Introduction
Manufacturers today face a landscape increasingly threatened by cyber attacks, where the convergence of operational technology and information technology creates unique vulnerabilities. With cybercriminals targeting this sector with alarming frequency, understanding and implementing effective cybersecurity measures is not merely an option; it is a necessity for safeguarding assets and ensuring operational resilience.
How can manufacturers navigate these complexities and emerge successfully in the face of evolving threats? This article explores five essential best practices that can fortify manufacturing operations against cyber risks, ensuring both compliance and security in an ever-changing digital environment.
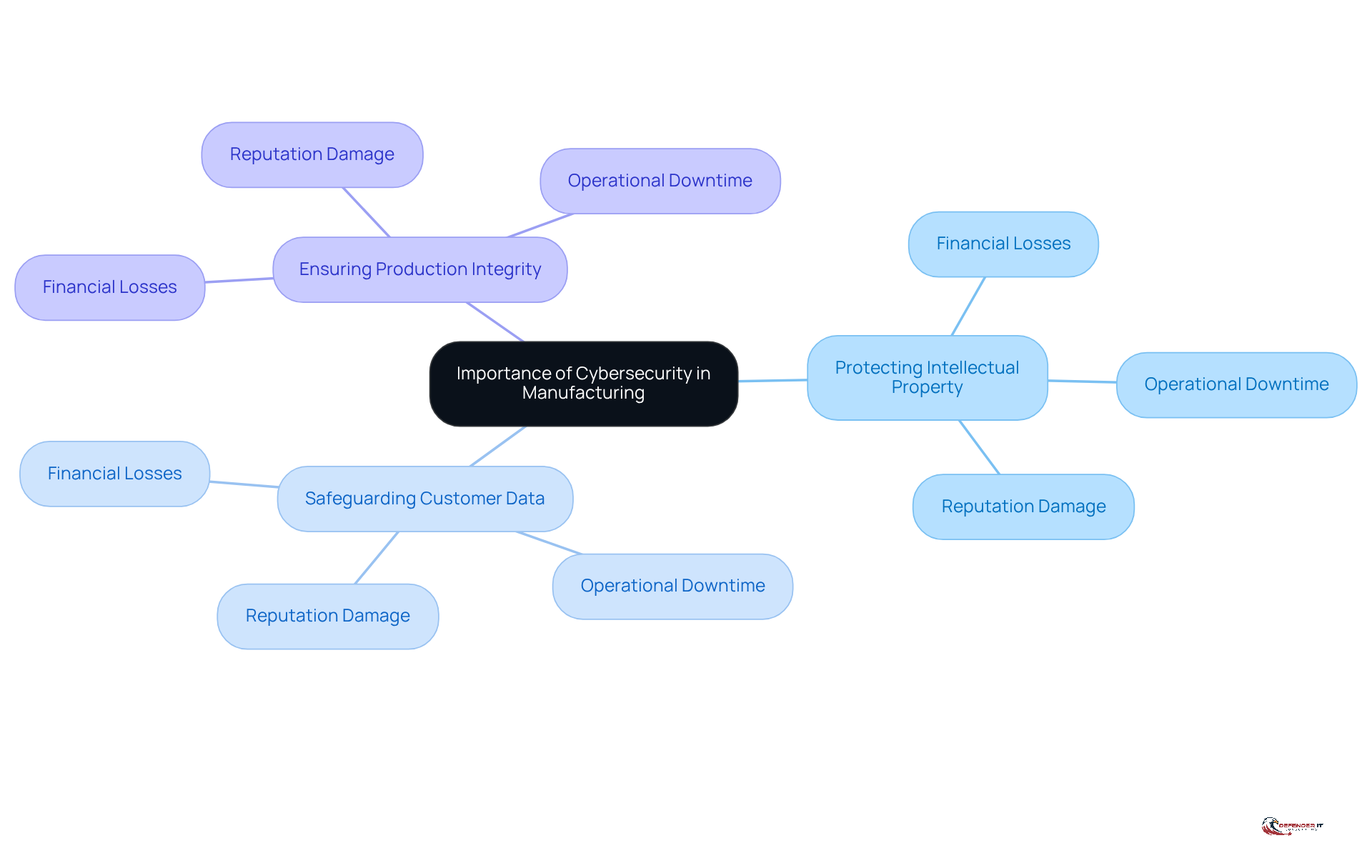
Understand the Importance of Cybersecurity in Manufacturing
is crucial in the manufacturing sector, where operational technology (OT) and information technology (IT) intersect. The unique challenges manufacturers face include:
- Protecting
- Safeguarding
- Ensuring the integrity of
A breach can result in substantial , operational downtime, and damage to reputation. For example, a can disrupt production lines, costing manufacturers millions in lost revenue. Notably, the manufacturing sector has been the most for four consecutive years, as reported in the IBM X-Force Threat Intelligence Report 2025.
Recognizing the is the first step toward establishing a robust manufacturing operation. Organizations must understand that is not merely an IT issue; it is a vital business priority that impacts overall .
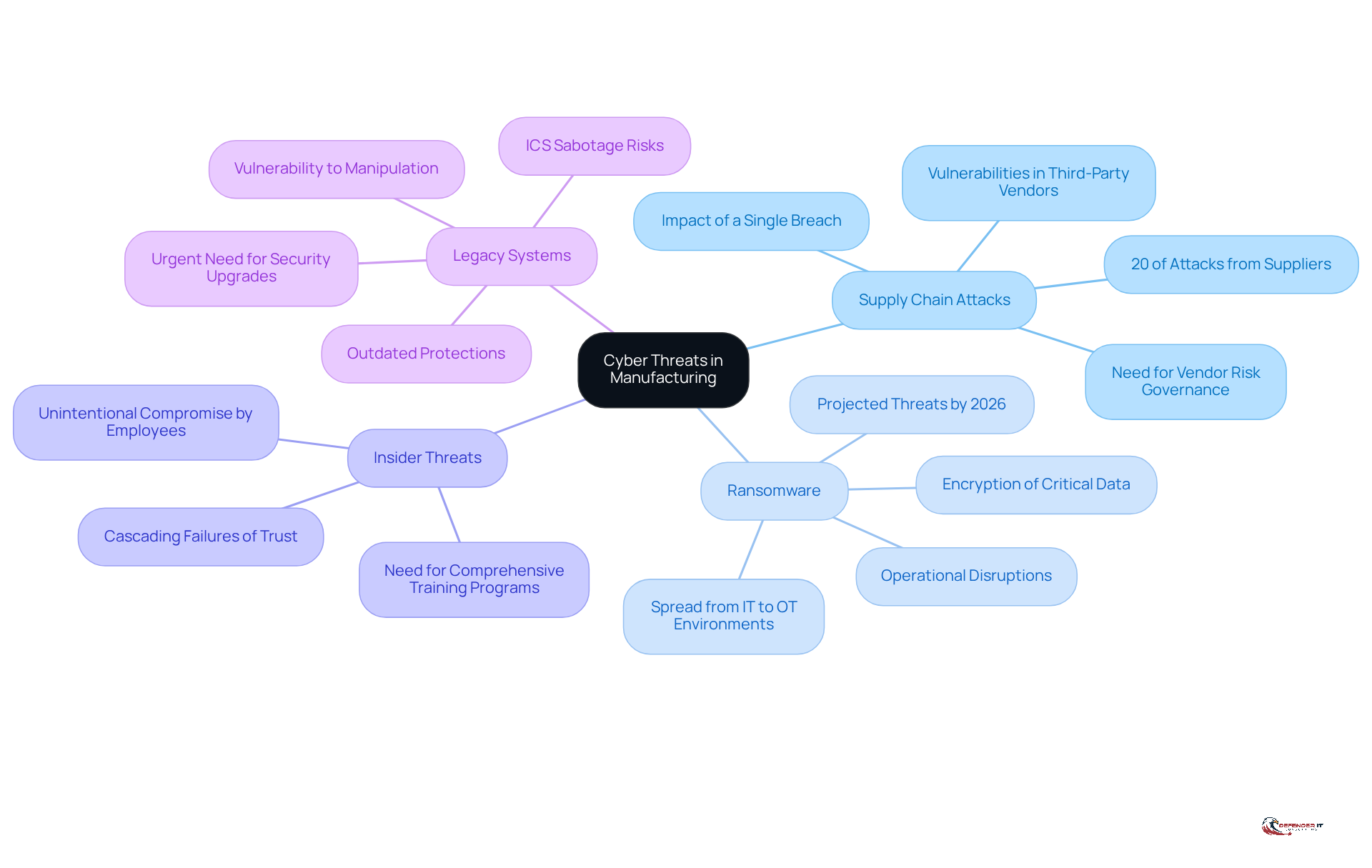
Identify Key Cyber Threats and Vulnerabilities in Manufacturing
Manufacturers need to prioritize as they face increasing threats from cybercriminals, primarily due to their reliance on interconnected systems and the high value of their intellectual property. Understanding these threats is crucial for prioritizing manufacturing cyber and developing effective .
: Cybercriminals often exploit vulnerabilities in third-party vendors to infiltrate manufacturing systems. A single breach in the supply chain can disrupt multiple dependent entities, underscoring the necessity for robust . Notably, approximately 20% of attacks in the manufacturing sector stem from supplier vulnerabilities, emphasizing the importance of implementing measures to ensure that all vendors adhere to stringent standards. have emerged as the most significant global cyber risk, surpassing traditional cyber intrusions, making it imperative for manufacturers to proactively address manufacturing cybersecurity threats.
Ransomware: This form of malware can encrypt critical data, demanding payment for decryption, and can lead to severe . (OT) are projected to pose the greatest risk to industrial companies by 2026, as they can halt operations and jeopardize safety. Most ransomware incidents initiate in the IT environment through phishing or compromised credentials, which can then spread laterally into OT environments, amplifying the impact and resulting in serious operational consequences.
Insider Threats: Employees with access to sensitive information can unintentionally or maliciously compromise security. The interconnected nature of modern means that insider risks can lead to cascading failures of trust. Therefore, it is essential for organizations to cultivate a culture of vigilance and implement comprehensive training programs aimed at minimizing .
: Many manufacturers continue to operate outdated systems that lack modern protections, making them vulnerable to attacks. The prevalence of legacy equipment in industrial environments heightens susceptibility to manipulation and sabotage, as evidenced by incidents where attackers exploited system vulnerabilities to disrupt operations. The escalating risk of industrial control system (ICS) sabotage from outdated systems further emphasizes the urgent need for manufacturing cybersecurity to improve security infrastructure.
By recognizing these threats, manufacturers can effectively prioritize their and develop tailored strategies to mitigate risks, thereby ensuring the integrity and safety of their operations.
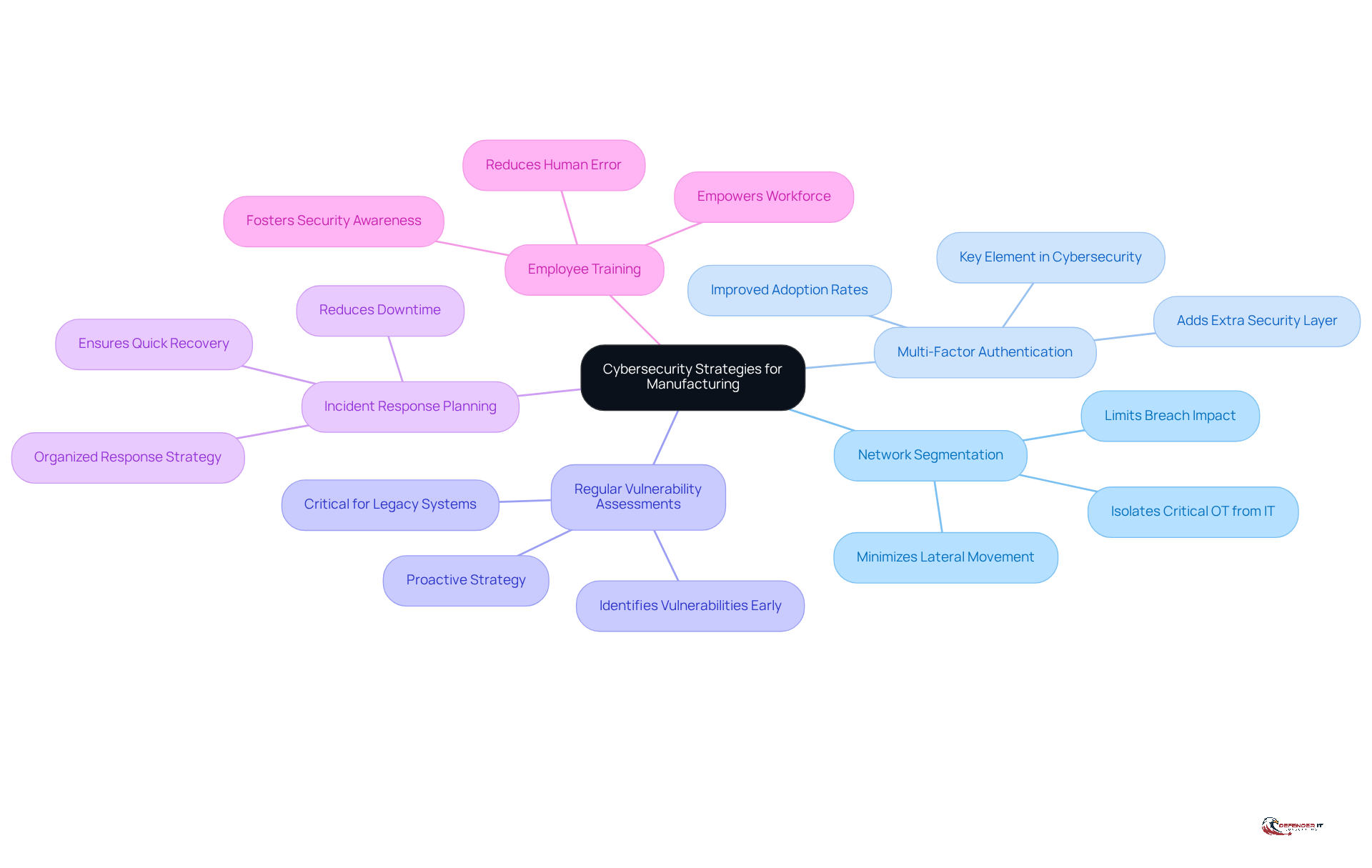
Implement Proven Cybersecurity Strategies for Manufacturing Success
To enhance cybersecurity, manufacturers should adopt the following proven strategies:
- : Isolating critical operational technology (OT) from corporate IT networks is essential to minimize the risk of lateral movement by attackers. This practice not only protects sensitive systems but also limits the potential impact of a breach, ensuring that vulnerabilities in one area do not compromise the entire network.
- : The adoption of MFA is crucial for adding an extra layer of security when accessing sensitive systems and data. As of 2026, the implementation rates of MFA in manufacturing have shown significant improvement, reflecting a growing recognition of its importance in safeguarding against unauthorized access. According to recent reports, producers are increasingly prioritizing MFA as a key element of their , with adoption rates rising to over 70% in regulated sectors.
- : Conducting frequent assessments is vital for identifying and remediating vulnerabilities before they can be exploited. This and upholding a secure operational environment. Given the challenges posed by legacy systems and increased IT/OT connectivity, regular assessments are more critical than ever.
- : Developing and regularly updating an incident response plan ensures quick recovery from cyber incidents. A well-organized strategy enables organizations to react efficiently to dangers, reducing downtime and operational disruption.
- : Regular training on digital security best practices is essential to reduce the risk of human error, which is often a significant factor in breaches. By fostering a culture of security awareness, producers can empower their workforce to recognize and respond to potential threats.
By implementing these strategies, manufacturers can establish a strong that not only but also enhances their operational resilience.
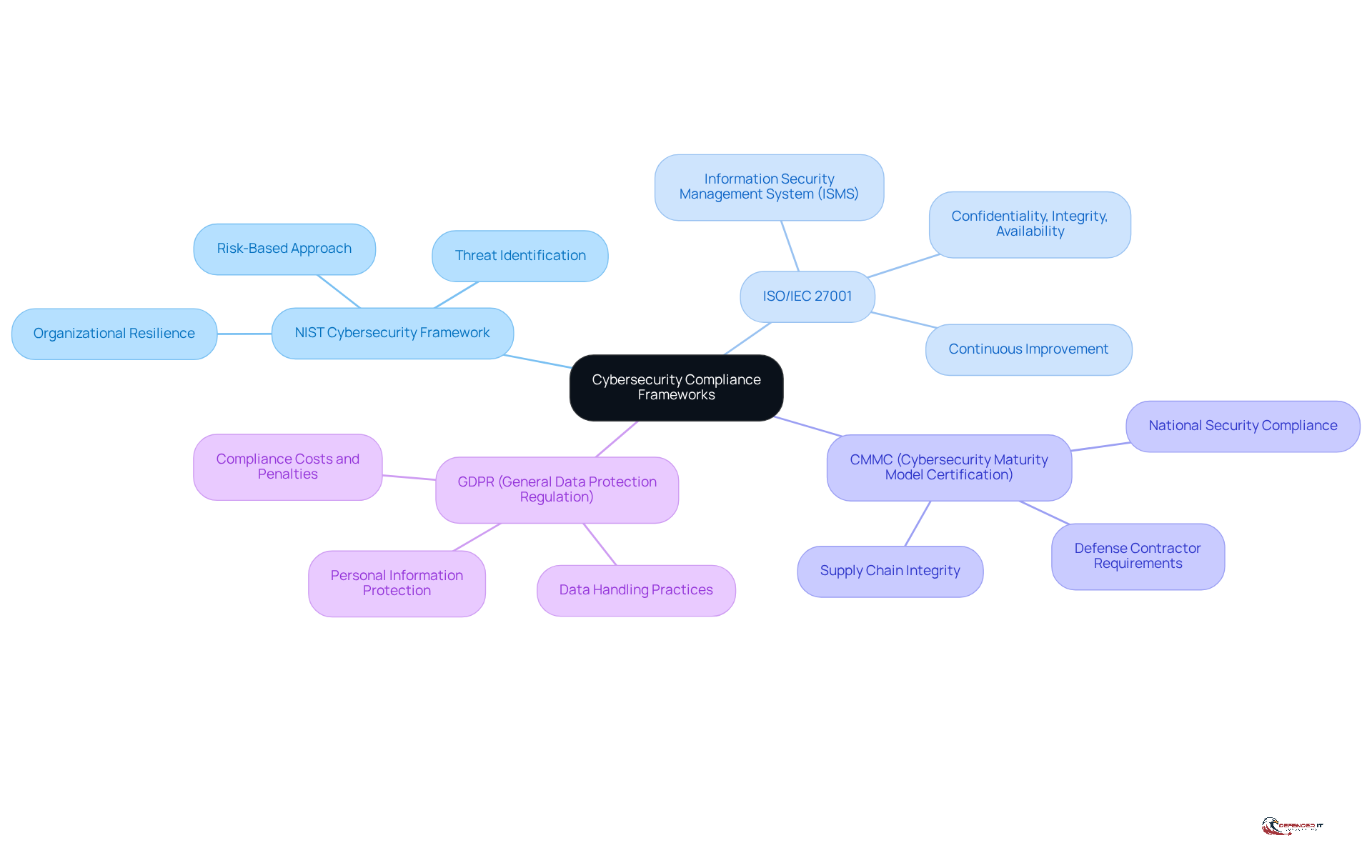
Ensure Compliance with Cybersecurity Regulations and Standards
Producers must navigate a complex landscape of online security regulations and standards to safeguard their operations and mitigate legal risks. Key compliance frameworks include:
- : This framework provides comprehensive guidelines for managing and enhancing organizational resilience. It emphasizes a risk-based approach, enabling producers to identify, assess, and respond to potential threats effectively. As Ephraim Batambuze III notes, “Companies can no longer treat compliance as a side task handled only by technical teams.”
- : This standard focuses on establishing, implementing, maintaining, and continually improving an information security management system (ISMS). By adhering to , manufacturers can systematically manage sensitive information as part of their efforts, ensuring its confidentiality, integrity, and availability.
- : Specifically required for defense contractors, CMMC ensures compliance with stringent cybersecurity standards. As the defense sector faces increasing cyber threats, adherence to CMMC is crucial for maintaining and national security. Amy Thompson emphasizes that “defense and aerospace suppliers must strengthen protections to meet new CMMC 2.0 requirements.”
- : For producers operating within or engaging with the European Union, adherence to GDPR is essential for . This regulation mandates strict data handling practices, and non-compliance can result in significant fines and reputational damage.
Manufacturers also face challenges regarding and the complexities of navigating multiple jurisdictions in the realm of . For instance, small aerospace companies are experiencing financial strain due to the accumulation of complex regulatory requirements, which may force some to reconsider their participation in the defense marketplace. By ensuring compliance with these regulations, producers not only protect themselves from possible penalties but also enhance their credibility and trustworthiness in the marketplace. The proactive implementation of these frameworks enables organizations to better and respond to the changing digital security environment.
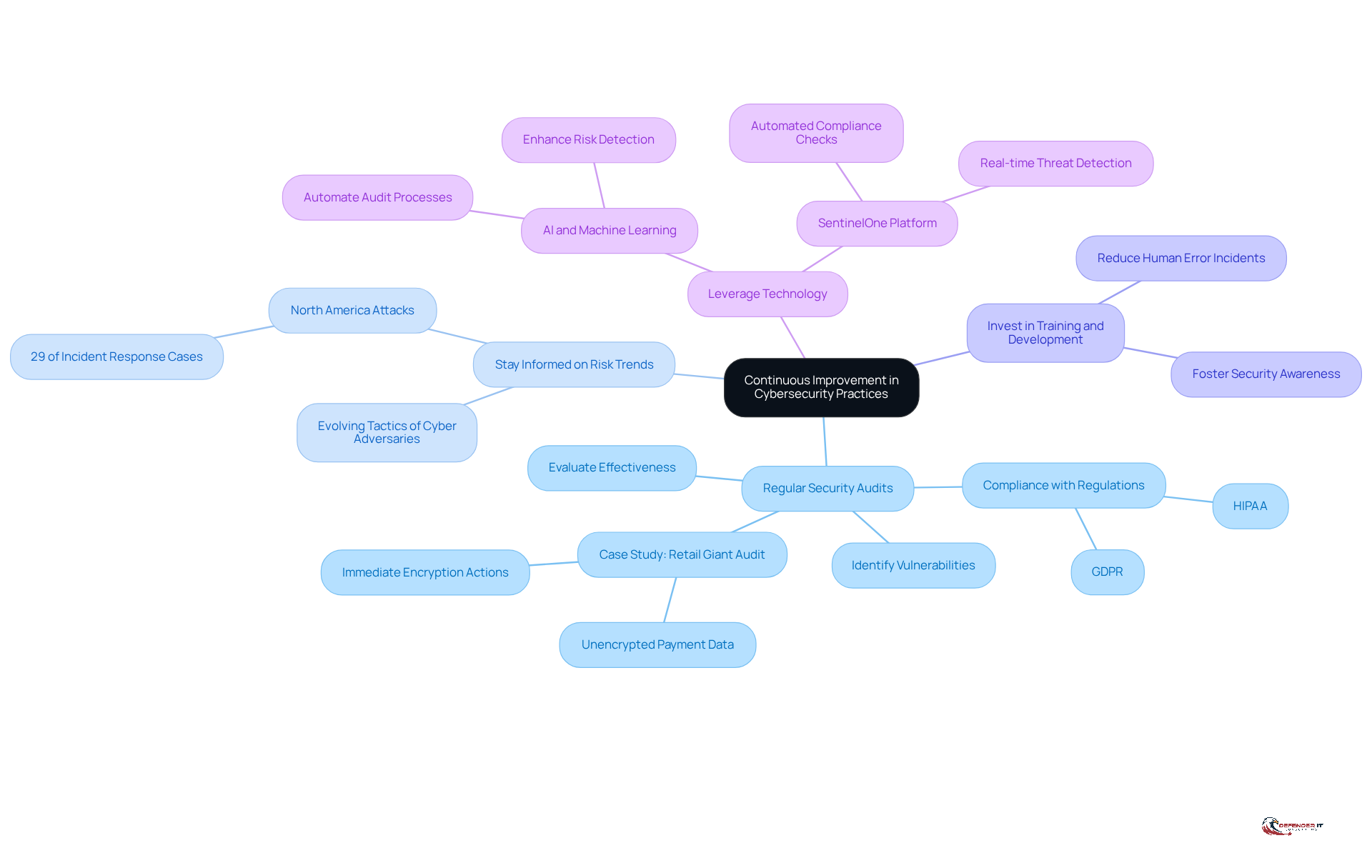
Maintain Continuous Improvement in Cybersecurity Practices
To effectively combat , manufacturers must embrace a culture of continuous improvement in their cybersecurity practices. This commitment is essential for against evolving threats.
- : Conducting security audits is crucial for evaluating the effectiveness of existing security measures and identifying vulnerabilities. These audits not only help organizations comply with regulations like GDPR and HIPAA but also provide a comprehensive vulnerability report that highlights areas needing attention. For instance, a recent inspection of a retail giant uncovered unencrypted payment information in its system, prompting swift encryption actions to prevent potential breaches. This example illustrates the essential role of audits in avoiding incidents.
- : Keeping up with the latest online security risks and trends is vital for adapting strategies. In 2025, North America became the most attacked region, accounting for 29% of incident response cases, a notable shift from the Asia Pacific region. This statistic underscores the need for vigilance against the evolving tactics employed by cyber adversaries.
- : Ongoing education for staff on new dangers and safety practices fosters a culture of security awareness. Organizations that prioritize training can significantly reduce the risk of incidents caused by human error, which remains a common vulnerability.
- : Utilizing advanced technologies such as AI and machine learning enhances risk detection and response capabilities. Automated tools can quickly identify vulnerabilities and anomalies, streamlining the audit process and ensuring that organizations remain proactive in their defense strategies.
By committing to these , manufacturers can ensure their cybersecurity measures evolve alongside the threat landscape.
Conclusion
Manufacturing cybersecurity stands as a cornerstone of contemporary industrial operations, where the convergence of operational technology and information technology introduces distinct vulnerabilities. Recognizing the critical importance of cybersecurity not only safeguards sensitive data and intellectual property but also upholds the integrity of production processes. As cyber threats continue to evolve, it is imperative for manufacturers to understand that robust cybersecurity measures are essential for operational success and effective risk management.
This article outlines several key strategies to enhance manufacturing cybersecurity. These strategies encompass a thorough understanding of specific threats, including supply chain attacks and ransomware, alongside the implementation of established practices such as:
- Network segmentation
- Multi-factor authentication
- Regular vulnerability assessments
Furthermore, adherence to cybersecurity regulations and fostering a culture of continuous improvement are vital for adapting to the dynamic landscape of cyber threats.
The significance of strong cybersecurity practices within the manufacturing sector cannot be overstated. By prioritizing these measures, organizations can not only protect their operations but also bolster their resilience against potential cyber incidents. Adopting a proactive approach to cybersecurity empowers manufacturers to excel in a digital environment where security is paramount, thereby ensuring long-term success and stability in a competitive market.
Frequently Asked Questions
Why is cybersecurity important in the manufacturing sector?
Cybersecurity is crucial in manufacturing because it protects intellectual property, safeguards sensitive customer data, and ensures the integrity of production processes. A breach can lead to significant financial losses, operational downtime, and damage to reputation.
What are the main cyber threats facing manufacturers?
The main cyber threats include supply chain attacks, ransomware, insider threats, and vulnerabilities associated with legacy systems. Each of these threats can disrupt operations and compromise sensitive information.
What is a supply chain attack and why is it significant for manufacturers?
A supply chain attack occurs when cybercriminals exploit vulnerabilities in third-party vendors to infiltrate manufacturing systems. This type of attack is significant because approximately 20% of attacks in the manufacturing sector stem from supplier vulnerabilities, highlighting the need for robust vendor risk governance.
How does ransomware affect manufacturing operations?
Ransomware can encrypt critical data and demand payment for decryption, leading to severe operational disruptions. It poses a significant risk to industrial companies, especially as many incidents begin in the IT environment and can spread to operational technology (OT).
What are insider threats in the context of manufacturing cybersecurity?
Insider threats refer to risks posed by employees who may unintentionally or maliciously compromise security. They can lead to cascading failures of trust, making it essential for organizations to foster a culture of vigilance and implement comprehensive training programs.
Why are legacy systems a concern for manufacturing cybersecurity?
Legacy systems often lack modern protections, making them vulnerable to attacks. Their prevalence in industrial environments increases susceptibility to manipulation and sabotage, necessitating improved security infrastructure.
How can manufacturers prioritize their cybersecurity investments?
Manufacturers can prioritize cybersecurity investments by understanding the key threats they face, such as supply chain attacks and ransomware, and developing tailored strategies to mitigate these risks, ensuring the integrity and safety of their operations.
List of Sources
- Understand the Importance of Cybersecurity in Manufacturing
- Cybersecurity 2026: AI, CISA, manufacturing sector all in the hot seat (https://cybersecuritydive.com/news/cyber-trends-outlook-2026/810708)
- Why Manufacturing Is the #1 Cyberattack Target in 2026 — And What to Do About It (https://blog.cybelesoft.com/manufacturing-cybersecurity-zero-trust-2026)
- Cyber risks grow as manufacturers turn to AI and cloud systems (https://manufacturingdive.com/news/cyber-risks-grow-as-manufacturers-turn-to-ai-and-cloud-systems/808049)
- Ransomware Remains Top Cyber Risk for U.S. Manufacturers (https://advancedmanufacturing.org/news-desk/ransomware-remains-top-cyber-risk-for-u-s-manufacturers/article_31ebabd5-2acf-4a90-8eb4-7479fc7a94b8.html)
- The Rules Of Cyber Risk Are Changing, Manufacturers’ OT Has To Keep Up (https://forbes.com/sites/lisacaldwell/2026/02/02/the-rules-of-cyber-risk-are-changing-manufacturers-ot-has-to-keep-up)
- Identify Key Cyber Threats and Vulnerabilities in Manufacturing
- Top Cybersecurity Threats in the Manufacturing Industry 2026 – Hoxhunt (https://hoxhunt.com/blog/cyber-security-threats-in-manufacturing-industry)
- Cyber threats to watch in 2026 – and other cybersecurity news (https://weforum.org/stories/2026/02/2026-cyberthreats-to-watch-and-other-cybersecurity-news)
- Supply chain attacks emerge as top global cyber threat in 2026 (https://gulfnews.com/technology/supply-chain-attacks-emerge-as-top-global-cyber-threat-in-2026-1.500456194)
- consilien.com (https://consilien.com/news/cybersecurity-threats-facing-manufacturers-in-2026)
- Key Threat for 2026 (https://mbtmag.com/cybersecurity/blog/22956096/key-threat-for-2026)
- Implement Proven Cybersecurity Strategies for Manufacturing Success
- Cybersecurity 2026: AI, CISA, manufacturing sector all in the hot seat (https://cybersecuritydive.com/news/cyber-trends-outlook-2026/810708)
- 7 Key Manufacturing Cybersecurity Trends for 2026 | Huntress (https://huntress.com/blog/manufacturing-cybersecurity-trends)
- Why Manufacturing Is the #1 Cyberattack Target in 2026 — And What to Do About It (https://blog.cybelesoft.com/manufacturing-cybersecurity-zero-trust-2026)
- 2026 Will Be a Breakthrough Year for Cyberthreats: Four Predictions for Manufacturers (https://ien.com/redzone/blog/22958566/2026-will-be-a-breakthrough-year-for-cyberthreats-four-predictions-for-manufacturers)
- Industrial Cybersecurity in 2026: Our Top Defense Strategies – DirectIndustry e-Magazine (https://emag.directindustry.com/2026/03/02/industrial-cybersecurity-defense-strategies-operational-tech)
- Ensure Compliance with Cybersecurity Regulations and Standards
- New cybersecurity rules for US defense industry create barrier for some small suppliers (https://reuters.com/business/aerospace-defense/new-cybersecurity-rules-us-defense-industry-create-barrier-for-some-small-2026-02-20)
- AI, Cybersecurity and Workforce Trends Shape Manufacturing in 2026 (https://ccat.us/news-insights/trends-shape-manufacturing-in-2026)
- Cyber Insights 2026: Regulations and the Tangled Mess of Compliance Requirements (https://securityweek.com/cyber-insights-2026-regulations-and-the-tangled-mess-of-compliance-requirements)
- Everything You Need To Know About Cybersecurity Regulations In 2026 – PC Tech Magazine (https://pctechmag.com/2026/03/everything-you-need-to-know-about-cybersecurity-regulations-in-2026)
- The Rules Of Cyber Risk Are Changing, Manufacturers’ OT Has To Keep Up (https://forbes.com/sites/lisacaldwell/2026/02/02/the-rules-of-cyber-risk-are-changing-manufacturers-ot-has-to-keep-up)
- Maintain Continuous Improvement in Cybersecurity Practices
- Cybersecurity 2026: AI, CISA, manufacturing sector all in the hot seat (https://cybersecuritydive.com/news/cyber-trends-outlook-2026/810708)
- Security Audit: Importance, Process, and Best Practices 2026 (https://sentinelone.com/cybersecurity-101/cloud-security/security-audit)
- Cybersecurity Trends 2026 | IBM (https://ibm.com/think/insights/more-2026-cyberthreat-trends)
- consilien.com (https://consilien.com/news/cybersecurity-threats-facing-manufacturers-in-2026)
- 7 Key Manufacturing Cybersecurity Trends for 2026 | Huntress (https://huntress.com/blog/manufacturing-cybersecurity-trends)