Introduction
In an era marked by rapidly evolving cyber threats, the importance of threat intelligence is paramount. Organizations that effectively leverage threat intelligence are not only positioned to anticipate and mitigate potential attacks but also foster a proactive security culture that enhances overall resilience. As the complexity of the cyber threat landscape increases, organizations must navigate the intricacies of threat intelligence to protect their assets effectively. This article explores best practices for mastering threat intelligence, providing insights that empower businesses to strengthen their cybersecurity strategies and respond adeptly to emerging threats.
Understand the Importance of Threat Intelligence
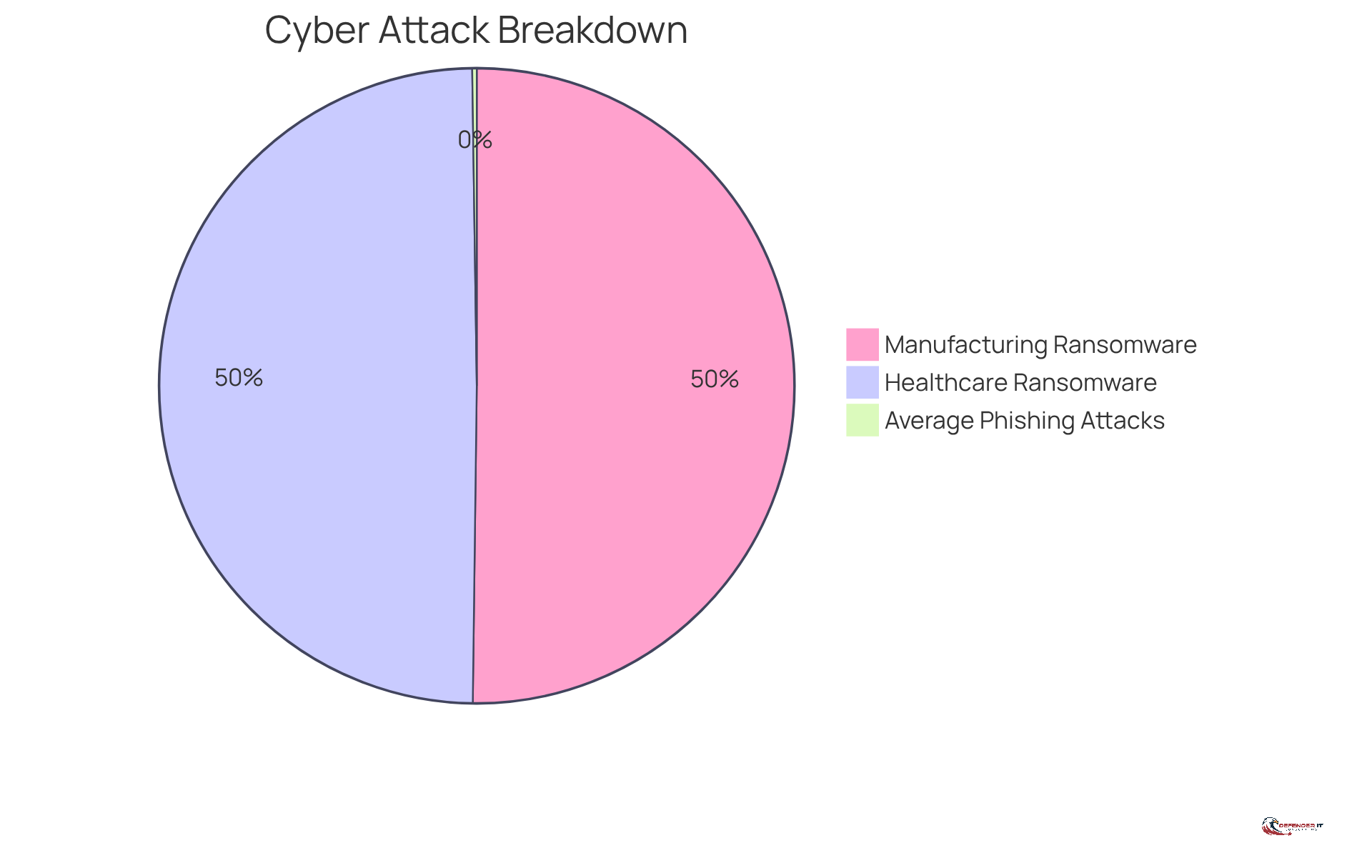
stands as a pivotal element in contemporary , encompassing the systematic collection and analysis of data related to potential and existing threats. By understanding the threat landscape, organizations can , significantly mitigating the risk of . For example, in 2023, over 630 ransomware incidents targeted healthcare institutions globally, while the manufacturing sector encountered 638 ransomware attacks, underscoring the urgent need for effective risk awareness.
Organizations that utilize can anticipate the tactics, techniques, and procedures (TTPs) used by cybercriminals, enabling them to implement targeted defenses. This not only bolsters security but also cultivates a culture of resilience within the organization. Recent trends reveal that the average number of phishing attacks per user reached 2.91 in 2024, with government entities experiencing an average of 2.8 attacks per user, while the manufacturing and construction sectors faced 1.65 attacks per user. Moreover, the , according to the 2024 Verizon DBIR report, highlighting the necessity of addressing human elements in cybersecurity.
By establishing a robust risk awareness framework, businesses can prioritize their , ensuring that resources are directed toward the most pressing threats and enhancing their overall . Additionally, the average time taken to resolve among federal agencies was 20 days, emphasizing the critical need for implementing security insights.
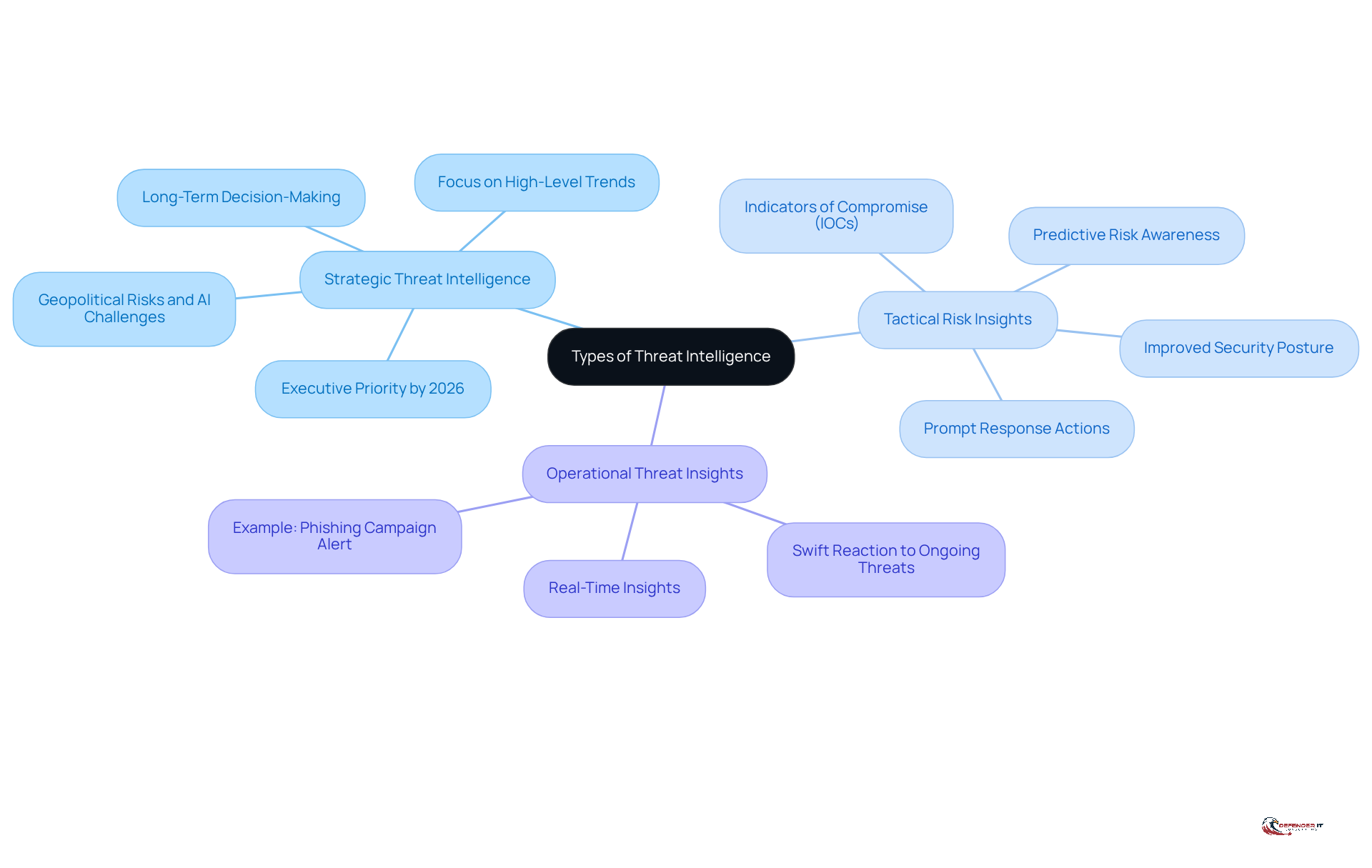
Identify Types of Threat Intelligence: Strategic, Tactical, and Operational
is essential for effective and can be categorized into three main types: strategic, tactical, and operational.
- Strategic : This type focuses on that inform long-term decision-making. It assists entities in comprehending the wider danger environment, including motivations behind cyber assaults, and is becoming increasingly essential as the complexity of risks develops. For instance, by 2026, cyber resilience should be a priority at the executive and board level for effective planning and resource distribution. This highlights the necessity for companies to emphasize strategic insight and threat intelligence in order to manage geopolitical risks and emerging challenges from AI-driven attacks.
- Tactical Risk Insights: Tactical insights provide detailed information about specific risks, including (IOCs) such as malicious IP addresses and file hashes. This information is crucial for prompt response actions, enabling organizations to quickly mitigate risks. Predictive risk awareness can significantly decrease the average time to identify (MTTD) and react (MTTR) to dangers, thereby improving their overall .
- Operational Threat Insights: This type bridges the gap between strategic and tactical knowledge, offering . It allows entities to react swiftly to ongoing attacks and modify their defenses as needed. For example, operational awareness informed a bank about a phishing campaign targeting other banks, enabling them to take prompt measures to block harmful domains and safeguard their systems.
By utilizing all three categories of risk information, entities can develop a comprehensive security plan that effectively integrates threat intelligence to address both short-term and long-term dangers, ensuring resilience in an increasingly complex cyber environment.
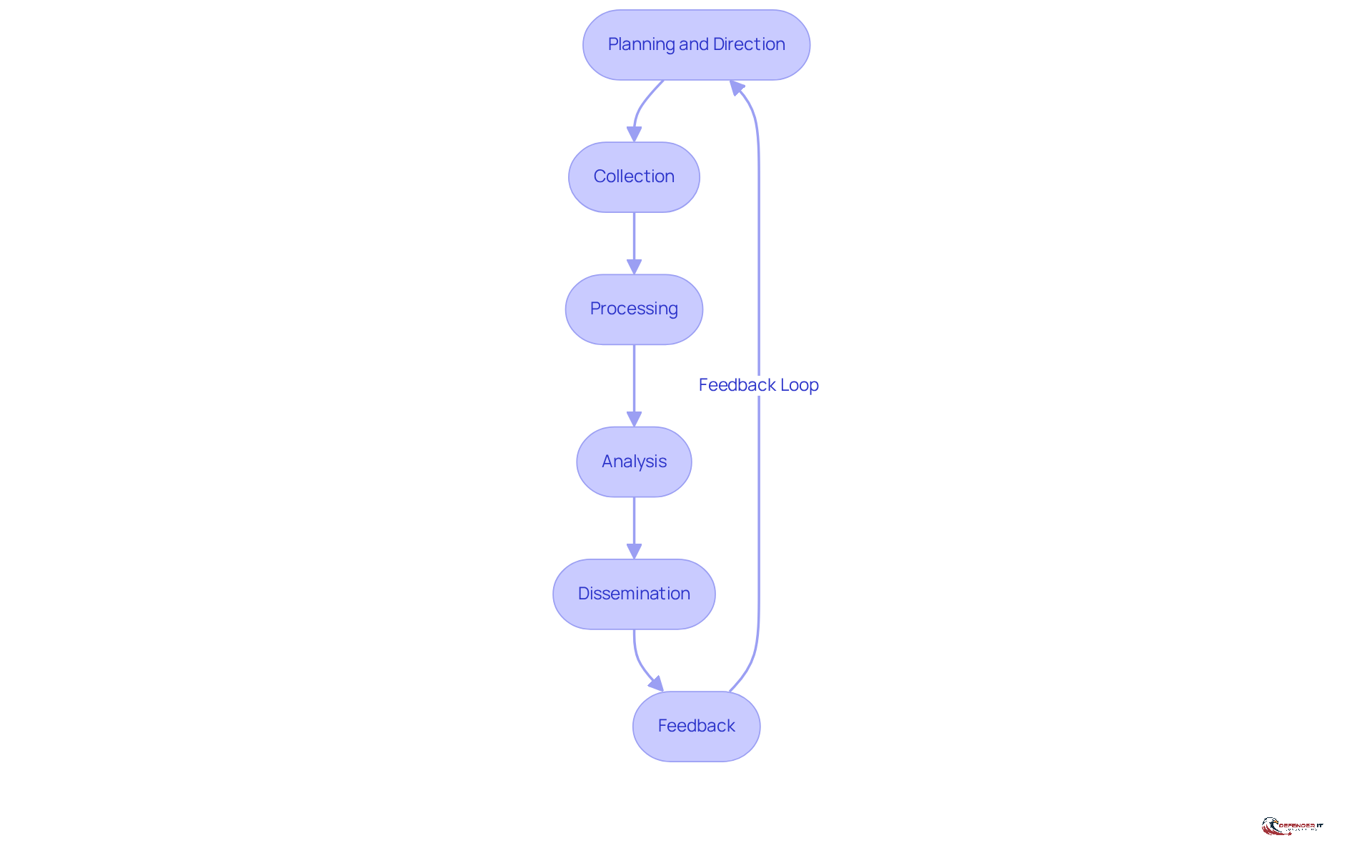
Navigate the Threat Intelligence Lifecycle: From Collection to Feedback
The consists of several critical phases that organizations must navigate to effectively manage their threat intelligence initiatives:
- Planning and Direction: This initial phase establishes the objectives and scope of the risk analysis program, focusing on identifying specific dangers pertinent to the organization. A well-defined plan lays the groundwork for effective information operations.
- Collection: Gathering data from diverse sources, including internal logs, external threat feeds, and open-source insights, is vital for obtaining relevant information. Organizations should prioritize the collection of high-quality data to .
- Processing: In this phase, the collected data is organized and filtered to extract actionable insights. Efficient processing ensures that only pertinent information is examined, minimizing distractions and enhancing the quality of insights.
- Analysis: This phase involves interpreting the processed data to identify patterns, trends, and potential threats. The analysis transforms raw data into , enabling organizations to make informed decisions about their .
- Dissemination: Sharing the analyzed information with relevant stakeholders is crucial for informing decision-making. Efficient distribution ensures that the appropriate individuals can access the information they require to respond to challenges swiftly.
- Feedback: Collecting input from stakeholders is essential for improving the knowledge process and enhancing future initiatives. Ongoing feedback fosters a culture of improvement, allowing entities to adjust their strategies in response to evolving challenges.
By adhering to this structured lifecycle, organizations can enhance their , leading to improved security outcomes and a more robust cybersecurity stance. Entities that effectively implement their threat intelligence insights report significantly improved detection and response times, with over half assessing success by these metrics. As Lee Noriega points out, “Starting in 2026, for public sector entities,” underscoring the importance of a developed information program in managing future compliance environments. Furthermore, , as demonstrated in various case studies, to ensure their effectiveness in real-world applications. However, organizations should be cautious of common pitfalls, such as failing to incorporate feedback effectively or neglecting the need to refresh their information processes in response to emerging threats.
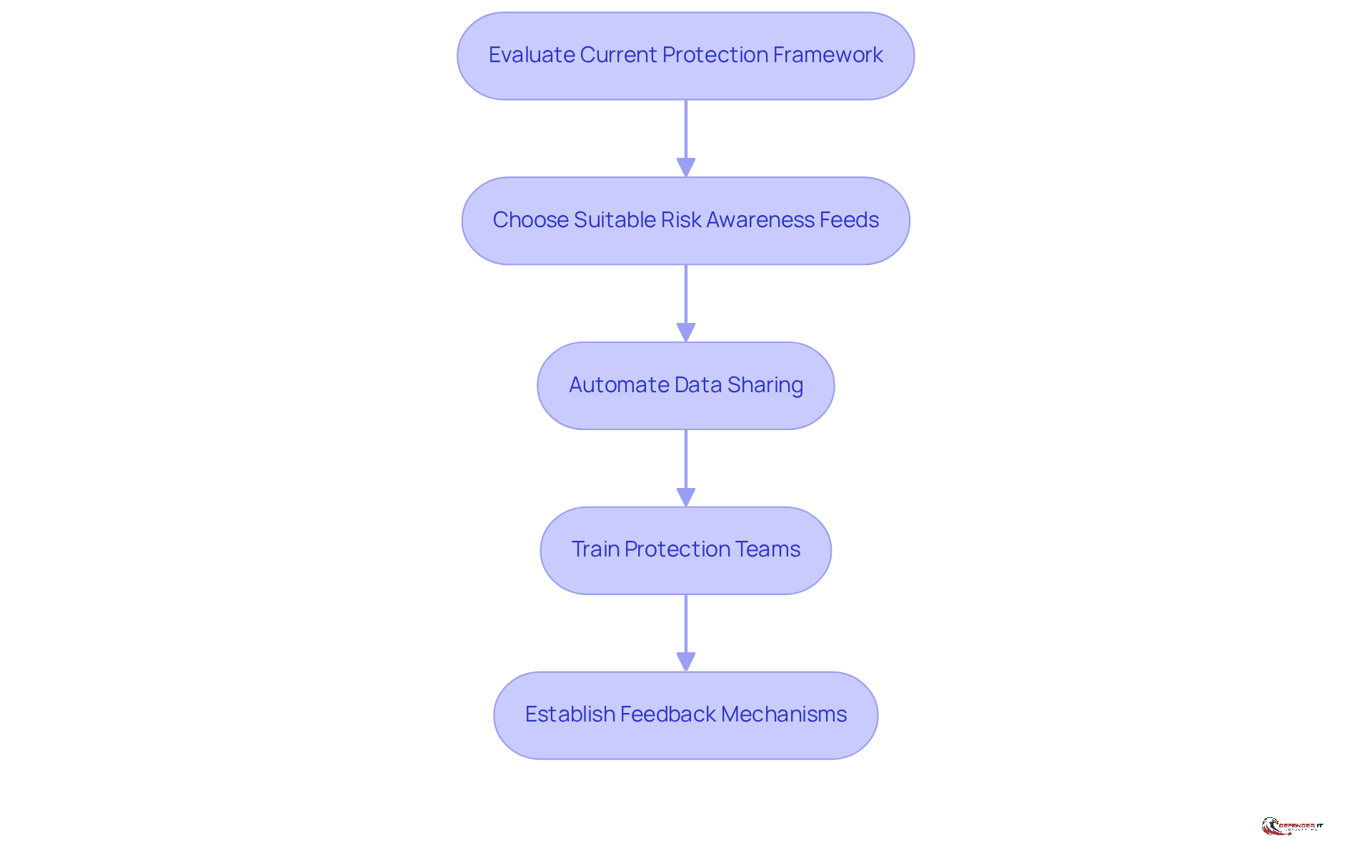
Integrate Threat Intelligence with Existing Security Solutions
Incorporating into current protective measures is essential for enhancing a company’s . The following steps outline an :
- Evaluate : Conduct a thorough assessment of existing protective tools and processes to identify gaps where risk awareness can improve effectiveness.
- Choose Suitable Risk Awareness Feeds: Identify and select risk awareness sources that align with the entity’s specific requirements and the current risk landscape, ensuring relevance and applicability.
- Automate Data Sharing: Implement automation to facilitate seamless sharing of risk information across protection platforms, such as Security Information and Event Management (SIEM) systems. This optimization significantly enhances during crises. Research indicates that risk information considerably reduces response times, enabling organizations to act promptly and effectively.
- Train Protection Teams: Provide personnel with instruction on effectively using within their workflows. This ensures that the information is actionable and directly applicable to their roles.
- Establish : Create channels for protection teams to provide feedback on the effectiveness of the integrated risk awareness, fostering a culture of continuous improvement.
By following these steps, entities can effectively integrate risk awareness into their overall protection strategy, significantly improving their detection and response capabilities. As highlighted by NCC Group, through risk analysis is crucial for ensuring compliance and protecting operations. This proactive approach not only reduces risks but also transforms protection from a cost center into a strategic asset, ultimately safeguarding the entity against evolving cyber threats. For instance, organizations that have successfully integrated have reported and improved operational efficiency.
Conclusion
The significance of threat intelligence in cybersecurity is paramount. Organizations that prioritize understanding and integrating threat intelligence into their security frameworks are better equipped to navigate the complex landscape of cyber threats. By adopting a proactive approach, businesses can enhance their defenses and foster a culture of resilience essential in today’s digital environment.
Key insights highlight the importance of a structured threat intelligence lifecycle, which encompasses:
- Planning
- Collection
- Processing
- Analysis
- Dissemination
- Feedback
Each phase plays a crucial role in transforming raw data into actionable insights, significantly improving incident response times and overall security posture. Furthermore, categorizing threat intelligence into strategic, tactical, and operational types equips organizations with the necessary tools to effectively address both immediate and long-term risks.
Ultimately, integrating threat intelligence with existing security solutions is a fundamental best practice for organizations aiming to bolster their defenses against evolving threats. By evaluating current frameworks, automating data sharing, and fostering continuous feedback, entities can shift their cybersecurity approach from a reactive stance to a proactive strategy. Embracing these best practices is essential for organizations striving to thrive in an increasingly perilous cyber landscape.
Frequently Asked Questions
What is the importance of threat intelligence in cybersecurity?
Threat intelligence is crucial for understanding the threat landscape, allowing organizations to proactively defend against cyberattacks and mitigate the risk of data breaches and financial losses.
What recent statistics highlight the need for risk awareness in cybersecurity?
In 2023, there were over 630 ransomware incidents targeting healthcare institutions and 638 attacks on the manufacturing sector, demonstrating the urgent need for effective risk awareness.
How does threat intelligence help organizations defend against cybercriminals?
It enables organizations to anticipate the tactics, techniques, and procedures (TTPs) used by cybercriminals, allowing for the implementation of targeted defenses and fostering a culture of resilience.
What trends were observed regarding phishing attacks in 2024?
The average number of phishing attacks per user reached 2.91, with government entities facing an average of 2.8 attacks per user, and the manufacturing and construction sectors encountering 1.65 attacks per user.
What role does the human factor play in cybersecurity breaches?
The human element was implicated in 68% of breaches, highlighting the necessity of addressing human factors within cybersecurity strategies.
How can organizations enhance their cybersecurity posture?
By establishing a robust risk awareness framework, organizations can prioritize security initiatives and direct resources toward the most pressing threats.
What is the average time taken to resolve cybersecurity incidents among federal agencies?
The average time taken to resolve cybersecurity incidents among federal agencies was 20 days, underscoring the importance of implementing security insights.