Introduction
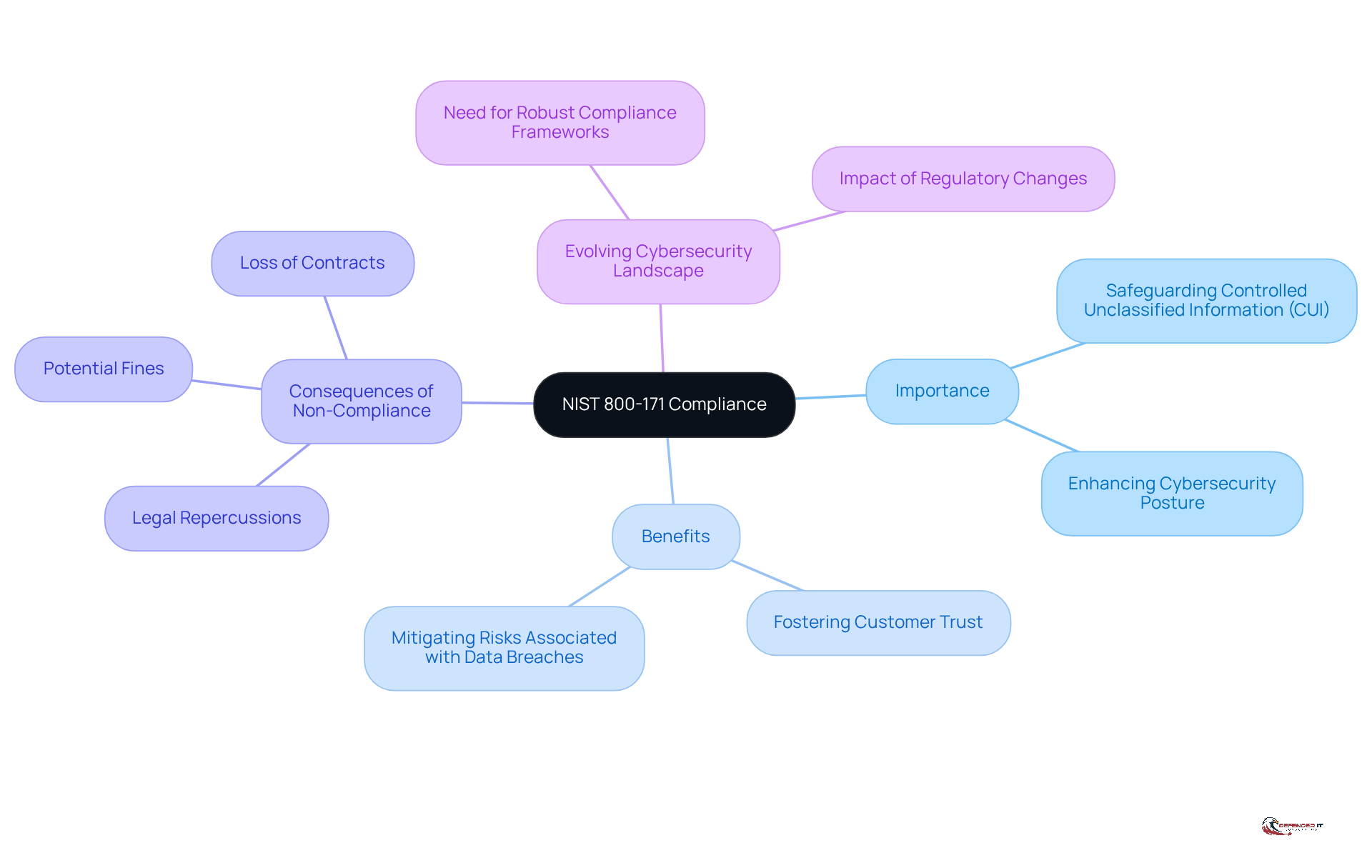
Achieving NIST 800-171 compliance is not just a regulatory checkbox; it represents a vital step for organizations aiming to safeguard Controlled Unclassified Information (CUI) against the ever-evolving landscape of cyber threats. By adopting a structured approach to compliance, businesses can significantly enhance their cybersecurity posture, build trust with clients, and reduce the risks associated with data breaches.
However, the journey to compliance is not without its challenges. What essential steps must organizations undertake to not only meet these standards but also sustain them within a dynamic regulatory environment?
Understand NIST 800-171 and Its Importance
The document for outlines essential guidelines from the National Institute of Standards and Technology for in non-federal systems. Its importance is paramount for organizations seeking to protect from unauthorized access and breaches. Adhering to not only fulfills federal requirements but also significantly enhances a company’s , fosters customer trust, and mitigates risks associated with .
Entities that implement these guidelines can expect a notable improvement in their protection frameworks. For instance, a case study illustrates that compliance with 800-171 controls could have potentially prevented or lessened the impact of breaches. In contrast, failing to comply can result in severe and the risk of losing contracts, especially in highly regulated industries like finance and healthcare.
As the cybersecurity landscape evolves, the need for robust frameworks becomes increasingly critical for maintaining and safeguarding .
Identify NIST 800-171 Requirements for Compliance
NIST 800-171 delineates 14 essential categories of requirements that organizations must adhere to in order to safeguard Controlled Unclassified Information (CUI). These categories include:
- : This requirement restricts access to authorized users, emphasizing the principle of least privilege.
- : It ensures that personnel are well-versed in safety policies and practices.
- : This mandates the maintenance of audit logs to monitor access and changes, thereby ensuring accountability.
- : It focuses on managing system configurations to prevent unauthorized alterations.
- Identification and Authentication: This requires the verification of user identities before granting access to sensitive information.
- : It involves creating and executing a comprehensive plan to effectively address breaches.
- Maintenance: This stipulates regular maintenance of systems to mitigate vulnerabilities.
- Media Protection: It ensures that sensitive media is secured against unauthorized access.
- Physical Protection: This secures physical access to systems to prevent unauthorized entry.
- : It calls for regular evaluations of risks associated with CUI handling.
- Security Assessment: This requires ongoing assessments of security controls to ensure their effectiveness.
- System and Communications Protection: It protects data both in transit and at rest from potential threats.
- System and Information Integrity: This involves continuous monitoring of systems for vulnerabilities and threats.
- Program Management: It establishes a comprehensive cybersecurity program to supervise adherence efforts.
By familiarizing themselves with the requirements of , organizations can effectively assess their current practices, identify compliance gaps, and enhance their . This ultimately ensures they achieve to meet the necessary standards for federal contracts. It is crucial to recognize that noncompliance with standards can result in significant penalties, including the termination of federal contracts. Furthermore, organizations should stay informed about the latest updates to NIST 800-171 compliance, which introduce new emphasis areas and modifications to existing requirements. Conducting self-evaluations and developing a (SSP) are essential actions for achieving NIST 800-171 compliance and demonstrating commitment to these protection requirements.
Implement Steps to Achieve NIST 800-171 Compliance
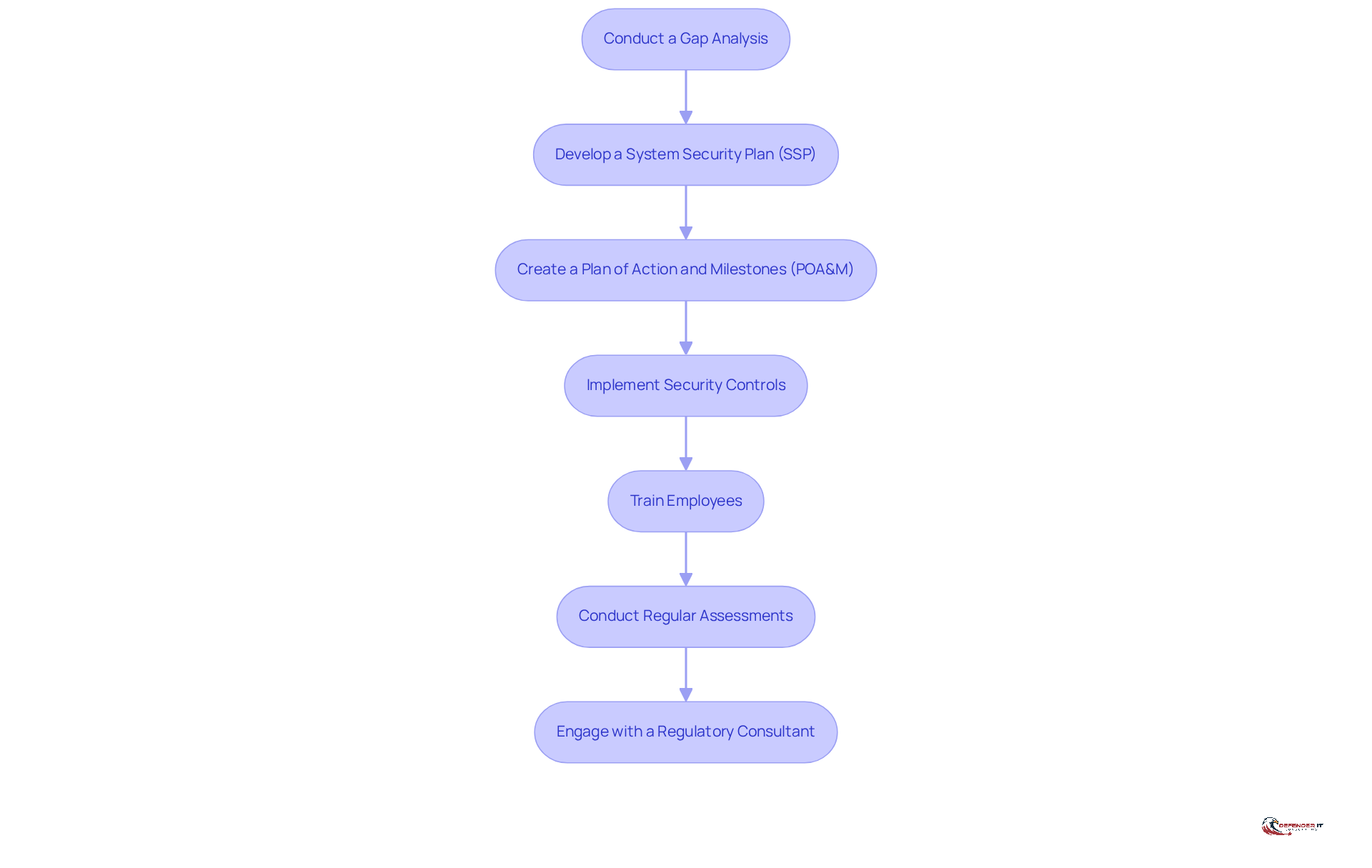
To achieve , organizations should systematically follow these essential steps:
- : Begin by evaluating current protective measures against NIST 800-171 requirements to identify any deficiencies. This analysis is vital, as it emphasizes areas requiring enhancement and establishes the groundwork for adherence initiatives.
- : Document how each requirement will be met, detailing the policies and procedures that will be implemented. A well-organized SSP is essential for adherence and acts as a guide for protective measures.
- Create a : Outline specific steps to address identified gaps, including timelines and responsible parties. This plan ensures accountability and provides a clear path forward.
- : Apply the necessary technical and administrative controls to protect Controlled Unclassified Information (CUI). Effective implementation of these controls is vital for safeguarding sensitive data.
- : Conduct to ensure all personnel understand their roles in maintaining regulations. Awareness and training are critical components of a robust .
- : Periodically review and evaluate adherence status to ensure ongoing conformity to NIST 800-171. Frequent assessments assist organizations in adjusting to new risks and sustaining adherence over time.
- Engage with a : Consider hiring a consultant to provide expertise and guidance throughout the regulatory process. Their insights can streamline efforts and enhance the effectiveness of regulatory initiatives.
By systematically following these steps, organizations can effectively work towards achieving , which generally requires 12 to 18 months for complete implementation. This organized method not only reduces risks but also enhances the overall protection framework.
Maintain and Monitor NIST 800-171 Compliance
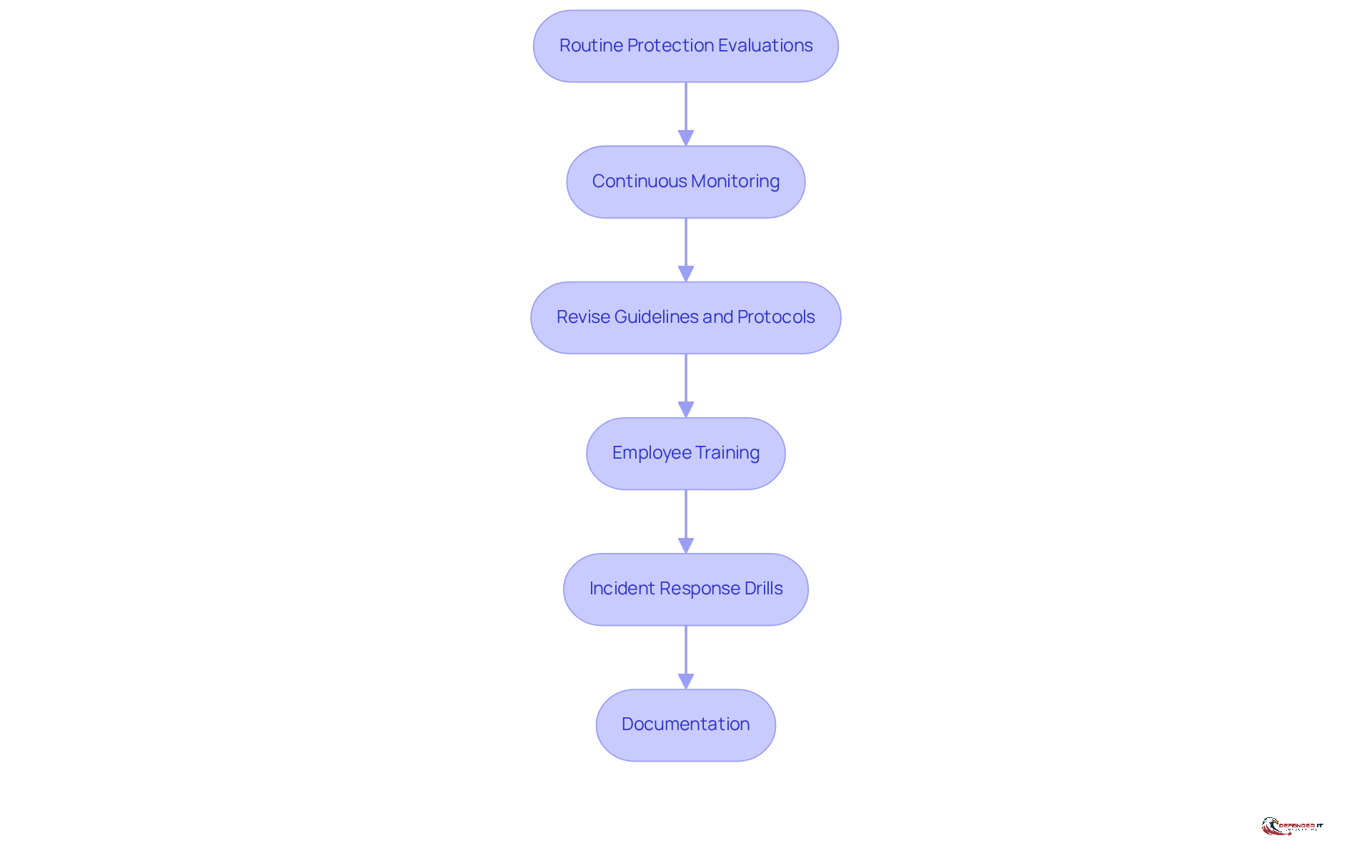
Maintaining and monitoring necessitates a structured approach that incorporates several essential practices:
- : Conduct evaluations at least annually to assess the effectiveness of protective measures, ensuring alignment with the evolving regulatory landscape.
- : Implement tools and processes for ongoing observation of systems to detect vulnerabilities and evaluate adherence status in real-time. This is crucial, as 72% of entities now employ some level of to enhance their monitoring capabilities. Additionally, 56% of risk and compliance specialists reported that their organizations faced at least one regulatory issue in the past three years, underscoring the prevalence of such challenges.
- Revise Guidelines and Protocols: Regularly assess and update protective policies to reflect changes in regulations and emerging threats, ensuring that adherence efforts remain relevant and effective.
- : Provide continuous training to ensure employees are informed about regulatory requirements and best practices. Ongoing awareness training empowers staff to identify threats and understand appropriate responses, fostering a culture of compliance throughout the organization.
- : Conduct regular drills to evaluate the effectiveness of the incident response plan, ensuring the organization is prepared to respond swiftly to potential breaches. This aligns with findings that 40% of adherence teams experienced a security breach due to manual practices, highlighting the necessity for preparedness.
- Documentation: Maintain , assessments, and incidents. This documentation is vital for demonstrating compliance and facilitating continuous improvement.
By integrating these practices into their operations, organizations can achieve compliance while reinforcing a robust security posture against evolving cyber threats. , in particular, is essential for early detection and rapid response, enabling organizations to adapt swiftly to the dynamic threat landscape. Furthermore, as Rick Stevenson noted, “90% of early adopters report AI is positively impacting the work they do in risk and compliance,” highlighting the significant role of technology in enhancing compliance efforts.
Conclusion
Achieving compliance with NIST 800-171 is essential for organizations that manage Controlled Unclassified Information (CUI). This framework not only ensures adherence to federal guidelines but also significantly enhances cybersecurity measures. By doing so, it fosters trust and minimizes the risks associated with data breaches. Organizations that understand and implement the requirements set forth by NIST 800-171 can effectively safeguard sensitive data and maintain operational integrity.
Key steps to achieving compliance include:
- Conducting a thorough gap analysis
- Developing a comprehensive System Security Plan
- Implementing robust security controls
Regular assessments and continuous training for employees are vital to ensure that organizations remain compliant and can adapt to the ever-evolving cybersecurity landscape. Additionally, engaging with regulatory consultants can provide valuable insights that streamline the compliance process and strengthen an organization’s defenses against potential threats.
Ultimately, the significance of NIST 800-171 compliance extends beyond mere regulatory adherence; it embodies a proactive approach to cybersecurity that can protect organizations from severe legal repercussions while enhancing their overall reputation. Embracing these best practices not only mitigates risks but also positions organizations to thrive in a competitive environment where data security is paramount. Taking action now to achieve and maintain NIST 800-171 compliance is not just a requirement; it is a strategic imperative for all organizations handling sensitive information.
Frequently Asked Questions
What is NIST 800-171?
NIST 800-171 is a document that outlines essential guidelines from the National Institute of Standards and Technology for safeguarding Controlled Unclassified Information (CUI) in non-federal systems.
Why is NIST 800-171 compliance important?
Compliance with NIST 800-171 is crucial for protecting sensitive data from unauthorized access and breaches, fulfilling federal requirements, enhancing a company’s cybersecurity posture, fostering customer trust, and mitigating risks associated with data breaches.
What benefits can organizations expect from implementing NIST 800-171 guidelines?
Organizations that implement NIST 800-171 guidelines can expect notable improvements in their protection frameworks, which may prevent or lessen the impact of data breaches.
What are the consequences of failing to comply with NIST 800-171?
Failing to comply with NIST 800-171 can lead to severe legal consequences, including hefty fines and the risk of losing contracts, particularly in highly regulated industries such as finance and healthcare.
How does NIST 800-171 relate to the evolving cybersecurity landscape?
As the cybersecurity landscape evolves, robust NIST 800-171 compliance frameworks become increasingly critical for maintaining operational integrity and safeguarding sensitive information.