Introduction
In an era where cyber threats are increasingly prevalent, organizations must prioritize their incident response strategies to protect their operations. The National Institute of Standards and Technology (NIST) offers a comprehensive framework that delineates best practices for effectively managing security incidents. By implementing these practices, organizations can bolster their preparedness, enhance detection capabilities, and ensure a swift recovery from incidents.
However, a significant challenge persists: how can organizations not only respond to incidents effectively but also learn from them to avert future occurrences?
Establish Preparation Strategies for Incident Response
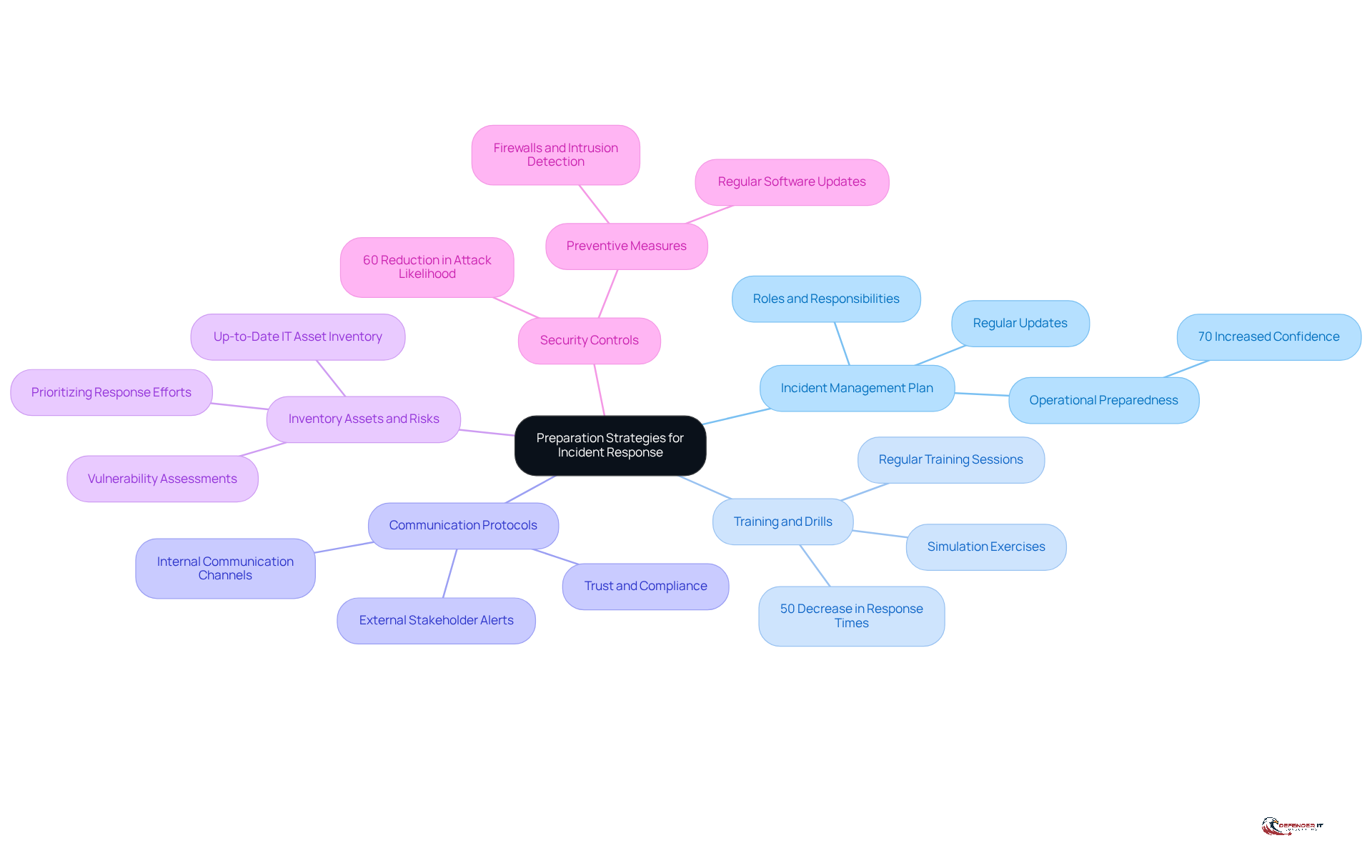
To establish effective preparation strategies for , organizations should focus on several key areas:
- Develop an : A thorough IMP should outline roles, responsibilities, and procedures for addressing incidents. This plan must be tailored to the organization’s specific needs and regularly updated to reflect evolving threats and compliance requirements. In 2026, organizations with documented emergency management strategies reported a and expand operations, with approximately 70% indicating that having a formal plan enhanced their operational preparedness.
- Conduct Training and Drills: Regular training sessions and simulation exercises are crucial for ensuring that all team members understand their roles during an emergency. These practices not only improve preparedness but also help in the action plan. For instance, organizations that participated in the reported a 50% decrease in response times during events, demonstrating the effectiveness of such training.
- : Clear communication channels for both internal and external stakeholders must be defined. This includes prompt alerts to relevant parties during an event and ensuring efficient information exchange, which is essential for maintaining trust and compliance. can significantly mitigate the impact of incidents on organizational reputation.
- : Organizations should maintain an up-to-date inventory of all IT assets and assess their vulnerabilities. Understanding what needs protection is critical for prioritizing response efforts and ensuring effective resource allocation. Frequent evaluations can help organizations stay ahead of potential risks.
- : Preventive measures such as firewalls, intrusion detection systems, and regular software updates should be deployed to mitigate risks before incidents occur. Organizations that invest in these controls are better equipped to handle risks and recover with minimal disruption. According to CISA, proactive security measures can reduce the likelihood of successful attacks by up to 60%.
By concentrating on these preparation strategies, organizations can significantly enhance their capabilities in line with , ensuring they are well-equipped to manage potential threats and maintain compliance with regulatory obligations.
Enhance Detection and Analysis Capabilities
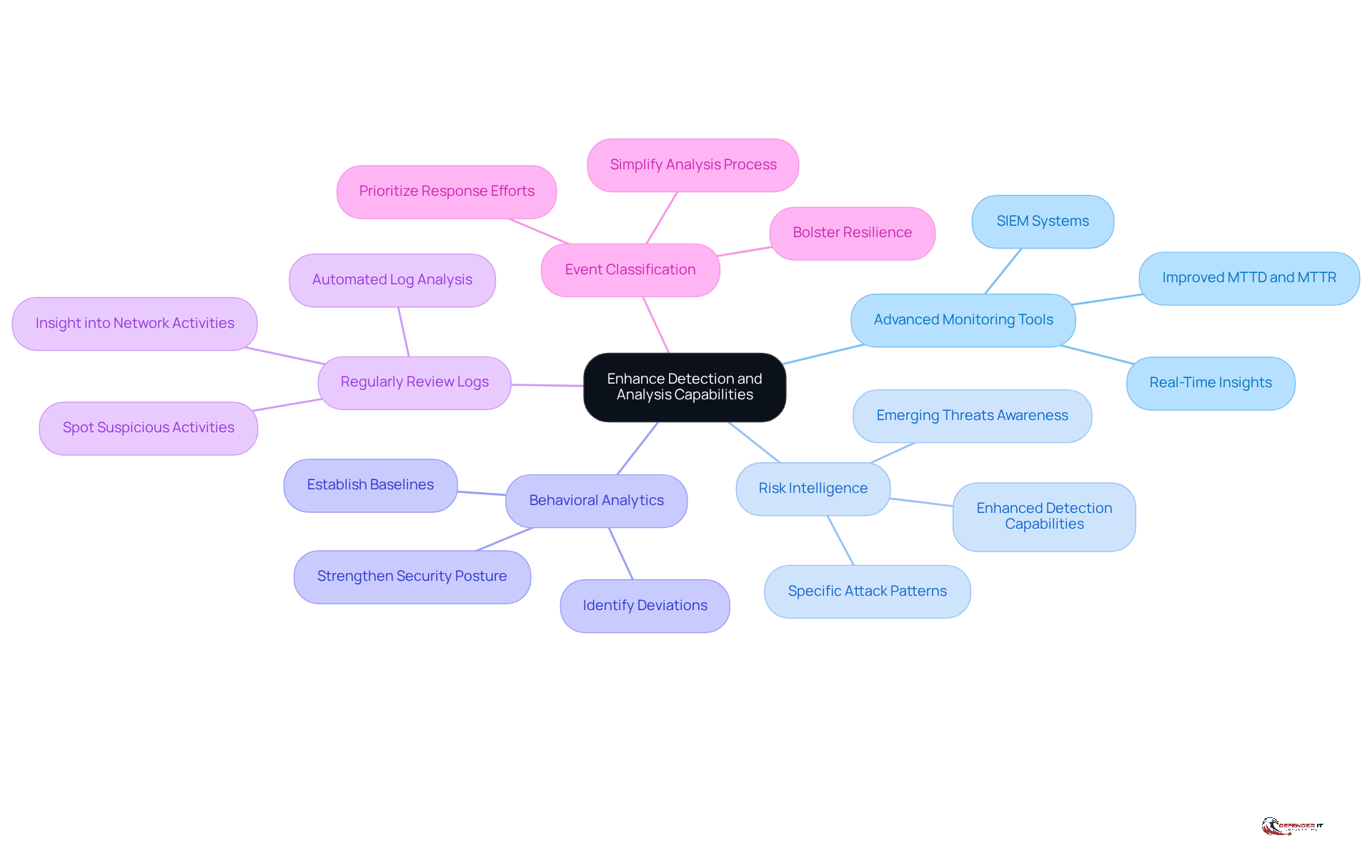
To enhance detection and analysis capabilities, organizations should implement the following practices:
- Utilize : Investing in is essential for aggregating and analyzing security data across the organization. These tools provide real-time insights, enabling the detection of anomalies and potential risks as they arise. SIEM solutions have been shown to improve Mean Time to Detect (MTTD) and Mean Time to Respond (MTTR), significantly enhancing overall . As Andrew Douthwaite, CTO at VirtualArmour, states, “SIEM benefits your security stack by delivering on a number of fronts.”
- Employ Risk Intelligence: Utilizing risk intelligence feeds is crucial for staying informed about emerging threats and vulnerabilities. This proactive approach allows companies to identify specific attack patterns relevant to their operations. Studies indicate that entities leveraging can enhance their detection capabilities, leading to quicker responses and reduced risk exposure.
- Implement : Employing helps establish baselines for normal user behavior, facilitating the identification of deviations that may signal a security issue. This method not only aids in early detection but also strengthens the overall security posture by enabling organizations to respond swiftly to unusual activities.
- : Conducting routine log reviews is vital for spotting suspicious activities. Automated log analysis tools can streamline this process, allowing security teams to identify potential issues more efficiently. Effective log management enhances insight into network activities, which is essential for prompt issue resolution.
- : Creating a classification system for events enables organizations to prioritize response efforts based on severity and potential impact. This systematic approach simplifies the analysis process and ensures that critical events are addressed promptly, ultimately bolstering the organization’s resilience against .
By enhancing detection and analysis capabilities through these practices, organizations can significantly improve their ability to implement NIST security incident response and effectively identify and respond to . Furthermore, those considering SIEM solutions can explore demos and free trials to assess their suitability for specific needs.
Implement Containment and Recovery Procedures
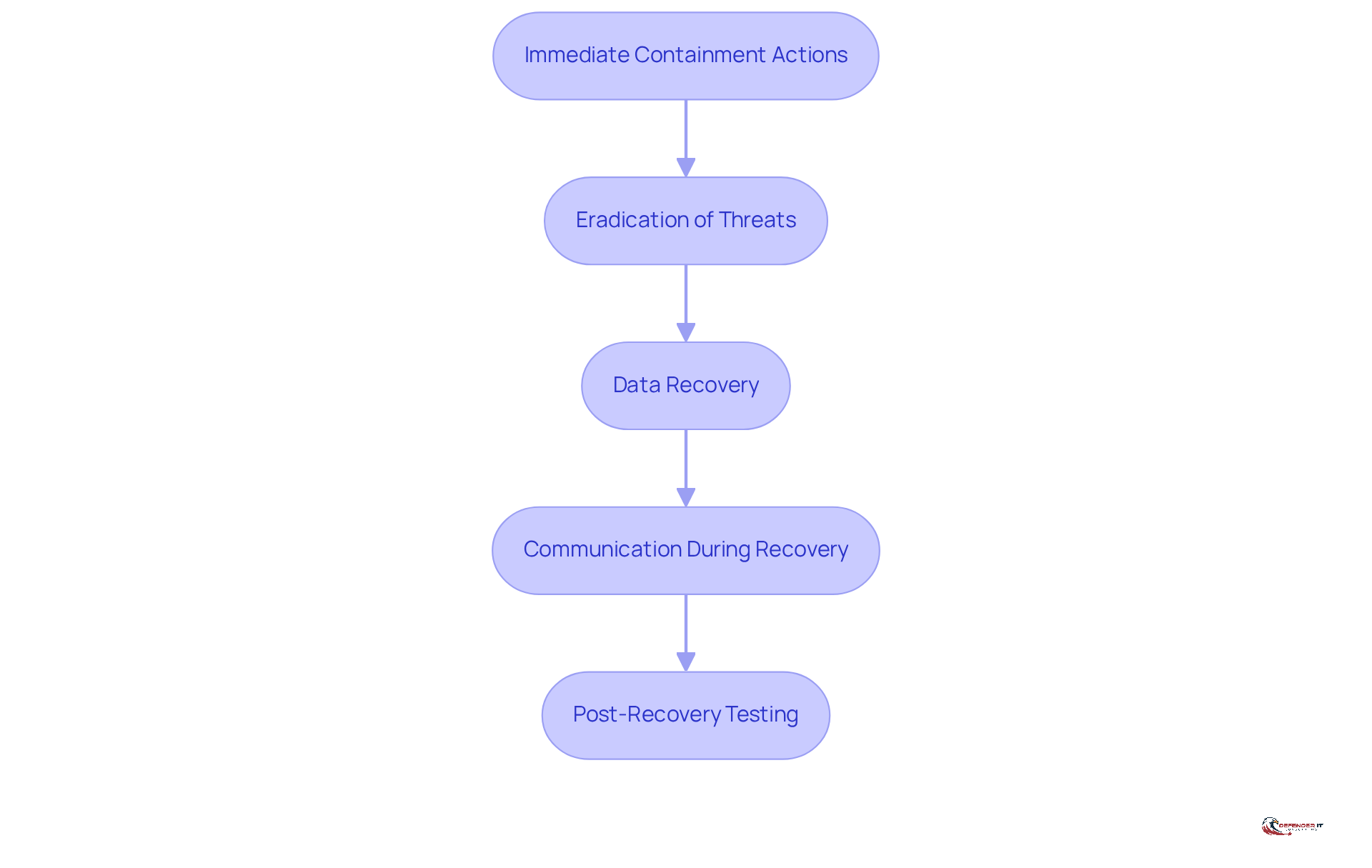
To implement , organizations should consider the following steps:
- Immediate Containment Actions: Upon detecting an occurrence, . This may involve isolating affected systems, disabling compromised accounts, or blocking malicious traffic to prevent further damage. with stakeholders during this phase is essential to reduce confusion and protect the organization’s reputation.
- Eradication of Threats: Once containment is achieved, the focus shifts to of the event. This includes , closing vulnerabilities, and applying necessary patches to affected systems. Efficient elimination is vital to avoid the reappearance of similar occurrences. Engaging legal counsel during this phase can ensure compliance with regulatory requirements.
- : Ensure that data backups are readily available and functional. In the event of data loss, initiate recovery processes to restore affected systems and data to their pre-incident state. It is vital to use verified clean backups for restoring operations securely. Regularly testing backup systems can significantly enhance recovery success rates after cyber events.
- Communication During Recovery: Maintain with stakeholders throughout the containment and recovery process. This includes providing updates on recovery efforts and any potential impacts on operations, which is vital for maintaining trust and compliance with regulatory obligations. Effective communication helps mitigate confusion and reputational damage.
- Post-Recovery Testing: After recovery, conduct and functioning correctly. This step is essential to confirm that all threats have been eliminated and to avert future occurrences. Gaining knowledge from previous incidents and carrying out forensic examinations can offer valuable insights for enhancing future responses.
By implementing these containment and recovery procedures as part of NIST security incident response, companies can effectively manage incidents and minimize their impact on business operations. Each step not only addresses immediate concerns but also contributes to long-term resilience against cyber threats.
Conduct Post-Incident Reviews for Continuous Improvement
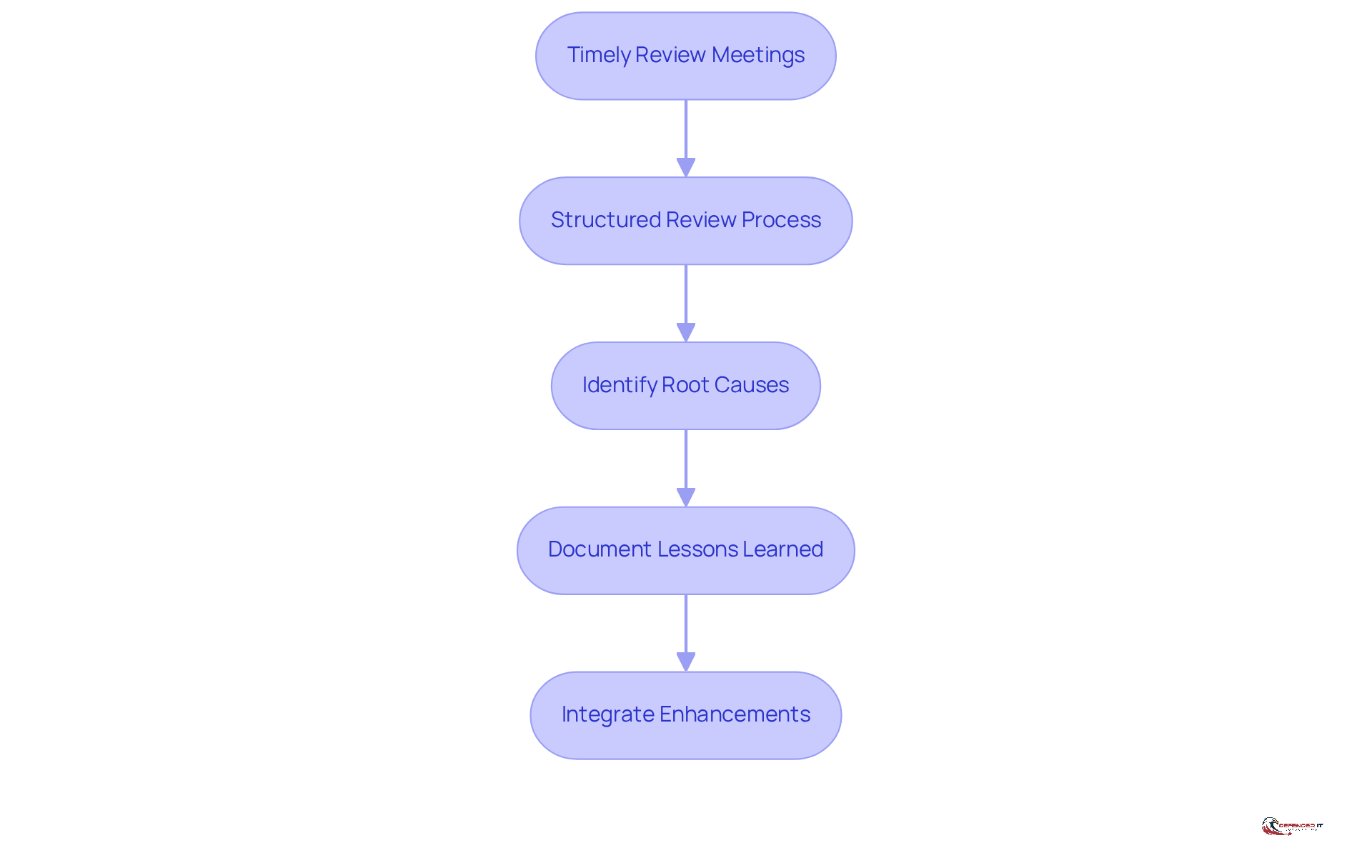
To conduct effective , organizations should adhere to the following best practices:
- : Schedule review meetings promptly after an event to ensure that details remain fresh in the minds of the involved personnel. Aim to conduct these meetings within a week of issue resolution.
- : Implement a structured agenda for the review to address all relevant aspects of the occurrence, including detection, response, and recovery efforts. This approach guarantees comprehensive coverage of the event.
- : Analyze the occurrence to ascertain root causes and contributing factors. Understanding why the event transpired is essential for preventing similar situations in the future.
- Document : Develop detailed documentation of the review findings, encompassing and recommendations for improvement. This documentation should be readily accessible to all relevant stakeholders.
- : Leverage the insights gained from the review to update occurrence management plans, training programs, and security measures. Continuous improvement is vital for enhancing the overall .
By conducting thorough , organizations can cultivate a culture of learning and resilience, ultimately fortifying their capabilities.
Conclusion
Organizations can significantly enhance their readiness to confront cybersecurity threats by implementing the best practices outlined for NIST security incident response. A structured approach is essential, encompassing:
- Preparation strategies
- Improved detection and analysis capabilities
- Effective containment and recovery procedures
- Comprehensive post-incident reviews
This framework is vital for maintaining resilience in an ever-evolving threat landscape.
Key strategies include:
- Developing a comprehensive Incident Management Plan
- Utilizing advanced monitoring tools
- Conducting timely post-incident reviews
These elements are crucial for success. Furthermore, organizations that prioritize training and communication will be better equipped to respond swiftly and effectively to incidents, thereby protecting their assets and reputation.
The significance of a proactive and well-structured incident response framework cannot be overstated. Organizations are encouraged to adopt these best practices, continually assess their incident response capabilities, and make necessary adjustments to stay ahead of potential threats. By fostering a culture of continuous improvement and learning, businesses can navigate the complexities of cybersecurity challenges and thrive in an increasingly digital world.
Frequently Asked Questions
What is an Incident Management Plan (IMP)?
An Incident Management Plan (IMP) is a comprehensive document that outlines the roles, responsibilities, and procedures for addressing incidents within an organization. It should be tailored to the organization’s specific needs and regularly updated to reflect evolving threats and compliance requirements.
How does having a documented emergency management strategy benefit organizations?
Organizations with documented emergency management strategies reported increased confidence in adopting new technologies and expanding operations, with about 70% indicating that having a formal plan enhanced their operational preparedness.
Why are training sessions and drills important for incident response?
Regular training sessions and simulation exercises are crucial as they ensure all team members understand their roles during emergencies, improve preparedness, and help identify gaps in the action plan. Organizations that participated in training programs reported a 50% decrease in response times during events.
What role do communication protocols play in incident response?
Clear communication protocols are essential for both internal and external stakeholders, allowing for prompt alerts during an incident and efficient information exchange, which helps maintain trust and compliance. Effective communication can significantly mitigate the impact of incidents on an organization’s reputation.
Why is it important to inventory assets and assess risks?
Maintaining an up-to-date inventory of IT assets and assessing their vulnerabilities is critical for prioritizing response efforts and ensuring effective resource allocation. Frequent evaluations help organizations stay ahead of potential risks.
What types of security controls should organizations implement?
Organizations should deploy preventive measures such as firewalls, intrusion detection systems, and regular software updates to mitigate risks before incidents occur. Proactive security measures can reduce the likelihood of successful attacks by up to 60%.
How can organizations enhance their incident response capabilities?
By focusing on preparation strategies such as developing an IMP, conducting training and drills, establishing communication protocols, inventorying assets and risks, and implementing security controls, organizations can significantly improve their incident response capabilities and maintain compliance with regulatory obligations.