Introduction
In an era marked by escalating cyber threats, organizations within regulated industries confront the pressing challenge of ensuring compliance while simultaneously protecting sensitive data. The implications are significant; a failure to implement robust incident response solutions can result in severe financial consequences and a loss of customer trust.
To effectively navigate these challenges, organizations must adopt essential strategies that not only fulfill regulatory requirements but also bolster their overall cybersecurity posture. This article explores the critical elements of an effective incident response plan, providing insights into best practices that empower organizations to manage crises with confidence.
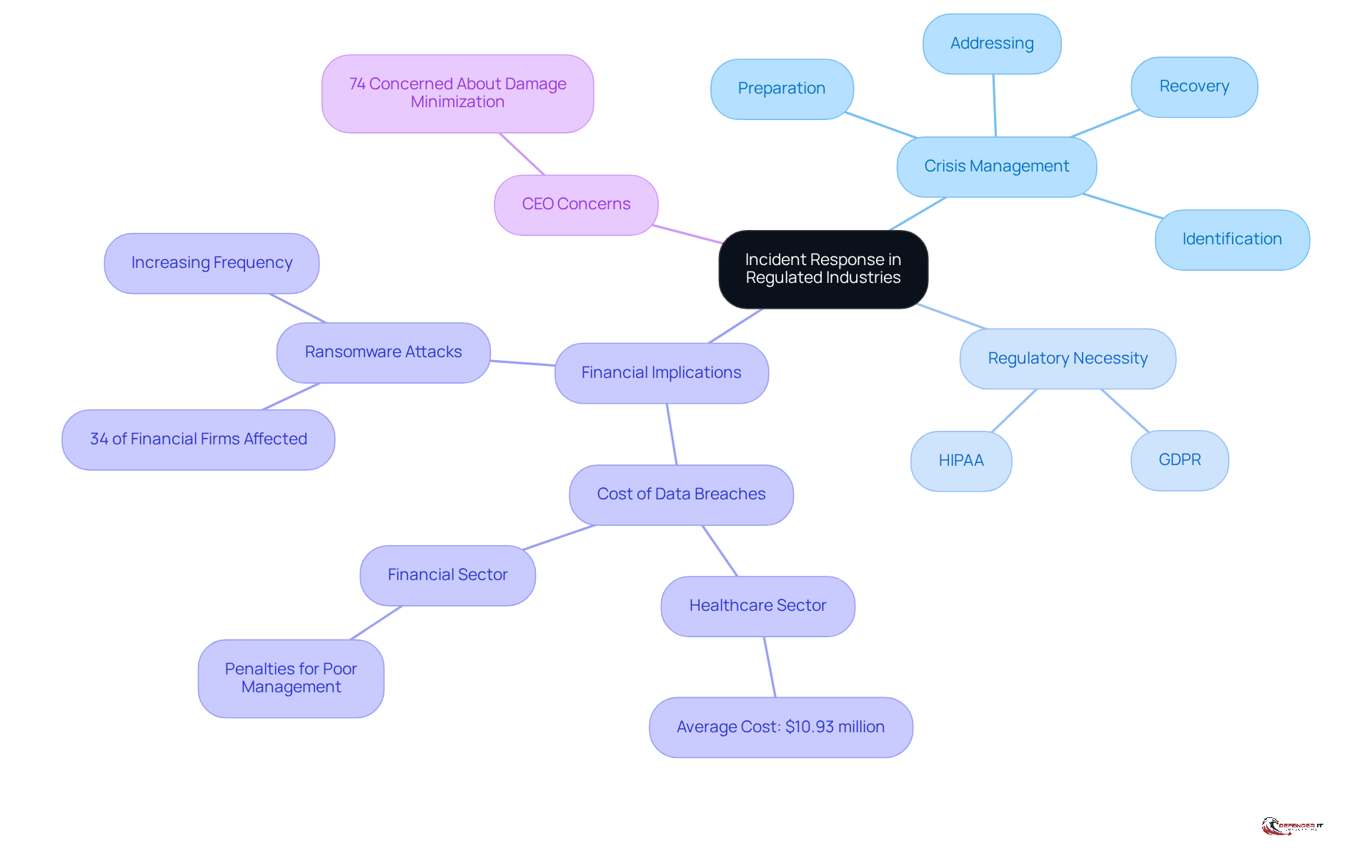
Define Incident Response and Its Importance in Regulated Industries
Crisis management (CM) is a systematic approach that organizations utilize to prepare for, identify, address, and recover from cybersecurity incidents by implementing incident response solutions. In regulated sectors such as finance and healthcare, effective event management transcends best practices; it is a regulatory necessity. Compliance with regulations like GDPR and HIPAA requires timely reporting and management of data breaches, highlighting the critical need for robust incident response solutions.
A well-structured response strategy not only mitigates harm and safeguards sensitive information but also preserves customer trust, thereby protecting the organization’s reputation and financial health. For example, financial institutions that inadequately manage data breaches face substantial penalties, with 34% of financial firms reporting ransomware attacks in 2021. In 2024, the average cost of a data breach in the healthcare sector escalated to $10.93 million, up from $9.77 million, underscoring the financial repercussions of poor management.
Moreover, 74% of CEOs express concern regarding their company’s capacity to minimize damages associated with cyberattacks. Therefore, emphasizing crisis management strategies is essential for organizations operating within these highly regulated environments.
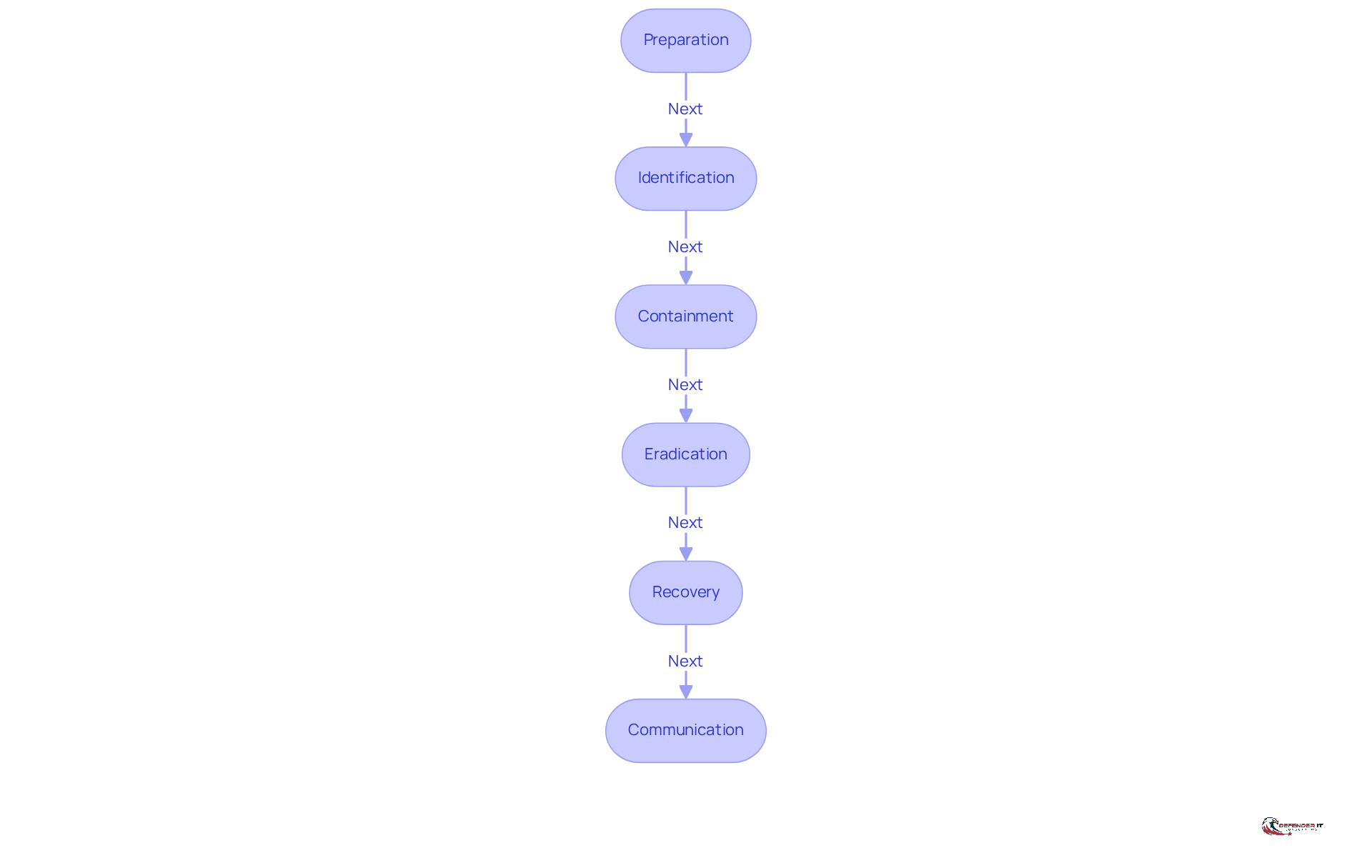
Develop Key Components of an Effective Incident Response Plan
A robust incident response solutions plan (IRP) is essential for organizations, particularly in regulated sectors, to effectively manage cybersecurity incidents. The key components of an effective IRP include:
-
Preparation: Establish a specialized response team with clearly defined roles and responsibilities. This team should engage in regular training and simulations to ensure readiness. Notably, statistics reveal that one in five companies lack any plan or procedure, underscoring the critical need for an IRP.
-
Identification: Employ advanced monitoring tools, such as Security Information and Event Management (SIEM) and Endpoint Detection and Response (EDR), to swiftly identify potential threats. Research indicates that organizations with effective detection mechanisms can significantly lower their Mean Time to Detect (MTTD).
-
Containment: Develop strategies to mitigate the impact of incidents, such as isolating affected systems to prevent further spread. This step is vital for minimizing damage and ensuring system availability.
-
Eradication: Determine the root cause of the incident and eliminate it from the environment. This process may involve forensic analysis tools to trace the origin of the event and prevent future occurrences.
-
Recovery: Restore systems to normal operations while addressing any vulnerabilities that were exploited. Tracking the Mean Time to Recovery (MTTR) is crucial for evaluating the efficiency of recovery efforts. Significantly, 42.7% of companies have cybersecurity response plans and review them annually or more, highlighting the importance of regular assessments.
-
Communication: Establish clear internal and external communication protocols to keep stakeholders informed throughout the incident lifecycle. Effective communication enhances collaboration and reduces confusion during critical moments.
By integrating these elements, organizations can formulate a comprehensive event management strategy that incorporates incident response solutions, ensuring it meets regulatory requirements while also strengthening their overall cybersecurity posture.
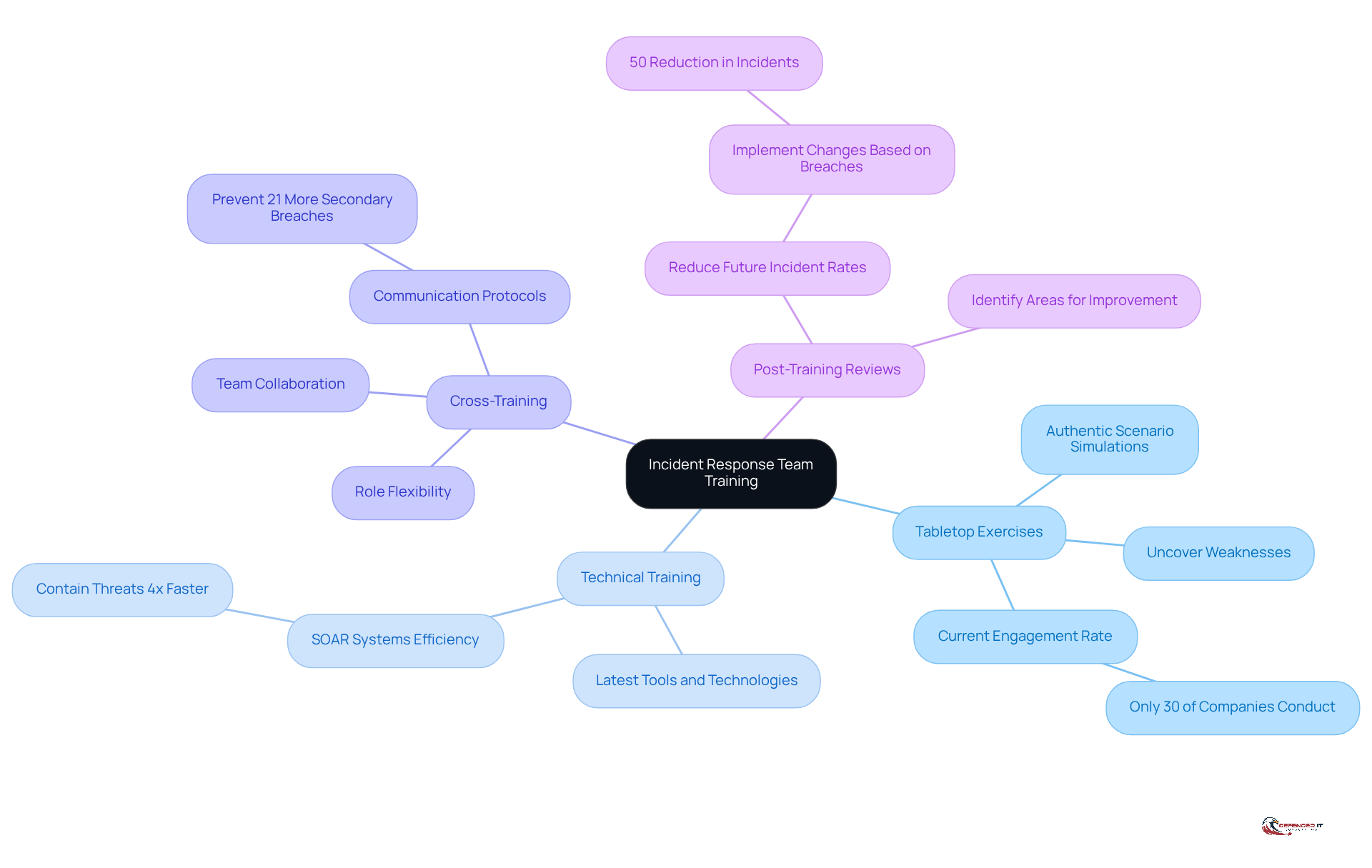
Train and Prepare Incident Response Teams for Effective Execution
Training cybersecurity management groups is essential for effective execution during security events. Organizations must prioritize regular training sessions that encompass several key components:
-
Tabletop Exercises: These simulations create authentic scenarios, allowing groups to practice their handling and decision-making procedures. Organizations that conduct tabletop drills can uncover hidden weaknesses in their crisis management strategies, thereby enhancing overall readiness against cyber threats. Notably, only 30% of companies engage in tabletop exercises to simulate real-world attack scenarios, underscoring the need for broader adoption.
-
Technical Training: Keeping group members informed about the latest tools and technologies is crucial for efficient crisis management. This training ensures that the group can utilize advanced solutions, such as Security Orchestration, Automation, and Response (SOAR) systems, which can contain threats four times faster than manual methods.
-
Cross-Training: Encouraging team members to learn different roles within the event management framework enhances flexibility and collaboration. This approach fosters a culture of teamwork, which is vital during high-stress situations, as effective crisis management is a collective effort. Organizations with clear internal communication protocols prevent 21% more secondary breaches caused by poorly managed efforts, highlighting the importance of structured communication during events.
-
Post-Training Reviews: Conducting evaluations after training sessions is critical for identifying areas for improvement. Organizations that implement changes based on previous breaches can reduce future occurrence rates by 50%, emphasizing the importance of ongoing learning and adaptation. As Peter Steinfeld aptly states, “If you can’t communicate, you can’t recover,” making communication a fundamental aspect of crisis management training.
By investing in comprehensive training, organizations can ensure that their crisis management teams are well-prepared to address situations promptly and effectively, ultimately safeguarding their operations and reputation.
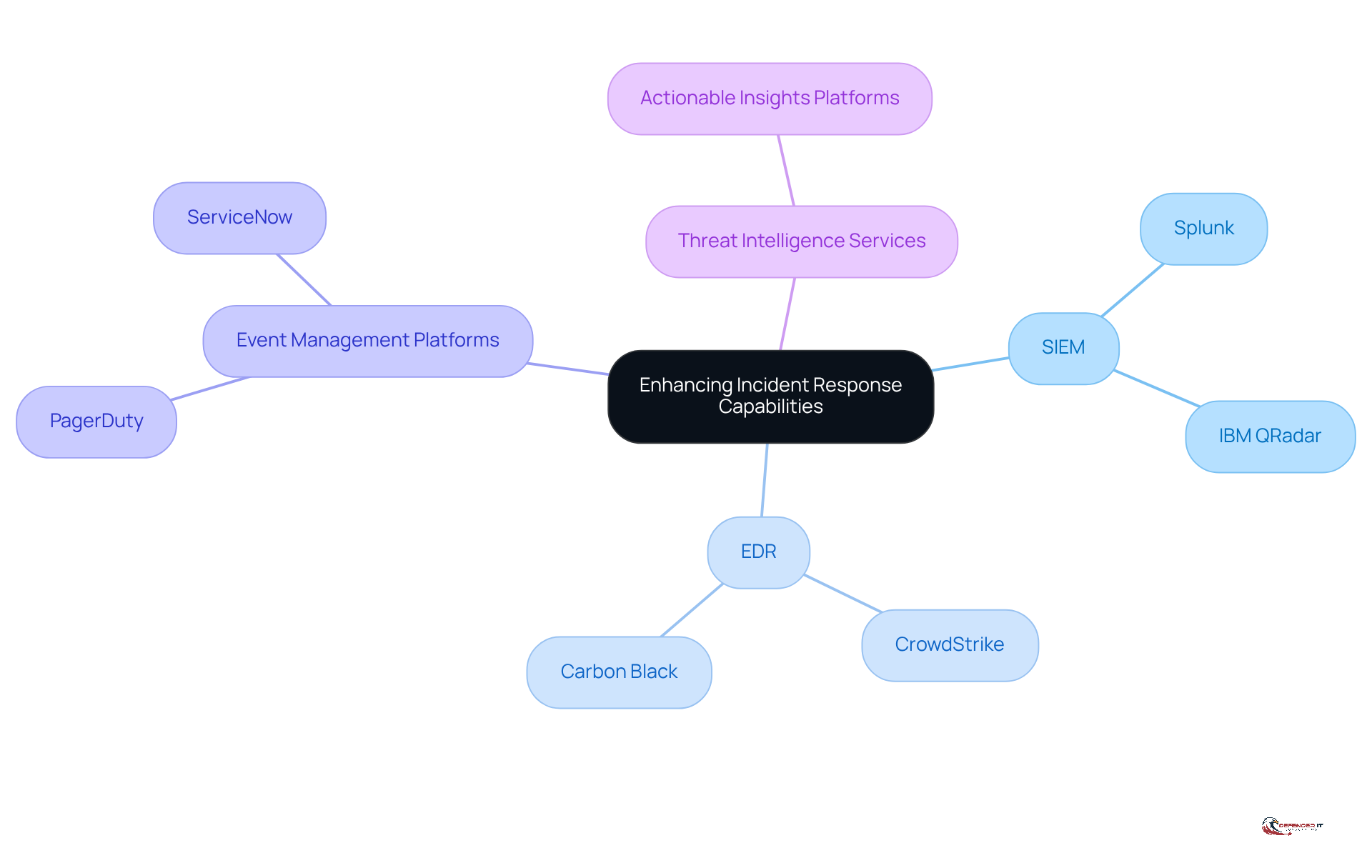
Leverage Technology and Tools to Enhance Incident Response Capabilities
To enhance event handling capabilities, organizations should incorporate a range of technologies and tools:
-
Security Information and Event Management (SIEM): Tools such as Splunk and IBM QRadar are essential for aggregating and analyzing security data in real-time, providing organizations with immediate insights into potential threats.
-
Endpoint Detection and Response (EDR): Solutions like CrowdStrike and Carbon Black deliver advanced threat detection and mitigation capabilities, ensuring that endpoints are continuously monitored and protected against emerging threats.
-
Event Management Platforms: Tools including PagerDuty and ServiceNow improve event tracking and communication, facilitating a more efficient response to incidents.
-
Threat Intelligence Services: Organizations should utilize platforms that offer actionable insights into emerging threats, enabling proactive measures to be taken before incidents occur.
By integrating these technologies into their event management strategy, organizations can significantly enhance their processes through effective incident response solutions for detection, response, and recovery.
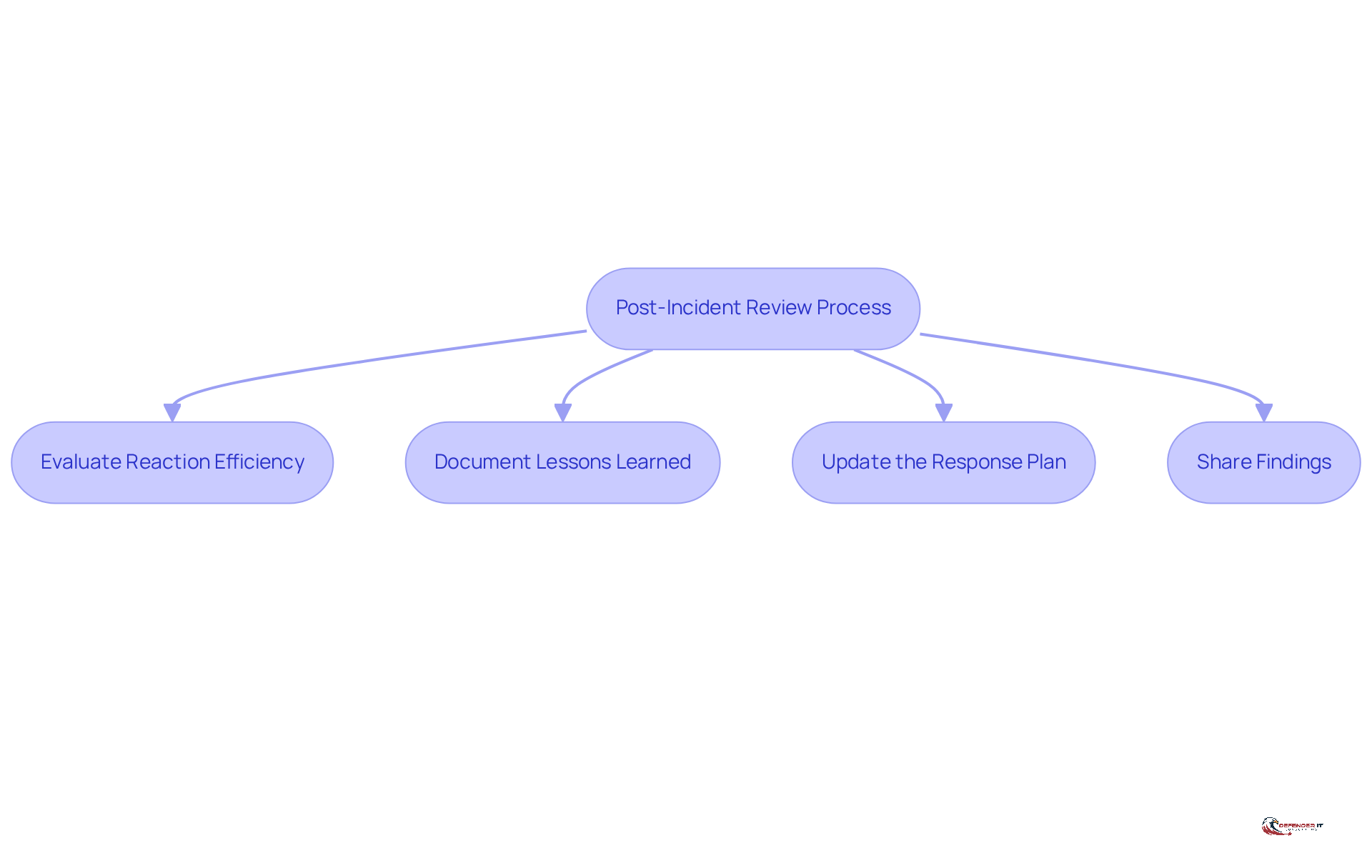
Implement Continuous Improvement Through Post-Incident Reviews
Post-event evaluations are essential for fostering continuous improvement in event management strategies. Organizations should conduct these reviews after every significant incident to achieve several key objectives:
-
Evaluate Reaction Efficiency: Assess the implementation of the event management strategy, identifying strengths and weaknesses in the reaction process. This evaluation is crucial, as entities that document their post-breach findings can significantly enhance their reaction time and accuracy. Additionally, evaluating the team’s performance encompasses aspects such as detection and containment, timeliness, communication clarity, and adherence to established procedures.
-
Document Lessons Learned: Capture valuable insights and recommendations that arise from the review. This documentation not only aids in refining future responses but also assists organizations in addressing systemic challenges, such as process confusion and alert fatigue, which can hinder effective incident management. Notably, only 40% of companies document post-breach findings, underscoring the necessity for structured reviews.
-
Update the Response Plan: Revise the response plan based on the insights gained from the review. This iterative process ensures that the plan adapts to emerging threats and incorporates lessons learned from previous events, ultimately enhancing its effectiveness. Conducting these evaluations ideally within 24-72 hours of addressing an incident ensures that details remain fresh in everyone’s minds, reducing the risk of memory lapses.
-
Share Findings: Communicate the lessons learned with relevant stakeholders to foster a culture of transparency and continuous improvement. Involving various stakeholders in the review process can provide a comprehensive perspective on the event and encourage collaboration in strengthening security measures. As Pritesh Parekh emphasizes, a faultless culture is the foundation of effective issue analysis, enabling teams to discuss errors openly and derive insights from them.
By establishing a structured post-event review process, organizations can significantly enhance their response capabilities. High-performing security teams that conduct thorough post-mortem analyses after incidents are better equipped to adapt and respond to future threats, ultimately leading to a more resilient cybersecurity posture.
Conclusion
In regulated industries, effective incident response solutions are not just best practices; they are critical requirements for compliance and operational integrity. Organizations must prioritize robust incident response plans to safeguard sensitive data, maintain regulatory compliance, and protect their reputations. By establishing a structured approach to crisis management, businesses can mitigate the risks associated with cybersecurity incidents and foster a culture of preparedness.
This article outlines several key components essential for developing an effective incident response plan:
- Preparation
- Identification
- Containment
- Eradication
- Recovery
- Communication
It emphasizes the importance of training incident response teams through realistic simulations and ongoing education, ensuring they are equipped to handle crises efficiently. Leveraging advanced technologies and tools further enhances an organization’s capabilities, allowing for quicker detection and response to threats. Additionally, conducting post-incident reviews is crucial for learning from past events and continually improving response strategies.
Ultimately, organizations in regulated sectors must recognize that a proactive and well-coordinated incident response strategy is vital not only for compliance but also for sustaining trust and resilience in an increasingly complex cybersecurity landscape. By committing to these best practices, businesses can navigate the challenges posed by cyber threats more effectively, ensuring they are prepared to respond and emerge stronger from any incident.
Frequently Asked Questions
What is incident response and why is it important in regulated industries?
Incident response is a systematic approach used by organizations to prepare for, identify, address, and recover from cybersecurity incidents. In regulated industries like finance and healthcare, effective incident response is not just a best practice but a regulatory requirement, as compliance with regulations such as GDPR and HIPAA mandates timely reporting and management of data breaches.
What are the consequences of poor incident management in regulated sectors?
Poor incident management can lead to significant financial repercussions, such as penalties for financial institutions and increased costs associated with data breaches. For instance, the average cost of a data breach in the healthcare sector rose to $10.93 million in 2024. Additionally, inadequate management can damage customer trust and the organization’s reputation.
What are the key components of an effective incident response plan (IRP)?
The key components of an effective IRP include: – Preparation: Establish a specialized response team with defined roles and regular training. – Identification: Use advanced monitoring tools to swiftly detect threats. – Containment: Develop strategies to mitigate the impact of incidents. – Eradication: Identify and eliminate the root cause of the incident. – Recovery: Restore systems to normal operations and address any vulnerabilities. – Communication: Establish clear communication protocols for stakeholders.
How does preparation contribute to incident response effectiveness?
Preparation involves forming a specialized response team with clearly defined roles and responsibilities, along with regular training and simulations. This readiness is crucial, as statistics show that one in five companies lack any incident response plan, highlighting the need for effective preparation.
What role does identification play in incident response?
Identification involves employing advanced monitoring tools, such as Security Information and Event Management (SIEM) and Endpoint Detection and Response (EDR), to quickly detect potential threats. Effective detection mechanisms can significantly reduce the Mean Time to Detect (MTTD), allowing for a quicker response to incidents.
Why is containment important during a cybersecurity incident?
Containment strategies are vital for minimizing damage and ensuring system availability by isolating affected systems to prevent further spread of the incident.
How is the eradication phase conducted in an incident response plan?
The eradication phase involves determining the root cause of the incident and eliminating it from the environment, often utilizing forensic analysis tools to trace the origin and prevent future occurrences.
What does the recovery phase entail in incident response?
Recovery involves restoring systems to normal operations while addressing any vulnerabilities that were exploited during the incident. Tracking the Mean Time to Recovery (MTTR) is crucial to assess the efficiency of recovery efforts.
How does communication factor into incident response?
Effective communication is essential during an incident, as it establishes clear internal and external protocols to keep stakeholders informed throughout the incident lifecycle, enhancing collaboration and reducing confusion.
What percentage of companies have cybersecurity response plans and how often are they reviewed?
Approximately 42.7% of companies have cybersecurity response plans and review them annually or more, emphasizing the importance of regular assessments to maintain an effective incident response strategy.