Introduction
In an era marked by increasingly sophisticated cyber threats, organizations must prioritize their cybersecurity measures. This article examines ten free vulnerability scanners that enable businesses to proactively identify and mitigate potential security risks, thereby ensuring a robust defense against evolving threats. However, with a plethora of options available, how can organizations discern which tools best align with their unique needs and offer the most effective protection?
Defenderit Consulting: Comprehensive Vulnerability Scanning Solutions
Defenderit Consulting stands out in delivering personalized scanning solutions tailored to the unique needs of businesses across various industries. A notable insight from 2026 reveals that 66% of organizations recognize the critical importance of customized risk evaluations in enhancing their cybersecurity posture, as highlighted by recent industry reports. By leveraging advanced methodologies and technologies, Defenderit Consulting adeptly identifies and mitigates potential threats, ensuring that clients are well-prepared to tackle evolving cyber challenges.
Their comprehensive suite of services encompasses:
- Risk assessments
- Penetration testing
- Ongoing support
All of which are vital for sustaining a robust security posture over time. Real-world incidents, such as the Odido cyberattack, underscore the effectiveness of tailored assessments; organizations that have engaged these services report significant enhancements in their defenses against cyber threats.
As the cybersecurity landscape continues to evolve, forecasts indicate a record-breaking increase in Common Vulnerabilities and Exposures (CVEs) for 2026, further underscoring the necessity of customized risk assessment solutions. Additionally, with 71% of chief risk officers anticipating severe operational disruptions in the coming year due to cyber risks, the urgency for implementing these strategies to protect operations is paramount.
Nessus: Industry-Leading Free Vulnerability Scanner
Nessus is recognized as a leading scanner for security vulnerabilities, distinguished by its extensive plugin library that effectively identifies a wide range of issues. The free vulnerability scanner, Nessus Essentials, allows users to scan up to 16 IPs, making it an optimal solution for small to medium-sized businesses seeking to enhance their security posture without significant financial investment.
In 2026, user satisfaction ratings for Nessus Essentials remain exceptionally high, with an impressive 98% of users indicating they would recommend the tool. This statistic underscores its reliability and effectiveness in the cybersecurity landscape. The user-friendly interface, coupled with comprehensive reporting capabilities, has solidified Nessus Essentials’ status as a preferred choice among cybersecurity professionals.
Industry experts consistently praise the free vulnerability scanner Nessus Essentials for its ability to streamline risk management processes, which is especially beneficial for organizations navigating the complexities of cybersecurity in today’s digital environment. Features such as automated scanning, compliance assessments, and customizable reporting further enhance its appeal, ensuring that small enterprises can effectively identify and address vulnerabilities while maintaining operational efficiency.
OpenVAS: Powerful Open-Source Vulnerability Scanner
OpenVAS (Open Vulnerability Assessment System) is a free vulnerability scanner that provides a comprehensive suite of tools for assessing vulnerabilities. It is particularly advantageous for organizations seeking a customizable solution, as it enables users to create tailored scans based on specific requirements. OpenVAS is regularly updated with new security assessments, ensuring that users can effectively identify and address emerging threats.
As of 2026, OpenVAS’s effectiveness is underscored by its widespread adoption, with 36% of its customers based in the United States, a market grappling with significant cybersecurity challenges. Notable firms, including GoDaddy and EPAM Systems, utilize OpenVAS to enhance their risk management procedures. This practical application demonstrates how OpenVAS can effectively detect critical vulnerabilities, thereby fortifying the security posture of enterprises.
The evolving threat landscape is further emphasized by a 51% increase in phishing attacks, highlighting the necessity for tools like OpenVAS. Cybersecurity leaders underscore the advantages of customizable risk evaluations. For instance, the ability to tailor scans not only improves the accuracy of threat identification but also allows organizations to prioritize vulnerabilities based on their unique risk profiles. This targeted approach is essential in today’s environment, where the frequency and sophistication of cyberattacks continue to escalate.
As Stéphane Nappo remarked, it takes years to build a reputation but only minutes for a cyber incident to destroy it. In conclusion, OpenVAS, which is a free vulnerability scanner, serves as a crucial tool for organizations aiming to strengthen their cybersecurity defenses. Its customizable scanning capabilities, coupled with a commitment to staying abreast of emerging threats, render it an invaluable asset in the ongoing battle against cyber risks.
Burp Suite: Free Tool for Web Application Vulnerability Scanning
Burp Suite is recognized as a premier tool for web application protection testing, particularly due to its free community edition, which provides users with essential features for effective vulnerability scanning using a free vulnerability scanner. This version includes an intercepting proxy, enabling users to examine and modify web traffic, a critical capability for uncovering vulnerabilities in web applications. Its intuitive interface, combined with robust scanning features, has established Burp Suite as a preferred choice among penetration testers and cybersecurity professionals.
The practical applications of Burp Suite underscore its effectiveness in identifying vulnerabilities. Organizations utilizing Burp Suite have reported significant success rates in detecting critical vulnerabilities, underscoring its reliability in enhancing web application security. Penetration testers frequently praise the community edition for its powerful capabilities, which facilitate comprehensive assessments of web applications, ultimately contributing to a more secure digital landscape. As the cybersecurity environment continues to evolve, tools like Burp Suite remain essential for organizations striving to protect their web applications against emerging threats.
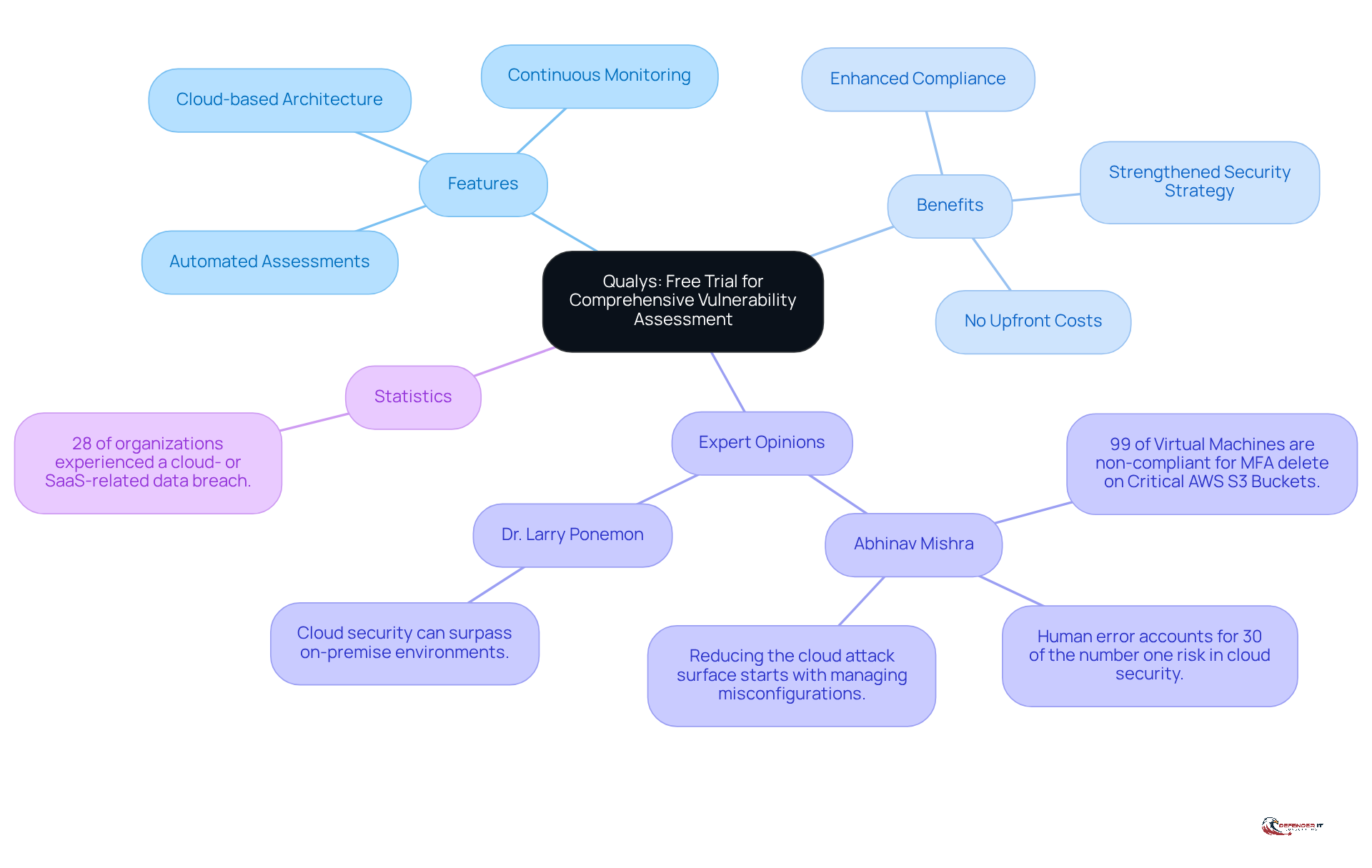
Qualys: Free Trial for Comprehensive Vulnerability Assessment
Qualys offers a compelling 30-day free trial of its risk management platform, allowing organizations to assess their security posture without upfront costs. Renowned for its cloud-based architecture, Qualys delivers continuous monitoring and automated vulnerability assessments, making it an ideal solution for businesses of all sizes. The platform’s robust reporting capabilities and integration features support organizations in enhancing their compliance efforts and strengthening their overall security strategy.
In 2026, organizations leveraging the Qualys platform are expected to report enhanced protective measures, particularly as 28% of organizations experienced a cloud- or SaaS-related data breach in the previous year. This statistic underscores the critical need for utilizing such platforms. Cybersecurity experts, including Abhinav Mishra, emphasize that addressing misconfigurations and educating users about phishing threats are essential for maintaining a proactive defense in today’s rapidly evolving threat landscape. Additionally, Dr. Larry Ponemon highlights that cloud security can often surpass that of on-premise environments, further validating the benefits of adopting Qualys.
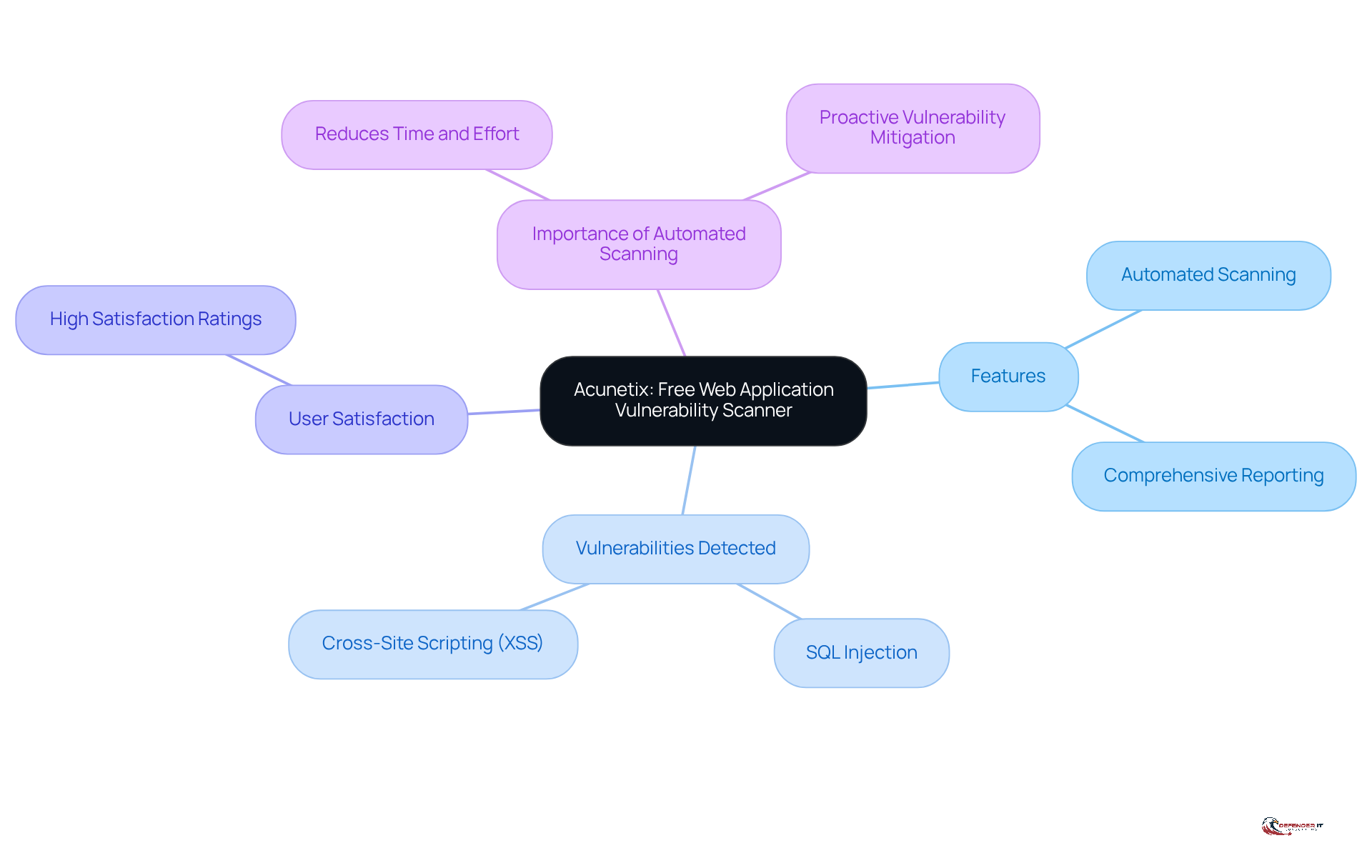
Acunetix: Free Web Application Vulnerability Scanner
Acunetix stands out as a robust web application security scanner, featuring a free vulnerability scanner that allows users to explore its functionalities. This tool is specifically designed to detect vulnerabilities such as SQL injection, cross-site scripting (XSS), and other prevalent web application threats. With its automated scanning process and comprehensive reporting, Acunetix proves to be an essential resource for organizations aiming to secure their web applications effectively.
By 2026, Acunetix has demonstrated exceptional proficiency in identifying SQL injection vulnerabilities, a critical concern for numerous businesses. Its intuitive interface and extensive scanning capabilities have garnered high satisfaction ratings from users of the free vulnerability scanner, making it an appealing choice for organizations looking to improve their cybersecurity posture without incurring costs.
Cybersecurity experts emphasize the importance of automated scanning for web applications, noting that it significantly reduces the time and effort required to identify and rectify vulnerabilities. Real-world case studies illustrate how various organizations have successfully fortified their web applications using Acunetix, further solidifying its status as a crucial tool in the cybersecurity toolkit. By utilizing Acunetix, businesses can proactively mitigate vulnerabilities, thereby protecting their digital assets and preserving trust with their customers.
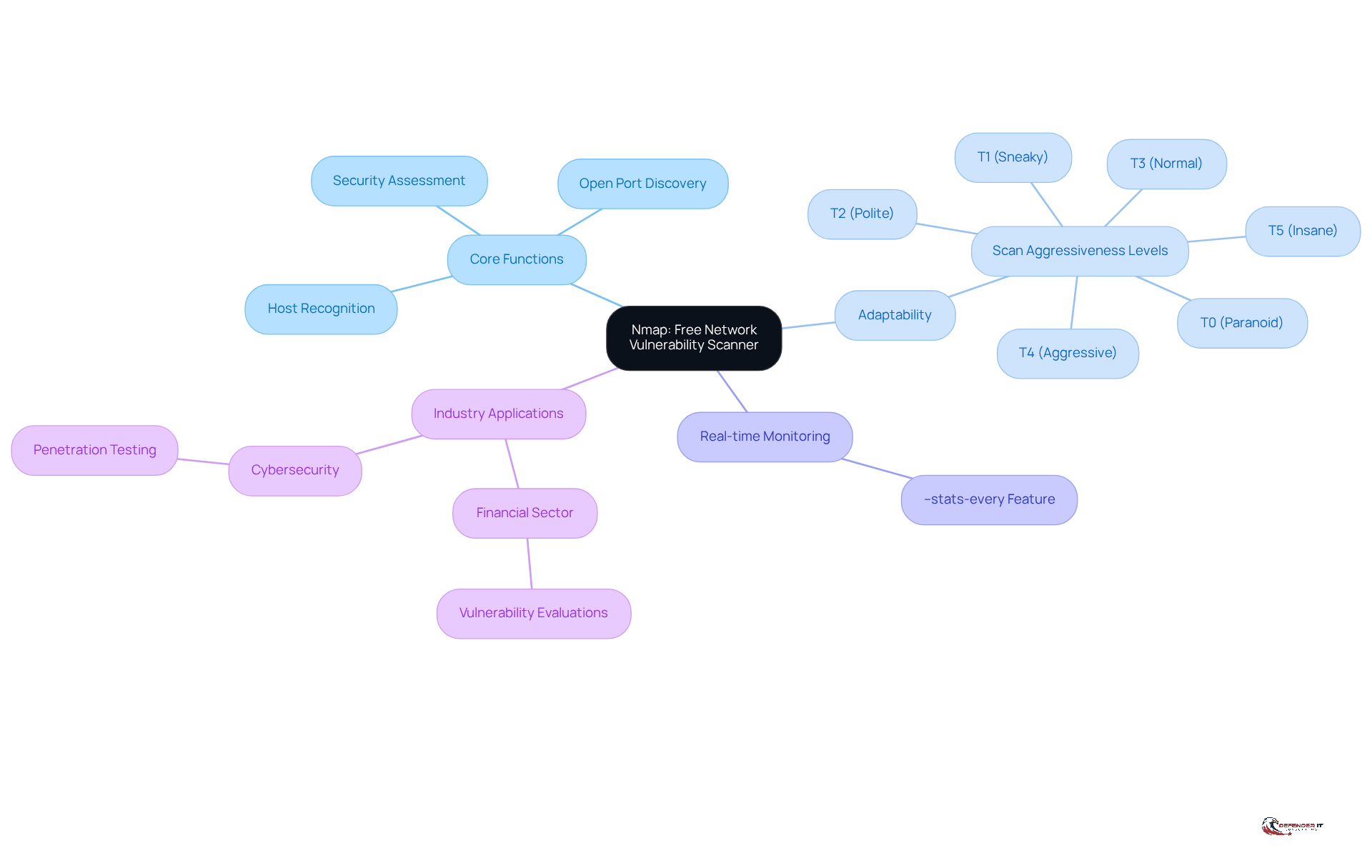
Nmap: Free Network Vulnerability Scanner
Nmap (Network Mapper) is a complimentary and open-source tool that has become essential for network exploration and auditing in 2026. It enables users to recognize hosts and services on a network, find open ports, and assess the protection of networked devices. With its powerful scripting engine and wide-ranging features, Nmap is an essential tool for penetration testers and network administrators seeking to enhance their protection stance.
The effectiveness of Nmap in identifying network weaknesses is underscored by its capacity to adapt to evolving threats. Organizations across various sectors have successfully leveraged Nmap to improve their safety frameworks. For instance, a financial organization has employed Nmap to conduct thorough vulnerability evaluations, resulting in the discovery and resolution of critical vulnerabilities that could have led to significant financial losses.
Cybersecurity experts frequently commend Nmap for its adaptability in vulnerability assessment. Its capability to perform scans with varying degrees of aggressiveness-ranging from the cautious T0 (paranoid) to the rapid T5 (insane)-enables administrators to tailor their approach according to specific network conditions and protection needs. This adaptability is crucial for maintaining an effective defense stance in today’s dynamic threat landscape.
Moreover, Nmap’s capabilities extend beyond mere flaw detection. By utilizing the --stats-every option, network administrators can monitor scan progress in real-time, gaining insights into the number of hosts scanned and the estimated time remaining. This feature is particularly advantageous for large networks, where understanding scan duration can optimize assessments and resource allocation. For example, using the command sudo nmap --stats-every 5s 192.168.1.0/24 allows users to display scan statistics at regular intervals, enhancing their monitoring capabilities.
In conclusion, Nmap is recognized as a robust tool for network protection assessment in 2026, offering organizations the ability to proactively detect weaknesses and improve their overall defense stance.
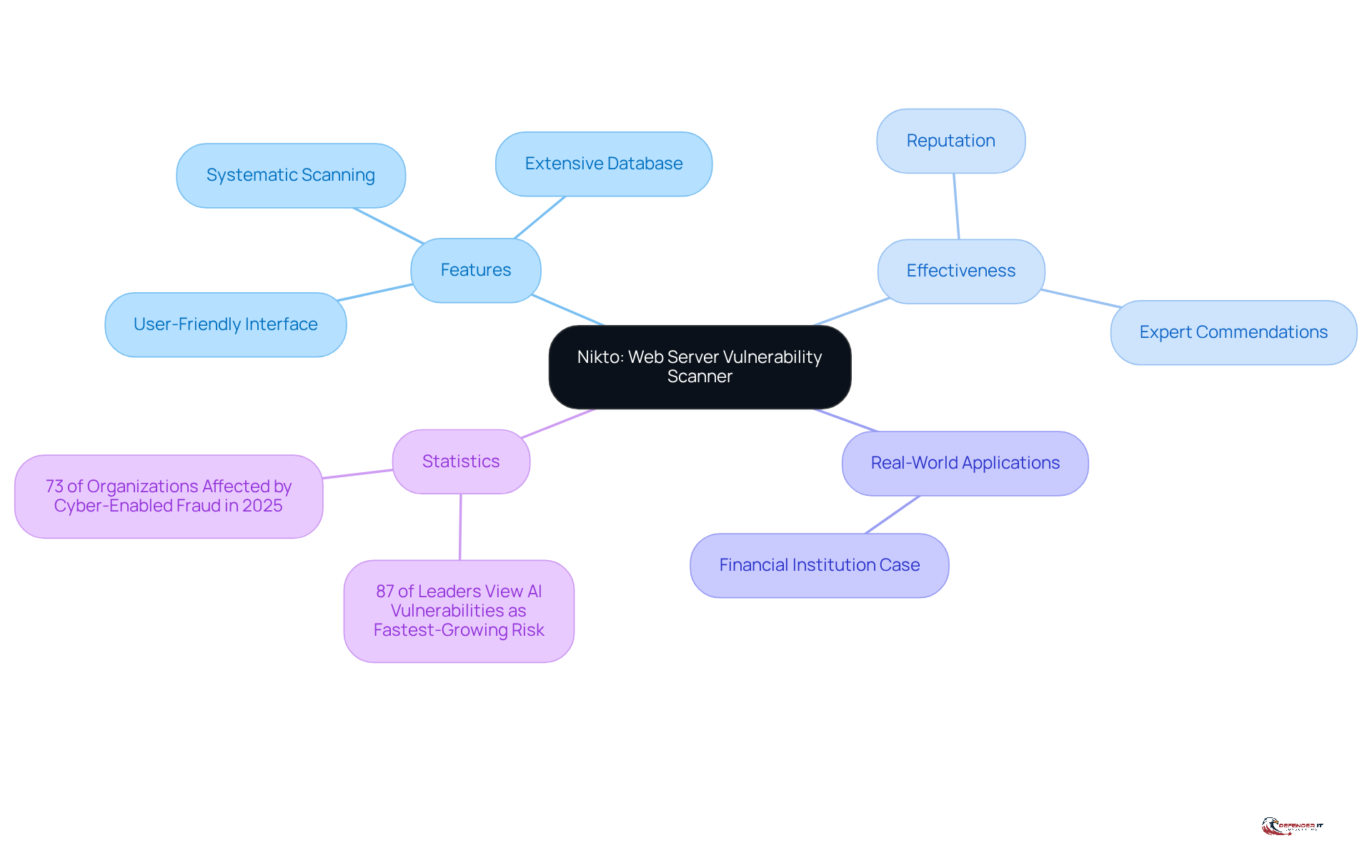
Nikto: Free Open-Source Web Server Vulnerability Scanner
Nikto is a robust open-source web server flaw scanner that conducts thorough assessments of web servers to identify potential security vulnerabilities. It systematically scans for outdated software, malicious files, and common weaknesses, making it an essential tool for web administrators and security professionals. With its user-friendly interface and extensive database of known vulnerabilities, Nikto facilitates rapid evaluations of web server security.
As of 2026, Nikto continues to demonstrate its effectiveness in identifying vulnerabilities, with numerous web administrators reporting successful detection of issues that could otherwise result in significant breaches. Security experts have commended Nikto for its capability to uncover hidden risks, solidifying its reputation as a dependable scanner within the cybersecurity domain. As Akshay Joshi, Head of the Centre for Cybersecurity at the World Economic Forum, noted, "87% of leaders view AI-related vulnerabilities as the fastest-growing cyber risk," underscoring the critical need for effective tools like Nikto in the current landscape.
Real-world examples further illustrate Nikto’s value; for instance, a web administrator at a financial institution utilized Nikto to conduct an assessment, revealing critical vulnerabilities that were promptly addressed, thereby enhancing the organization’s overall security posture. Such cases underscore the necessity of integrating tools like Nikto into regular evaluations to sustain robust defenses against evolving cyber threats. Indeed, statistics indicate that 73% of organizations reported that someone in their network was affected by cyber-enabled fraud in 2025, highlighting the urgency for proactive protective measures.
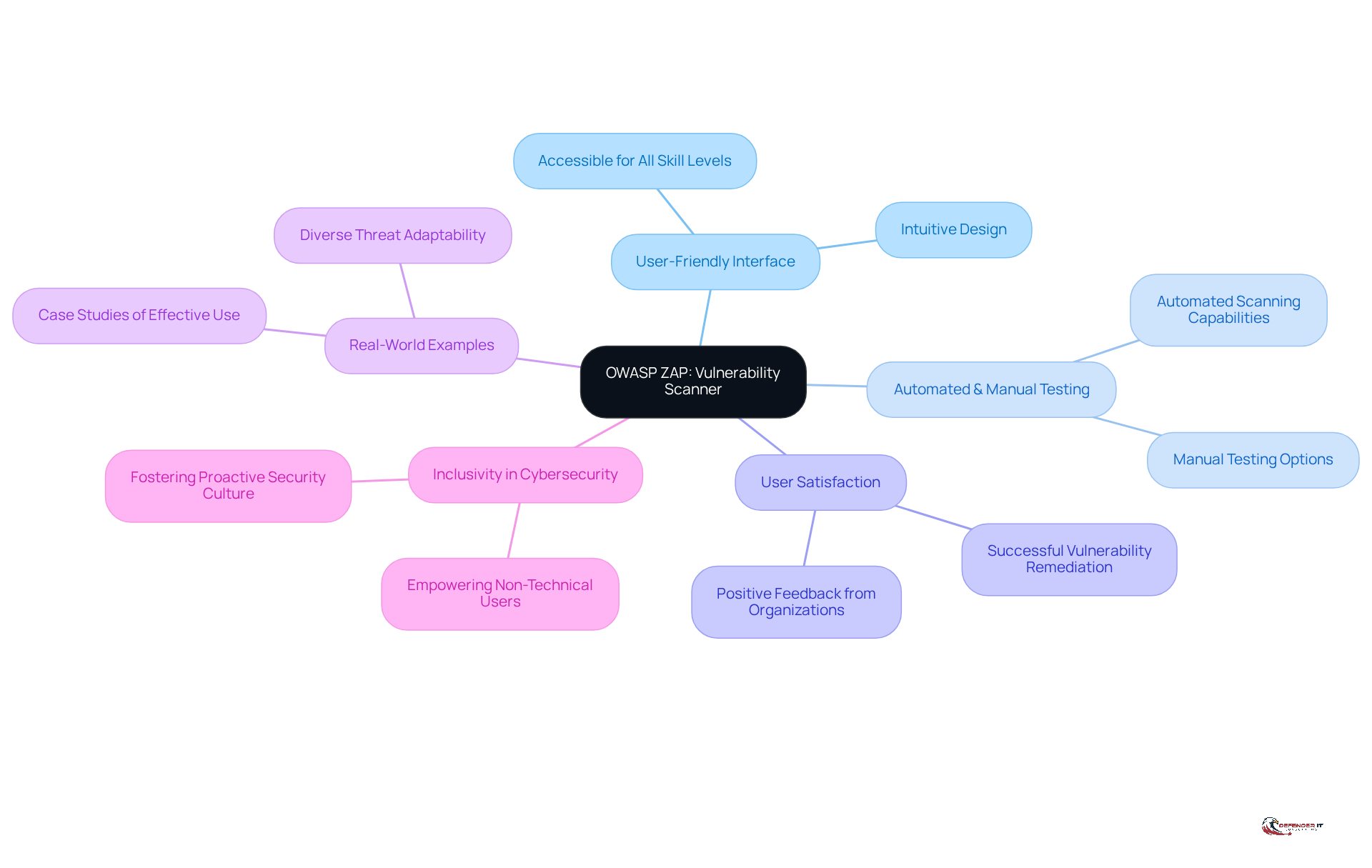
ZAP: User-Friendly Free Web Application Vulnerability Scanner
OWASP ZAP (Zed Attack Proxy) is a free vulnerability scanner and an open-source tool designed to identify weaknesses in web applications. It provides both automated and manual testing capabilities, making it suitable for users of all skill levels. Its user-friendly interface and robust scanning capabilities enable professionals to effectively identify and resolve vulnerabilities with a free vulnerability scanner, thereby strengthening web applications against potential threats.
In 2026, user satisfaction ratings for OWASP ZAP underscore its effectiveness, with numerous organizations reporting successful vulnerability remediation through its use. Real-world examples demonstrate how various organizations leverage ZAP to enhance their security posture, showcasing its adaptability in addressing diverse threats.
Cybersecurity leaders have noted the tool’s accessibility, emphasizing that it empowers users, regardless of their technical background, to engage in effective testing against threats. This inclusivity is crucial in fostering a proactive security culture within organizations.
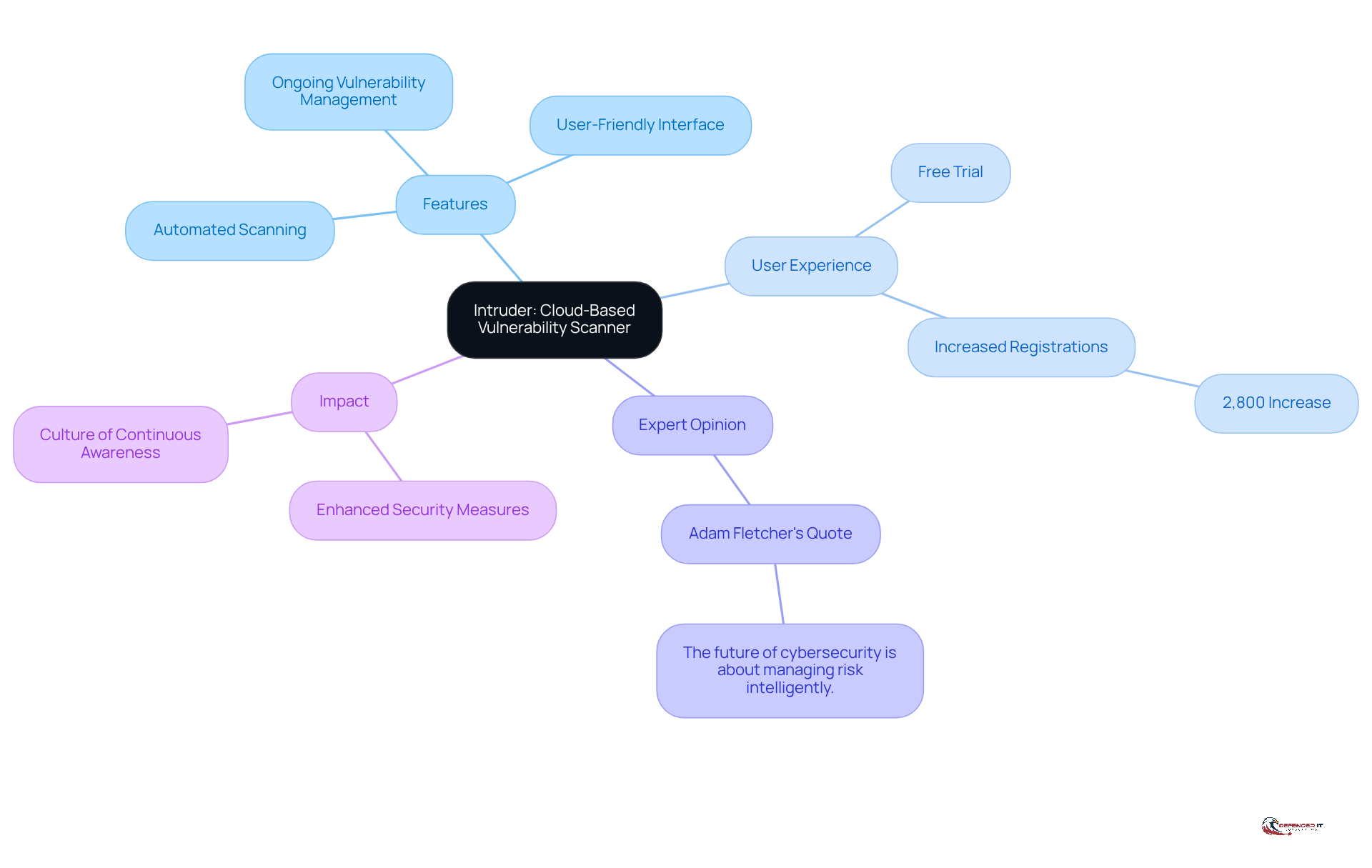
Intruder: Cloud-Based Vulnerability Scanner with Free Trial
Intruder serves as a cloud-based security scanner that provides organizations with a comprehensive view of their security posture. It offers a free trial, enabling users to explore its features without any commitment. Intruder places a strong emphasis on ongoing vulnerability management, allowing organizations to proactively detect and address vulnerabilities.
The platform’s user-friendly interface and automated scanning capabilities position it as an excellent choice for businesses aiming to bolster their cybersecurity defenses. Notably, organizations utilizing Intruder’s free trial have reported an impressive 2,800% increase in registrations, highlighting its effectiveness in converting users to full subscriptions.
As cybersecurity expert Adam Fletcher states, "The future of cybersecurity is about managing risk intelligently," and Intruder’s approach aligns seamlessly with this vision. By leveraging Intruder, organizations can not only fortify their defenses but also foster a culture of continuous awareness-an essential aspect in today’s evolving threat landscape.
Real-world examples illustrate that companies employing Intruder have significantly enhanced their security measures, further reinforcing the platform’s value in proactive cybersecurity management.
Conclusion
Utilizing free vulnerability scanners is essential for enhancing cybersecurity. These tools empower organizations to identify and address potential threats, playing a crucial role in establishing a resilient security framework. By leveraging various scanners, businesses can proactively manage vulnerabilities and protect their digital assets.
This article highlights ten free vulnerability scanners, each offering unique features and benefits. For instance:
- Nessus provides an extensive plugin library
- OpenVAS offers customizable scanning capabilities
- Burp Suite specializes in web application testing tools
These resources are vital for organizations of all sizes. Additionally, insights into tools like Qualys, Acunetix, Nmap, Nikto, ZAP, and Intruder illustrate the diverse options available for conducting thorough assessments and effectively mitigating risks.
In a landscape where cyber threats are increasingly sophisticated and prevalent, adopting these free tools is not merely a strategic advantage; it is a necessity. Organizations are encouraged to explore these scanners, integrate them into their security protocols, and foster a culture of continuous vigilance. By doing so, they can significantly enhance their cybersecurity posture and safeguard against the ever-evolving array of cyber risks.