Introduction
Understanding the complexities of NT hash is crucial for organizations seeking to enhance their cybersecurity defenses. As a cryptographic representation of user passwords, NT hash is integral to user authentication; however, it is susceptible to various attacks that can jeopardize sensitive data. This article examines effective practices for NT hash implementation, providing insights into how organizations can safeguard themselves against the ever-evolving landscape of cyber threats.
What strategies can be employed to mitigate the risks associated with NT hash vulnerabilities, and how can organizations effectively integrate these practices into their existing frameworks?
Understand NT Hash and Its Role in Cybersecurity
The nt hash serves as a cryptographic representation of a user’s password, generated through the MD4 algorithm applied to the UTF-16LE encoding of the password. This value is securely stored in the Security Account Manager (SAM) database on Windows systems and plays a crucial role in authenticating users within environments that utilize nt hash. Understanding NT hash digests is vital due to their , including Pass-the-Digest (PtD) attacks, where an intruder can exploit the NT hash to authenticate without needing the plaintext password. Consequently, organizations must implement from unauthorized access and exploitation.
Recent incidents, such as the data breach at Loblaw Companies Limited, underscore the severe repercussions of compromised nt hash authentication, where hackers accessed sensitive customer data by exploiting vulnerabilities. Furthermore, a critical vulnerability (CVE-2026-25750) identified in LangSmith poses significant risks, highlighting the urgent need for vigilance against .
The impact of nt hash attacks on organizations in 2026 is substantial, as the is underway, with Microsoft planning to deactivate it by default in future Windows versions. This shift aims to enhance security by prioritizing Kerberos authentication; however, many organizations continue to rely on NTLM due to legacy dependencies. As a result, the prevalence of nt hash vulnerabilities remains a considerable risk, necessitating strong protective measures to safeguard these nt hashes from exploitation.
In light of these challenges, organizations must adopt a proactive cybersecurity strategy, ensuring that nt hash is adequately protected and that security protocols are updated to mitigate risks associated with outdated authentication methods. The significance of nt hash in cybersecurity cannot be overstated, as it is a critical element in defending against credential theft and unauthorized access. Additionally, embracing a is essential for countering evolving threats, equipping organizations to navigate the complexities of modern cybersecurity challenges. As Microsoft indicates, in the operating system and can be explicitly re-enabled via policy if necessary, striking a balance between meaningful security enhancements and support for legacy applications.
Implement Best Practices for NT Hash Integration
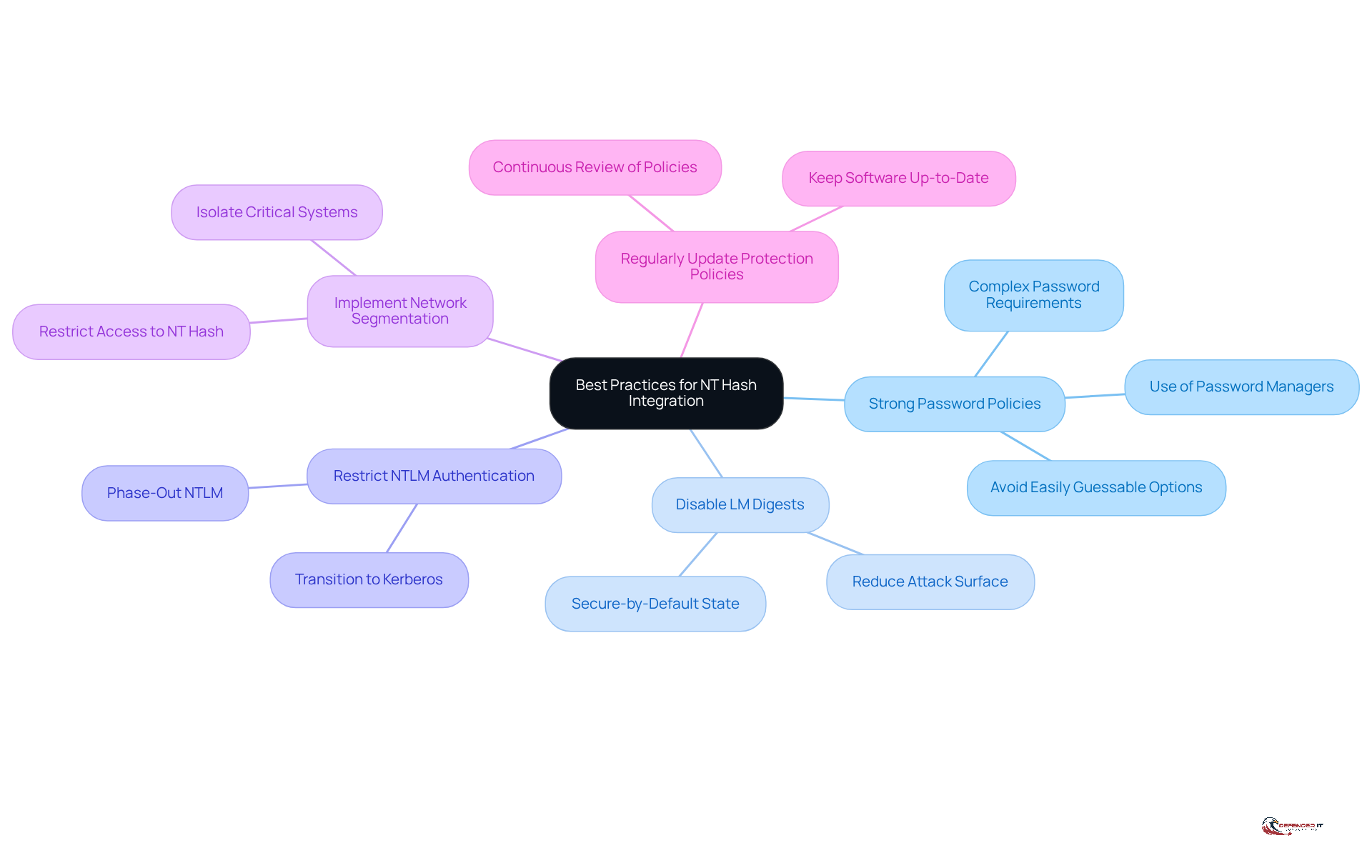
To effectively integrate NT hashes into your , consider the following best practices:
- Use : Enforce complex password requirements to ensure that user passwords are difficult to guess or crack. Passwords should be at least 16 characters long and include a mix of uppercase and lowercase letters, numbers, and special characters. Avoid easily guessable options and personal details, as these can be easily discovered. Millions of passwords are hacked daily, underscoring the urgent need for robust .
- Disable LM Digests: Ensure that only NT digests are stored by disabling the older and less secure LM digests. This action significantly reduces the attack surface for potential value cracking, as LM values are vulnerable to various attacks, including replay and man-in-the-middle attacks. As Mariam Gewida from Microsoft stated, ” means that Windows will be delivered in a secure-by-default state where network authentication of this type is blocked and no longer used automatically.”
- Restrict : such as Kerberos, which do not rely on cryptographic values for verification. Microsoft officially deprecated NTLM in June 202The value is 4, which can be represented using nt hash, and organizations should prioritize to enhance security. The ongoing phase-out process emphasizes the urgency of this transition.
- Implement : Isolate critical systems and restrict access to nt hash to reduce the risk of lateral movement by attackers within the network. This practice helps contain potential breaches and protects sensitive data from unauthorized access.
- Regularly Update Protection Policies: Continuously review and refresh protection policies to adapt to evolving threats and ensure compliance with industry standards. Keeping software up-to-date is crucial, as updates often include security patches for known vulnerabilities, further strengthening your cybersecurity posture. Significantly, an NTLMv1 code can be broken within a day for around 50 euros, underscoring the dangers linked to its ongoing usage.
Monitor and Evaluate NT Hash Effectiveness
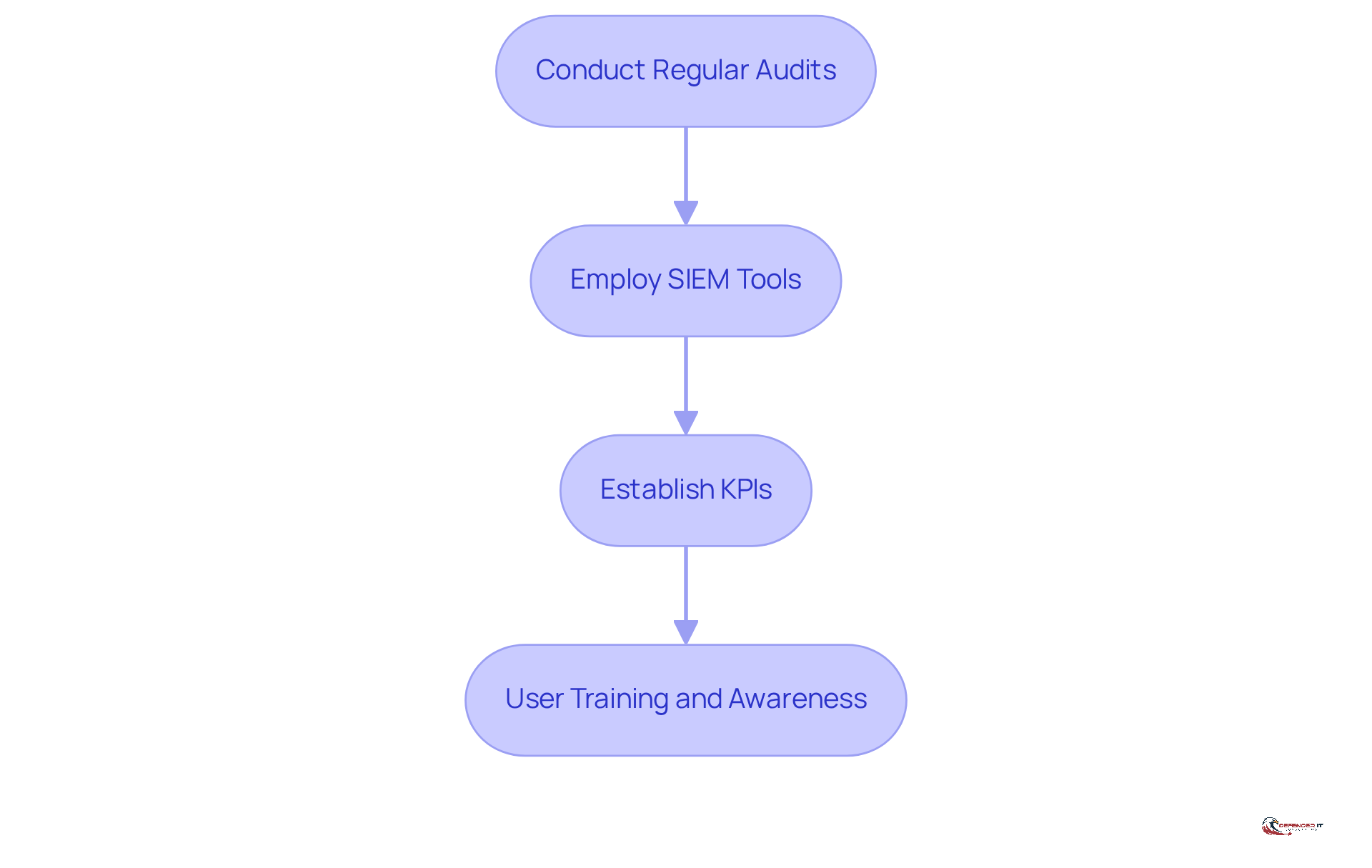
To ensure the effectiveness of your management practices for , it is essential to implement .
- Conduct Regular Audits: Schedule and control measures. This practice helps identify any unauthorized entry or anomalies that could compromise .
- Employ to oversee logs for suspicious activities associated with NT hash. Monitoring for repeated failed login attempts or unusual entry patterns is crucial for early detection of potential threats.
- Establish : Define KPIs related to NT hash data integrity. Metrics such as the number of or the time taken to identify and respond to incidents provide valuable insights into the effectiveness of your .
- : Regularly educate employees on the and the potential dangers linked to poor password practices. This proactive approach can significantly minimize human errors that may lead to security breaches.
Address Challenges in NT Hash Implementation
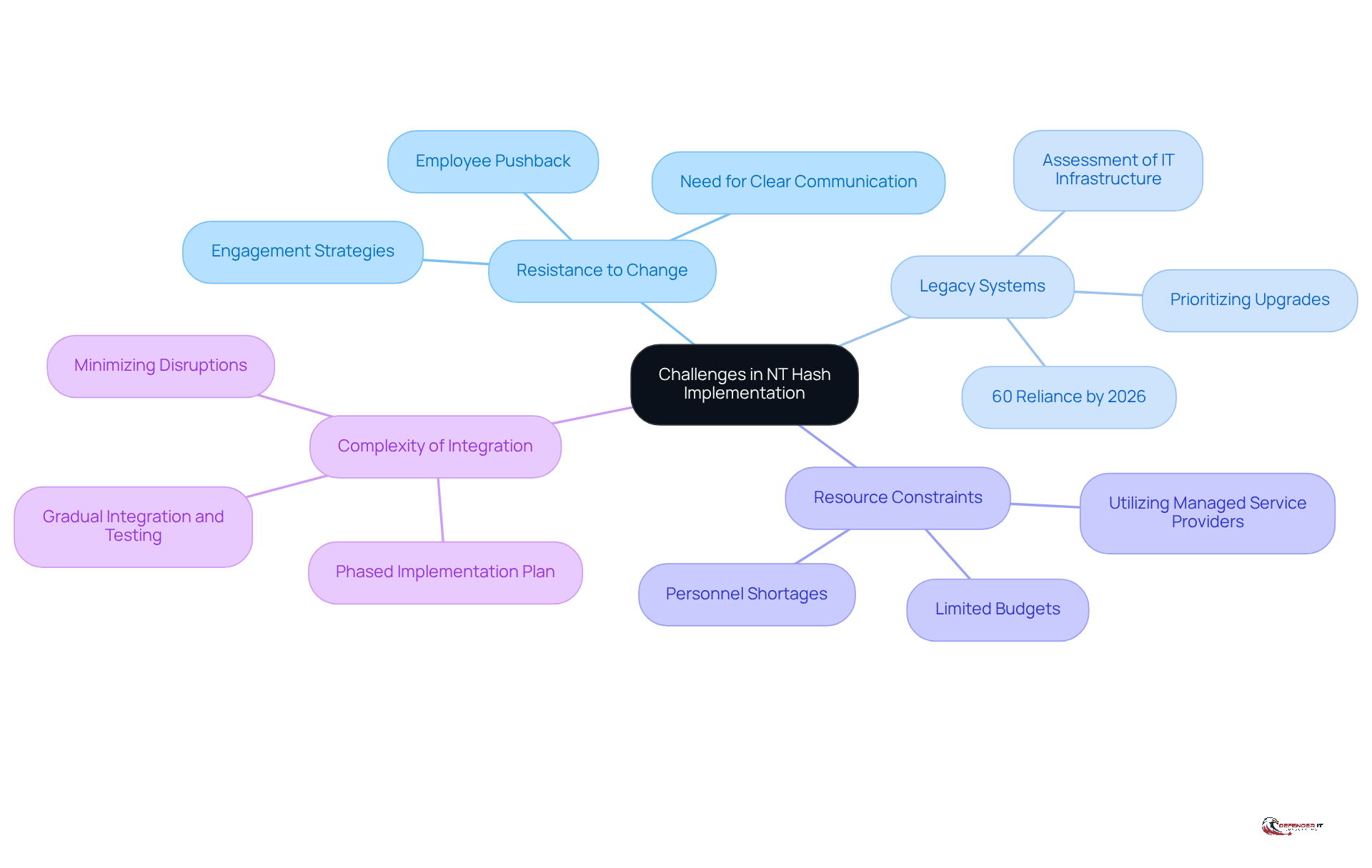
Organizations may encounter several challenges when implementing measures for NT hash protection. Addressing these issues effectively is crucial for .
- Resistance to Change: Employees may resist . Engaging them in the process and providing clear communication about the benefits of can alleviate this resistance. As Microsoft has indicated, transitioning to more secure protocols is vital since the nt hash is no longer actively developed and will be phased out in favor of more secure alternatives.
- : A significant portion of organizations, estimated to be around 60% by 2026, still rely on legacy systems that may not support modern protective measures. It is essential to conduct a thorough assessment of your IT infrastructure and prioritize upgrades or replacements for systems that present substantial risks.
- : Limited budgets and personnel can impede implementation efforts. Utilizing (MSSPs) can enhance internal resources and expertise. This collaboration can help bridge gaps in internal capabilities and strengthen overall defense strategies.
- Complexity of Integration: The integration of new protective measures can be complex. Developing a allows for gradual integration and testing of new practices, minimizing disruptions. This approach enables teams to adapt to changes more effectively, ensuring a smoother transition to enhanced security protocols.
Conclusion
The importance of implementing NT hash in cybersecurity cannot be overstated. Organizations must prioritize this aspect to protect against unauthorized access and credential theft. By understanding the nuances of NT hash, including its vulnerabilities and the potential risks associated with its misuse, businesses can adopt more effective strategies to safeguard their systems and data.
To enhance the security of NT hash, several best practices have been outlined. These include:
- Enforcing strong password policies
- Disabling outdated LM digests
- Transitioning to secure authentication methods like Kerberos
- Implementing network segmentation
- Regularly updating protection policies
Additionally, monitoring and evaluating the effectiveness of these measures through audits and user training can significantly strengthen an organization’s cybersecurity posture.
As organizations navigate the complexities of modern cybersecurity threats, embracing proactive strategies and fostering a culture of security awareness are essential. By prioritizing NT hash security and addressing the challenges associated with its implementation, organizations can better defend against potential breaches and ensure the integrity of their sensitive information.
Frequently Asked Questions
What is an NT hash?
An NT hash is a cryptographic representation of a user’s password, generated using the MD4 algorithm applied to the UTF-16LE encoding of the password. It is securely stored in the Security Account Manager (SAM) database on Windows systems.
Why is understanding NT hash important in cybersecurity?
Understanding NT hash is vital because it is susceptible to various attacks, such as Pass-the-Digest (PtD) attacks, where an intruder can authenticate without needing the plaintext password. Protecting NT hash from unauthorized access is crucial for maintaining security.
What recent incidents highlight the risks associated with compromised NT hash authentication?
The data breach at Loblaw Companies Limited is a notable incident where hackers exploited vulnerabilities in NT hash authentication to access sensitive customer data, underscoring the severe repercussions of compromised NT hashes.
What is the significance of the vulnerability CVE-2026-25750?
CVE-2026-25750 is a critical vulnerability identified in LangSmith that poses significant risks, highlighting the urgent need for vigilance against NT hash vulnerabilities.
How is the transition away from NT hash authentication impacting organizations?
Many organizations are still reliant on NTLM due to legacy dependencies, even as Microsoft plans to deactivate NTLM by default in future Windows versions to enhance security through Kerberos authentication. This ongoing reliance presents a considerable risk due to NT hash vulnerabilities.
What proactive measures should organizations take to protect NT hash?
Organizations should adopt a proactive cybersecurity strategy that includes protecting NT hash, updating security protocols, and implementing robust measures to mitigate risks associated with outdated authentication methods.
How does the Zero Trust + AI protection model contribute to cybersecurity?
Embracing a Zero Trust + AI protection model is essential for countering evolving threats, helping organizations navigate the complexities of modern cybersecurity challenges and defend against credential theft and unauthorized access.
Will NTLM still be available in future Windows operating systems?
Yes, NTLM will persist in the operating system and can be explicitly re-enabled via policy if necessary, allowing organizations to balance meaningful security enhancements while still supporting legacy applications.