Introduction
In an era marked by escalating cyber threats, the manufacturing sector stands at a pivotal crossroads. Cyberattacks are increasingly prevalent, posing significant risks of operational disruptions. Consequently, industry leaders must prioritize the implementation of robust cybersecurity measures. This article examines nine essential Managed Security Service Provider (MSSP) services specifically designed for the manufacturing industry. These services not only fortify defenses but also enhance compliance and protect both operations and intellectual property. Given the multitude of options available, how can manufacturing leaders discern which services are truly indispensable in combating the ever-evolving landscape of cyber threats?
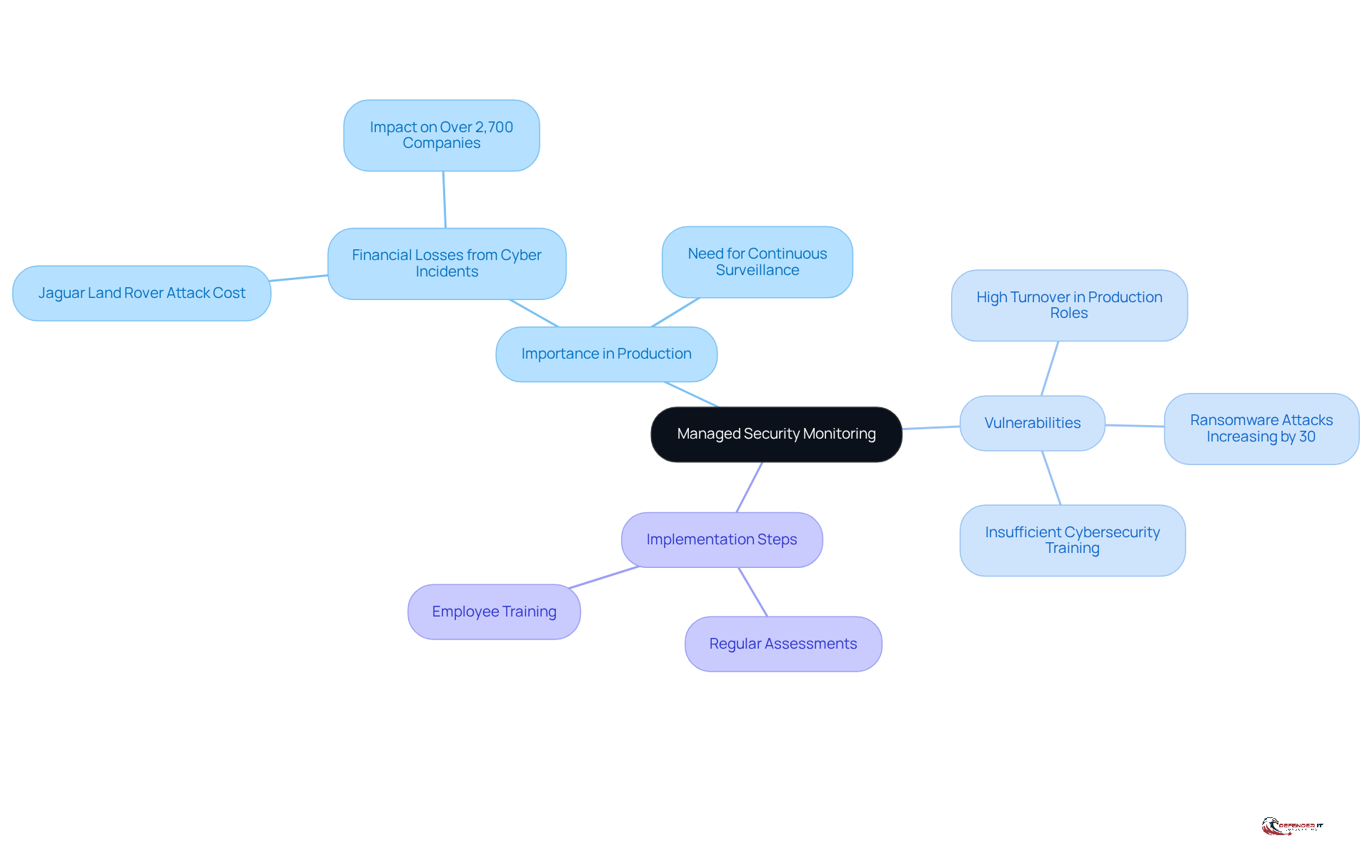
Defenderit Consulting: Managed Security Monitoring
(MSM) serves as a cornerstone service offered by , which utilizes a to focus on the of an organization’s IT infrastructure to detect and respond to potential threats. By leveraging advanced technologies and skilled analysts, a enables industry leaders to maintain a robust security posture, thereby minimizing the risk of cyber incidents that could disrupt operations. This service is particularly crucial in the production industry, where downtime can result in significant financial losses. For instance, the recent cyberattack on Jaguar Land Rover incurred approximately $2.5 billion in costs and affected over 2,700 companies, underscoring the financial ramifications of cyber incidents within production.
The production sector is notably vulnerable to , with increasing by 30% annually. not only facilitates the early detection of threats but also bolsters , ensuring organizations can swiftly mitigate risks. Experts emphasize the necessity of ongoing monitoring in production cybersecurity, asserting that insufficient oversight and varying cybersecurity maturity among partners create a broad attack surface that [cyber security MSSP](https://msspalert.com) must address. Furthermore, they highlight that the lack of consistent standards exacerbates these vulnerabilities, reinforcing the urgent need for robust measures from a cyber security MSSP.
Additionally, the high turnover in production roles and limited cybersecurity training contribute to vulnerabilities within the sector, making continuous monitoring even more imperative. By prioritizing ongoing IT infrastructure surveillance, manufacturing leaders can enhance the protection of their operations and safeguard their intellectual property from increasingly sophisticated cybercriminals. To implement effective continuous monitoring, organizations should consider:
- Conducting regular assessments
- Investing in employee training to cultivate a culture of vigilance and preparedness against evolving threats
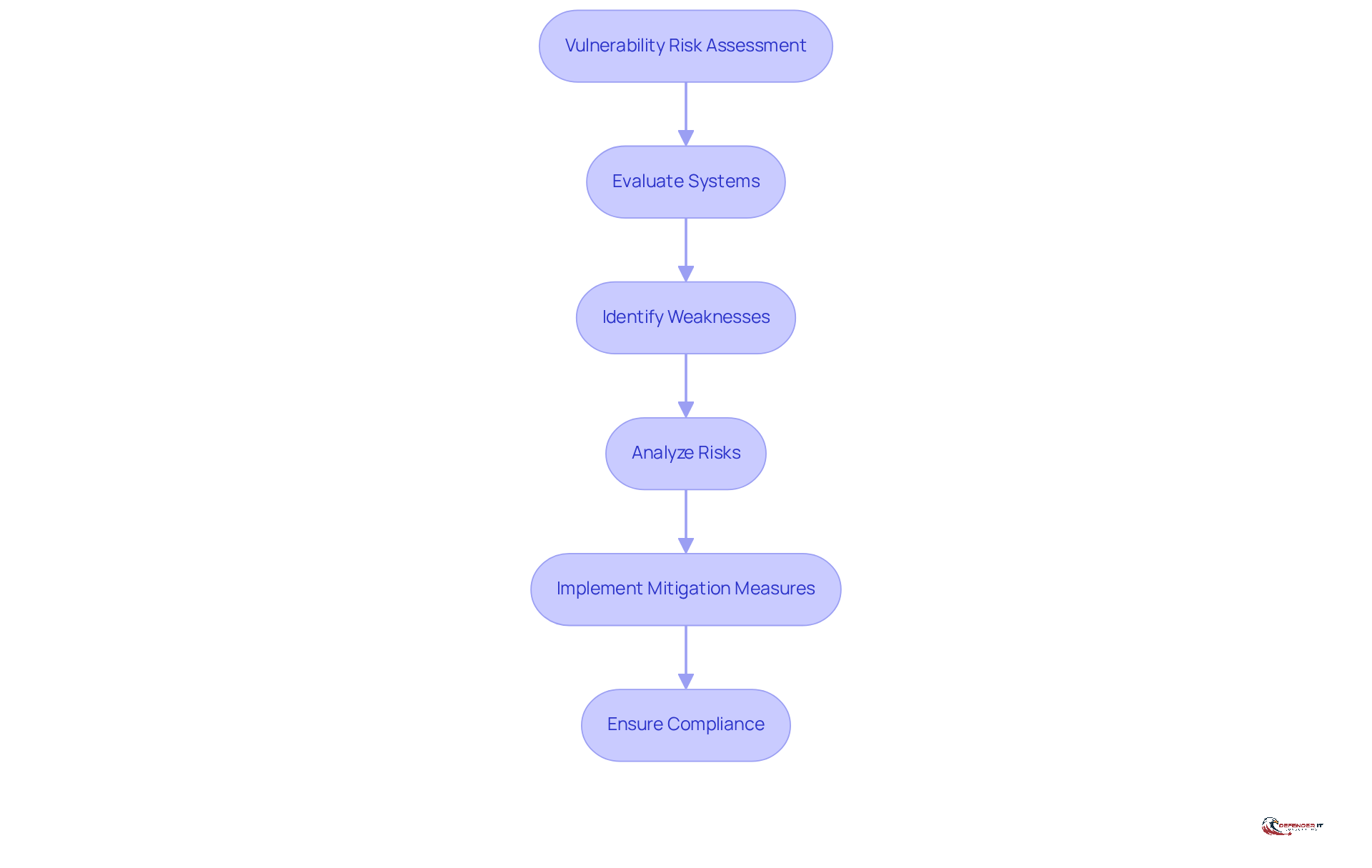
Vulnerability Risk Assessment: Identifying Potential Threats
A is a systematic evaluation of a company’s systems and processes aimed at identifying potential . This assessment is crucial for production leaders, as it provides into areas susceptible to . By pinpointing these vulnerabilities, organizations can implement to mitigate risks effectively. This ensures that operations remain secure and .
Threat Intelligence: Staying Ahead of Cyber Threats
is crucial for manufacturing leaders aiming to outpace their competitors. It involves the systematic gathering and examination of information related to potential cyber threats in the context of . By understanding the strategies, methods, and processes employed by cybercriminals, companies can proactively bolster their defenses and respond effectively to emerging challenges through . This strategic approach not only but also cultivates a culture of vigilance within the organization.
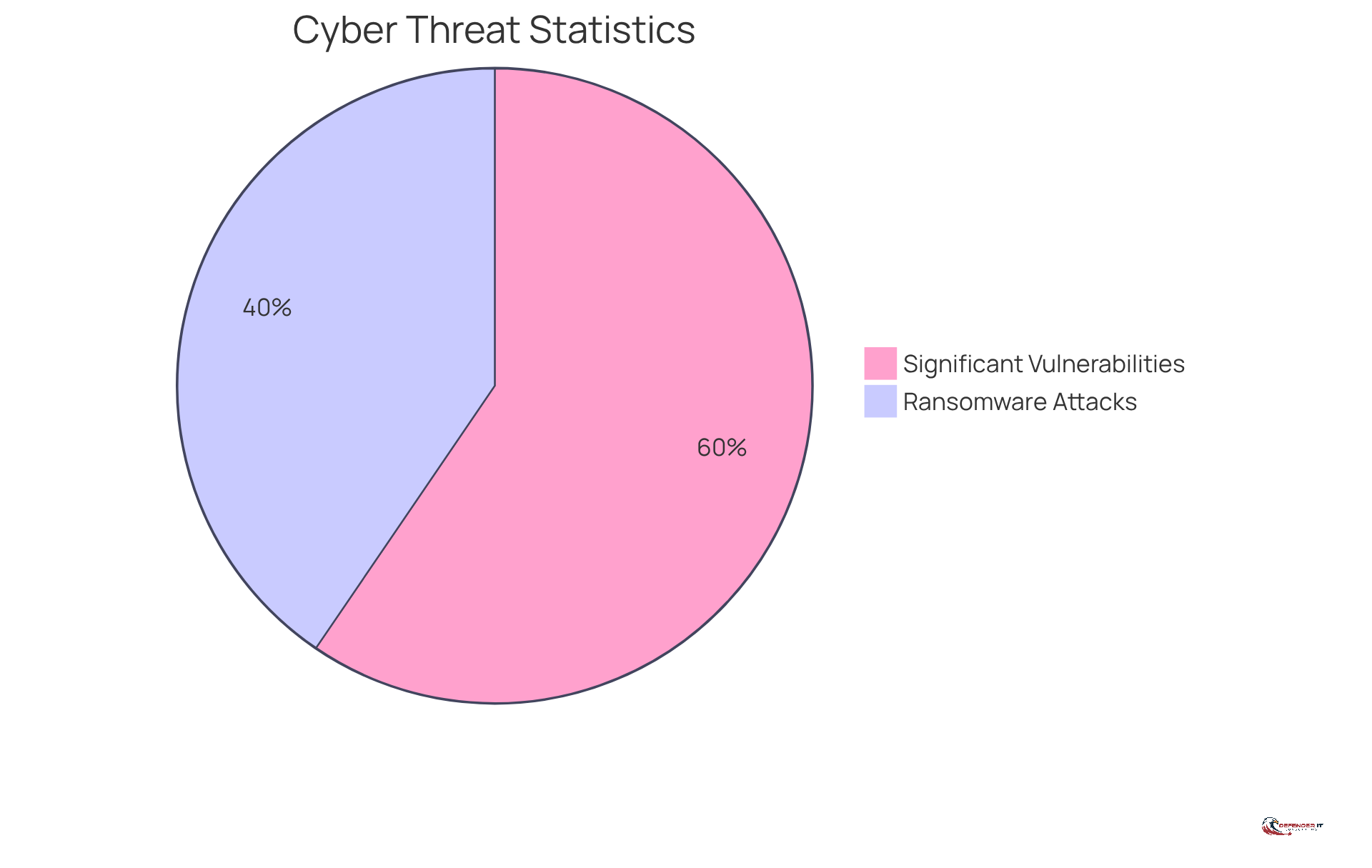
The urgency of focusing on is underscored by alarming statistics:
- In 2025, 51% of manufacturers experienced , with the average recovery cost-excluding ransom-reaching approximately $1.3 million.
- Furthermore, 75% of producers reported , as indicated by a Common Vulnerability Scoring System (CVSS) score of 8.0 or higher.
These figures highlight the pressing need for .
Effective intelligence initiatives in manufacturing involve integrating real-time data streams into existing safety operations, thereby enhancing the ability to swiftly identify and respond to risks, with the support of a cyber security MSSP. For instance, organizations can leverage that provide contextual metadata, enabling teams to differentiate between low-priority alerts and high-impact issues. This capability is vital, as it transforms operations from reactive to predictive, allowing manufacturers to anticipate attacks and minimize downtime.
As cybersecurity analysts emphasize, “Remaining ahead of necessitates a .” By aligning safety initiatives with business objectives and investing in , industry leaders can not only protect their operations but also drive innovation and growth in an increasingly digital landscape.
Security Consultation: Tailoring Strategies for Protection
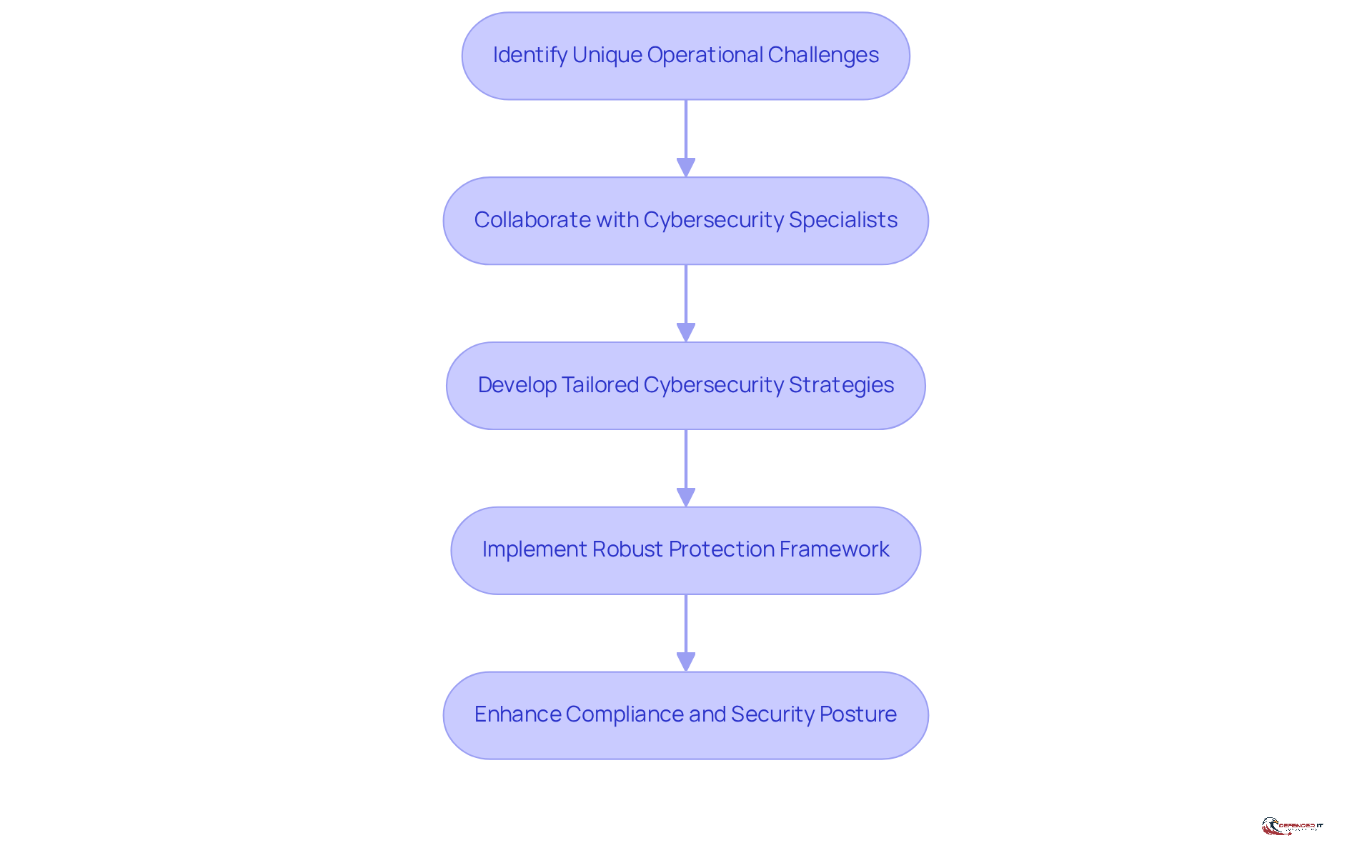
provides essential expert guidance for organizations aiming to develop tailored that address the unique operational challenges and . By collaborating with cybersecurity specialists, manufacturing leaders can establish a that not only mitigates specific vulnerabilities but also aligns with their business objectives. This alignment is critical, as it enhances compliance rates and strengthens the overall security posture of the organization.
For instance, companies that have engaged in customized consultations have reported notable improvements in their adherence to industry regulations. A proactive stance on cybersecurity not only diminishes risks but also fosters a culture of awareness among employees, which is vital in environments where operational urgency may lead to shortcuts in cybersecurity responses.
Successful consultation initiatives within the manufacturing sector have demonstrated that can effectively protect valuable intellectual property and critical systems from evolving . As manufacturers increasingly embrace a , the implementation of robust access controls and multi-factor authentication has become standard practice. This transition is particularly important as IT and operational technology (OT) networks become more interconnected, .
emphasize the importance of customizing strategies to meet the specific needs of manufacturing companies. By concentrating on the distinctive characteristics of each business, these experts can offer actionable insights that result in . As the landscape of continues to shift, with ransomware increasingly targeting critical systems and the pressure to pay substantial ransoms rising, the necessity for tailored has never been more pressing for industry leaders.
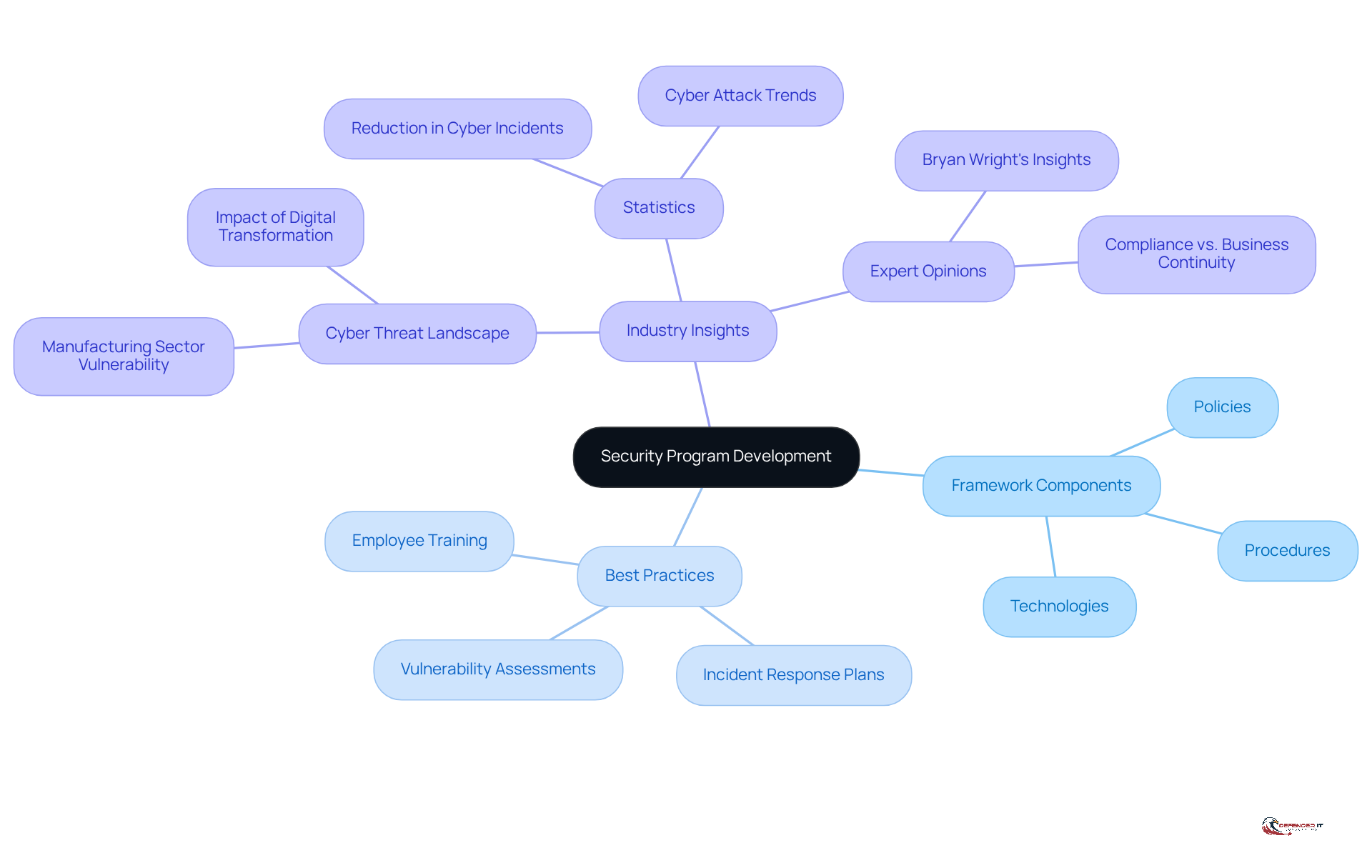
Security Program Development: Structuring Your Defense
is crucial for manufacturing entities, establishing a that addresses the complex landscape of cyber threats. A robust security program integrates policies, procedures, and technologies, creating a cohesive defense strategy that safeguards digital assets. By defining clear guidelines and responsibilities, organizations can significantly enhance their resilience against while ensuring compliance with industry regulations.
Industry experts emphasize that a is not merely a compliance requirement but a critical component of . Bryan Wright notes, “The challenge for manufacturers is to embrace digital transformation, which increases their threat surface, without creating undue risk. Digitisation must be balanced with , not just for compliance’s sake but for ’s sake.” Best practices indicate that industry leaders should prioritize the creation of a comprehensive that includes:
- Regular
Statistics show that organizations with well-structured security programs experience a marked reduction in successful cyber incidents, underscoring the effectiveness of proactive measures. Notably, the production sector has been the industry most at risk for for four consecutive years, according to IBM.
In an era where cyber risks are increasingly sophisticated, the significance of a comprehensive cannot be overstated. It serves as the foundation for a successful safety program, enabling production companies to navigate the evolving threat environment and safeguard their operations efficiently. Furthermore, addressing the disconnect in decision-making processes is crucial, as it contributes to the failure of critical Industry 4.0 initiatives, highlighting the need for a structured approach to cybersecurity.
Penetration Testing: Simulating Attacks to Identify Weaknesses
serves as a critical evaluation of a company’s through simulated cyber assaults. This service is particularly invaluable for , as it uncovers . Understanding how an assailant might enables organizations to implement their security posture. Furthermore, regular [](https://defenderit.consulting) not only identifies these vulnerabilities but also fosters a within the organization.
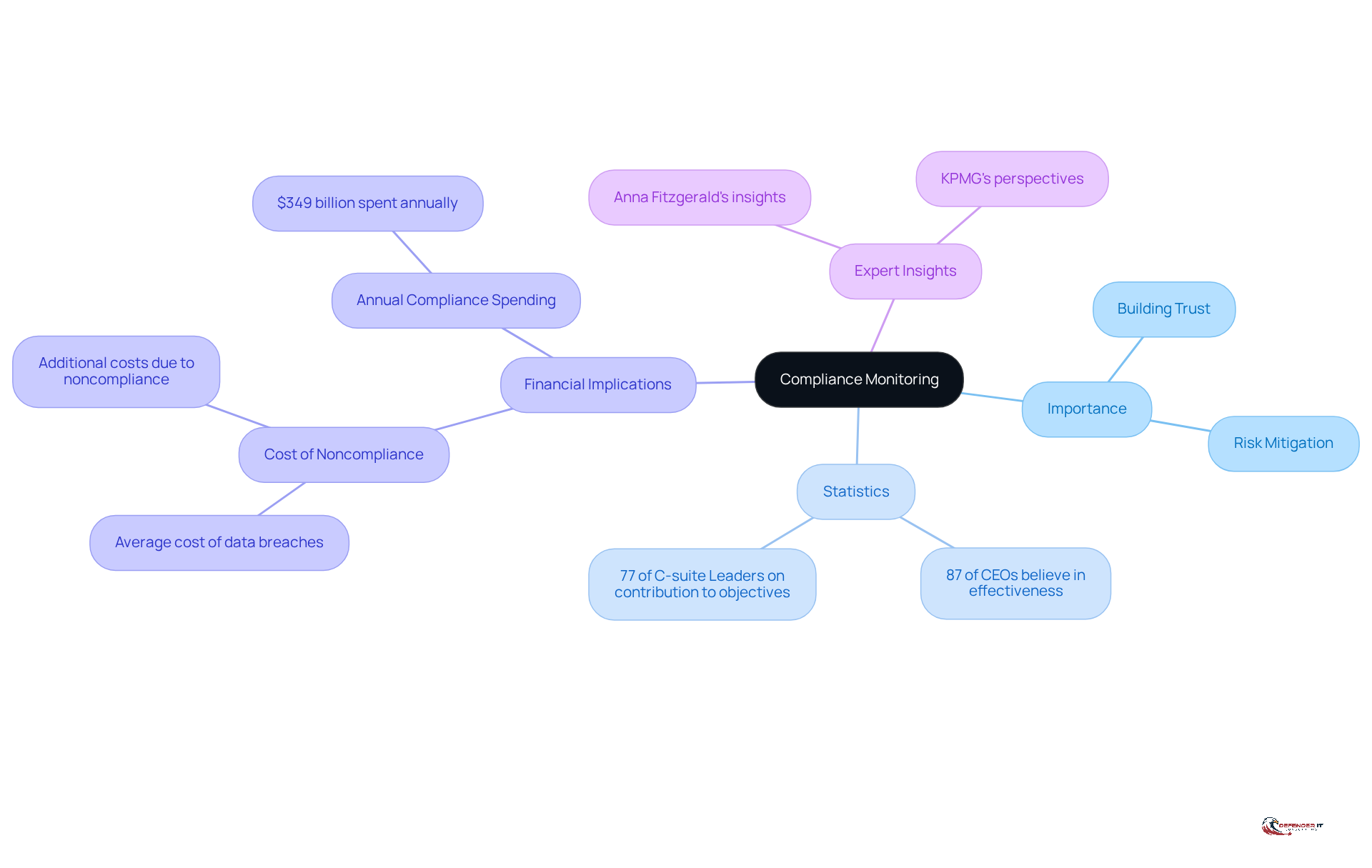
Compliance Monitoring: Ensuring Regulatory Adherence
serves as a critical service that ensures entities adhere to relevant regulations and standards. For manufacturing leaders, maintaining compliance goes beyond a mere legal obligation; it is essential for building trust with customers and stakeholders. By implementing comprehensive , organizations can identify and take corrective actions to mitigate risks. This proactive approach not only shields the company from potential penalties-data breaches related to noncompliance average a cost of $4.61 million-but also bolsters its reputation in a competitive marketplace.
In fact, 87% of CEOs believe that cyber and privacy regulations effectively reduce their entities’ . Additionally, 77% of global C-suite leaders assert that . The scale of compliance efforts in the sector is underscored by the fact that to comply with various regulations. As Anna Fitzgerald highlights, , illustrating the .
Incorporating expert insights and relevant statistics underscores the vital role of compliance in safeguarding both operational integrity and customer confidence.
Incident Response: Managing Security Breaches Effectively
serves as a systematic approach to managing and minimizing their impact on production activities. For leaders in this field, a well-defined is crucial for ensuring a swift recovery from . This service encompasses preparation for potential breaches, incident detection, and the execution of a response strategy aimed at mitigating damage.
By establishing clear protocols and providing staff training, organizations can bolster their resilience and decrease the likelihood of extended disruptions to their operations. Notably, the 2025 indicated a 30% year-over-year increase in overall attacks on the production sector, highlighting the urgent need for .
As Anna Chung, a prominent researcher at Palo Alto Networks, stated, “the production sector is the most dependable area to derive a profit,” underscoring the importance of . Organizations that adopt frequently experience significant improvements in their recovery timelines, which can vary considerably based on the level of preparedness and the execution of their response plans.
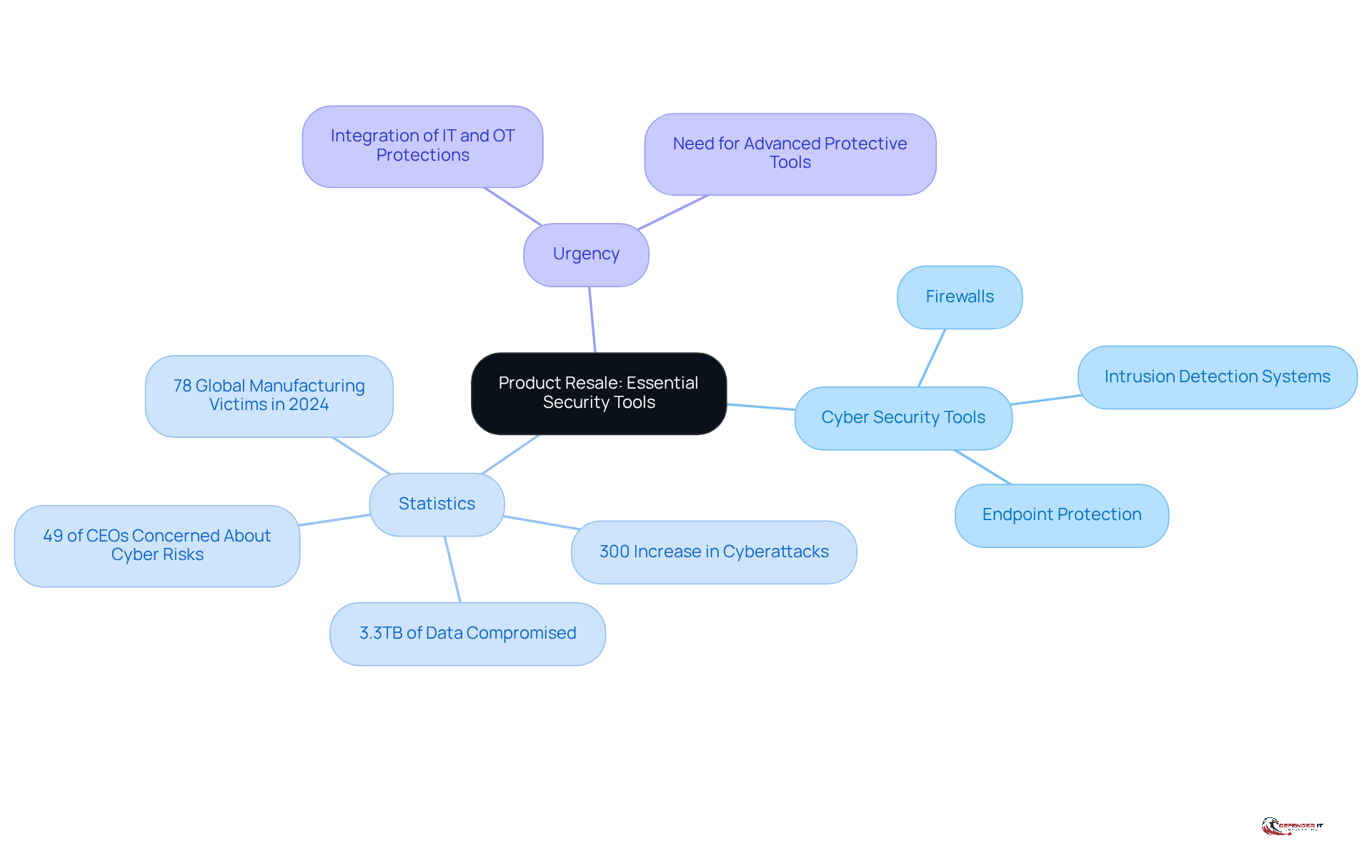
Product Resale: Providing Essential Security Tools
Product resale is crucial for equipping businesses with essential tools and technologies for . For manufacturing leaders, having the right is vital for effectively safeguarding against , particularly through a . This service provides access to the latest technologies, including:
- Firewalls
- Intrusion detection systems
- Endpoint protection solutions
By partnering with reliable suppliers, organizations can significantly enhance their protective measures with the help of a cyber security MSSP and stay ahead of evolving cyber threats.
A recent analysis indicates that 49% of CEOs consider the primary challenge to growth, underscoring the urgency for manufacturers to implement robust . The production industry is currently facing a staggering 300% increase in cyberattacks, with over 3.3TB of data compromised in reviewed incidents. Additionally, RansomHub reported 78 global production victims in 2024, highlighting the critical need for advanced to safeguard operations and maintain a competitive edge.
Furthermore, the 71% rise in threat actors targeting the production sector emphasizes the expanding . It is essential for companies to integrate IT and OT protections to fortify their defenses against these growing risks.
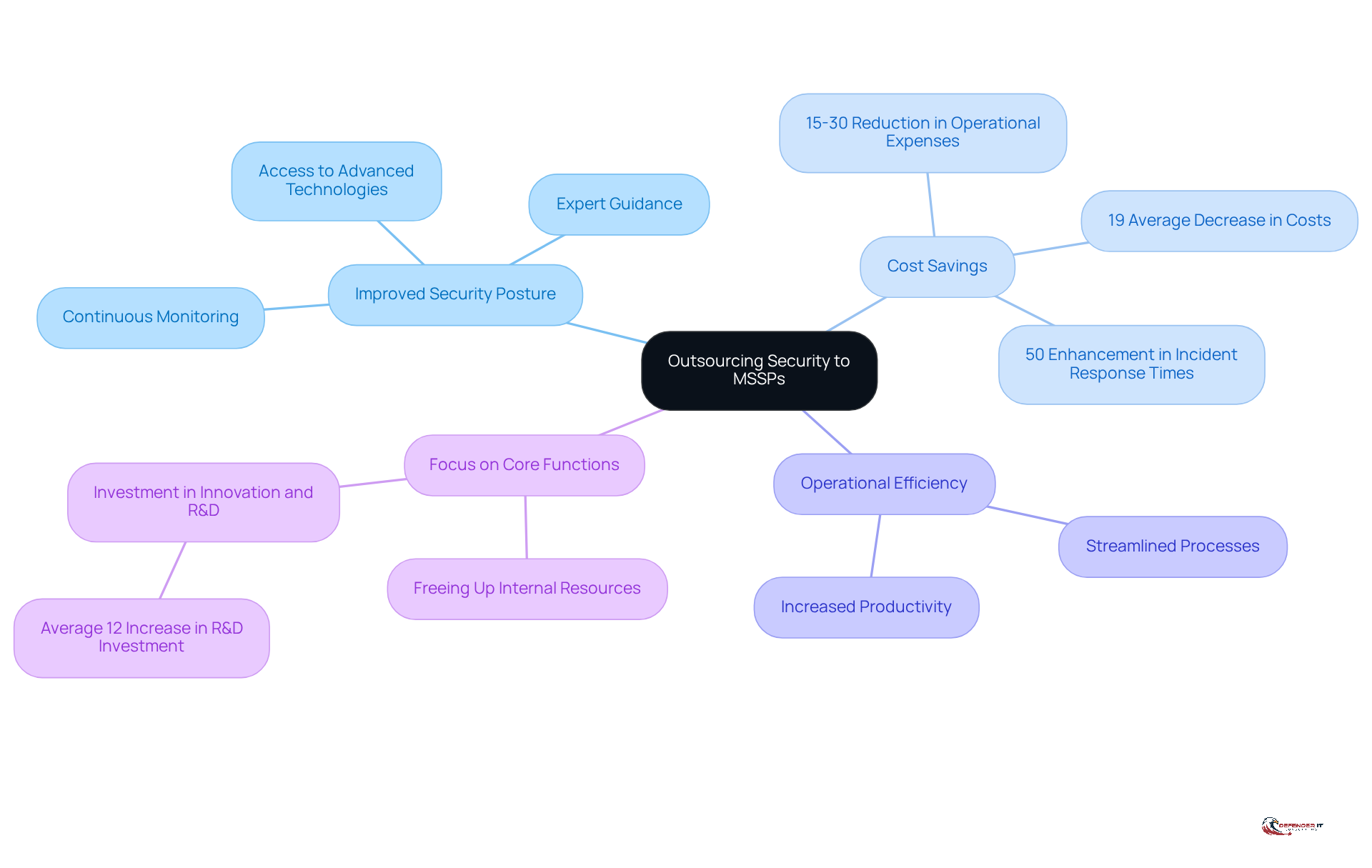
Outsourcing Security: The Comprehensive Benefits of MSSP Services
Delegating protection to a offers significant advantages for manufacturing leaders. By leveraging the specialized expertise and resources of a , organizations can markedly improve their security posture without the complexities of internal management. This partnership provides access to state-of-the-art technologies, including advanced firewalls, intrusion detection systems, continuous monitoring, and expert guidance, ensuring businesses are well-prepared to address evolving .
Furthermore, outsourcing security functions can lead to considerable . Organizations utilizing frequently report an average reduction of 15-30% in , enabling more effective resource allocation. Specifically, companies have noted an average decrease of 19% in operational costs due to outsourcing, highlighting the financial advantages of this strategic decision. For example, 15-20% of their IT budgets to Managed Security Services (MSS), resulting in a remarkable 50% enhancement in .
The strategic decision to collaborate with an MSSP not only boosts operational efficiency but also allows manufacturing leaders to concentrate on core business functions. As the industry faces increasing cybersecurity threats, exacerbated by supply chain disruptions, the utilization of cyber security becomes essential for maintaining a robust . A survey indicated that 32% of manufacturers have encountered cyber incidents linked to supply chain vulnerabilities, emphasizing the urgent need for .
In conclusion, integrating cyber security MSSP services into manufacturing operations not only strengthens defenses against cyber risks but also drives significant cost efficiencies, making it a compelling strategy for sector leaders. As highlighted by cybersecurity experts, “Outsourcing frees up internal resources, allowing companies to invest in innovation and research & development by an average of 12%” (Deloitte). This reinforces the in response to today’s rapidly evolving threat landscape.
Conclusion
Integrating essential cyber security MSSP services into manufacturing operations is not just beneficial; it is a strategic imperative for industry leaders. By embracing these services, organizations can significantly bolster their defenses against the rising tide of cyber threats while simultaneously achieving operational efficiencies. This dual focus on security and cost-effectiveness safeguards vital assets and cultivates an environment that fosters innovation and growth.
Key services highlighted throughout this article include:
- Managed Security Monitoring
- Vulnerability Risk Assessment
- Threat Intelligence
- Incident Response
Each of these services plays a critical role in strengthening manufacturing operations against cyber risks. By prioritizing continuous monitoring, tailored security strategies, and proactive risk management, manufacturing leaders can better protect their intellectual property and ensure compliance with industry regulations.
The urgency of addressing cyber security in the manufacturing sector is paramount. As cyber threats evolve and grow more sophisticated, reliance on expert MSSP services becomes essential for maintaining resilience and operational continuity. By investing in these vital services, organizations not only safeguard their operations but also position themselves for future success in an ever-changing digital landscape. Adopting a proactive approach to cyber security is not merely a necessity; it is a fundamental step toward securing a competitive edge in the market.
Frequently Asked Questions
What is Managed Security Monitoring (MSM)?
Managed Security Monitoring (MSM) is a service provided by Defenderit Consulting that focuses on the continuous surveillance of an organization’s IT infrastructure to detect and respond to potential cyber threats, utilizing a cyber security managed service provider (MSSP).
Why is MSM important for the production industry?
MSM is crucial for the production industry because it helps minimize the risk of cyber incidents that can lead to significant financial losses, as evidenced by the $2.5 billion costs from a recent cyberattack on Jaguar Land Rover.
What are the trends in cyber risks within the production sector?
The production sector is experiencing a 30% annual increase in ransomware attacks, highlighting its vulnerability to cyber risks.
How does continuous surveillance benefit organizations?
Continuous surveillance facilitates early detection of threats and enhances incident response capabilities, allowing organizations to swiftly mitigate risks and protect their operations.
What challenges does the production sector face regarding cybersecurity?
Challenges include insufficient oversight, varying cybersecurity maturity among partners, a lack of consistent standards, high turnover in production roles, and limited cybersecurity training.
What steps can organizations take to implement effective continuous monitoring?
Organizations should conduct regular assessments and invest in employee training to foster a culture of vigilance against evolving threats.
What is a Vulnerability Risk Assessment?
A Vulnerability Risk Assessment is a systematic evaluation of a company’s systems and processes aimed at identifying potential security weaknesses, which is essential for implementing targeted risk mitigation measures.
How can threat intelligence help manufacturing leaders?
Threat intelligence involves gathering and analyzing information about potential cyber threats, enabling companies to proactively strengthen their defenses and respond effectively to emerging challenges.
What statistics highlight the need for robust threat intelligence in manufacturing?
In 2025, 51% of manufacturers experienced ransomware attacks, with recovery costs averaging $1.3 million, and 75% of producers reported significant vulnerabilities with a Common Vulnerability Scoring System (CVSS) score of 8.0 or higher.
How can organizations enhance their threat intelligence initiatives?
Organizations can enhance their threat intelligence by integrating real-time data streams into safety operations and utilizing advanced risk intelligence platforms to differentiate between low-priority alerts and high-impact issues.
](https://defenderit.consulting), and the branches show its key aspects. Follow the branches to understand how it helps in identifying weaknesses and improving security.](https://images.tely.ai/telyai/vecslyyb-the-center-represents-penetration-testing-and-the-branches-show-its-key-aspects-follow-the-branches-to-understand-how-it-helps-in-identifying-weaknesses-and-improving-security.webp)
](https://welivesecurity.com/en/business-security/manufacturing-fire-strengthening-cyber-defenses-surging-threats) effectively. Follow the arrows to see how each step leads to the next, from preparing for potential incidents to recovering after a breach.](https://images.tely.ai/telyai/vwsdopjw-this-flowchart-outlines-the-steps-organizations-should-take-to-manage-security-breaches-effectively-follow-the-arrows-to-see-how-each-step-leads-to-the-next-from-preparing-for-potential-incidents-to-recovering-after-a-breach.webp)