Introduction
The cybersecurity landscape is becoming increasingly complex, with organizations confronting a multitude of evolving threats daily. Engaging with managed security service providers (MSSPs) offers a strategic opportunity for businesses to enhance their defenses against these challenges. However, selecting and collaborating with the right MSSP can be a daunting task.
What criteria should organizations prioritize to ensure they choose a partner capable of effectively safeguarding their assets? This article explores essential best practices for engaging MSSPs, providing organizations with the insights necessary to navigate this critical partnership successfully.
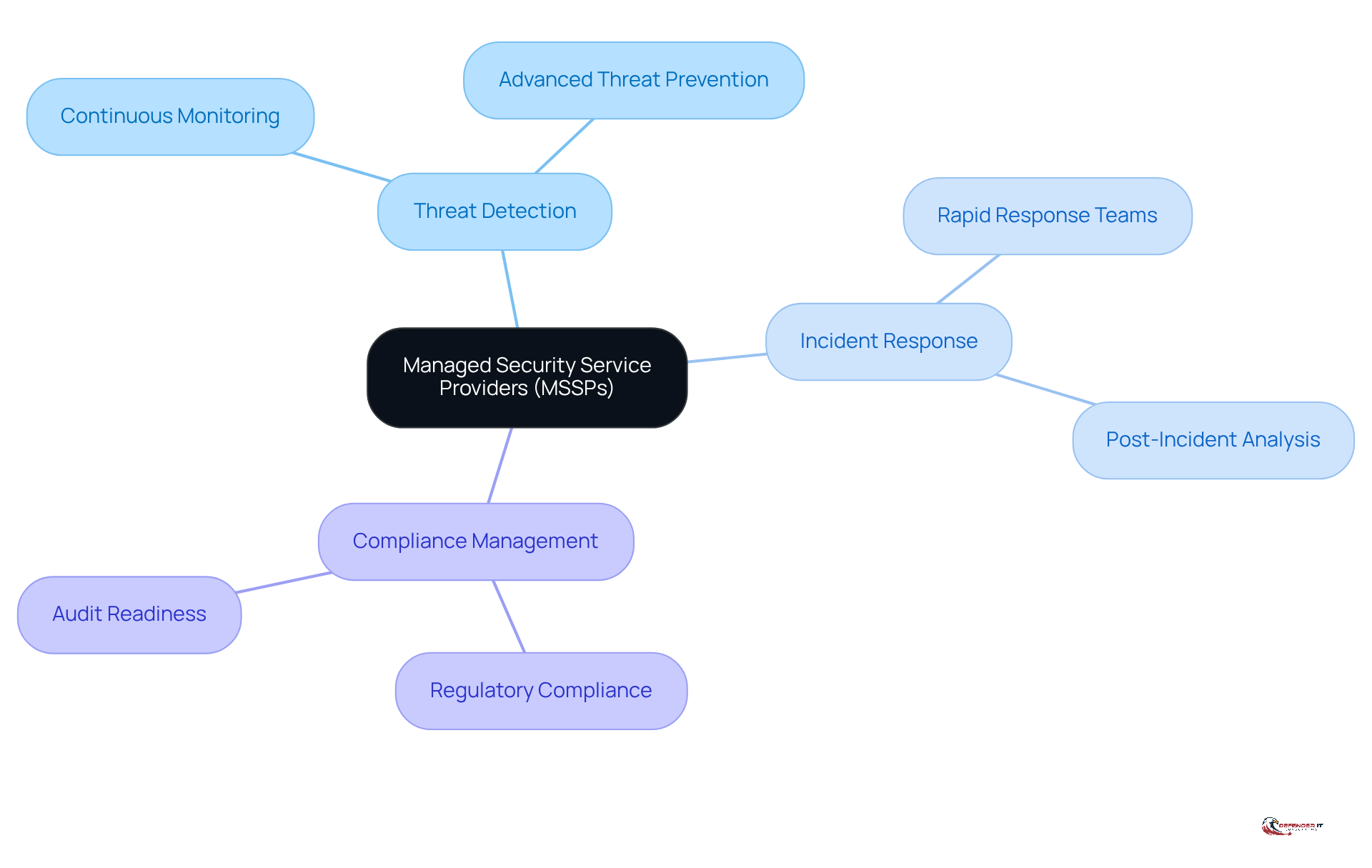
Define Managed Security Service Providers (MSSPs)
(MSSPs) are specialized third-party entities that provide outsourced and devices. They provide a range of services, including:
These services are tailored to meet the specific needs of organizations across various sectors.
(MSSPs) focus exclusively on cybersecurity, unlike traditional IT service providers. They leverage advanced technologies and expertise to protect enterprises from the ever-evolving landscape of . This distinction is crucial, as organizations increasingly face sophisticated attacks that require .
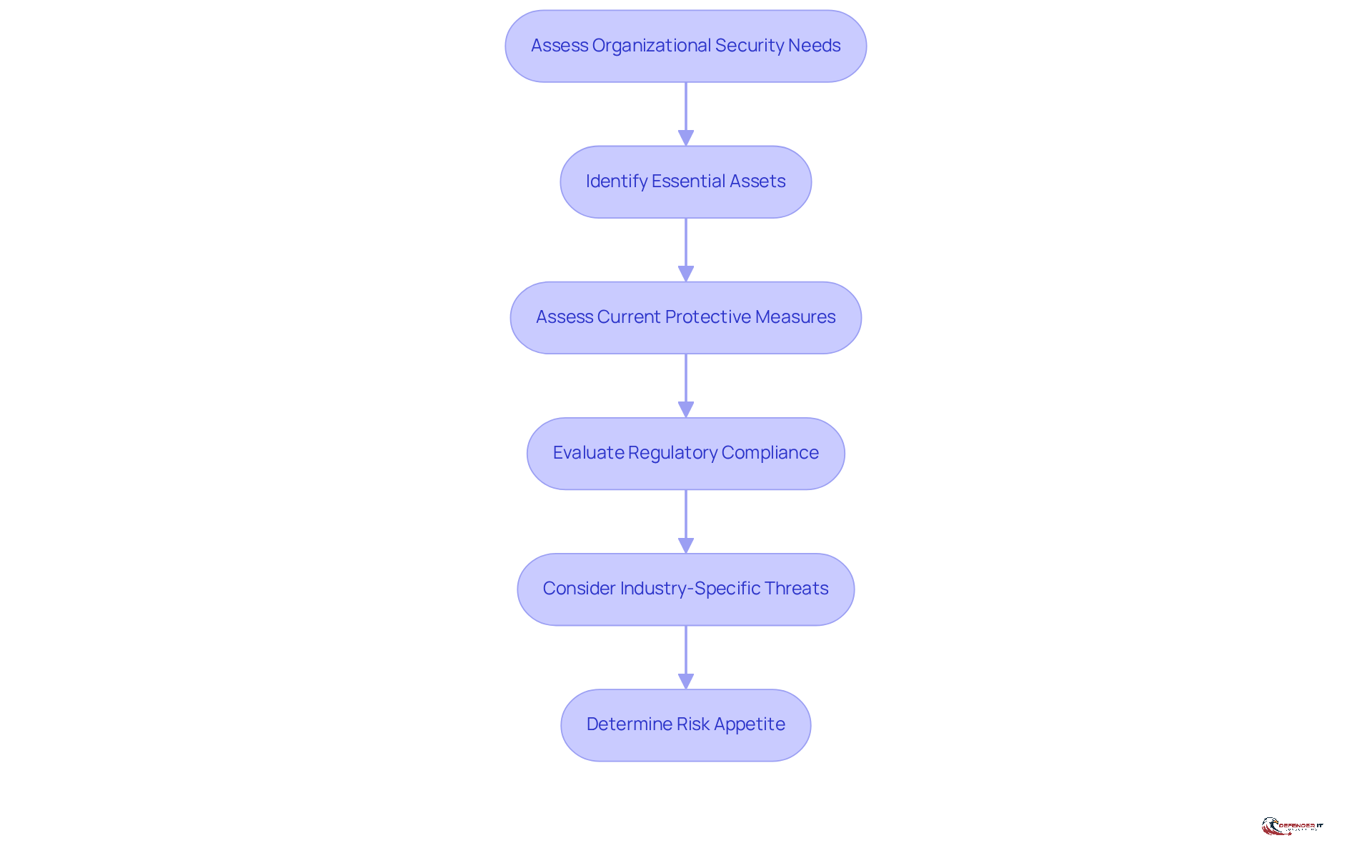
Assess Organizational Security Needs
To effectively engage with , entities must first conduct a comprehensive evaluation of their protection requirements. This evaluation begins with identifying essential assets and assessing current protective measures to uncover . Key considerations include , industry-specific threats, and the overall risk appetite of the entity.
In 2026, the significance of is paramount, as they highlight common weaknesses that could be exploited, such as unpatched software and inadequate access controls. For example, the , coupled with a concerning 27-day ‘patching gap’ between exploit and patch. Utilizing and tools, such as , provides critical insights into the entity’s protective stance, facilitating informed decision-making.
This foundational understanding is essential for selecting that are capable of addressing identified gaps and enhancing the entity’s . Furthermore, entities that have conducted thorough often find themselves better equipped to choose managed security service providers that align with their specific security needs, ultimately leading to . As AI tools advance in 2026, they will possess the capability to detect threats in real-time and predict vulnerabilities, underscoring the increasing importance of these assessments.
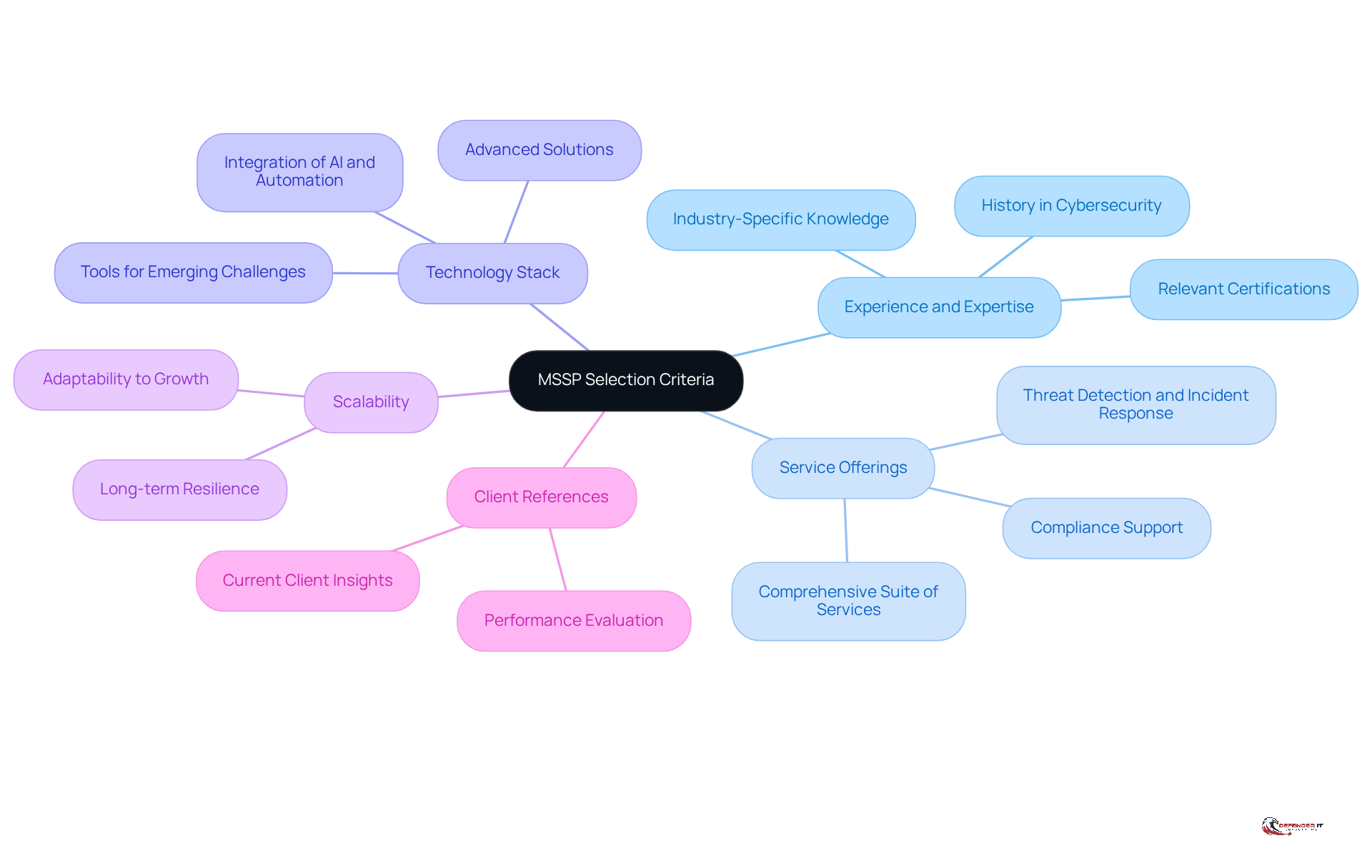
Evaluate MSSP Selection Criteria
When selecting , organizations must prioritize several critical criteria to ensure a successful partnership.
- Experience and Expertise: It is essential to review the MSSP’s history in the , particularly within industries similar to your own. Relevant certifications and partnerships can highlight their specialized knowledge. Given the rapidly evolving cybersecurity landscape, the expertise of significantly impacts their effectiveness in addressing current challenges.
- Service Offerings: Confirm that the MSSP provides a , including , , and . As organizations face increasing regulatory scrutiny, partnering with a provider that understands compliance requirements is crucial.
- Technology Stack: Assess the technologies and tools employed by the MSSP. They should utilize . The integration of AI and automation in their processes can enhance risk detection and response times, which is vital in today’s fast-paced cyber environment.
- Scalability: Consider whether the MSSP can adapt its services to accommodate your organization’s growth and evolving security needs. A provider that can scale effectively will help ensure long-term resilience against cyber threats.
- : Request references from current clients to . Insights from existing clients can offer valuable perspectives on the MSSP’s commitment to enhancing their security posture.
By thoroughly evaluating these criteria, organizations can select that are not only well-equipped to bolster their cybersecurity defenses but also aligned with their specific operational requirements.
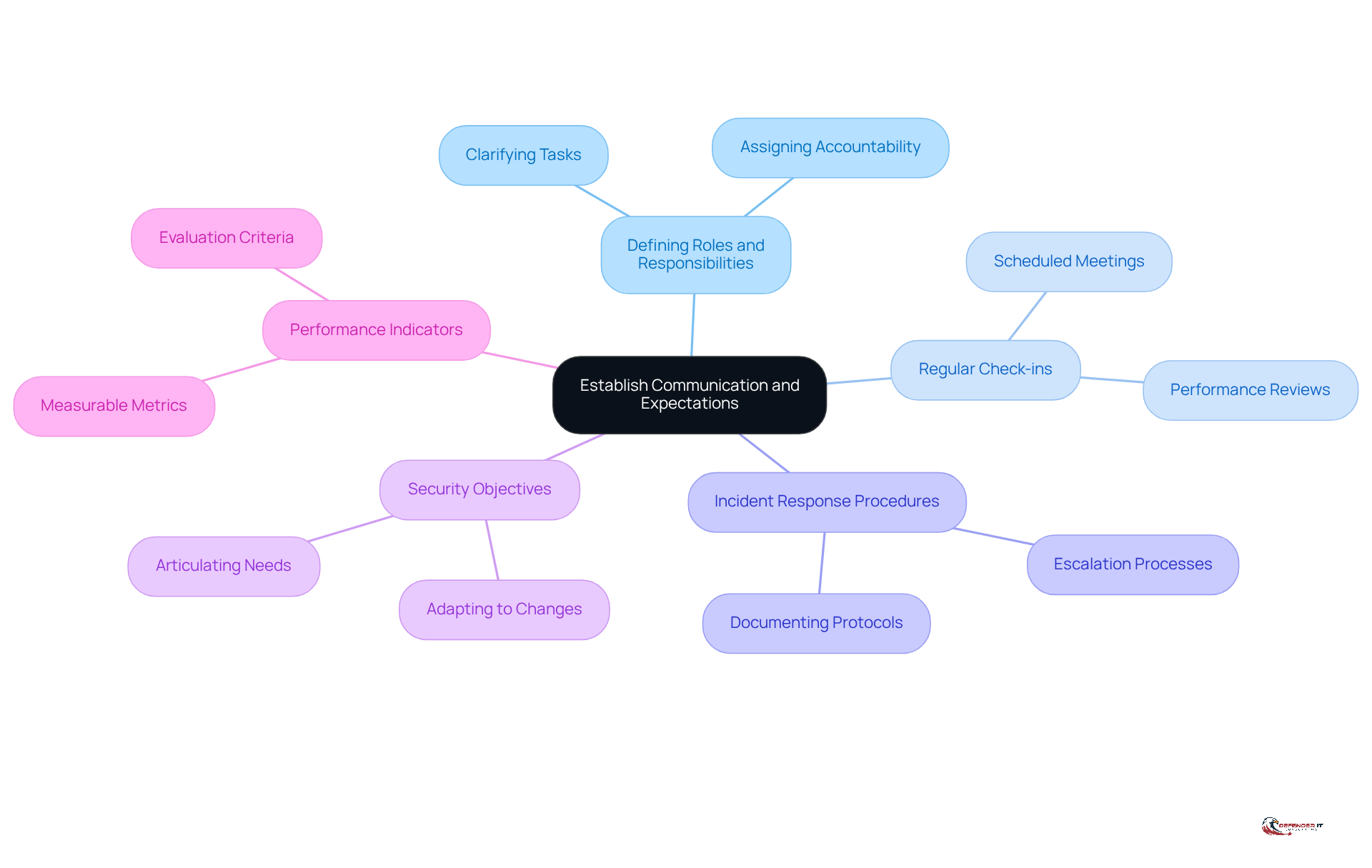
Establish Communication and Expectations
To enhance the effectiveness of partnerships with , organizations must establish and set mutual expectations from the outset. This foundational step includes:
- Defining
- Establishing
- Agreeing on
Furthermore, organizations should articulate their and communicate any changes in their operational environment that may impact security needs.
Additionally, establishing is crucial. These indicators will assist both parties in evaluating the effectiveness of ‘ offerings over time. Regular communication fosters transparency and trust, enabling a to managing .
Monitor and Assess MSSP Performance
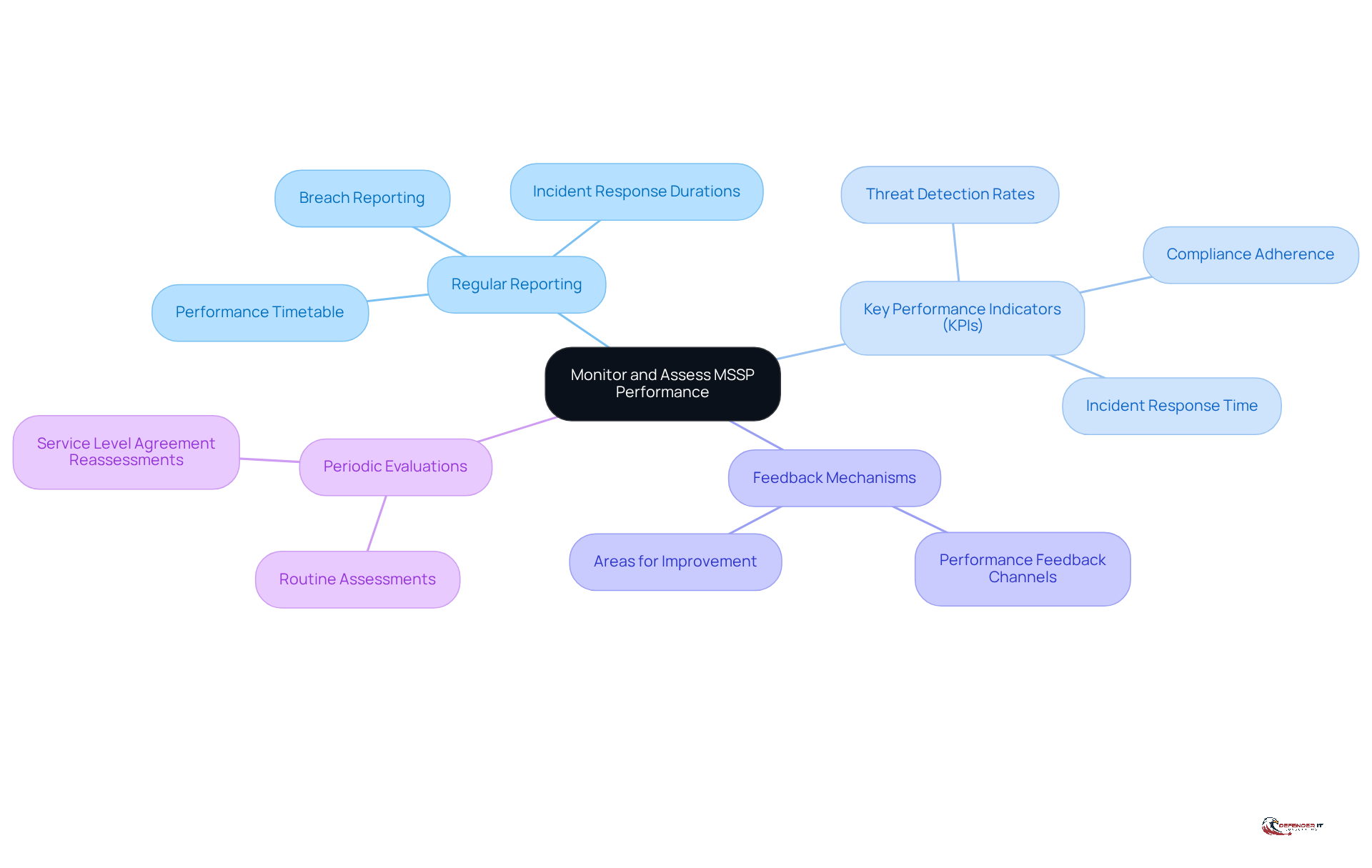
Organizations must adopt a structured approach to monitor and evaluate the performance of their . This is essential for ensuring optimal service delivery and robust . The following components are critical:
- Regular Reporting: Establish a timetable for that detail the service provider’s activities, , and any breaches that occurred.
- : Define KPIs that align with your security objectives, such as incident response time, threat detection rates, and compliance adherence.
- : Create channels for providing feedback to the MSSP regarding their performance and responsiveness. This can help pinpoint areas for improvement.
- : Conduct routine assessments of the service provider’s offerings to ensure they continue to meet your organization’s evolving security needs. This may involve reassessing service level agreements and making necessary adjustments.
By actively monitoring and evaluating the performance of , organizations can ensure they receive the highest level of service and protection against .
Conclusion
Engaging effectively with managed security service providers (MSSPs) is crucial for organizations aiming to strengthen their cybersecurity defenses. By comprehensively understanding the unique capabilities of MSSPs and implementing best practices in collaboration, businesses can significantly enhance their protection against the constantly evolving landscape of cyber threats.
This article outlines several key strategies for successful engagement with MSSPs:
- Conducting a thorough assessment of organizational security needs establishes a solid foundation for selecting the appropriate provider.
- Evaluating MSSP selection criteria – such as experience, service offerings, and technology stack – ensures alignment with specific security requirements.
- Establishing clear communication and expectations fosters a productive partnership.
- Ongoing monitoring and assessment of MSSP performance are essential for maintaining effective security measures.
Ultimately, collaboration with MSSPs should be viewed not merely as an outsourcing decision but as a strategic partnership that can lead to improved resilience against cyber risks. Organizations are encouraged to proactively assess their security needs, engage with qualified MSSPs, and continuously evaluate the effectiveness of these partnerships. By doing so, they can safeguard their assets and adapt to the dynamic challenges posed by the cybersecurity landscape, ensuring a robust defense against potential threats.
Frequently Asked Questions
What are Managed Security Service Providers (MSSPs)?
Managed Security Service Providers (MSSPs) are specialized third-party entities that offer outsourced monitoring and management of security systems and devices. They provide services such as threat detection, incident response, and compliance management, tailored to meet the specific needs of various organizations.
How do MSSPs differ from traditional IT service providers?
MSSPs focus exclusively on cybersecurity, utilizing advanced technologies and expertise to protect enterprises from cyber threats, whereas traditional IT service providers may cover a broader range of IT services without the specialized focus on security.
Why is it important for organizations to assess their security needs before engaging with MSSPs?
Conducting a comprehensive evaluation of security needs helps organizations identify essential assets, assess current protective measures, and uncover potential vulnerabilities. This understanding is crucial for selecting MSSPs that can effectively address identified gaps and enhance the organization’s protection framework.
What factors should organizations consider during their security needs assessment?
Organizations should consider regulatory compliance requirements, industry-specific threats, and their overall risk appetite when assessing their security needs.
What is the significance of vulnerability assessments in 2026?
Vulnerability assessments are vital as they highlight common weaknesses that could be exploited, such as unpatched software and inadequate access controls. They provide critical insights into an organization’s protective stance, facilitating informed decision-making.
What are the potential consequences of not addressing vulnerabilities?
The average cost of a data breach is $4.88 million, and organizations often experience a 27-day ‘patching gap’ between exploit and patch, emphasizing the importance of addressing vulnerabilities promptly.
How will advancements in AI tools impact threat detection and vulnerability assessments in 2026?
Advancements in AI tools will enable real-time threat detection and the ability to predict vulnerabilities, highlighting the increasing importance of conducting thorough vulnerability evaluations for improved resilience against cyber risks.