Introduction
The rise of cyber threats has made robust cybersecurity measures more critical than ever. Organizations are increasingly seeking advanced solutions that go beyond traditional defenses. Managed Detection and Response (MDR) represents a game-changing approach, combining cutting-edge technology with expert human oversight to enhance security and compliance. However, the challenge lies in effectively implementing these solutions to maximize their potential.
What best practices can ensure successful integration and long-term resilience against evolving threats?
Define Managed Detection and Response (MDR)
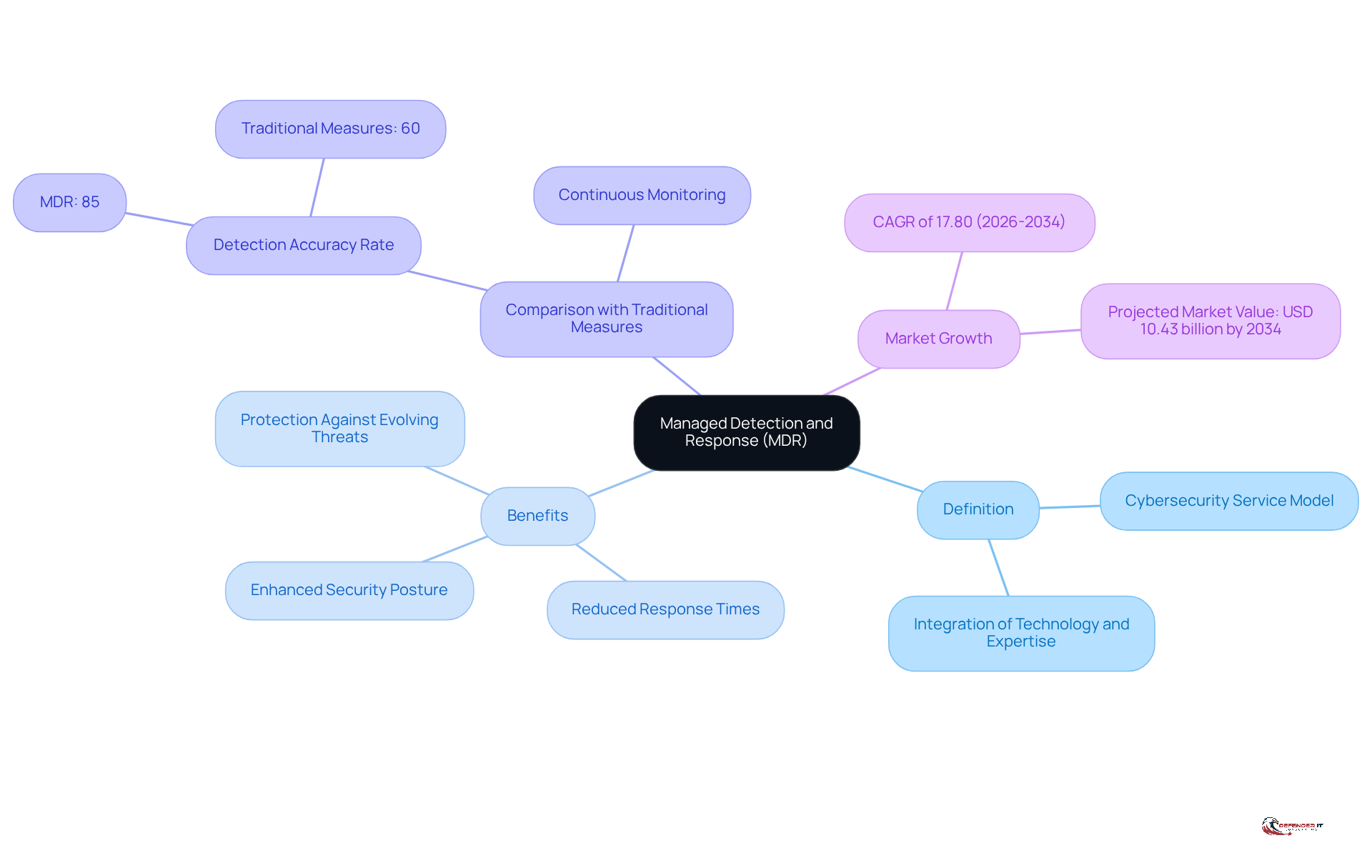
is a that integrates advanced technology with human expertise to . This model stands apart from traditional protective measures by offering and proactive risk hunting, enabling organizations to identify vulnerabilities and . This capability is especially vital for businesses operating in regulated industries, where compliance and data protection are critical.
By adopting MDR, organizations can enhance their , reduce response times, and effectively protect their against evolving threats. According to TeamT5, “Managed detection and response (MDR) services can significantly enhance a company’s protective stance by assisting in identifying, analyzing, and responding to risks more effectively.” Furthermore, the detection accuracy rate of MDR solutions reaches 85%, significantly surpassing the 60% that is typical of conventional protective measures.
As cyber threats become increasingly sophisticated, including risks emerging from the dark web, integrating MDR into an organization’s defense strategy is not just beneficial; it is essential for maintaining resilience and compliance. The market for MDR solutions is projected to grow at a compound annual growth rate (CAGR) of 17.80% from 2026 to 2034, highlighting the escalating significance of these services within the .
Explore Core Components and Framework of MDR Services
An effective MDR service comprises several that are essential for robust :
- : This involves utilizing advanced analytics and machine learning to recognize potential dangers in real-time, allowing organizations to stay ahead of threats.
- : A systematic approach is crucial for handling and mitigating incidents. This includes predefined protocols tailored for various situations, ensuring a swift and effective response.
- : Continuous gathering and analysis of threat data is vital. This proactive measure enhances detection capabilities and informs strategic decisions.
- : 24/7 surveillance of network activity is necessary to identify anomalies and potential breaches, providing a critical layer of defense.
- : Regular updates on the organization’s safety stance and adherence to relevant regulations ensure transparency and accountability.
Understanding these components enables entities to that align with their specific protection needs and regulatory obligations.
Evaluate and Choose the Right MDR Provider
When selecting , organizations should prioritize several key criteria to ensure effective .
- Experience and Expertise: It is crucial to choose providers with a . Look for those adept at navigating , as this expertise can significantly impact compliance and security.
- Service Offerings: Ensure that the provider delivers a . This should include danger detection, , and , all of which are vital for robust cybersecurity.
- Technology Stack: Evaluate the technologies employed by the provider. They should utilize and response, including integration with existing protective infrastructures like SIEM and EDR, to enhance overall security posture.
- Customer Support: Assess the quality of assistance offered by the provider. Focus on their responsiveness and accessibility during critical incidents, as well as the availability of certified analysts for active danger response, which can be crucial in mitigating threats.
- Visibility Across Protection Domains: It is essential that the provider can offer complete . This comprehensive management of protection is vital for identifying and addressing potential vulnerabilities.
- Risk Identification Methods: Evaluate the efficiency of the vendor’s risk identification methods. Their ability to reduce alert fatigue for protection teams is important for maintaining operational effectiveness and ensuring timely responses to genuine threats.
- Client References: Request . This will help gauge the provider’s effectiveness and reliability in real-world scenarios, providing insight into their performance and client satisfaction.
By thoroughly assessing these factors, organizations can select MDR solutions that not only meet their immediate cybersecurity needs but also align with their long-term protection strategy. This approach ultimately enhances resilience against evolving cyber threats.
Integrate MDR Solutions with Existing Security Infrastructure
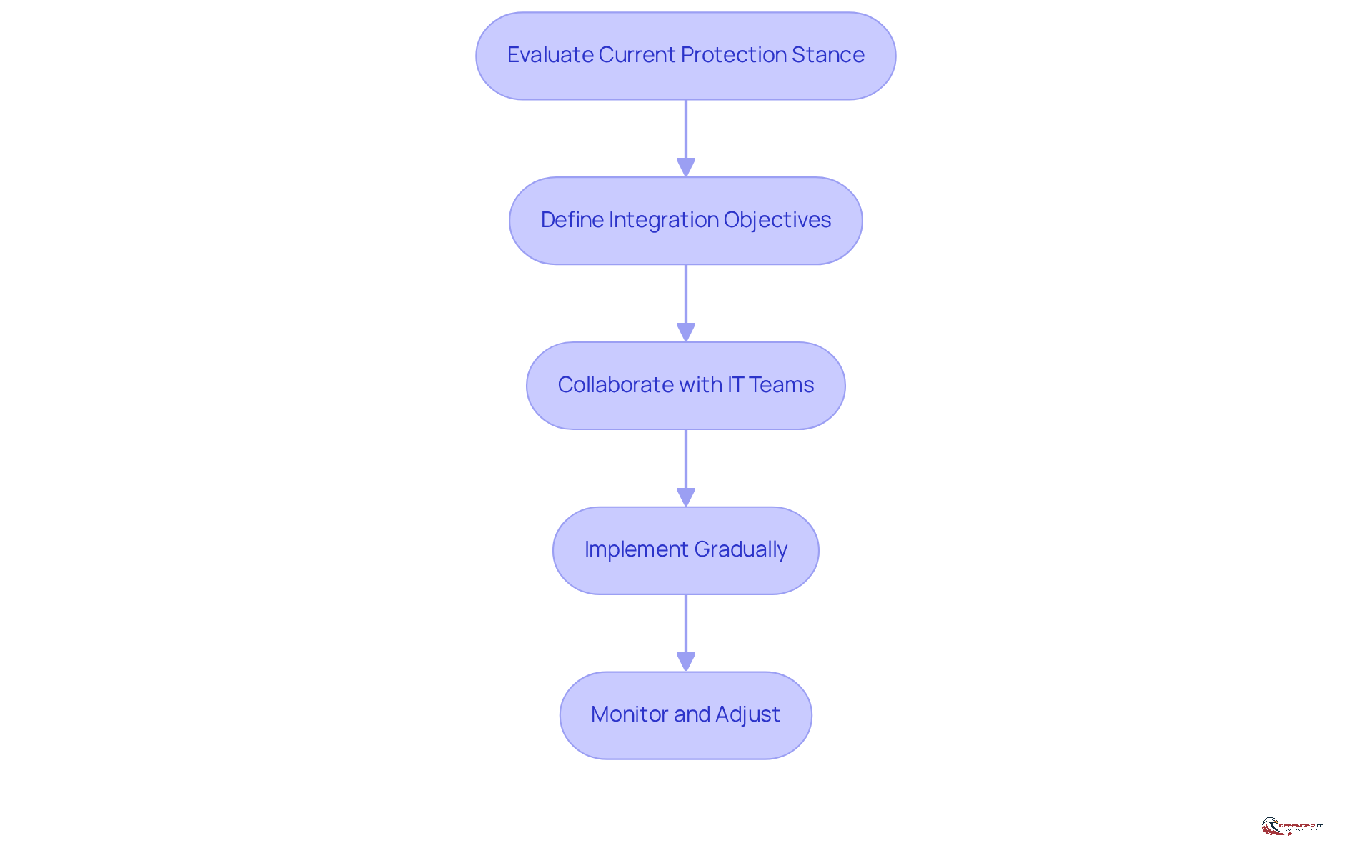
To effectively integrate Managed Detection and Response (MDR) solutions with existing security infrastructure, organizations should adhere to the following best practices:
- Evaluate Current Protection Stance: Begin with a to identify weaknesses and areas for improvement. Regular risk assessments can pinpoint potential gaps in security systems, ensuring a robust foundation for MDR integration. has been shown to decrease dwell time for undetected assaults, underscoring the importance of this initial step.
- Define Integration Objectives: Clearly articulate the goals of the integration, such as or streamlining processes. Establishing specific objectives will guide implementation and facilitate the measurement of success.
- Collaborate with IT Teams: Engage internal IT and security teams early in the process to ensure alignment and address any concerns regarding the integration. This collaboration fosters a mutual understanding of security requirements and promotes smoother implementation. Cybersecurity experts note that effective communication with MDR providers simplifies compliance reporting and enhances the overall .
- Implement Gradually: Roll out MDR solutions in phases, allowing for adjustments based on feedback and performance metrics. This incremental approach helps organizations adapt to new systems without overwhelming existing processes. Case studies indicate that organizations implementing MDR gradually experience fewer disruptions and improved integration outcomes.
- : Continuously track the performance of the integrated system and make necessary adjustments to optimize effectiveness. Regular assessments and revisions are crucial for maintaining a strong defensive stance and adapting to evolving threats. Industry insights emphasize that and ensuring compliance with regulations.
By following these steps, organizations can ensure that their existing security infrastructure is enhanced by MDR solutions while also contributing to a more resilient . Successful integration examples demonstrate that organizations can achieve measurable improvements in threat detection and incident response, ultimately reducing their overall cyber risk.
Manage and Optimize MDR Services for Long-Term Success
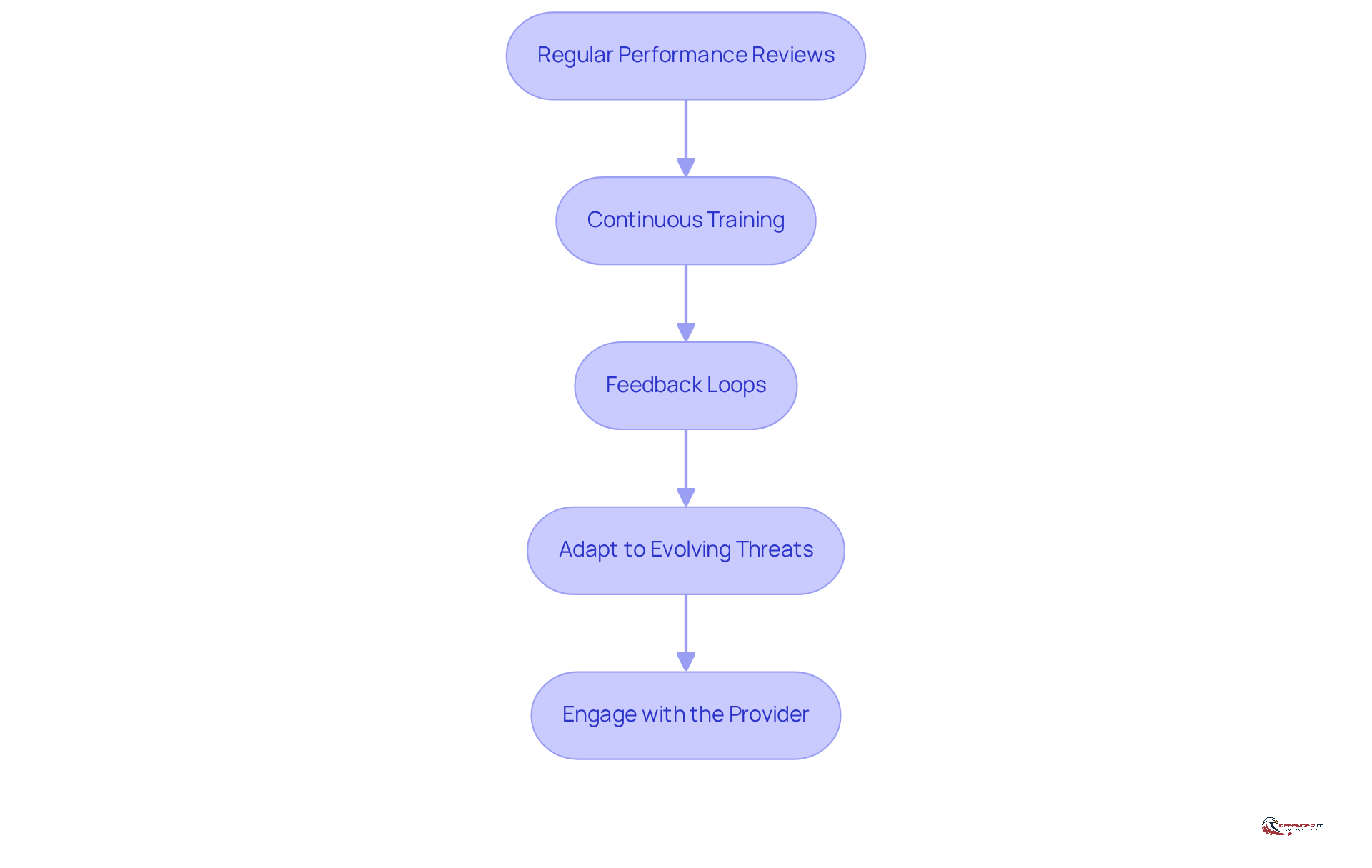
To ensure the long-term success of , organizations must implement effective management strategies:
- : Periodic assessments of MDR service effectiveness are essential. Focus on key metrics such as detection rates, response times, and overall security posture. This practice identifies strengths and weaknesses while aligning the service with organizational goals.
- : Ongoing training for internal teams is crucial to keep them informed about the latest risks and response strategies. Given the rapid evolution of the , well-informed teams are better equipped to respond effectively.
- : Establish mechanisms for gathering feedback from stakeholders, including IT staff and end-users. This collaborative approach identifies areas for improvement in MDR services and fosters a culture of continuous improvement and responsiveness to user needs.
- Adapt to Evolving Threats: Staying informed about accordingly is vital. Proactive adaptation ensures resilience against new attack vectors and upholds a strong defense posture. The managed detection and response market is projected to reach USD 11.2 billion in 2026, underscoring the urgency of these adaptations.
- Engage with the Provider: Maintaining open communication with the MDR provider is essential. Discuss performance, updates, and necessary adjustments to the service. This partnership enhances the effectiveness of MDR solutions and ensures they meet the entity’s evolving needs. As noted by the Biden-Harris Administration, the growing intricacy of cyber dangers necessitates a .
By implementing these strategies, organizations can optimize their MDR solutions, ensuring they remain effective against evolving and contribute to a stronger .
Conclusion
Effectively implementing Managed Detection and Response (MDR) solutions is essential for organizations aiming to strengthen their cybersecurity defenses. By combining advanced technology with human expertise, MDR provides a proactive approach to identifying and mitigating cyber threats in real-time. This transition from traditional security measures to a more dynamic model not only enhances an organization’s security posture but also ensures compliance with regulatory requirements, establishing it as a critical component in today’s digital landscape.
The article delineates several best practices for the successful implementation of MDR solutions. Key considerations include:
- Defining core components such as risk identification, incident response, and threat intelligence.
- Selecting the right MDR provider based on experience, service offerings, and technology stack.
- Integrating MDR with existing security infrastructure.
- Managing these services for long-term success through regular performance reviews and continuous training.
Ultimately, adopting and optimizing MDR solutions transcends being merely a strategic move; it represents a proactive measure to safeguard against the ever-evolving cyber threats. Organizations are urged to prioritize these best practices to enhance their resilience and ensure that their cybersecurity efforts are not only effective but also sustainable. By taking decisive action now, businesses can better prepare for the complexities of the digital world and protect their valuable assets from potential cyber risks.
Frequently Asked Questions
What is Managed Detection and Response (MDR)?
Managed Detection and Response (MDR) is a cybersecurity service model that combines advanced technology with human expertise to detect, respond to, and mitigate cyber risks in real-time. It offers continuous monitoring and proactive risk hunting, which helps organizations identify vulnerabilities and respond swiftly to incidents.
How does MDR differ from traditional cybersecurity measures?
MDR differs from traditional measures by providing continuous monitoring and proactive risk hunting, rather than just reactive protective measures. This allows for quicker identification of threats and vulnerabilities, enhancing the organization’s overall security posture.
Why is MDR important for businesses in regulated industries?
MDR is crucial for businesses in regulated industries because it helps ensure compliance and data protection, which are critical in these sectors. It allows organizations to maintain resilience against evolving cyber threats.
What are the benefits of adopting MDR for an organization?
By adopting MDR, organizations can enhance their security posture, reduce response times, and effectively protect their digital assets against evolving threats.
What is the detection accuracy rate of MDR solutions compared to conventional measures?
The detection accuracy rate of MDR solutions reaches 85%, which significantly surpasses the 60% accuracy typical of conventional protective measures.
What are the core components of an effective MDR service?
The core components of an effective MDR service include: – Risk Identification: Utilizing advanced analytics and machine learning to recognize potential dangers in real-time. – Incident Response: A systematic approach for handling and mitigating incidents with predefined protocols. – Threat Intelligence: Continuous gathering and analysis of threat data to enhance detection capabilities. – Security Monitoring: 24/7 surveillance of network activity to identify anomalies and potential breaches. – Reporting and Compliance: Regular updates on safety stance and adherence to regulations.
What is the projected growth rate of the MDR market?
The market for MDR solutions is projected to grow at a compound annual growth rate (CAGR) of 17.80% from 2026 to 2034, indicating the increasing significance of these services in the cybersecurity landscape.