Introduction
In an era marked by increasingly sophisticated cyber threats, organizations are tasked with the critical responsibility of safeguarding their digital assets. A well-structured cyber security vulnerability assessment serves not only to identify potential weaknesses but also to empower businesses to effectively fortify their defenses. Alarmingly, 80% of companies fail to address new vulnerabilities in a timely manner. This raises an important question: how can organizations implement best practices to ensure a successful and ongoing vulnerability assessment process?
This article explores essential steps, prioritization strategies, and remediation techniques that can elevate vulnerability assessments from routine tasks to robust defense mechanisms against evolving cyber threats.
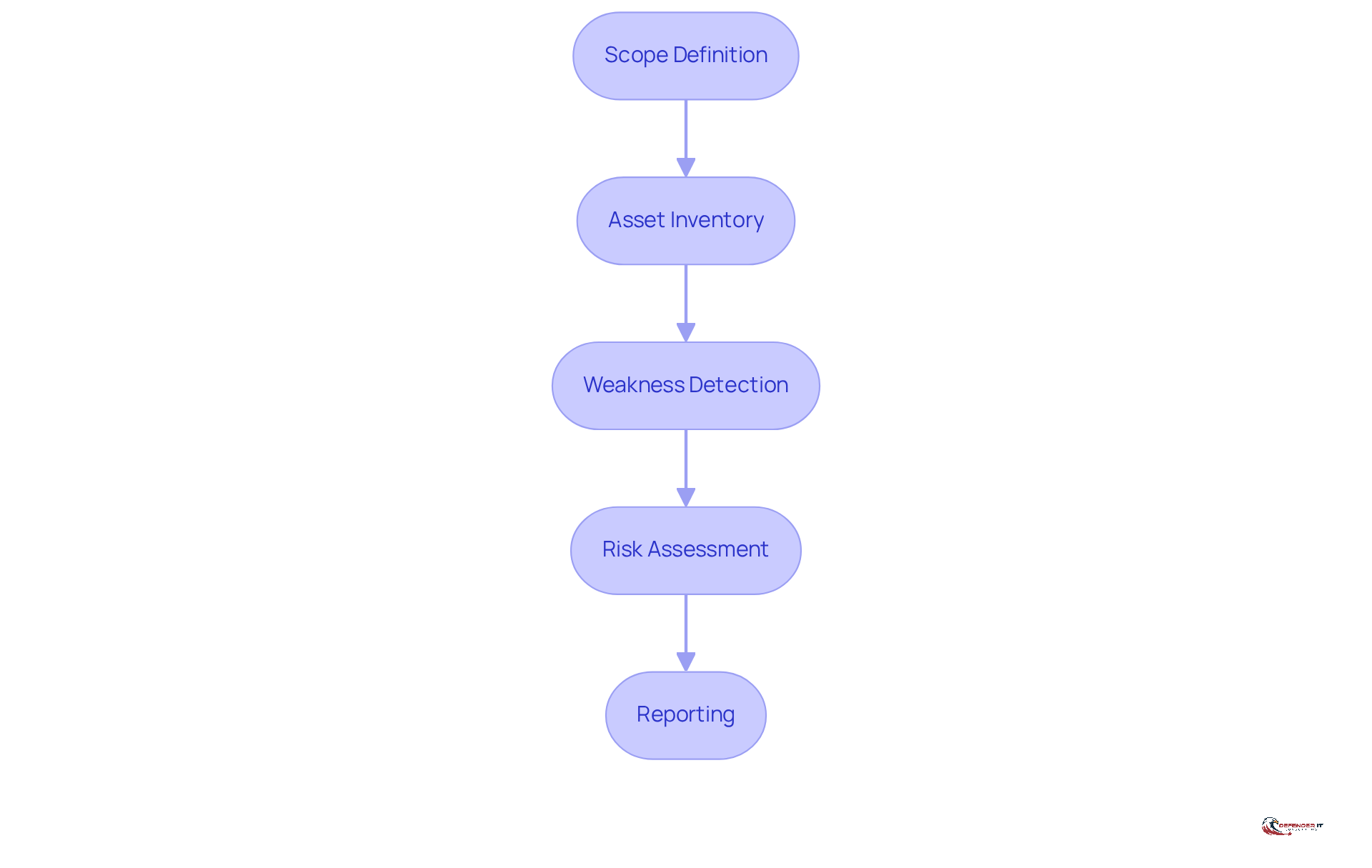
Define the Vulnerability Assessment Process
A is a systematic process designed to identify and mitigate security risks effectively. This process involves several key steps:
- : The first step is to clearly define the assessment’s scope, specifying the systems, networks, and applications to be evaluated. This initial step is crucial as it sets the boundaries for the assessment and ensures that all critical assets are included.
- : Next, create a comprehensive inventory of all assets within the defined scope, encompassing hardware, software, and data. This inventory serves as the foundation for recognizing potential weaknesses.
- : Utilize a combination of automated tools and manual methods to within the assets. Continuous testing is essential, as it keeps risk visibility current and adapts to changes in the environment.
- : Evaluate the potential impact and likelihood of exploitation for each identified weakness. This step assists in prioritizing weaknesses based on their severity and the possible outcomes of an attack.
- Reporting: Finally, that outlines weaknesses, their severity, and recommended remediation steps. Effective reporting ensures that leaders in protection receive timely, actionable insights, facilitating prompt remediation efforts.
By adhering to this systematic method, organizations can conduct a to thoroughly evaluate their , allowing them to prioritize weaknesses efficiently. For instance, a recent case study highlighted that organizations with developed programs experienced a , demonstrating the effectiveness of systematic evaluations. Furthermore, statistics reveal that 80% of companies fail to address new vulnerabilities within the first 1.5 years after the initial scan, underscoring the necessity of regular assessments to maintain a robust . As Dan DeCloss, founder of PlexTrac, states, ‘Security leaders no longer view penetration tests as one-off engagements that end with a PDF.’ This shift emphasizes the need for .
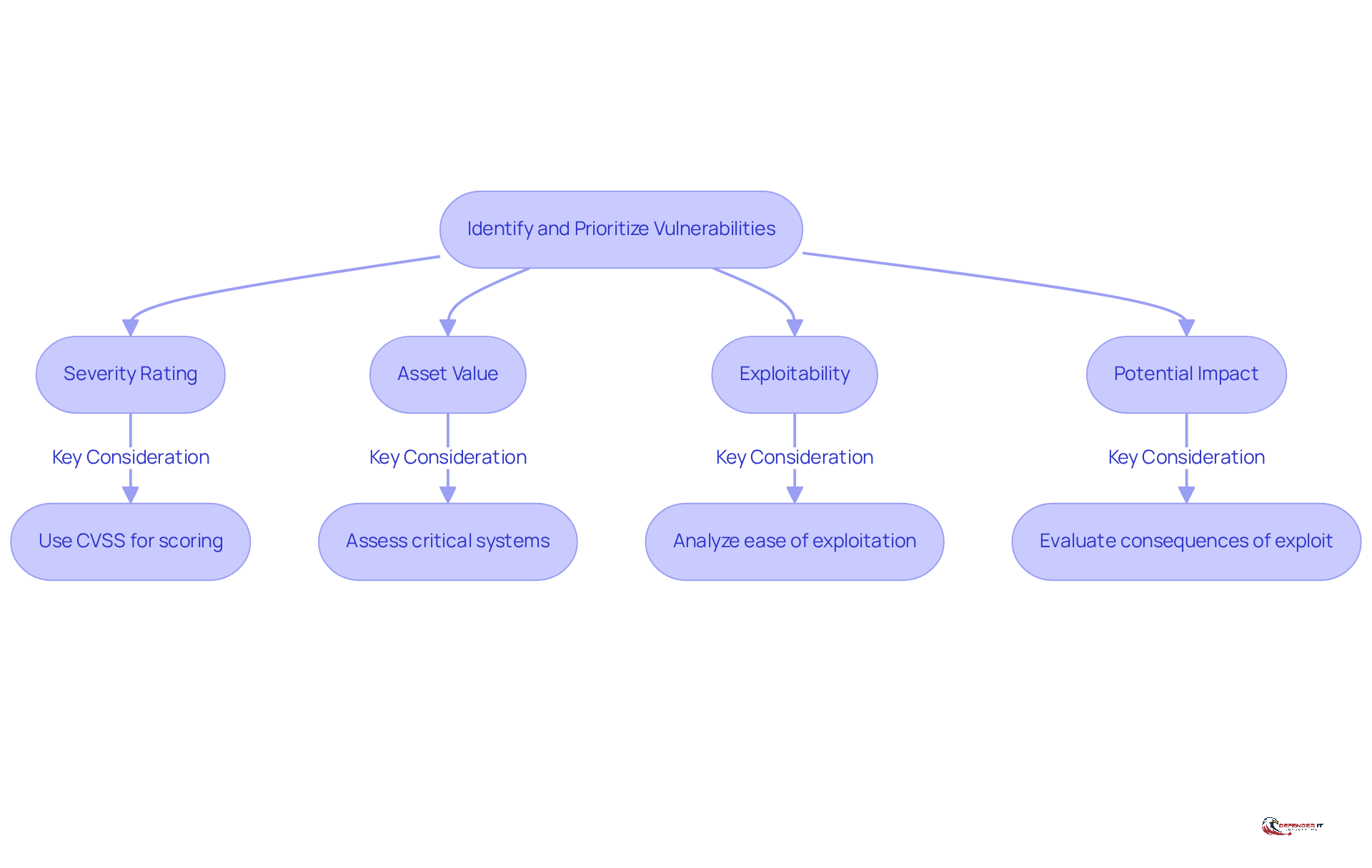
Identify and Prioritize Vulnerabilities
Recognizing weaknesses is just the first step; effectively prioritizing them is crucial for enhancing and overall cybersecurity resilience. This process hinges on several key factors:
- Severity Rating: Employ established scoring systems, such as the , to evaluate the severity of each flaw. Revisions to the CVSS scoring system in 2026 underscore the need for a nuanced understanding of vulnerabilities, particularly in light of evolving . For instance, while over 40,000 flaws were reported in 2024, fewer than 10% were actually exploited, highlighting the importance of .
- Asset Value: Assess the significance of the affected asset to the organization. Critical systems, such as those involved in identity management or CI/CD pipelines, should be prioritized over less essential assets, as weaknesses in these areas can lead to cascading impacts on overall security.
- Exploitability: Analyze how easily a weakness can be exploited by attackers. , particularly those associated with high-risk components, should be addressed as a priority to avert potential breaches. Recent vulnerabilities listed in the illustrate the urgency of addressing specific threats.
- Potential Impact: Evaluate the of a successful exploit, including financial losses, reputational damage, and regulatory repercussions. Understanding the enables organizations to make informed decisions regarding . CISA emphasizes the importance of promptly addressing weaknesses identified in a as part of effective .
By adopting a risk-oriented strategy for prioritizing weaknesses, organizations can allocate resources more effectively, focusing on the most critical threats. This approach not only strengthens their protective posture but also aligns with best practices in risk management, ensuring that organizations remain resilient against the ever-evolving landscape of .
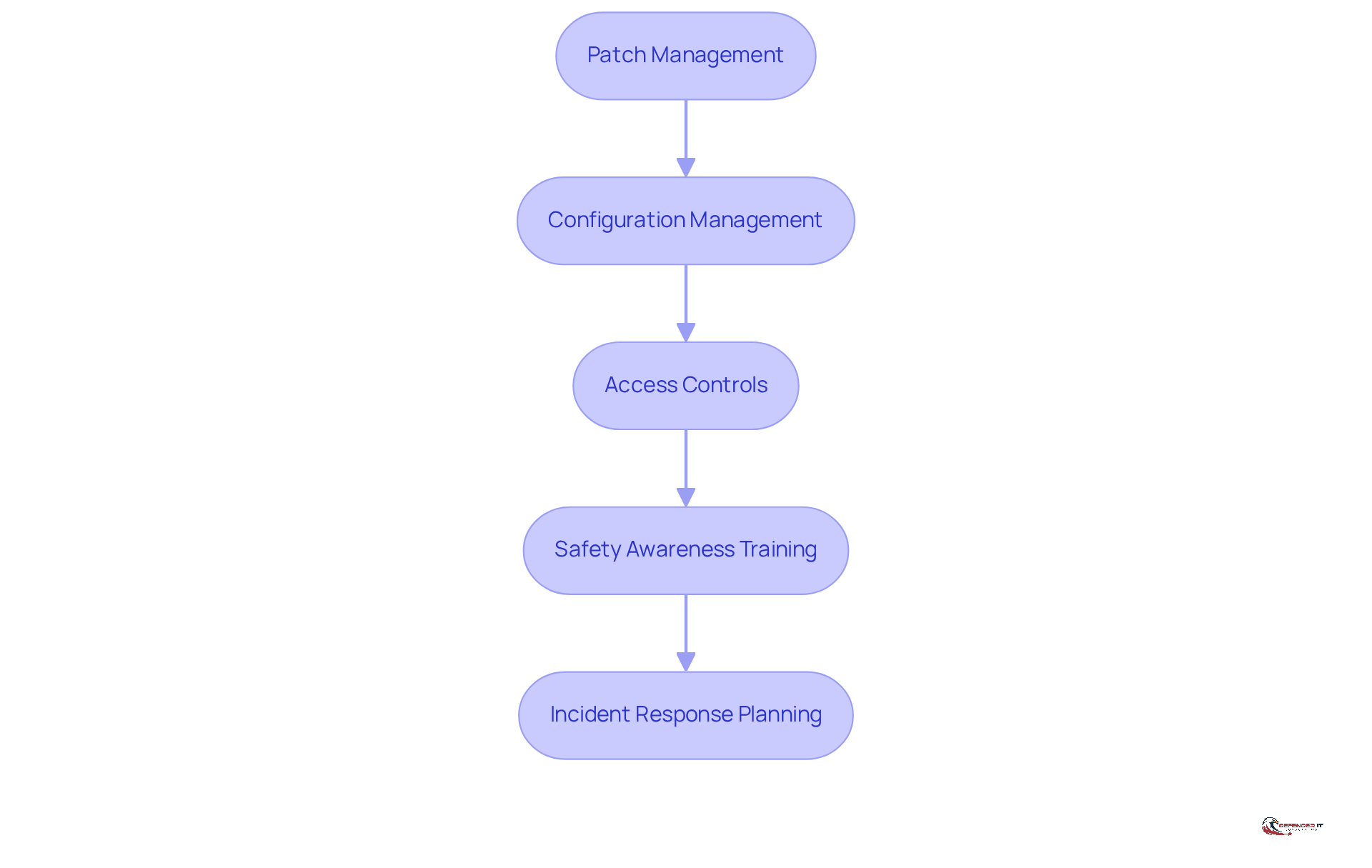
Implement Effective Remediation Strategies
To effectively remediate vulnerabilities, organizations should adopt the following strategies:
- : Regularly apply security patches and updates to software and systems to close known vulnerabilities. In 2025, ransomware assaults surged, with over 2,200 victims reported in just one quarter. This underscores the critical importance of to mitigate such risks. Effective not only reduces the attack surface but also reinforces client trust in an organization’s cybersecurity capabilities.
- : Ensure that systems are configured securely in accordance with industry best practices and organizational policies.
- : Implement strict to limit user permissions based on the principle of least privilege.
- : Educate staff on best practices and the significance of identifying potential threats.
- : Develop and maintain an incident response plan to swiftly address any security breaches that may occur.
By adopting these remediation strategies, organizations can significantly reduce their risk exposure and enhance their overall , particularly through a .
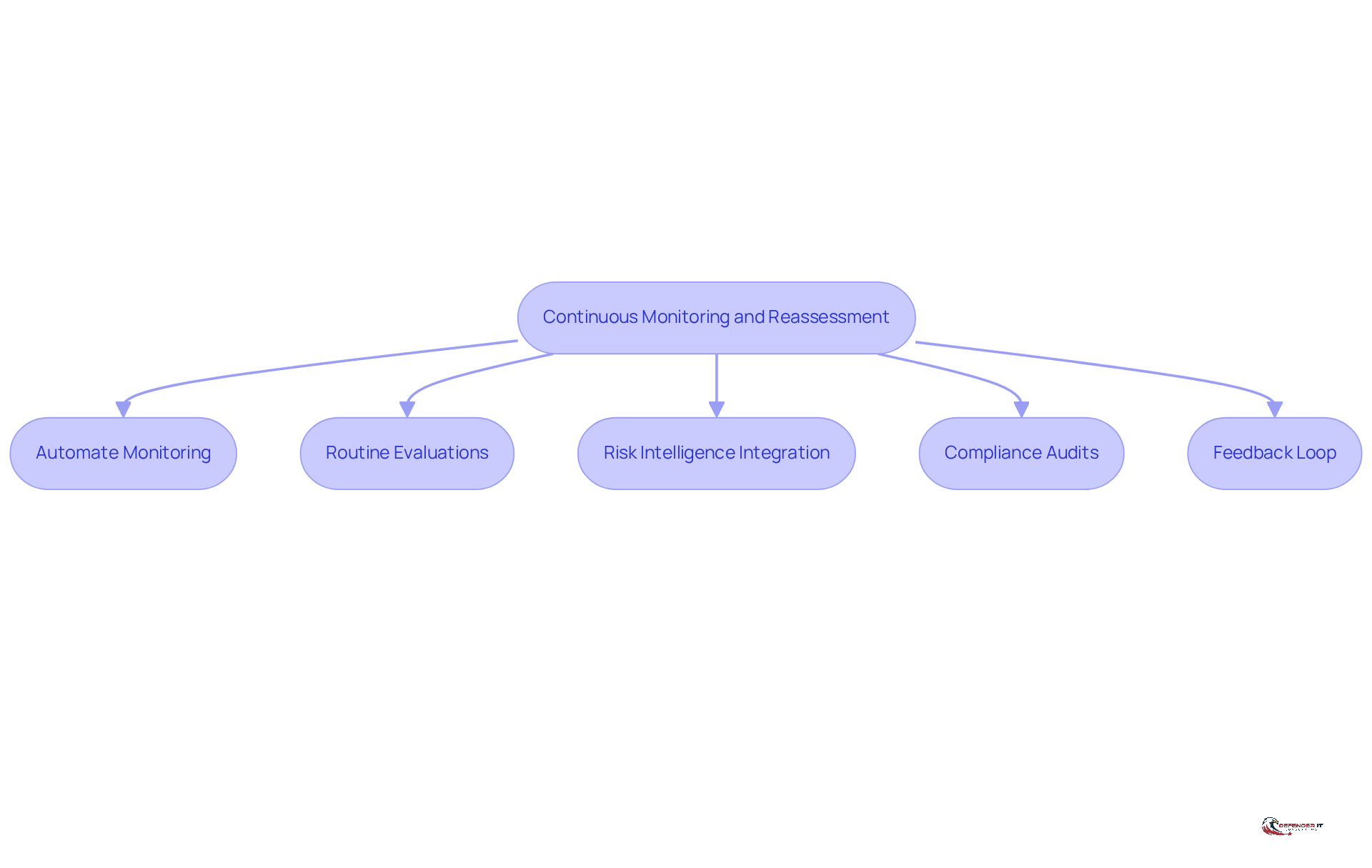
Establish Continuous Monitoring and Reassessment
and reassessment are essential elements of a robust cybersecurity strategy. Organizations should adopt the following practices:
- : Utilize automated tools to continuously scan for vulnerabilities and monitor changes in the IT environment.
- Routine evaluations should involve conducting a to identify new vulnerabilities and reassess existing ones.
- Risk Intelligence Integration: Incorporate to remain informed about .
- : Perform regular audits to ensure adherence to industry regulations and internal policies.
- : Establish a to learn from past incidents and enhance the .
By implementing and reassessment, organizations can enhance their to maintain a , ensuring that their security measures evolve in tandem with the changing threat landscape.
Conclusion
A comprehensive cyber security vulnerability assessment is essential for organizations seeking to protect their digital assets from evolving threats. By systematically identifying and mitigating risks, organizations can strengthen their security posture and effectively address vulnerabilities as they arise. This assessment process not only uncovers weaknesses but also highlights the necessity of prioritizing these vulnerabilities based on their potential impact and exploitability.
Key strategies include:
- Establishing a clear vulnerability assessment process
- Prioritizing weaknesses according to severity and asset value
- Implementing effective remediation techniques such as patch management and access controls
Furthermore, the importance of continuous monitoring and reassessment cannot be overstated, as it ensures that organizations remain vigilant and proactive in their defense strategies.
Ultimately, adopting these best practices in cyber security vulnerability assessment is crucial for building resilience against cyber threats. Organizations that prioritize regular assessments and embrace a proactive approach to risk management will not only safeguard their assets but also foster trust with clients and stakeholders. The time to act is now-implement these strategies to strengthen defenses and stay ahead in the ever-evolving landscape of cyber security.
Frequently Asked Questions
What is the purpose of a cyber security vulnerability assessment?
A cyber security vulnerability assessment is a systematic process designed to identify and mitigate security risks effectively within an organization.
What are the key steps involved in the vulnerability assessment process?
The key steps include: 1. Scope Definition: Clearly defining the assessment’s scope. 2. Asset Inventory: Creating a comprehensive inventory of all assets. 3. Weakness Detection: Using automated tools and manual methods to uncover weaknesses. 4. Risk Assessment: Evaluating the impact and likelihood of exploitation for identified weaknesses. 5. Reporting: Documenting findings in a clear and actionable report.
Why is scope definition important in the vulnerability assessment process?
Scope definition is crucial as it sets the boundaries for the assessment and ensures that all critical assets are included in the evaluation.
How is an asset inventory created in a vulnerability assessment?
An asset inventory is created by compiling a comprehensive list of all hardware, software, and data within the defined scope of the assessment.
What methods are used to detect weaknesses in assets?
Weakness detection involves utilizing a combination of automated tools and manual methods to uncover vulnerabilities within the assets.
How is risk assessed during the vulnerability assessment?
Risk is assessed by evaluating the potential impact and likelihood of exploitation for each identified weakness, which helps prioritize them based on severity.
What should be included in the reporting phase of the vulnerability assessment?
The reporting phase should include documented findings that outline weaknesses, their severity, and recommended remediation steps.
Why is continuous testing important in vulnerability assessments?
Continuous testing is essential as it keeps risk visibility current and adapts to changes in the environment, ensuring ongoing security.
What does the statistic about companies failing to address vulnerabilities indicate?
The statistic reveals that 80% of companies fail to address new vulnerabilities within the first 1.5 years after the initial scan, highlighting the necessity of regular assessments to maintain a robust security posture.
How has the perspective on penetration tests changed according to Dan DeCloss?
Dan DeCloss notes that security leaders now view penetration tests as ongoing engagements rather than one-off activities, emphasizing the need for continuous risk management as part of a comprehensive cybersecurity strategy.
List of Sources
- Define the Vulnerability Assessment Process
- BOD 26-02: Mitigating Risk From End-of-Support Edge Devices | CISA (https://cisa.gov/news-events/directives/bod-26-02-mitigating-risk-end-support-edge-devices)
- NIST is rethinking its role in analyzing software vulnerabilities (https://cybersecuritydive.com/news/nist-cve-vulnerability-analysis-nvd-review/810300)
- CISA Shares Lessons Learned from an Incident Response Engagement | CISA (https://cisa.gov/news-events/cybersecurity-advisories/aa25-266a)
- The 2026 State of Pentesting: How Modern Teams Manage and Deliver Results (https://thehackernews.com/expert-insights/2026/01/the-2026-state-of-pentesting-how-modern.html)
- 35 Cyber Security Vulnerability Statistics, Facts In 2026 (https://getastra.com/blog/security-audit/cyber-security-vulnerability-statistics)
- Identify and Prioritize Vulnerabilities
- CTEM in Practice: Prioritization, Validation, and Outcomes That Matter (https://thehackernews.com/2026/01/ctem-in-practice-prioritization.html)
- Vulnerability prioritization beyond the CVSS number (https://csoonline.com/article/4119130/vulnerability-prioritization-beyond-the-cvss-number.html)
- CISA Adds Six Known Exploited Vulnerabilities to Catalog | CISA (https://cisa.gov/news-events/alerts/2026/02/10/cisa-adds-six-known-exploited-vulnerabilities-catalog)
- The Top Cybersecurity Threats in 2026 & How to Prevent Them | Prime Secured (https://primesecured.com/top-cybersecurity-threats-2026-and-prevention)
- Vulnerability Statistics Report (https://edgescan.com/stats-report)
- Implement Effective Remediation Strategies
- Importance of Patch Management for Ransomware Protection | Splashtop (https://splashtop.com/blog/patch-management-ransomware-protection)
- forbes.com (https://forbes.com/sites/chuckbrooks/2025/12/31/what-every-company-needs-to-know-about-cybersecurity-in-2026)
- 2026 Cybersecurity Predictions | ConnectWise (https://connectwise.com/blog/2026-cybersecurity-predictions)
- Cyber Resilience 2026 | Proactive Defense Against Online Threats (https://trustcloud.ai/risk-management/fortify-cyber-resilience-unstoppable-defense-strategies-for-2025)
- Establish Continuous Monitoring and Reassessment
- RMF Continuous Monitoring Strategy [for 2026] (https://ipkeys.com/blog/rmf-continuous-monitoring)
- Cybersecurity Trends Shaping Defense Contracting in 2026 (https://securestrux.com/resources/insights/cybersecurity-trends-that-might-shape-defense-contracting-in-2026)
- Threat and Vulnerability Management in 2026 (https://recordedfuture.com/blog/threat-and-vulnerability-management)
- Cyber Security Best Practices for 2026 (https://sentinelone.com/cybersecurity-101/cybersecurity/cyber-security-best-practices)