Introduction
In today’s landscape, where cyber threats are more prevalent than ever, the manufacturing sector emerges as a primary target for malicious attacks. Alarming statistics indicate a significant increase in incidents, prompting industry leaders to confront the complexities of safeguarding their operations. Understanding the essential cyber security services provided by Managed Security Service Providers (MSSPs) is crucial for these leaders.
This article examines ten indispensable MSSP cyber security services specifically designed for manufacturing executives, highlighting how these services not only strengthen defenses but also enhance operational resilience.
What strategies can manufacturers adopt to stay ahead of evolving threats and ensure compliance in an increasingly digital environment?
Defenderit Consulting: Comprehensive Vulnerability Assessments
represent a crucial initial phase in any , particularly for industry leaders. These assessments systematically identify, quantify, and prioritize vulnerabilities within systems, enabling organizations to pinpoint where their operations are most at risk in the context of MSSP cyber security. In 2026, approximately 75% of production firms reported conducting vulnerability assessments, underscoring their essential role in protecting operations against .
Defenderit Consulting utilizes advanced tools and methodologies to perform comprehensive assessments, ensuring that all potential weaknesses are thoroughly identified and documented. This proactive approach not only mitigates risks but also aligns with across various industry regulations, including those mandated by the (CMMC).
The significance of vulnerability assessments is further highlighted by alarming trends in . The sector has been the for four consecutive years, with ransomware gangs claiming over 1,000 attacks in the past year alone. These incidents have resulted in , emphasizing the need for manufacturers to . By implementing effective vulnerability assessments, organizations can significantly reduce their risk exposure, ultimately safeguarding their operations and reputation in an increasingly digital landscape.
Penetration Testing: Uncovering Security Weaknesses
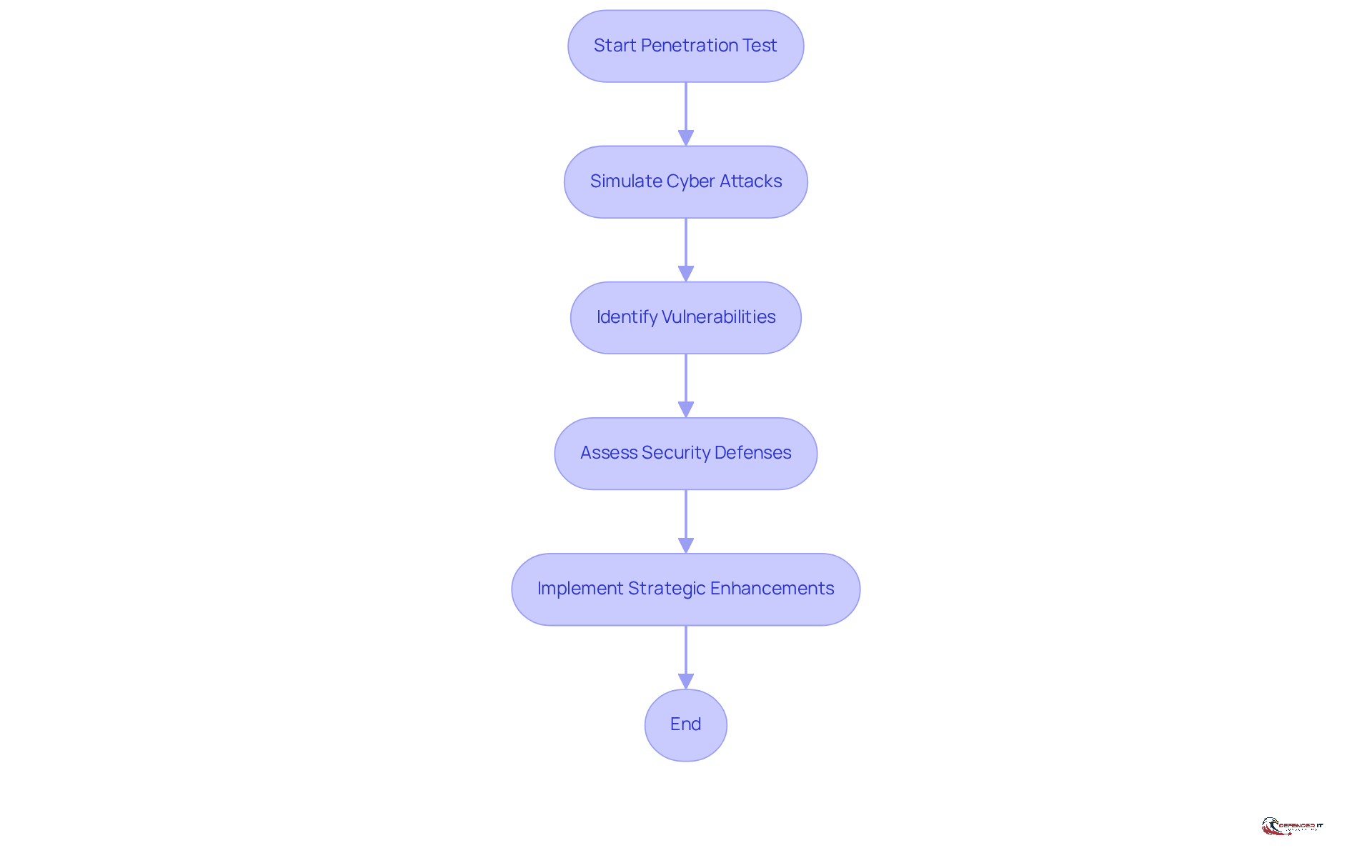
is a critical process that simulates to . This service is particularly invaluable for , as it offers a of their .
conducts that closely mimic the tactics employed by cybercriminals. This approach allows organizations to observe firsthand where their defenses may be insufficient. The outcomes of these assessments not only highlight vulnerabilities but also guide strategic enhancements, ultimately .
Threat Intelligence: Staying Ahead of Cyber Threats
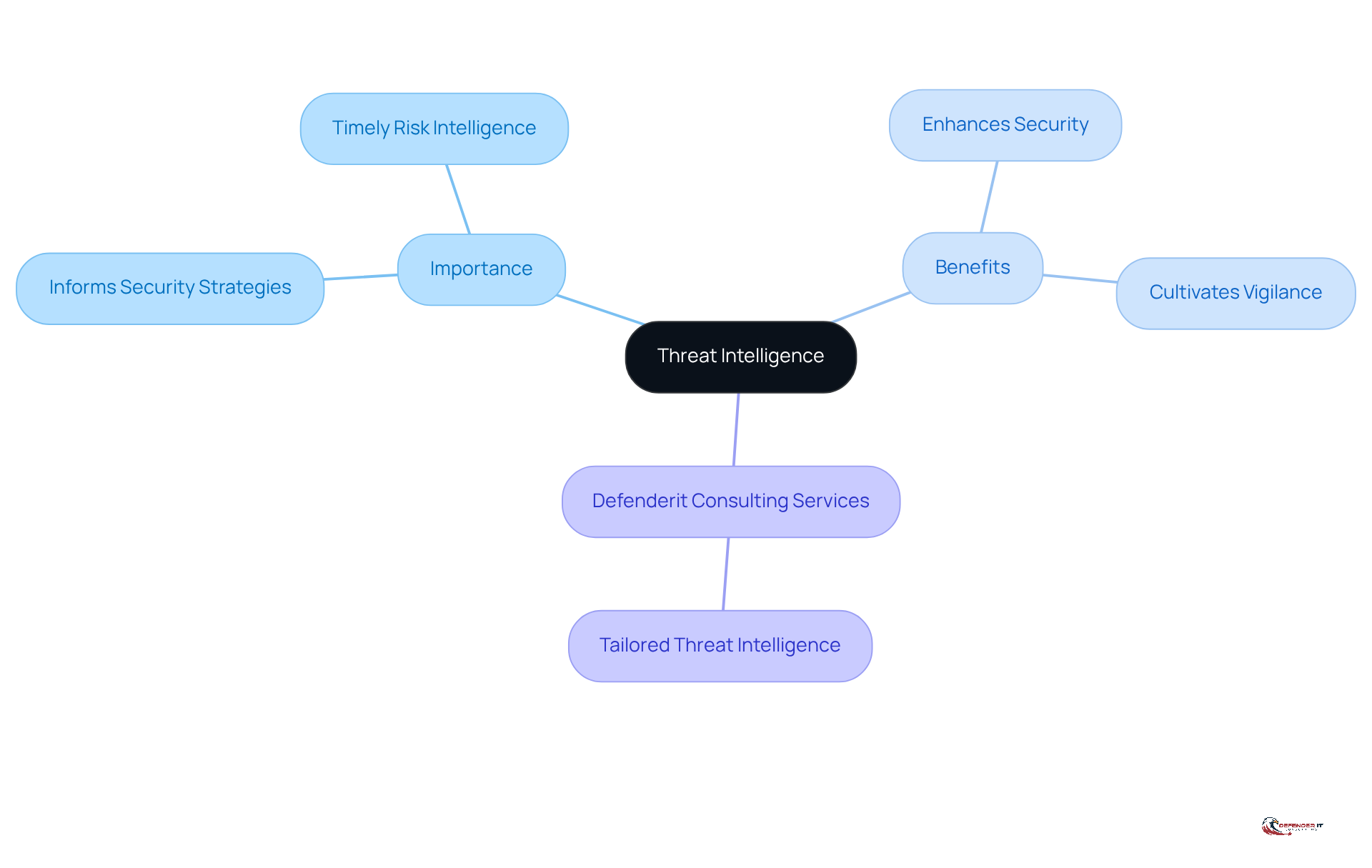
Threat intelligence is essential for informing security strategies by gathering and analyzing information about current and . For manufacturing leaders, is critical. offers tailored that empower organizations to understand the they face. This understanding enables them to implement effectively.
This not only enhances security but also within the organization. By prioritizing threat intelligence, organizations can stay ahead of potential risks and foster a resilient .
Incident Response: Managing Security Breaches Effectively
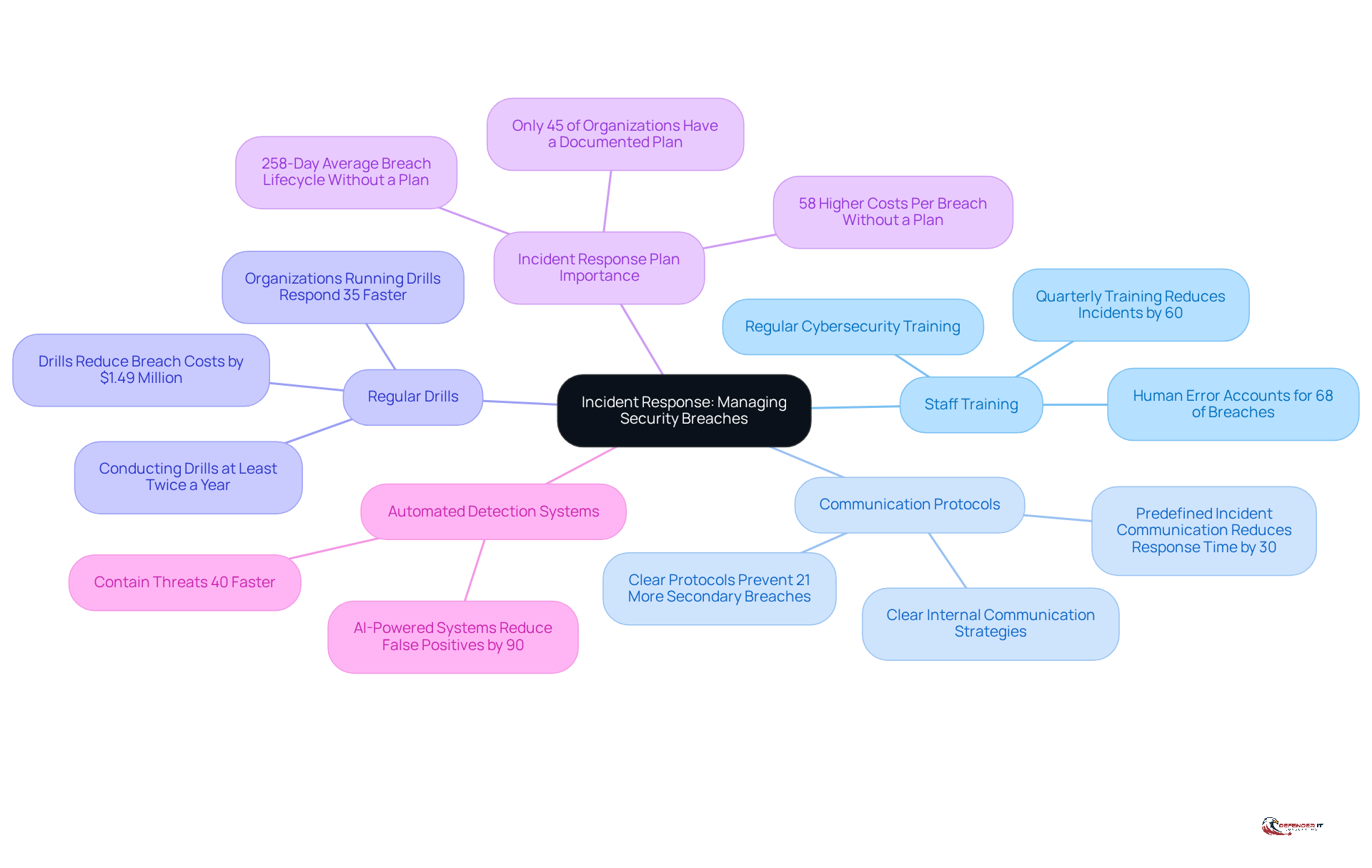
encompasses the systematic processes and procedures that organizations implement to detect, respond to, and recover from . For production leaders, having a clearly outlined is not merely advantageous; it is essential for safeguarding operations and minimizing potential damage. specializes in aiding organizations to develop and implement effective incident response strategies tailored to the unique challenges of their industry.
Key components of a robust incident response strategy include:
- Staff Training: Regular equip employees with the knowledge to recognize and respond to security threats, significantly reducing the likelihood of breaches caused by human error, which accounts for 68% of incidents.
- Communication Protocols: Establishing clear internal communication strategies can prevent 21% more secondary breaches, ensuring that all team members are informed and coordinated during a crisis.
- Regular Drills: Conducting frequent incident response drills prepares teams for real-world scenarios, enhancing their readiness and response times. Organizations that run drills at least twice a year can reduce breach costs by an average of $1.49 million.
Recent incidents in the production sector, such as the Jaguar Land Rover cyberattack, underscore the critical need for effective response strategies. This attack, which resulted in a , highlighted vulnerabilities that can emerge from inadequate preparation. Currently, manufacturers face an average of 1,585 attempted cyberattacks per week, with overall attacks on the sector increasing by 30% year over year, making proactive incident response planning more crucial than ever.
Current best practices for incident response in manufacturing include:
- Developing a comprehensive incident response plan that is regularly updated and tested.
- Utilizing automated detection systems to identify threats more quickly, as companies with such systems can contain threats 40% faster.
- Engaging in to learn from breaches and improve future responses, as only 40% of companies document these findings, which can significantly enhance response speed and accuracy.
The in manufacturing is currently around 258 days, emphasizing the importance of having a in place. Organizations without a formal incident response plan face a 258-day average breach lifecycle and incur 58% higher costs per breach. By partnering with Defenderit Consulting for , industry leaders can ensure they are well-prepared to effectively manage security breaches, thereby protecting their operations and reputation in an increasingly digital landscape.
Compliance Consulting: Navigating Regulatory Requirements
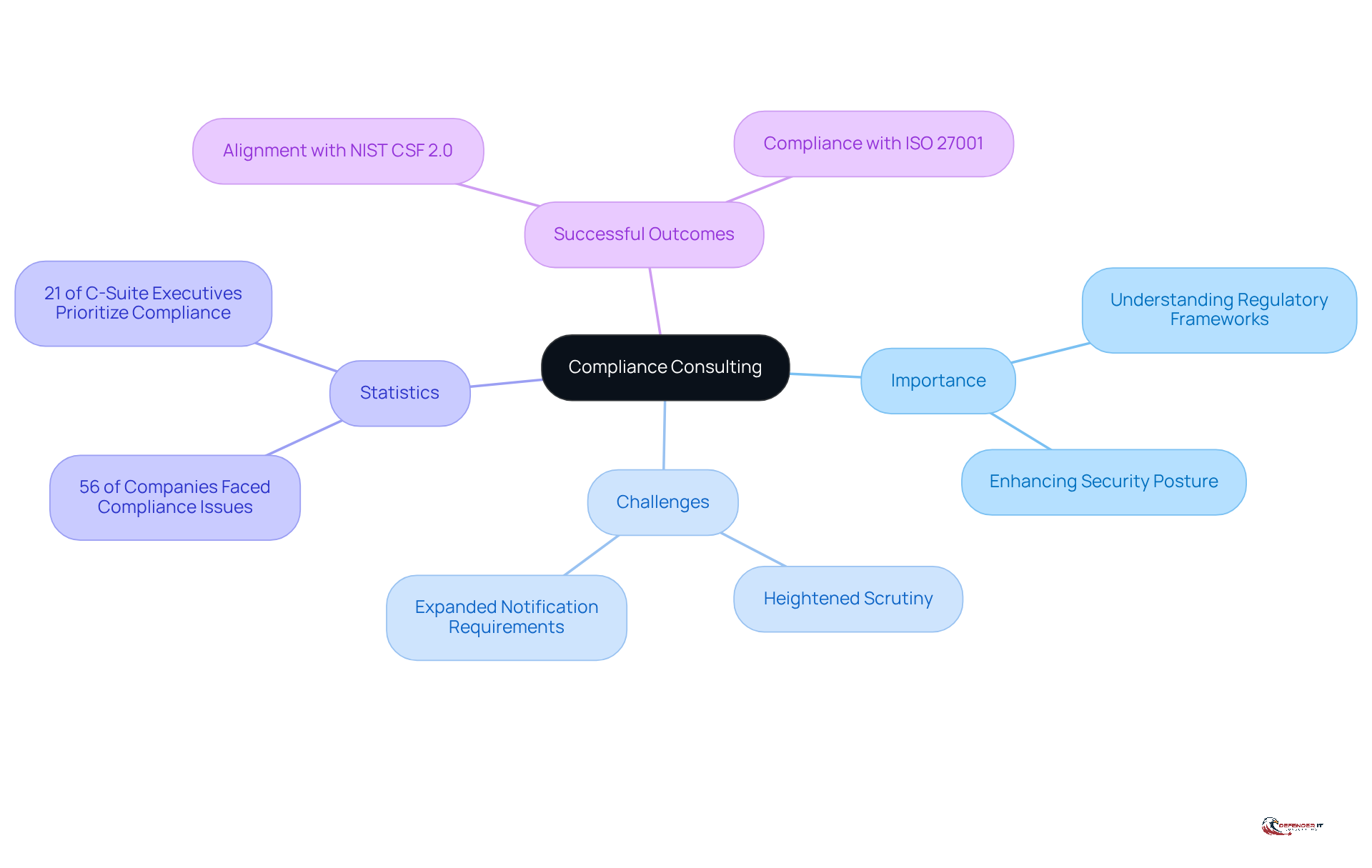
is essential for organizations to effectively navigate the . For production leaders operating under stringent regulatory frameworks, understanding and adhering to these regulations is vital. Defenderit Consulting specializes in tailored for the manufacturing sector, helping organizations manage intricate regulations such as GDPR and HIPAA. This proactive approach not only ensures compliance but also enhances the overall of the organization with .
As we progress through 2026, manufacturers are anticipated to encounter due to escalating digital threats and new mssp cyber security laws. Recent statistics indicate that 56% of risk and compliance experts reported their companies faced at least one compliance issue in the past three years, underscoring the urgent need for , particularly within the industrial context. Additionally, a significant 21% of C-Suite executives in the manufacturing sector have recognized as a top strategic priority, reflecting a notable shift in corporate focus towards compliance in this industry.
Successful outcomes in compliance consulting can be observed in case studies where production organizations have established , particularly in relation to mssp cyber security, leading to improved operational resilience and reduced risks. For example, manufacturers that align with frameworks such as NIST CSF 2.0 and ISO 27001 not only safeguard their revenue but also secure a competitive advantage in the market. As the regulatory landscape continues to evolve, the importance of compliance consulting in maintaining a secure and compliant operation cannot be overstated.
Managed Security Monitoring: Continuous Oversight
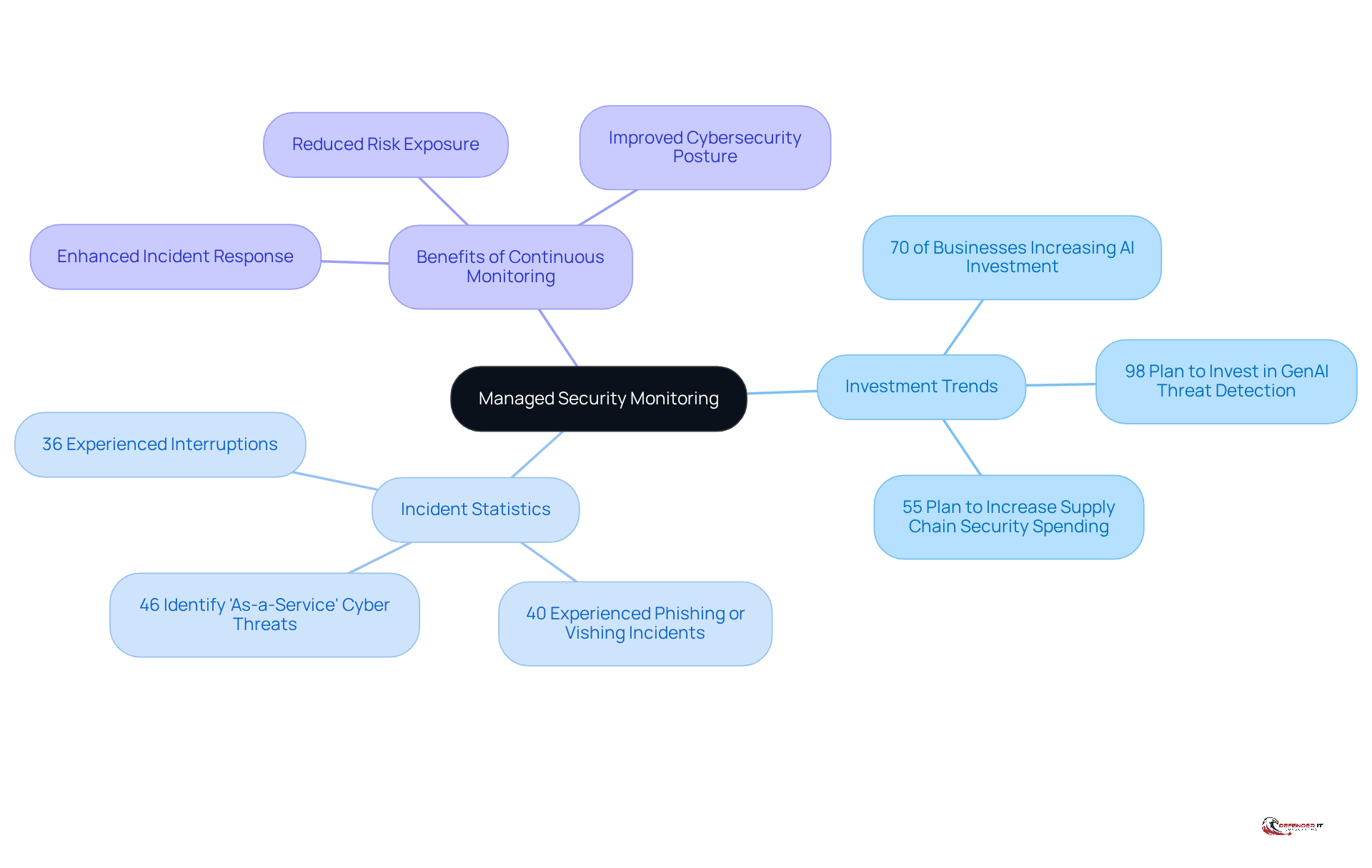
Managed safety monitoring is crucial for production leaders, as it involves the continuous observation of IT environments to identify and address safety risks in real-time. In 2026, the focus on this service is intensifying, with 70% of manufacturing and utilities businesses planning to increase their investment in AI and machine learning security applications.
provides 24/7 monitoring services that leverage advanced technologies to detect potential threats before they escalate into significant issues. This proactive approach not only enhances but also mitigates potential harm. Notably, 36% of entities experienced in the past year, which included temporary system outages or operational disruptions.
Continuous oversight allows organizations to swiftly address incidents, thereby improving their overall . Effective applications of through have demonstrated that organizations can significantly reduce their risk exposure and enhance resilience against emerging threats, particularly at a time when 46% of production companies identify ‘as-a-service’ as their primary challenge.
By prioritizing , manufacturing firms can better protect their operations and ensure compliance with industry regulations.
Security Program Development: Building a Robust Framework
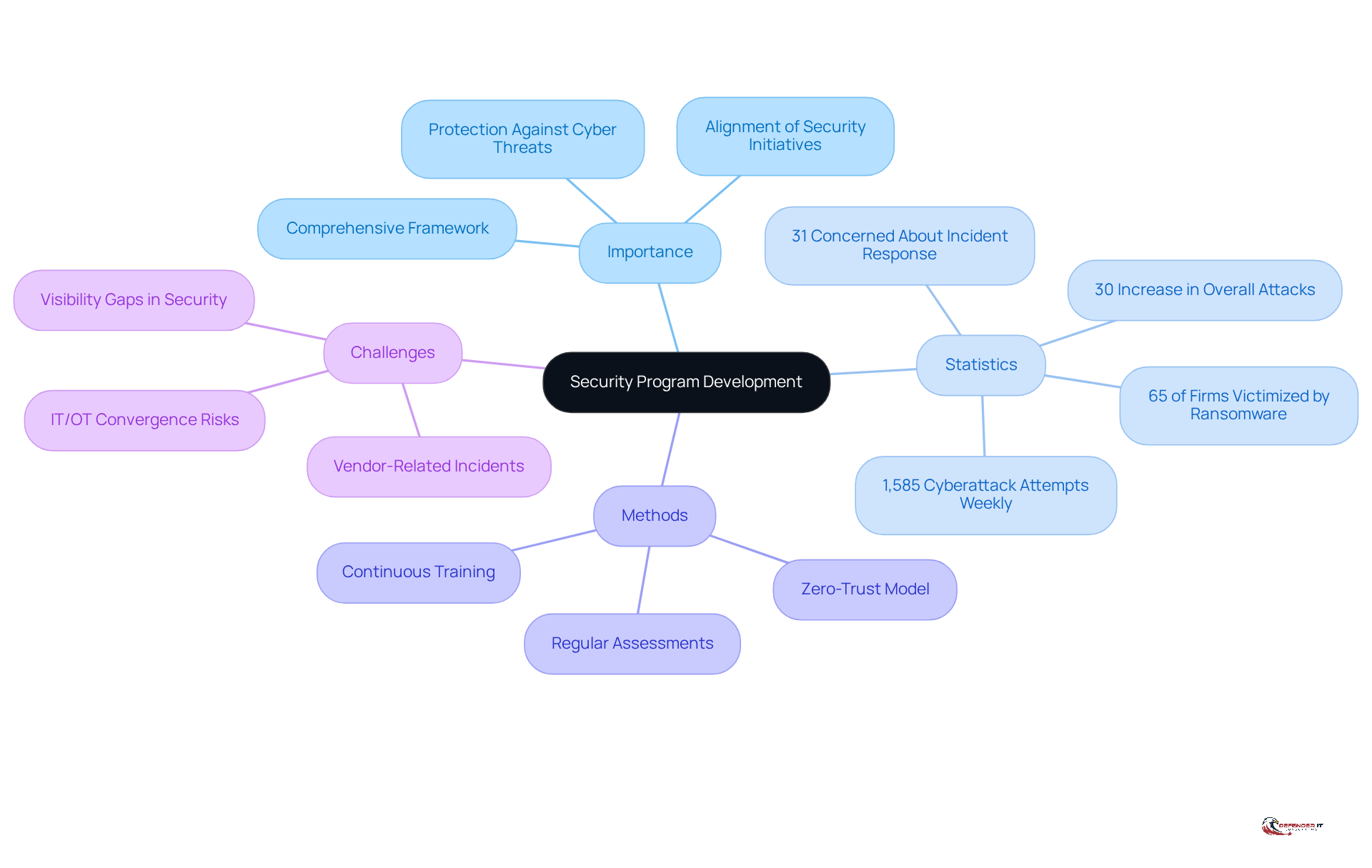
Creating a robust protection program is essential for industry leaders, as it establishes a comprehensive framework that guides an organization’s . This structure ensures that all are aligned and effective, addressing the specific challenges faced by the manufacturing sector. Customized protection programs, such as those offered by , focus on establishing clear policies, procedures, and best practices that are crucial for navigating the complex landscape of .
Statistics reveal that organizations with tailored protection frameworks experience significantly lower rates of successful cyberattacks. For instance, while 65% of production firms reported being victims of ransomware attacks last year, the average manufacturer faces approximately 1,585 attempted cyberattacks weekly, with overall attacks increasing by 30% year over year. This underscores the urgent need for effective . Furthermore, 31% of production and utilities firms identified as their primary concern, particularly as 46% of these entities were impacted by cybersecurity incidents caused by external vendors in the past year.
Coordinating protective measures across all organizational levels is critical, especially as the manufacturing sector increasingly integrates operational technology (OT) with information technology (IT). This convergence can introduce vulnerabilities if not managed appropriately. Effective program development methods in mssp cyber security include:
- Regular assessments of protective posture
- Continuous training for staff
- Implementing a zero-trust model that emphasizes stringent access controls and segmentation
As manufacturers enhance their digital presence, the necessity for a well-structured protection program becomes even more pronounced. By investing in , organizations can not only safeguard their assets but also ensure compliance with evolving regulatory standards, ultimately protecting their operations and reputation in an increasingly digital landscape.
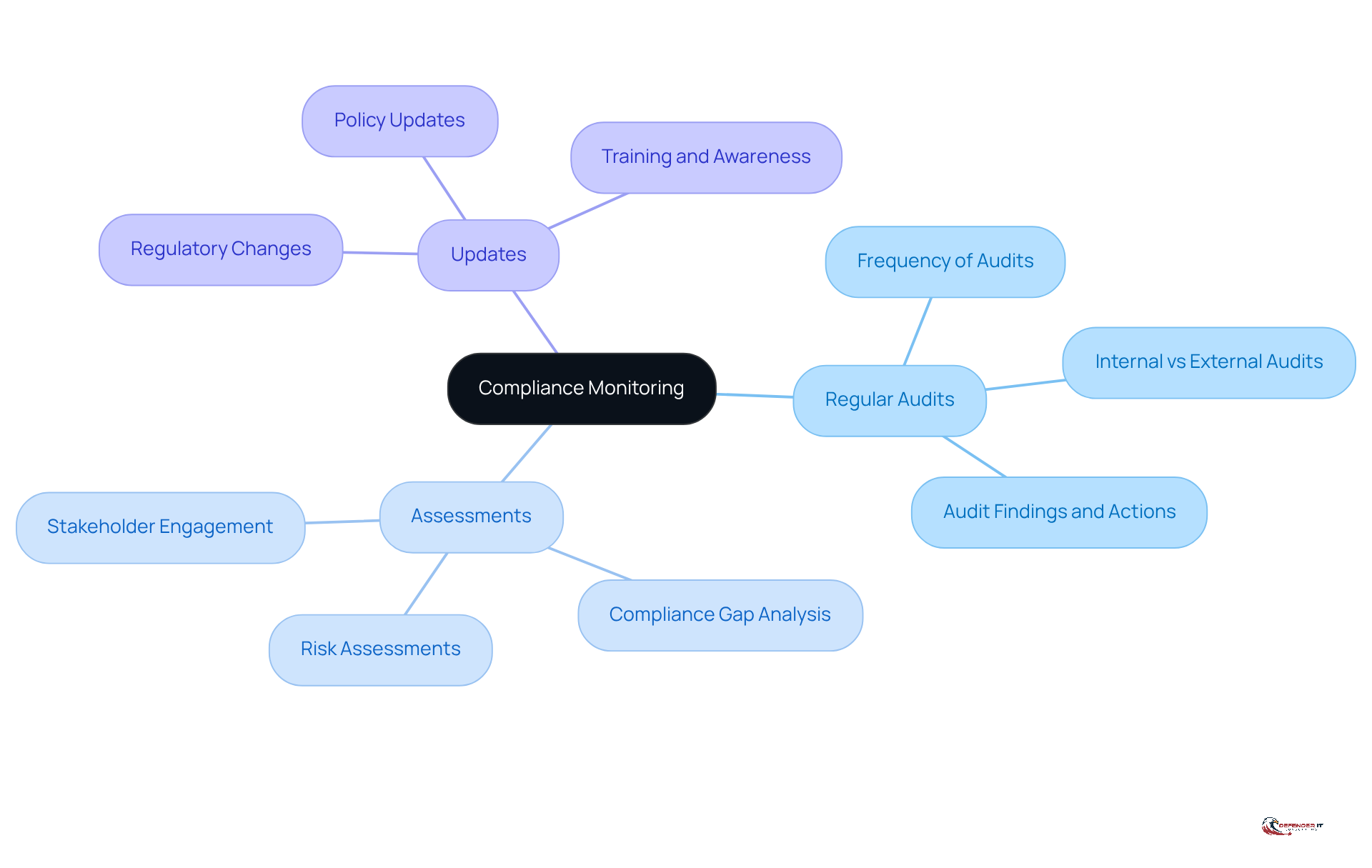
Compliance Monitoring: Ensuring Ongoing Adherence
Compliance monitoring is crucial for organizations to regularly assess their adherence to . For , this practice is essential to avoid penalties and . Defenderit Consulting provides designed to assist organizations in meeting their effectively. These services encompass:
- Assessments
- Updates
Ensuring that entities remain aligned with the .
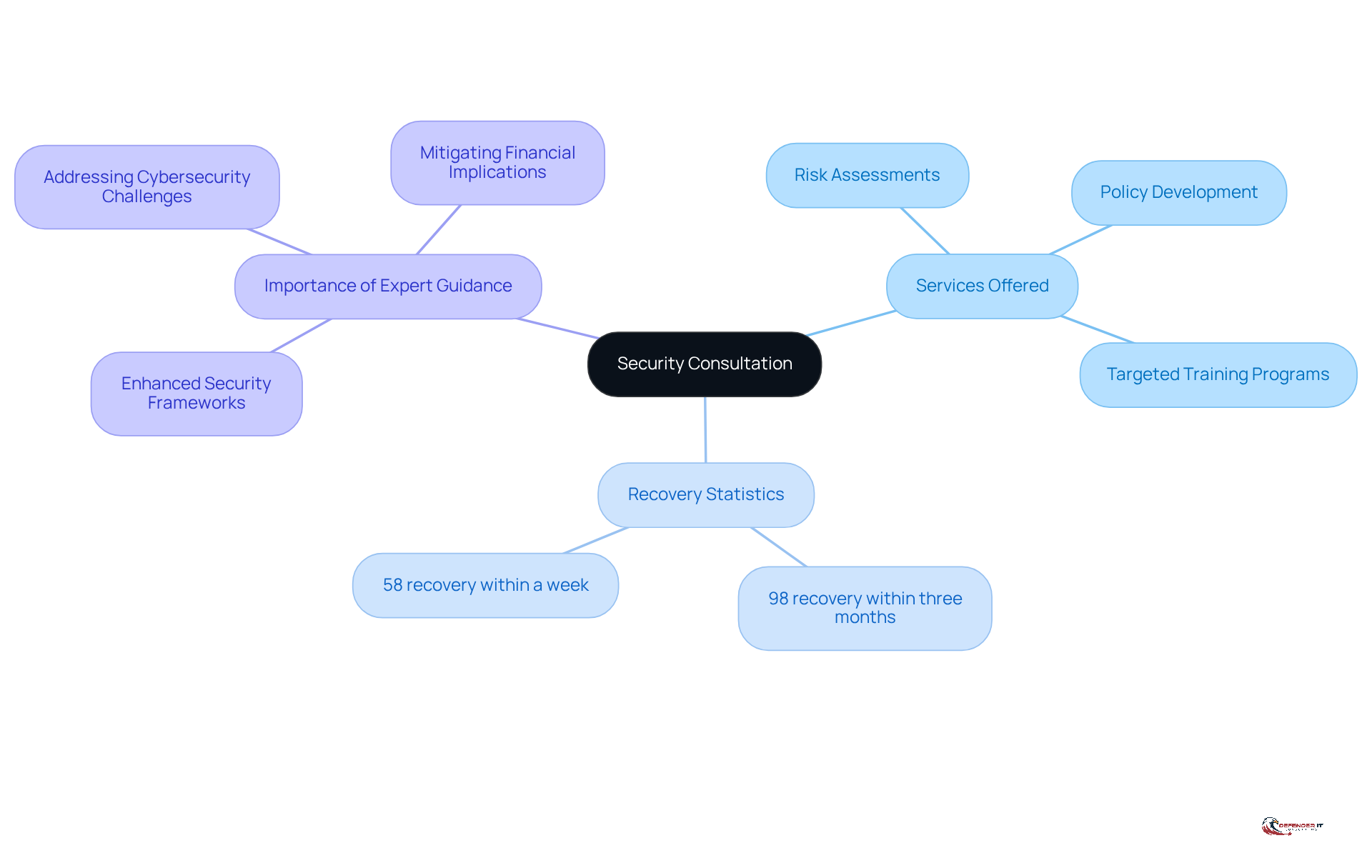
Security Consultation: Expert Guidance for Improvement
Security consultation is vital for manufacturing leaders who seek to enhance their . By engaging with experts, organizations can identify vulnerabilities and implement tailored strategies for improvement. specializes in delivering comprehensive , which include:
- Risk assessments
- Policy development
- Targeted training programs
These initiatives are crafted to address the unique challenges faced by the manufacturing sector, especially given the rising frequency of cyberattacks and the complexities of supply chains.
In 2026, the significance of is highlighted by the evolving landscape of . Recent trends show that organizations leveraging external expertise experience substantial enhancements in their . For example, a significant percentage of manufacturing firms reported improved resilience, with:
- 98% recovering from attacks within three months
- 58% recovering within a week
Additionally, the average recovery cost for production firms, excluding ransom payments, has decreased to $1.3 million, underscoring the financial implications of cyber incidents and the effectiveness of proactive protective measures.
Furthermore, a lack of expertise was identified by 42.5% of victims as a critical factor in , reinforcing the essential role of expert consultation in navigating complex cybersecurity challenges. Successful outcomes from often encompass the development of robust and compliance with industry regulations, both of which are crucial for maintaining operational integrity. As production companies continue to face advanced , the demand for expert advice becomes increasingly essential, ensuring they remain vigilant and prepared against potential attacks.
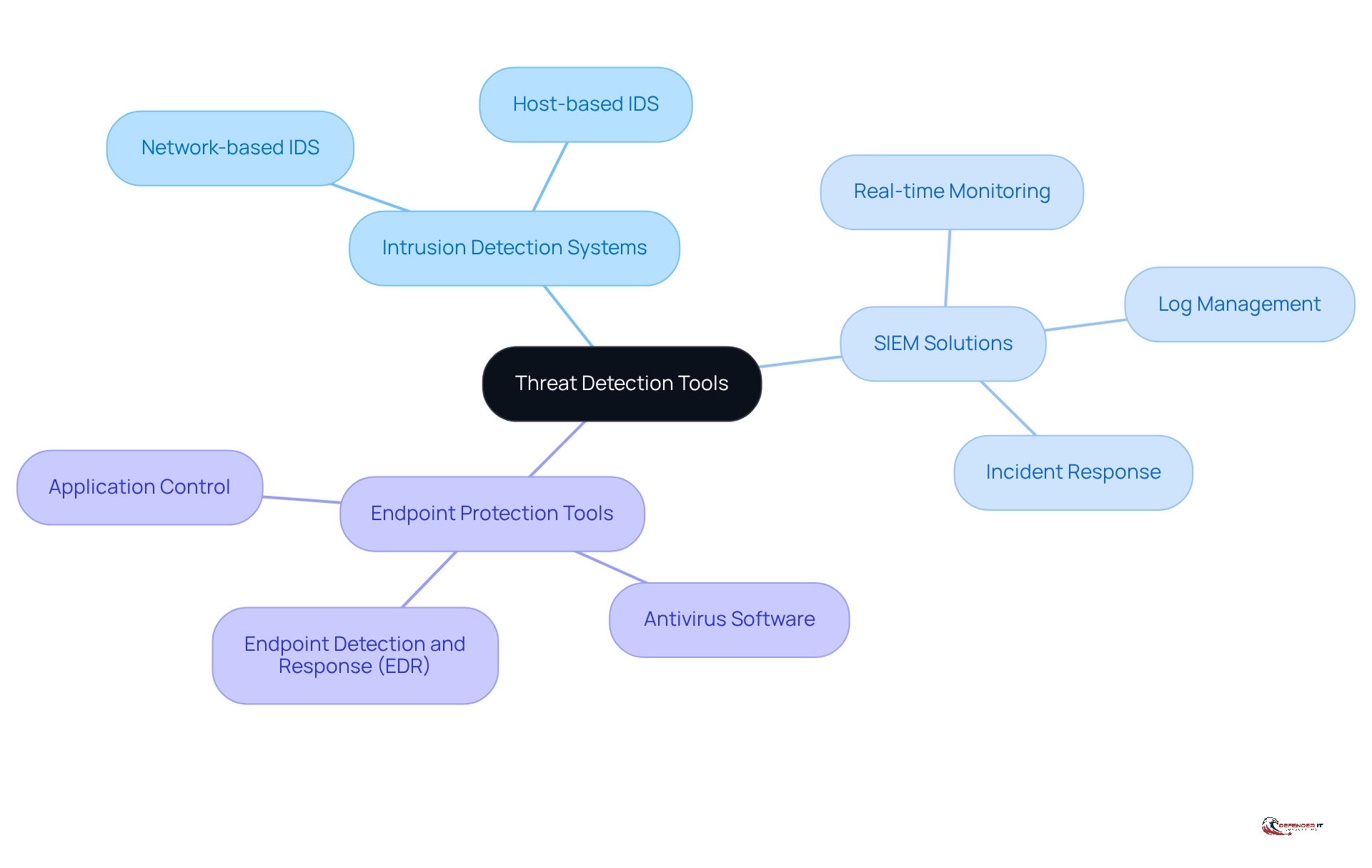
Threat Detection Tools: Essential Technologies for Protection
are crucial for identifying and addressing cyber threats in real-time. For leaders in manufacturing, the implementation of effective risk detection solutions is vital for ensuring safety. offers expert guidance on selecting and deploying the appropriate tools to enhance . This encompasses , including:
- (SIEM) solutions
These collectively provide comprehensive security coverage.
Conclusion
Manufacturing leaders must navigate an increasingly complex landscape of cyber threats, making a proactive and comprehensive approach to cybersecurity essential. Investing in comprehensive MSSP cyber security services is not merely a defensive measure; it is a strategic imperative for manufacturing leaders. By prioritizing services such as:
- Vulnerability assessments
- Penetration testing
- Incident response strategies
organizations can significantly enhance their security posture and protect their valuable assets.
Key insights highlight the importance of:
- Continuous security monitoring
- Compliance consulting
- The development of robust security programs tailored to the unique challenges of the manufacturing sector
As cyber threats evolve, the need for expert guidance and effective risk detection tools becomes paramount. Engaging with MSSP services not only assists manufacturers in navigating regulatory requirements but also fosters a culture of vigilance that is crucial in today’s digital landscape.
Ultimately, by taking proactive steps to address vulnerabilities and enhance security frameworks, organizations can protect their operations, ensure compliance, and maintain a competitive edge in an increasingly challenging environment. Embracing these essential services will empower manufacturers to thrive in a secure and resilient manner.
Frequently Asked Questions
What are vulnerability assessments and why are they important?
Vulnerability assessments are systematic evaluations that identify, quantify, and prioritize vulnerabilities within systems. They are crucial for organizations to understand where they are most at risk, particularly in the context of MSSP cyber security, and help protect against cyber threats.
How prevalent are vulnerability assessments in the manufacturing sector?
In 2026, approximately 75% of production firms reported conducting vulnerability assessments, highlighting their essential role in safeguarding operations against cyber threats.
What methods does Defenderit Consulting use for vulnerability assessments?
Defenderit Consulting utilizes advanced tools and methodologies to perform comprehensive assessments, ensuring that all potential weaknesses are thoroughly identified and documented.
How do vulnerability assessments align with compliance requirements?
Vulnerability assessments help organizations meet compliance requirements across various industry regulations, including those mandated by the Cybersecurity Maturity Model Certification (CMMC).
What alarming trends have been observed in manufacturing MSSP cyber security?
The manufacturing sector has been the most attacked industry for four consecutive years, with ransomware gangs claiming over 1,000 attacks in the past year, resulting in significant financial losses.
What is penetration testing and its significance?
Penetration testing is a process that simulates cyber attacks on systems to identify vulnerabilities that malicious actors could exploit. It provides a real-world assessment of security defenses, particularly valuable for manufacturing leaders.
How does Defenderit Consulting conduct penetration tests?
Defenderit Consulting conducts comprehensive penetration tests that closely mimic the tactics employed by cybercriminals, allowing organizations to see where their defenses may be insufficient.
What is threat intelligence and why is it essential?
Threat intelligence involves gathering and analyzing information about current and emerging threats to inform security strategies. It is essential for organizations to understand specific threats they face and implement effective defenses.
How does Defenderit Consulting provide threat intelligence services?
Defenderit Consulting offers tailored threat intelligence services that empower organizations to understand their specific threats, enhancing security and fostering a culture of vigilance.
What benefits does a proactive approach to threat intelligence offer?
A proactive approach to threat intelligence enhances security and helps organizations stay ahead of potential risks, ultimately fostering a resilient security posture.