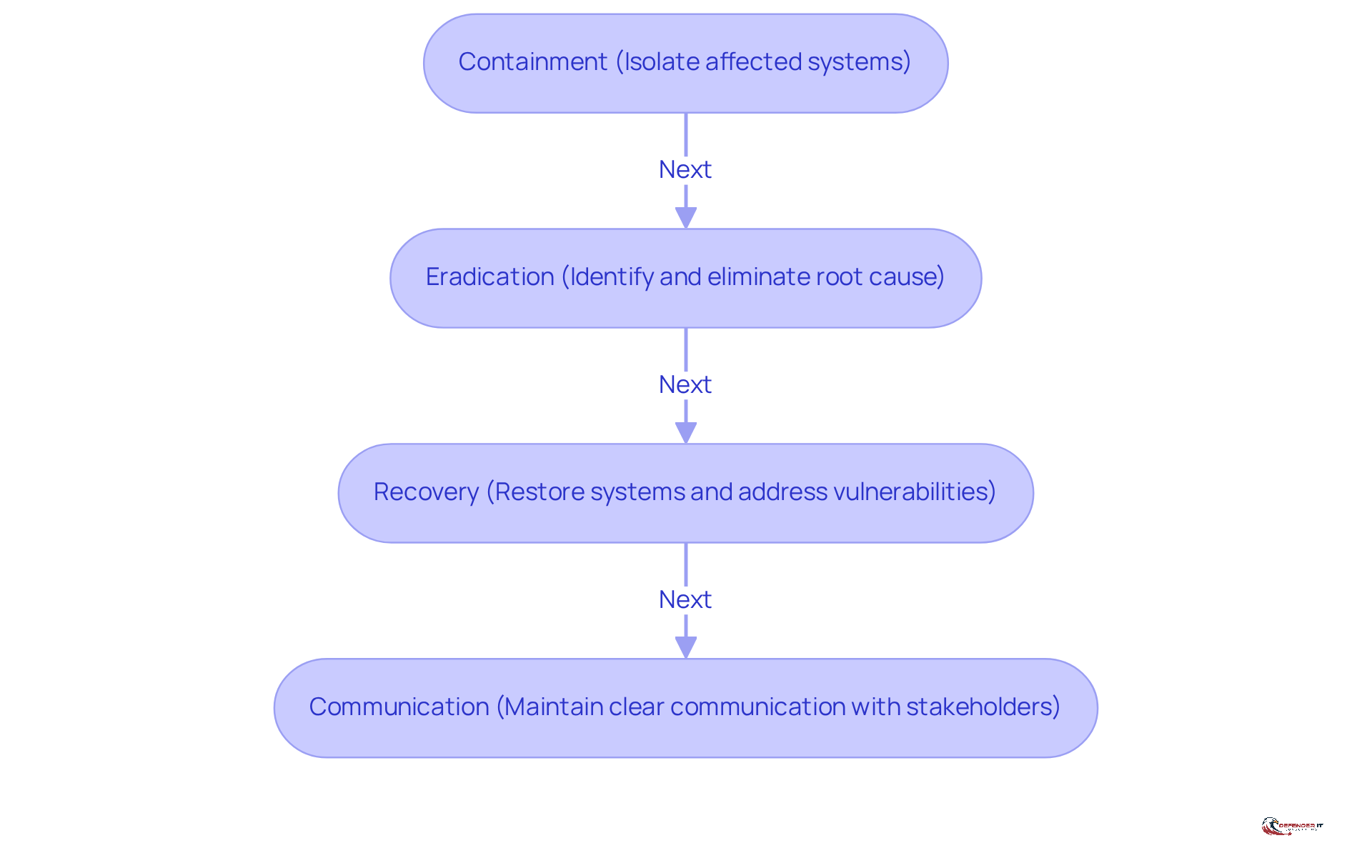
Adopt Comprehensive Response Strategies
Effectively managing with is essential, particularly in the manufacturing sector where is paramount. A comprehensive strategy encompasses several key elements:
- Containment: Rapid isolation of affected systems is vital to prevent further damage. This step is critical, as 36% of firms have experienced that required immediate action due to cybersecurity issues.
- Eradication: Identifying and eliminating the root cause of incidents is necessary to prevent recurrence. Efficient eradication strategies significantly reduce the likelihood of future occurrences; indeed, 31% of manufacturing organizations prioritize enhancing their readiness for events and recovery capabilities.
- Recovery: Restoring systems to normal operation while addressing all vulnerabilities is crucial. Organizations must ensure that their are robust enough to handle the complexities of modern , especially considering that 40% of manufacturing firms reported phishing or vishing incidents in the past year.
- Communication: Maintaining with stakeholders throughout the response process is vital for managing expectations and providing timely updates. This and ensures that all parties are informed about the measures being implemented to address the situation.
Implementing these strategies not only minimizes downtime but also protects essential assets, thereby enhancing the organization’s resilience against future . The cyber attack on Jaguar Land Rover, which disrupted over 2,700 entities, underscores the importance of having a well-defined plan for to address such incidents. By integrating these practices, manufacturing firms can strengthen their cybersecurity posture and protect their operations.
Conduct Post-Incident Reviews and Improvements
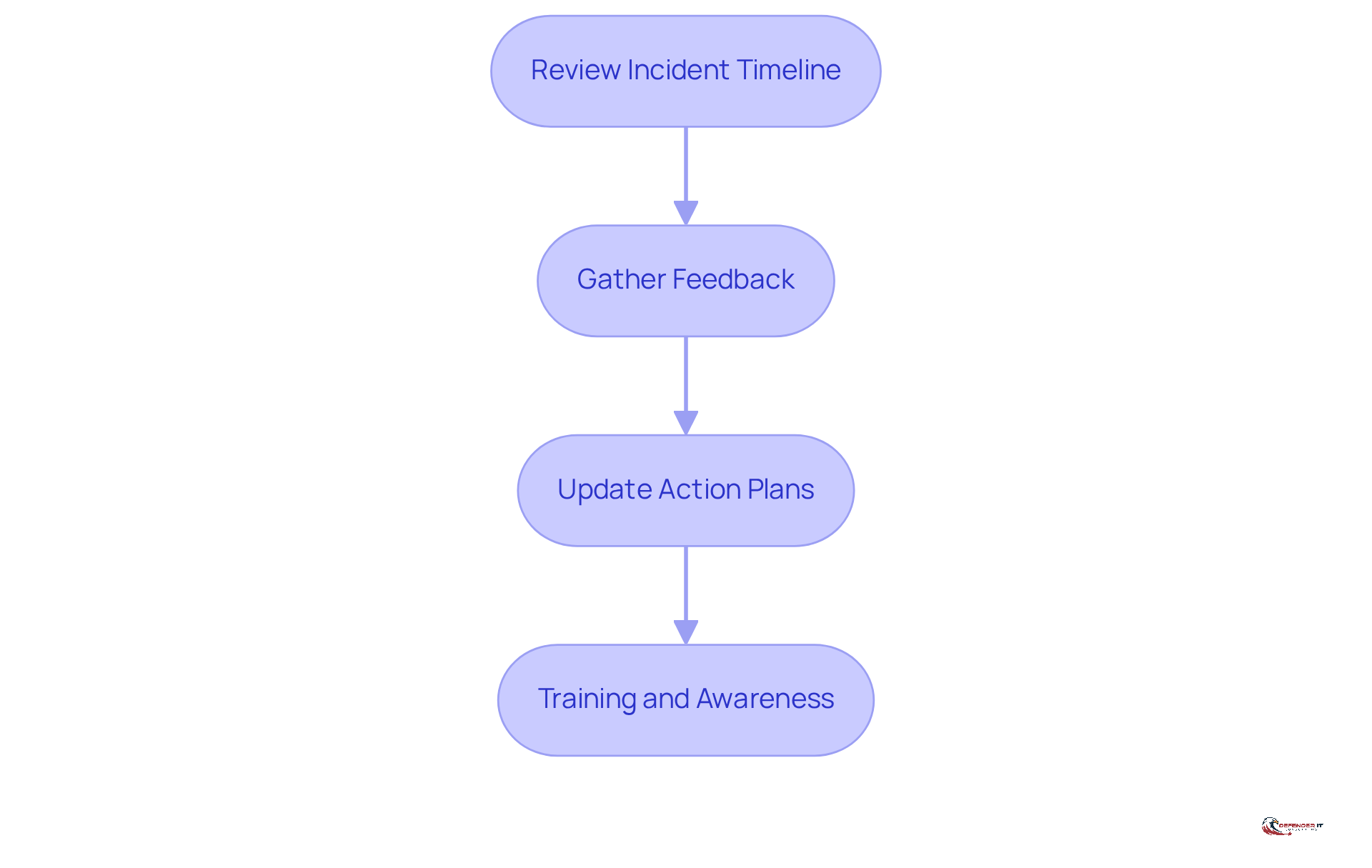
Post-event evaluations are essential for understanding occurrences and refining strategic approaches. The key steps in this process include:
- Review Incident Timeline: Analyzing the sequence of events allows organizations to pinpoint effective actions and identify areas for improvement. This structured approach helps highlight critical moments that influenced the event’s outcome.
- : Collecting insights from all team members involved in managing the situation fosters a blame-free environment, promoting open dialogue. Diverse perspectives enrich the review process, ensuring that all operational aspects are thoroughly considered.
- : The insights gained should directly inform modifications to , aligning them with current threats and organizational objectives. This proactive approach enhances readiness for future events, ensuring that plans remain relevant and effective.
- : Insights from evaluations should inform , enhancing overall organizational awareness of . Continuous education ensures that teams are well-equipped to address evolving effectively.
By conducting comprehensive , organizations can systematically refine their , significantly bolstering their resilience against future incidents.
Conclusion
Implementing effective incident detection and response practices is crucial for the manufacturing sector, where the repercussions of cyber threats can be significant. A comprehensive approach that encompasses preparation, advanced detection technologies, and robust response strategies is essential for safeguarding operations and minimizing disruptions. By understanding and applying these best practices, organizations can markedly enhance their resilience against potential cyber incidents.
Key insights from the article underscore the importance of preparation protocols, such as:
- Risk assessments
- Regular training
These can lead to quicker response times and diminished breach impacts. The integration of advanced detection technologies, including:
- Intrusion Detection Systems
- Security Information and Event Management solutions
further fortifies an organization’s capacity to identify threats early. Moreover, adopting comprehensive response strategies ensures that organizations can manage incidents effectively, thereby maintaining operational continuity and trust among stakeholders.
Ultimately, the significance of a proactive stance in incident detection and response cannot be overstated. Manufacturing firms must prioritize the development and continual refinement of their crisis management plans to adapt to evolving cyber threats. By fostering a culture of preparedness and leveraging modern technologies, organizations can not only protect their assets but also secure a more stable future for the manufacturing industry as a whole.
Frequently Asked Questions
What is incident detection and response in cybersecurity?
Incident detection and response involves systematic strategies that organizations use to recognize, manage, and mitigate cybersecurity incidents, including threats like data breaches and unauthorized access.
Why is an occurrence management plan (OMP) important?
An OMP outlines actions to take during an event, ensuring all team members understand their roles, which minimizes damage and facilitates a swift recovery.
What are the key components of effective incident detection and response according to the NIST framework?
The key components include preparation, detection, analysis, containment, eradication, recovery, and post-event review.
How can crisis management testing impact breach costs?
Organizations that conduct crisis management testing at least twice a year can reduce breach costs by an average of $1.49 million.
What is the significance of having a crisis communication plan?
A predefined crisis communication plan can decrease reaction times by 30%, which is crucial for organized communication during emergencies.
What percentage of small and medium-sized enterprises lack a cybersecurity emergency plan?
75% of small and medium-sized enterprises do not have a cybersecurity emergency plan, leaving them vulnerable to risks.
What do experts say about the preparedness of crisis management teams?
A report indicates that 68% of crisis management teams feel unprepared for actual cyberattacks due to insufficient practical training.
How long do organizations typically take to identify and manage a breach?
Organizations average 258 days to identify and manage a breach.
What role does AI and automation play in incident detection and response?
Companies utilizing AI and automation experience faster detection and shorter breach containment times, enhancing their situation management capabilities.
What are the key components of preparation protocols for incident management?
Key components include risk assessment, establishing a response team, creating a communication plan, and implementing regular training.
How does regular training impact an organization’s response to incidents?
Regular training and simulations significantly improve readiness and response times, with entities that perform drills reacting 35% quicker to situations.
What is the average breach lifecycle for organizations without a documented response plan?
Organizations without a documented response plan face an average breach lifecycle of 258 days.
List of Sources
- Define Incident Detection and Response
- Incident Response Statistics to Know in 2025 (https://jumpcloud.com/blog/incident-response-statistics)
- Manufacturers fortify cyber defenses in response to dramatic surge in attacks (https://cybersecuritydive.com/news/manufacturing-sector-cyber-threats-collaboration-ransomware/810930)
- CISA Shares Lessons Learned from an Incident Response Engagement | CISA (https://cisa.gov/news-events/cybersecurity-advisories/aa25-266a)
- 205 Cybersecurity Stats and Facts for 2026 (https://vikingcloud.com/blog/cybersecurity-statistics)
- Establish Preparation Protocols
- 29 Cybersecurity Quotes to Protect Your Digital Life (https://acecloudhosting.com/blog/cybersecurity-quotes)
- The State of Manufacturing Employee Training Report [2023] | Poka (https://poka.io/en/blog/the-state-of-training-in-manufacturing)
- Incident Response Statistics to Know in 2025 (https://jumpcloud.com/blog/incident-response-statistics)
- CISA Shares Lessons Learned from an Incident Response Engagement | CISA (https://cisa.gov/news-events/cybersecurity-advisories/aa25-266a)
- frsecure.com (https://frsecure.com/blog/incident-response-statistics-how-do-you-compare)
- Implement Effective Detection Technologies
- Security Information and Event Management (SIEM) Market 2033 (https://custommarketinsights.com/report/security-information-and-event-management-siem-market)
- Top Cybersecurity Statistics: Facts, Stats and Breaches for 2025 (https://fortinet.com/resources/cyberglossary/cybersecurity-statistics)
- Cybersecurity Awareness Month Quotes and Commentary from Industry Experts in 2025 (https://solutionsreview.com/cybersecurity-awareness-month-quotes-and-commentary-from-industry-experts-in-2025)
- SwRI develops cyber security intrusion detection system for industrial control systems | Southwest Research Institute (https://swri.org/newsroom/press-releases/swri-develops-cybersecurity-intrusion-detection-system-industrial-control-systems)
- CISA Shares Lessons Learned from an Incident Response Engagement | CISA (https://cisa.gov/news-events/cybersecurity-advisories/aa25-266a)
- Adopt Comprehensive Response Strategies
- Manufacturers fortify cyber defenses in response to dramatic surge in attacks (https://cybersecuritydive.com/news/manufacturing-sector-cyber-threats-collaboration-ransomware/810930)
- Cybersecurity Facts and Stats as of 2026 (https://preveil.com/blog/cybersecurity-statistics)
- State of Information Security Report: 11 Key Statistics and Trends for the Manufacturing and Utilities Industry (https://isms.online/information-security/state-of-information-security-report-11-key-statistics-and-trends-for-the-manufacturing-and-utilities-industry)
- IBM X-Force 2025 Threat Intelligence Index (https://ibm.com/thought-leadership/institute-business-value/en-us/report/2025-threat-intelligence-index)
- CISA Shares Lessons Learned from an Incident Response Engagement | CISA (https://cisa.gov/news-events/cybersecurity-advisories/aa25-266a)
- Conduct Post-Incident Reviews and Improvements
- Post-Incident After-Action Reviews Are Critical to Building Organizational Resilience, Says McLean & Company (https://prnewswire.com/news-releases/post-incident-after-action-reviews-are-critical-to-building-organizational-resilience-says-mclean–company-302674415.html)
- Incident prevention: the power of an effective post incident review (https://woodwing.com/blog/the-power-of-effective-post-incident-reviews)
- How to conduct an effective post-incident review (https://csoonline.com/article/4009438/how-to-conduct-an-effective-post-incident-review.html)
- CISA Shares Lessons Learned from an Incident Response Engagement | CISA (https://cisa.gov/news-events/cybersecurity-advisories/aa25-266a)
- Building the Perfect Post-Security Incident Review Playbook (https://darkreading.com/cybersecurity-operations/perfect-post-security-incident-review-playbook)