Introduction
Healthcare organizations face increasing challenges in safeguarding sensitive patient data from cybercriminals, making robust cybersecurity solutions essential. The necessity for compliance leaders to navigate a landscape fraught with unique threats, such as ransomware and insider risks, has never been more evident.
How can these entities not only protect their data but also meet stringent regulatory standards while fostering a culture of security awareness among their staff? This article delves into essential strategies that healthcare compliance leaders can implement to fortify their defenses.
Without effective strategies, healthcare organizations risk severe regulatory penalties and a loss of patient trust in their ability to protect sensitive information.
Identify Unique Cyber Threats in Healthcare
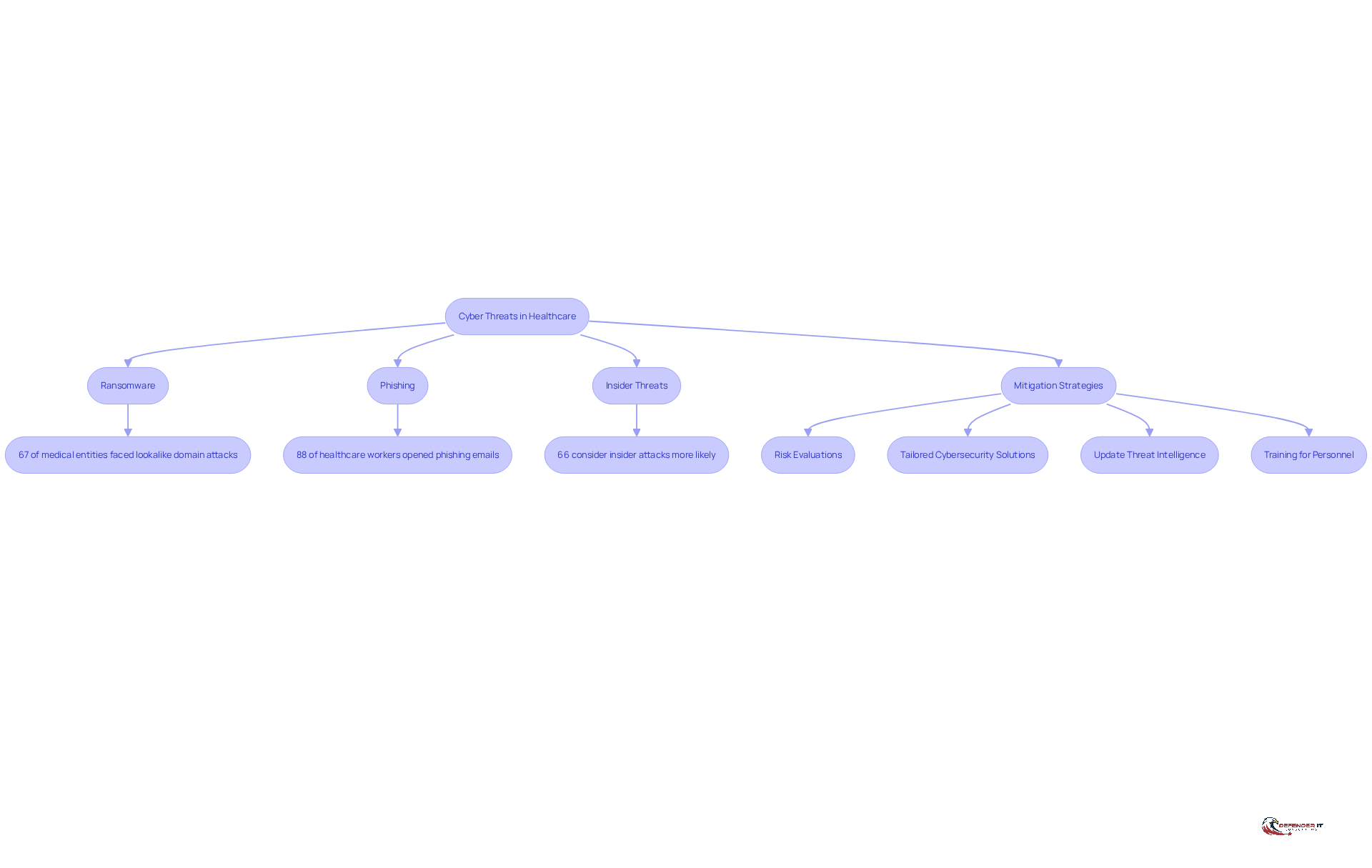
Healthcare entities face escalating cyber threats, highlighting the need for robust healthcare cybersecurity solutions to combat significant risks from ransomware and phishing attacks on patient data security. Ransomware has become a major concern. Attackers often target Electronic Health Records (EHRs) to hold sensitive patient data hostage. In 2026, it was reported that 67% of medical entities encountered attacks utilizing lookalike domains, a strategy frequently used in phishing schemes to trick employees into disclosing credentials or downloading malware.
Furthermore, insider threats – whether malicious or accidental – pose significant risks, as employees may inadvertently compromise security protocols. For instance, 88% of medical professionals have opened phishing emails, highlighting the critical need for enhanced cybersecurity awareness.
To tackle these risks effectively, healthcare organizations need to:
- Conduct thorough risk evaluations.
- Implement healthcare cybersecurity solutions tailored to their specific operations and data management practices.
- Regularly update threat intelligence.
- Provide comprehensive training for personnel on identifying potential threats.
These measures can significantly enhance a company’s security posture. Many healthcare entities struggle to detect breaches in a timely manner, leading to prolonged vulnerabilities. This delay in detection can result in severe repercussions for patient safety and organizational integrity.
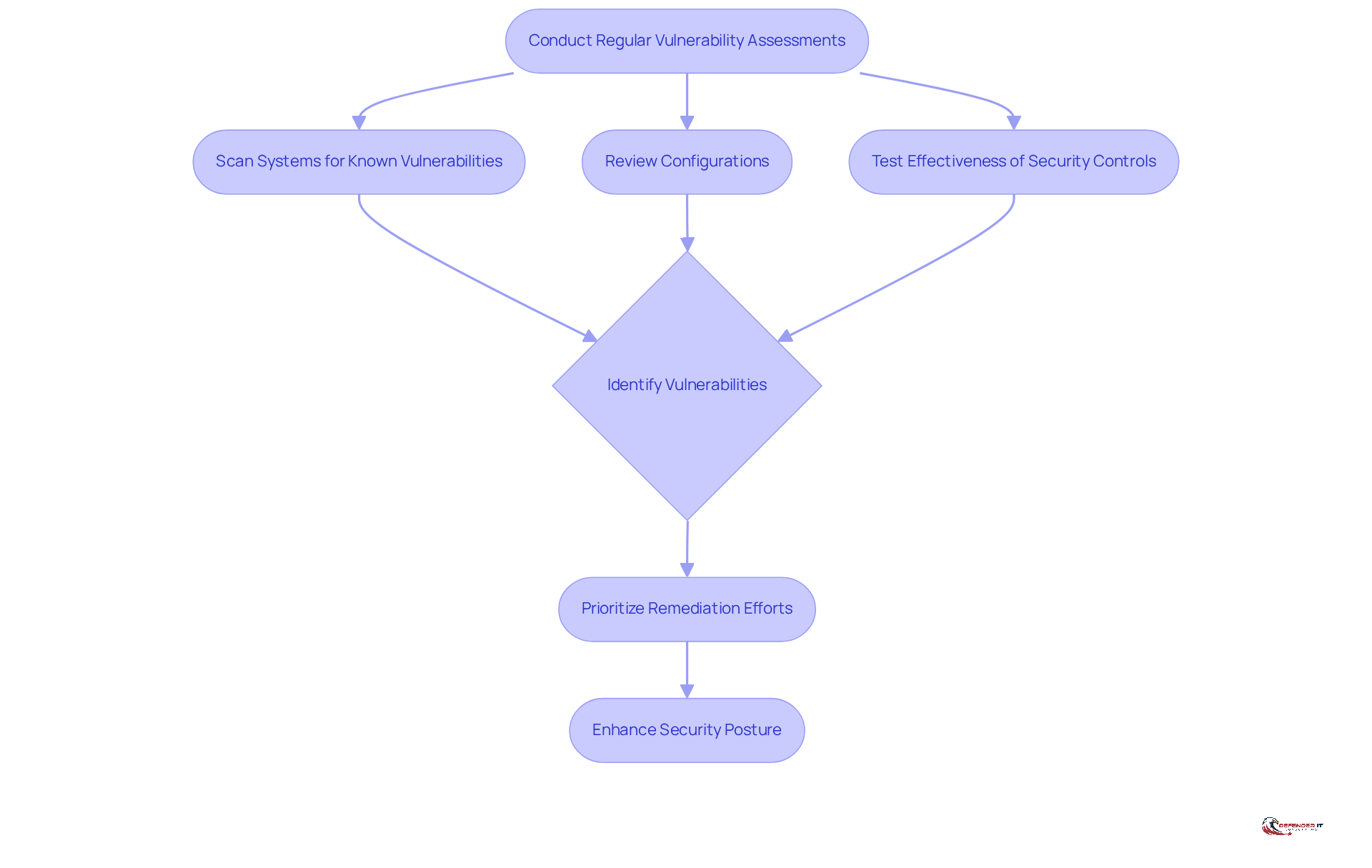
Conduct Regular Vulnerability Assessments
Regular vulnerability evaluations are essential for medical facilities to safeguard patient information and ensure compliance with industry regulations by utilizing healthcare cybersecurity solutions. These assessments should be performed at least once a year or more frequently when notable changes occur, such as new technology implementations or staff alterations. They involve:
- Scanning systems for known vulnerabilities
- Reviewing configurations
- Testing the effectiveness of existing security controls
While automated tools can streamline this process, manual reviews remain critical for identifying complex vulnerabilities that automated systems may overlook.
After conducting the assessment, prioritizing remediation efforts based on the severity of identified vulnerabilities is crucial, as this directly impacts patient safety and data integrity. For instance, if a medical facility discovers outdated software vulnerable to ransomware attacks, addressing this weakness promptly can avert an expensive breach. Regular evaluations not only improve adherence to regulations such as HIPAA, which mandates a comprehensive evaluation of risks and vulnerabilities to electronic protected health information (ePHI), but also reinforce the overall security stance of medical providers, ensuring the effectiveness of healthcare cybersecurity solutions in safeguarding sensitive patient information.
Furthermore, it is crucial to remove unneeded software on devices, as this can increase potential vulnerabilities. Statistics indicate that around 60% of breaches involved exploiting known vulnerabilities for which patches were already available. This statistic underscores the urgency of timely remediation efforts, as addressing vulnerabilities promptly can significantly mitigate risks and enhance the overall security posture of medical providers.
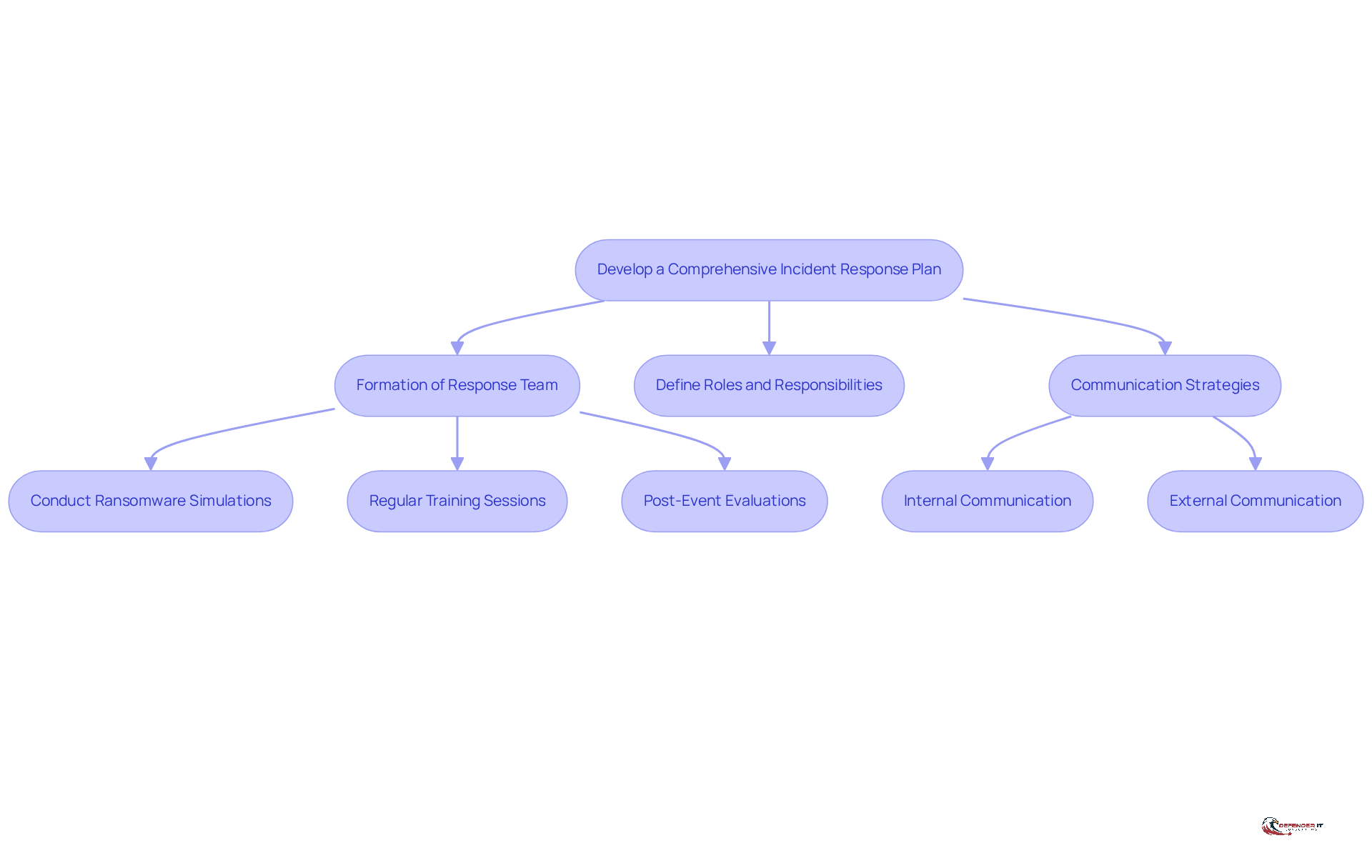
Develop a Comprehensive Incident Response Plan
A robust response strategy is essential for medical institutions to effectively navigate the complexities of healthcare cybersecurity solutions and threats. Key elements include:
- The formation of a response team
- Clearly defined roles and responsibilities
- Thorough communication strategies for both internal and external stakeholders
Consistent training and simulations are vital; for instance, medical institutions frequently conduct ransomware attack simulations to assess their response capabilities. These exercises reveal weaknesses in the plan, allowing for targeted improvements. Additionally, post-event evaluations are crucial for learning from incidents. They enable entities to refine their response strategies and bolster resilience against future threats.
In 2026, entities with clearly outlined response strategies are considerably better equipped to reduce risks, as evidenced by data indicating that healthcare entities are reporting notifiable breaches 26.4% more often. This underscores the importance of continuous training and readiness, particularly since organizations employing automated risk evaluation tools are twice as likely to report occurrences on time or ahead of schedule. Furthermore, teams that monitor and respond to data achieve a 50% quicker time-to-breach decision, emphasizing the advantages of organized response plans in the face of evolving cyber threats.
Addressing the challenges posed by human error, which was the leading cause of privacy incidents in 2025, further highlights the necessity of comprehensive training and preparedness. As the landscape of cyber threats evolves, the ability to adapt and respond swiftly through effective healthcare cybersecurity solutions will define the resilience of healthcare organizations in the future.
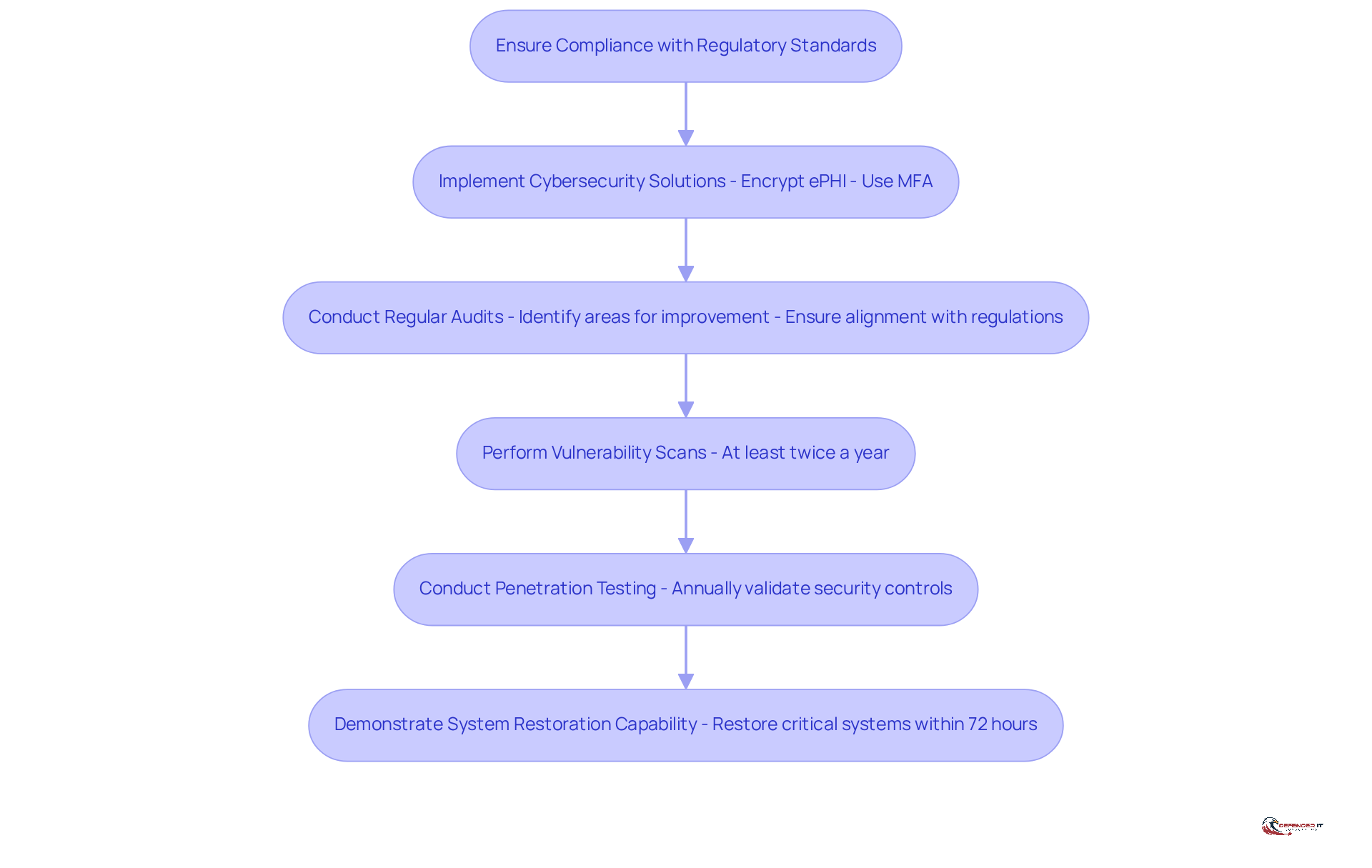
Ensure Compliance with Regulatory Standards
Healthcare entities face significant challenges in meeting various regulatory standards, including HIPAA, HITECH, and state-specific regulations. To ensure compliance, organizations must implement robust healthcare cybersecurity solutions that safeguard patient data, conduct regular audits, and maintain thorough documentation to demonstrate adherence to these standards.
For instance, to comply with HIPAA’s security rule, a healthcare provider may implement encryption for all electronic protected health information (ePHI), especially since encryption at rest will be mandatory under the 2026 HIPAA changes. Conducting regular compliance audits is essential, as they help identify areas for improvement and ensure that the entity remains aligned with evolving regulations.
Moreover, entities are required to conduct vulnerability scans at least twice a year and perform full penetration testing annually as part of their healthcare cybersecurity solutions to bolster their security posture. By 2026, it is anticipated that approximately 70% of healthcare entities will have achieved HITECH compliance, reflecting a growing commitment to safeguarding patient data and enhancing overall security measures.
Additionally, entities must demonstrate their capability to restore critical systems within 72 hours following an incident, a significant compliance expectation under the updated HIPAA regulations. Finally, a compliance grace period of 180 days has been established for the 2026 HIPAA changes, providing organizations with the necessary time to align with the new requirements.
Conclusion
Healthcare organizations face significant challenges in safeguarding sensitive patient data against rising cyber threats. Without effective strategies, these organizations risk severe penalties and the loss of patient trust in their ability to protect vital information.
Throughout this article, key strategies have been outlined, including:
- The identification of unique cyber threats
- Conducting regular vulnerability assessments
- Developing a comprehensive incident response plan
- Ensuring compliance with regulatory standards
Each of these practices plays a crucial role in fortifying the defenses of healthcare organizations against the persistent and evolving landscape of cyber risks, such as ransomware and insider threats.
The proactive implementation of these cybersecurity measures is essential for maintaining patient trust and ensuring compliance in a rapidly evolving digital landscape. As healthcare compliance leaders navigate the complexities of protecting patient data, fostering a culture of security awareness among staff is equally essential. By taking proactive steps to enhance cybersecurity practices, healthcare organizations can not only mitigate risks but also build a resilient framework that upholds patient trust and ensures compliance with ever-evolving regulations. Embracing these strategies is vital for safeguarding the future of healthcare in an increasingly digital world.
Frequently Asked Questions
What are the main cyber threats faced by healthcare entities?
Healthcare entities face escalating cyber threats, primarily from ransomware and phishing attacks that target patient data security.
How does ransomware affect healthcare organizations?
Ransomware attacks often target Electronic Health Records (EHRs) to hold sensitive patient data hostage, posing significant risks to healthcare organizations.
What is the prevalence of phishing attacks in the healthcare sector?
In 2026, it was reported that 67% of medical entities encountered attacks utilizing lookalike domains, a common tactic in phishing schemes to deceive employees into disclosing credentials or downloading malware.
What role do insider threats play in healthcare cybersecurity?
Insider threats, whether malicious or accidental, pose significant risks as employees may inadvertently compromise security protocols. For instance, 88% of medical professionals have opened phishing emails, highlighting the need for improved cybersecurity awareness.
What measures should healthcare organizations take to enhance cybersecurity?
Healthcare organizations should conduct thorough risk evaluations, implement tailored cybersecurity solutions, regularly update threat intelligence, and provide comprehensive training for personnel on identifying potential threats.
Why is timely breach detection important in healthcare?
Many healthcare entities struggle to detect breaches quickly, leading to prolonged vulnerabilities that can severely impact patient safety and organizational integrity.
List of Sources
- Identify Unique Cyber Threats in Healthcare
- Health care is not ready for the new era of AI-enabled cyberattacks (https://statnews.com/2026/04/17/health-care-cybersecurity-ransomware-project-glasswing)
- The State Of Ransomware 2026 | BlackFog (https://blackfog.com/the-state-of-ransomware-2026)
- 80+ Healthcare Data Breach Statistics 2026 (https://getastra.com/blog/security-audit/healthcare-data-breach-statistics)
- 7 Cybersecurity Threats Every Healthcare Provider Must Know in 2026 (And How to Stop Them) – Alis Technology (https://alistechnology.com/7-cybersecurity-threats-every-healthcare-provider-must-know-in-2026-and-how-to-stop-them)
- Conduct Regular Vulnerability Assessments
- Healthcare Data Security in 2026: Protecting Sensitive Medical Information (https://eccu.edu/blog/healthcare-data-security-in-2026)
- January 2026 OCR Cybersecurity Newsletter (https://hhs.gov/hipaa/for-professionals/security/guidance/cybersecurity-newsletter-january-2026)
- Ultimate Guide to Vulnerability Assessment: What, Why & How (2026 Edition) (https://acronis.com/en/blog/posts/ultimate-guide-to-vulnerability-assessment-2026)
- Vulnerability Statistics 2026: Key Trends & Data | Indusface (https://indusface.com/blog/key-vulnerability-statistics)
- Develop a Comprehensive Incident Response Plan
- 10 Privacy Incident Metrics Health Systems Must Track in 2026 (https://radarfirst.com/blog/top-10-privacy-incident-metrics-every-healthcare-provider-should-track-in-2026)
- Here’s how Congress plans to fight new cyberattacks (https://axios.com/2026/03/09/congress-health-cyberattacks-cyber-security)
- Ensure Compliance with Regulatory Standards
- 2026 HIPAA Changes: New Security Rule Requirements (https://hipaavault.com/resources/2026-hipaa-changes)
- Healthcare Data Breach Statistics (https://hipaajournal.com/healthcare-data-breach-statistics)
- Healthcare Security Predictions 2026: Top Threats, AI-Driven Defenses, and Compliance Trends (https://accountablehq.com/post/healthcare-security-predictions-2026-top-threats-ai-driven-defenses-and-compliance-trends)
- 51 HIPAA Statistics Every Healthcare Entity Needs to Know in 2026 | UpGuard (https://upguard.com/blog/hipaa-statistics)
- Why Some Hospitals Won’t Be Able to Comply With Upcoming HIPAA Updates – MedCity News (https://medcitynews.com/2026/04/hipaa-hhs-healthcare-cybersecurity-security)